
GaussDB
24.4.0
Service Overview
Issue 01
Date 2024-04-30
HUAWEI CLOUD COMPUTING TECHNOLOGIES CO., LTD.

Copyright © Huawei Cloud Computing Technologies Co., Ltd. 2024. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior
written consent of Huawei Cloud Computing Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are the property of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective
holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei
Cloud and the customer. All or part of the products, services and features described in this document may
not be within the purchase scope or the usage scope. Unless otherwise specied in the contract, all
statements, information, and recommendations in this document are provided "AS IS" without
warranties, guarantees or representations of any kind, either express or implied.
The information in this document is subject to change without notice. Every eort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute a warranty of any kind, express or implied.
Huawei Cloud Computing Technologies Co., Ltd.
Address: Huawei Cloud Data Center Jiaoxinggong Road
Qianzhong Avenue
Gui'an New District
Gui Zhou 550029
People's Republic of China
Website: https://www.huaweicloud.com/intl/en-us/
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. i
Contents
1 GaussDB Infographics............................................................................................................. 1
2 What Is GaussDB?....................................................................................................................3
3 Scenarios....................................................................................................................................6
4 Basic Concepts.......................................................................................................................... 7
5 Advantages............................................................................................................................. 10
6 DB Instance Description.......................................................................................................11
6.1 Instance Statuses.................................................................................................................................................................. 11
6.2 Instance Specications........................................................................................................................................................ 12
6.3 Instance Storage Types....................................................................................................................................................... 19
6.4 DB Engine Versions.............................................................................................................................................................. 20
6.5 DB Instance Types.................................................................................................................................................................21
6.6 DB Instance Parameters..................................................................................................................................................... 24
6.7 System Accounts for DB Instances..................................................................................................................................43
7 Compatibility with Oracle...................................................................................................45
7.1 Distributed Instances........................................................................................................................................................... 45
7.1.1 Oracle Compatibility Overview.....................................................................................................................................45
7.1.2 Basic SQL Elements...........................................................................................................................................................45
7.1.2.1 Data Types........................................................................................................................................................................ 46
7.1.2.2 Data Type Comparison Rules..................................................................................................................................... 52
7.1.2.3 Literals................................................................................................................................................................................57
7.1.2.4 Format Models................................................................................................................................................................58
7.1.2.5 Nulls....................................................................................................................................................................................59
7.1.2.6 Comments........................................................................................................................................................................ 59
7.1.2.7 Database Objects........................................................................................................................................................... 60
7.1.2.8 Database Object Names and Qualiers.................................................................................................................62
7.1.2.9 Syntax for Schema Objects and Parts in SQL Statements...............................................................................62
7.1.3 Pseudocolumns.................................................................................................................................................................. 63
7.1.4 Operators............................................................................................................................................................................. 64
7.1.5 Expressions...........................................................................................................................................................................67
7.1.6 Conditions............................................................................................................................................................................ 68
7.1.7 Common SQL DDL Clauses............................................................................................................................................70
GaussDB
Service Overview Contents
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. ii

7.1.8 SQL Queries and Subqueries......................................................................................................................................... 71
7.1.9 PL/SQL Language.............................................................................................................................................................. 72
7.1.9.1 Basic PL/SQL Syntax......................................................................................................................................................72
7.1.9.2 Data Type Compatibility.............................................................................................................................................. 75
7.1.9.3 Control Statements........................................................................................................................................................76
7.1.9.4 Collections and Records...............................................................................................................................................78
7.1.9.5 Static SQL Statements..................................................................................................................................................84
7.1.9.6 Dynamic SQL Statements........................................................................................................................................... 88
7.1.9.7 Triggers.............................................................................................................................................................................. 88
7.1.10 System Functions............................................................................................................................................................ 98
7.1.10.1 Single-row Functions..................................................................................................................................................99
7.1.10.2 Other Functions......................................................................................................................................................... 116
7.1.11 System Views................................................................................................................................................................. 118
7.1.12 Advanced Packages......................................................................................................................................................124
7.2 Primary/Standby Instances..............................................................................................................................................201
7.2.1 Oracle Compatibility Overview.................................................................................................................................. 201
7.2.2 Basic SQL Elements........................................................................................................................................................ 201
7.2.2.1 Data Types..................................................................................................................................................................... 202
7.2.2.2 Data Type Comparison Rules.................................................................................................................................. 209
7.2.2.3 Literals............................................................................................................................................................................. 213
7.2.2.4 Format Models............................................................................................................................................................. 214
7.2.2.5 Nulls................................................................................................................................................................................. 215
7.2.2.6 Comments...................................................................................................................................................................... 215
7.2.2.7 Database Objects.........................................................................................................................................................215
7.2.2.8 Database Object Names and Qualiers.............................................................................................................. 218
7.2.2.9 Syntax for Schema Objects and Parts in SQL Statements............................................................................ 218
7.2.3 Pseudocolumns................................................................................................................................................................ 218
7.2.4 Operators........................................................................................................................................................................... 220
7.2.5 Expressions........................................................................................................................................................................ 223
7.2.6 Conditions.......................................................................................................................................................................... 226
7.2.7 Common SQL DDL Clauses......................................................................................................................................... 229
7.2.8 SQL Queries and Subqueries.......................................................................................................................................231
7.2.9 PL/SQL Language............................................................................................................................................................232
7.2.9.1 Basic PL/SQL Syntax................................................................................................................................................... 232
7.2.9.2 Data Type Compatibility............................................................................................................................................237
7.2.9.3 Control Statements..................................................................................................................................................... 239
7.2.9.4 Collections and Records............................................................................................................................................ 241
7.2.9.5 Static SQL Statements............................................................................................................................................... 249
7.2.9.6 Dynamic SQL Statements......................................................................................................................................... 253
7.2.9.7 Triggers............................................................................................................................................................................254
7.2.10 System Functions.......................................................................................................................................................... 267
7.2.10.1 Single-Row Functions.............................................................................................................................................. 267
GaussDB
Service Overview Contents
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. iii

7.2.10.2 Other Functions......................................................................................................................................................... 291
7.2.11 System Views................................................................................................................................................................. 292
7.2.12 Advanced Packages......................................................................................................................................................299
8 Compatibility with MySQL Databases........................................................................... 395
8.1 Distributed Instances.........................................................................................................................................................395
8.1.1 MySQL Compatibility in MySQL-Compatible Mode............................................................................................395
8.1.1.1 MySQL Compatibility Overview..............................................................................................................................395
8.1.1.2 Data Types..................................................................................................................................................................... 395
8.1.1.2.1 Numeric Data Types................................................................................................................................................ 396
8.1.1.2.2 Date and Time Data Types................................................................................................................................... 404
8.1.1.2.3 String Data Types..................................................................................................................................................... 420
8.1.1.2.4 Binary Data Types.................................................................................................................................................... 425
8.1.1.2.5 JSON Data Type........................................................................................................................................................ 427
8.1.1.2.6 Attributes Supported by Data Types..................................................................................................................427
8.1.1.2.7 Data Type Conversion.............................................................................................................................................428
8.1.1.3 System Functions......................................................................................................................................................... 431
8.1.1.3.1 Flow Control Functions.......................................................................................................................................... 431
8.1.1.3.2 Date and Time Functions...................................................................................................................................... 435
8.1.1.3.3 String Functions........................................................................................................................................................ 449
8.1.1.3.4 Forced Conversion Functions................................................................................................................................455
8.1.1.3.5 Encryption Functions...............................................................................................................................................456
8.1.1.3.6 JSON Functions......................................................................................................................................................... 456
8.1.1.3.7 Aggregate Functions............................................................................................................................................... 459
8.1.1.3.8 Arithmetic Functions............................................................................................................................................... 461
8.1.1.3.9 Other Functions........................................................................................................................................................ 462
8.1.1.4 Operators........................................................................................................................................................................462
8.1.1.5 Character Sets............................................................................................................................................................... 464
8.1.1.6 Collation Rules..............................................................................................................................................................464
8.1.1.7 SQL................................................................................................................................................................................... 465
8.1.1.7.1 DDL............................................................................................................................................................................... 466
8.1.1.7.2 DML.............................................................................................................................................................................. 476
8.1.1.7.3 DCL................................................................................................................................................................................ 488
8.1.1.8 Drivers..............................................................................................................................................................................489
8.1.1.8.1 JDBC.............................................................................................................................................................................. 489
8.2 Primary/Standby Instances..............................................................................................................................................489
8.2.1 Introduction.......................................................................................................................................................................490
8.2.2 MySQL Compatibility in B-Compatible Mode.......................................................................................................490
8.2.2.1 MySQL Compatibility Overview..............................................................................................................................490
8.2.2.2 Data Types..................................................................................................................................................................... 490
8.2.2.2.1 Numeric Data Types................................................................................................................................................ 490
8.2.2.2.2 Date and Time Data Types................................................................................................................................... 498
8.2.2.2.3 String Data Types..................................................................................................................................................... 514
GaussDB
Service Overview Contents
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. iv

8.2.2.2.4 Binary Data Types.................................................................................................................................................... 519
8.2.2.2.5 JSON Data Type........................................................................................................................................................ 521
8.2.2.2.6 Attributes Supported by Data Types..................................................................................................................521
8.2.2.2.7 Data Type Conversion.............................................................................................................................................522
8.2.2.3 System Functions......................................................................................................................................................... 525
8.2.2.3.1 Flow Control Functions.......................................................................................................................................... 525
8.2.2.3.2 Date and Time Functions...................................................................................................................................... 529
8.2.2.3.3 String Functions........................................................................................................................................................ 543
8.2.2.3.4 Forced Conversion Functions................................................................................................................................550
8.2.2.3.5 Encryption Functions...............................................................................................................................................550
8.2.2.3.6 Information Functions............................................................................................................................................ 550
8.2.2.3.7 JSON Functions......................................................................................................................................................... 551
8.2.2.3.8 Aggregate Functions............................................................................................................................................... 553
8.2.2.3.9 Arithmetic Functions............................................................................................................................................... 555
8.2.2.3.10 Other Functions......................................................................................................................................................555
8.2.2.4 Operators........................................................................................................................................................................556
8.2.2.5 Character Sets............................................................................................................................................................... 558
8.2.2.6 Collation Rules..............................................................................................................................................................558
8.2.2.7 Expressions.....................................................................................................................................................................559
8.2.2.8 SQL................................................................................................................................................................................... 560
8.2.2.8.1 DDL............................................................................................................................................................................... 560
8.2.2.8.2 DML.............................................................................................................................................................................. 573
8.2.2.8.3 DCL................................................................................................................................................................................ 586
8.2.2.9 Drivers..............................................................................................................................................................................587
8.2.2.9.1 JDBC.............................................................................................................................................................................. 587
8.2.3 MySQL Compatibility in M-Compatible Mode......................................................................................................587
8.2.3.1 MySQL Compatibility Overview..............................................................................................................................588
8.2.3.2 Data Types..................................................................................................................................................................... 589
8.2.3.2.1 Numeric Data Types................................................................................................................................................ 589
8.2.3.2.2 Date and Time Data Types................................................................................................................................... 592
8.2.3.2.3 String Data Types..................................................................................................................................................... 594
8.2.3.2.4 Binary Data Types.................................................................................................................................................... 598
8.2.3.2.5 Attributes Supported by Data Types..................................................................................................................602
8.2.3.2.6 Data Type Conversion.............................................................................................................................................603
8.2.3.3 System Functions......................................................................................................................................................... 607
8.2.3.3.1 Flow Control Functions.......................................................................................................................................... 609
8.2.3.3.2 Date and Time Functions...................................................................................................................................... 609
8.2.3.3.3 String Functions........................................................................................................................................................ 617
8.2.3.3.4 Forced Conversion Functions................................................................................................................................620
8.2.3.3.5 Encryption Functions...............................................................................................................................................621
8.2.3.3.6 Comparison Functions............................................................................................................................................ 622
8.2.3.3.7 Aggregate Functions............................................................................................................................................... 623
GaussDB
Service Overview Contents
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. v

8.2.3.3.8 Arithmetic Functions............................................................................................................................................... 625
8.2.3.3.9 Other Functions........................................................................................................................................................ 626
8.2.3.4 Operators........................................................................................................................................................................626
8.2.3.5 Character Sets............................................................................................................................................................... 636
8.2.3.6 Collation Rules..............................................................................................................................................................637
8.2.3.7 Transactions................................................................................................................................................................... 638
8.2.3.8 SQL................................................................................................................................................................................... 642
8.2.3.8.1 Keywords..................................................................................................................................................................... 643
8.2.3.8.2 Identiers.................................................................................................................................................................... 644
8.2.3.8.3 DDL............................................................................................................................................................................... 646
8.2.3.8.4 DML.............................................................................................................................................................................. 666
8.2.3.8.5 DCL................................................................................................................................................................................ 677
8.2.3.8.6 Other Statements.....................................................................................................................................................677
8.2.3.8.7 Users and Permissions............................................................................................................................................679
8.2.3.8.8 System Catalogs and System Views.................................................................................................................. 685
9 Security.................................................................................................................................. 690
9.1 Shared Responsibilities..................................................................................................................................................... 690
9.2 Identity Authentication and Access Control..............................................................................................................691
9.2.1 Service Access Control................................................................................................................................................... 691
9.3 Data Protection................................................................................................................................................................... 692
9.4 Audit and Logs.................................................................................................................................................................... 693
9.5 Risk Monitoring................................................................................................................................................................... 693
9.6 Fault Recovery..................................................................................................................................................................... 694
9.7 Certicates............................................................................................................................................................................ 694
10 Permissions Management...............................................................................................696
11 GaussDB Constraints........................................................................................................ 703
12 Billing...................................................................................................................................707
13 Related Services................................................................................................................ 709
A Change History....................................................................................................................710
GaussDB
Service Overview Contents
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. vi

1 GaussDB Infographics
GaussDB
Service Overview 1 GaussDB Infographics
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 1

Figure 1-1 Introduction to Huawei Cloud GaussDB
GaussDB
Service Overview 1 GaussDB Infographics
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 2

2 What Is GaussDB?
GaussDB is a distributed relational database from Huawei. It supports intra-city
cross-AZ deployment with zero data loss. With a distributed architecture, GaussDB
supports petabytes of storage and contains more than 1,000 nodes per DB
instance. It is highly available, secure, and scalable and provides services including
quick deployment, backup, restoration, monitoring, and alarm reporting for
enterprises.
Progressive Knowledge
You can go to GaussDB Progressive Knowledge to learn the basic concepts and
usage of GaussDB.
Using GaussDB
You can use GaussDB in either of the following ways:
● Management console: Create and manage DB instances on the management
console.
● API: You can call APIs to use GaussDB. For details, see GaussDB API
Reference.
Architecture of a Distributed GaussDB Instance
The overall architecture of a distributed GaussDB instance is as follows.
GaussDB
Service Overview 2 What Is GaussDB?
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 3

Figure 2-1 Overall architecture of a distributed GaussDB instance
● Coordinator node: A coordinator node (CN) receives access requests from
applications and returns execution results to clients. It also splits and
distributes tasks to dierent data nodes (DNs) for parallel processing.
● GTM: The global transaction manager (GTM) generates and maintains the
global transaction IDs, transaction snapshots, timestamps, and sequences that
must be unique globally.
● Data node: A DN stores service data, performs data queries, and returns
execution results to a CN.
Architecture of a Primary/Standby GaussDB Instance
The overall architecture of a primary/standby GaussDB instance is as follows.
GaussDB
Service Overview 2 What Is GaussDB?
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 4

Figure 2-2 Overall architecture of a primary/standby GaussDB instance
● ETCD: The editable text conguration daemon (ETCD) is used for shared
conguration and service discovery (service registry and search).
● CMS: The cluster manager (CMS) manages and monitors the running status
of functional units and physical resources in a distributed system, ensuring
stable running of the entire system.
● Data node: A DN stores service data, performs data queries, and returns
execution results.
GaussDB
Service Overview 2 What Is GaussDB?
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 5
3 Scenarios
● Transaction applications
The distributed, highly scalable architecture of GaussDB makes it an ideal t
for highly concurrent online transactions containing a large volume of data
from government, nance, e-commerce, O2O, telecom customer relationship
management (CRM), and billing. GaussDB supports dierent deployment
models.
● CDR query
GaussDB can process petabytes of data and use the memory analysis
technology to query massive volumes of data when data is being written to
databases. Therefore, it is suitable for the Call Detail Record (CDR) query
service in the security, telecom, nance, and Internet of things (IoT) sectors.
GaussDB
Service Overview 3 Scenarios
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 6

4 Basic Concepts
Instances
The smallest management unit of GaussDB is the instance. A DB instance is an
isolated database environment on the cloud. You can create and manage
instances on the management console. For details about instance statuses,
instance specications, storage types, and versions, see DB Instance Description.
DB Engine Version
GaussDB supports the following versions: 3.223, 3.226, and 8.102.
Instance Types
GaussDB supports distributed and primary/standby instances.
● You can add nodes for distributed instances as needed to handle large
volumes of concurrent requests.
● The primary/standby instances are suitable for scenarios with small and stable
volumes of data, where data reliability and service availability are extremely
important.
Instance Specications
The instance specications determine the computation (vCPUs) and memory
capacity (in GB) of an instance. For details, see Instance Specications.
Coordinator Nodes
A coordinator node (CN) receives access requests from applications and returns
execution results to clients. It also splits and distributes tasks to dierent data
nodes (DNs) for parallel processing.
Data Nodes
A data node (DN) stores service data, queries data, and returns execution results
to CNs.
GaussDB
Service Overview 4 Basic Concepts
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 7

Automated Backups
When you buy a GaussDB instance, an automated backup policy is enabled by
default with the retention period set to seven days. You can modify it as required.
GaussDB automatically creates full backups for the instance based on your
conguration.
Manual Backups
Manual backups are user-initiated full backups of instances. They are retained
until you delete them manually.
Regions and AZs
A region and availability zone (AZ) identify the location of a data center. You can
create resources in a specic region and AZ.
● Regions are dened by a combination of geographical location and network
latency. Public services, such as Elastic Cloud Server (ECS), Elastic Volume
Service (EVS), Object Storage Service (OBS), Virtual Private Cloud (VPC),
Elastic IP (EIP), and Image Management Service (IMS), are shared within the
same region. Regions can be universal or dedicated. A universal region
provides all sorts of cloud services for all users. A dedicated region provides
only services of a given type or only for specic users.
● An AZ contains one or more physical data centers. Each AZ has independent
cooling, re extinguishing, moisture-proong, and electricity facilities. Within
an AZ, compute, network, storage, and other resources are logically divided
into multiple instances. AZs within a region are interconnected using high-
speed optical bers to allow you to build highly available systems across AZs.
Figure 4-1 shows the relationship between regions and AZs.
Figure 4-1 Regions and AZs
Huawei Cloud provides services in many regions around the world. You can select
a region and an AZ as needed. For more information, see Global Products and
Services.
GaussDB
Service Overview 4 Basic Concepts
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 8

Projects
Projects are used to group and isolate OpenStack resources (compute, storage,
and network resources). A project can be a department or a project team. Multiple
projects can be created for one account.
GaussDB
Service Overview 4 Basic Concepts
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 9

5 Advantages
● High Security
GaussDB provides the following features to let you enjoy the security of top-
level commercial databases. These features meet the core data security
requirements of enterprises, government, and nance institutions.
Dynamic data masking, row-level access control, and cryptographic
computing
● Comprehensive Tools and Service-oriented Capabilities
GaussDB can be deployed in Huawei Cloud for commercial use and can work
with ecosystem tools such as Data Replication Service (DRS) and Data Admin
Service (DAS) to make database development, O&M, tuning, monitoring, and
migration easy.
● In-House, Full-Stack Development
GaussDB provides guaranteed business continuity with full-stack, independent
and controllable capabilities. Based on the Kunpeng ecosystem, GaussDB
performance is always improved to meet ever-increasing demands in dierent
scenarios.
● Open-Source Ecosystem
The primary/standby version of GaussDB is available for you to download
from the open source community.
GaussDB
Service Overview 5 Advantages
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 10

6 DB Instance Description
6.1 Instance Statuses
Instance Statuses
The status of a DB instance reects the health of the instance. You can use the
management console to view the status of a DB instance.
Table 6-1 DB Instance statuses
Status
Description
Available The instance is available.
Abnormal The instance is unavailable.
Creating The instance is being created.
Creation failed The instance failed to be created.
Rebooting The DB instance is being rebooted.
Starting The DB instance is being started.
Starting node The DB instance node is being started.
Stopping The DB instance is being stopped.
Stopping node The DB instance node is being stopped.
Stopped The DB instance or node is stopped.
Scaling up The storage space of the instance is being scaled up.
Adding nodes The nodes are being added to the instance.
Backing up The backup is being created.
Restoring The instance is being restored from a backup.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 11

Status Description
Restore failed The instance failed to be restored.
Frozen The instance is frozen because of an unpaid account
balance. Frozen instances are unfrozen only after your
account is recharged and the overdue payments are
cleared.
Storage full The storage space of the instance is full. No more data can
be written to the databases on this instance. You need to
scale up the storage space to restore the instance to be
available.
Deleted The instance has been deleted. Deleted instances will not
be displayed in the instance list.
Upgrading The engine version is being upgraded.
Parameters
change. Pending
reboot
A modication to a database parameter is waiting for a DB
instance reboot before it can take eect.
Changing replicas The number of replicas for the DB instance is being
reduced.
Backup Statuses
Table 6-2 Backup statuses
Status
Description
Completed The backup was successfully created.
Failed The backup failed to be created.
Creating The backup is being created.
6.2 Instance Specications
GaussDB instances in dierent regions support x86 or Arm architecture. For
details, see Table 6-3. GaussDB instances also support dierent specications. For
details, see Table 6-4.
● x86: Dedicated (with a CPU-to-memory ratio of 1:4), dedicated (with a CPU-
to-memory ratio of 1:8), and general-purpose (with a CPU-to-memory ratio
of 1:4)
● Arm: Kunpeng dedicated (with a CPU-to-memory ratio of 1:4) and Kunpeng
dedicated (with a CPU-to-memory ratio of 1:8)
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 12
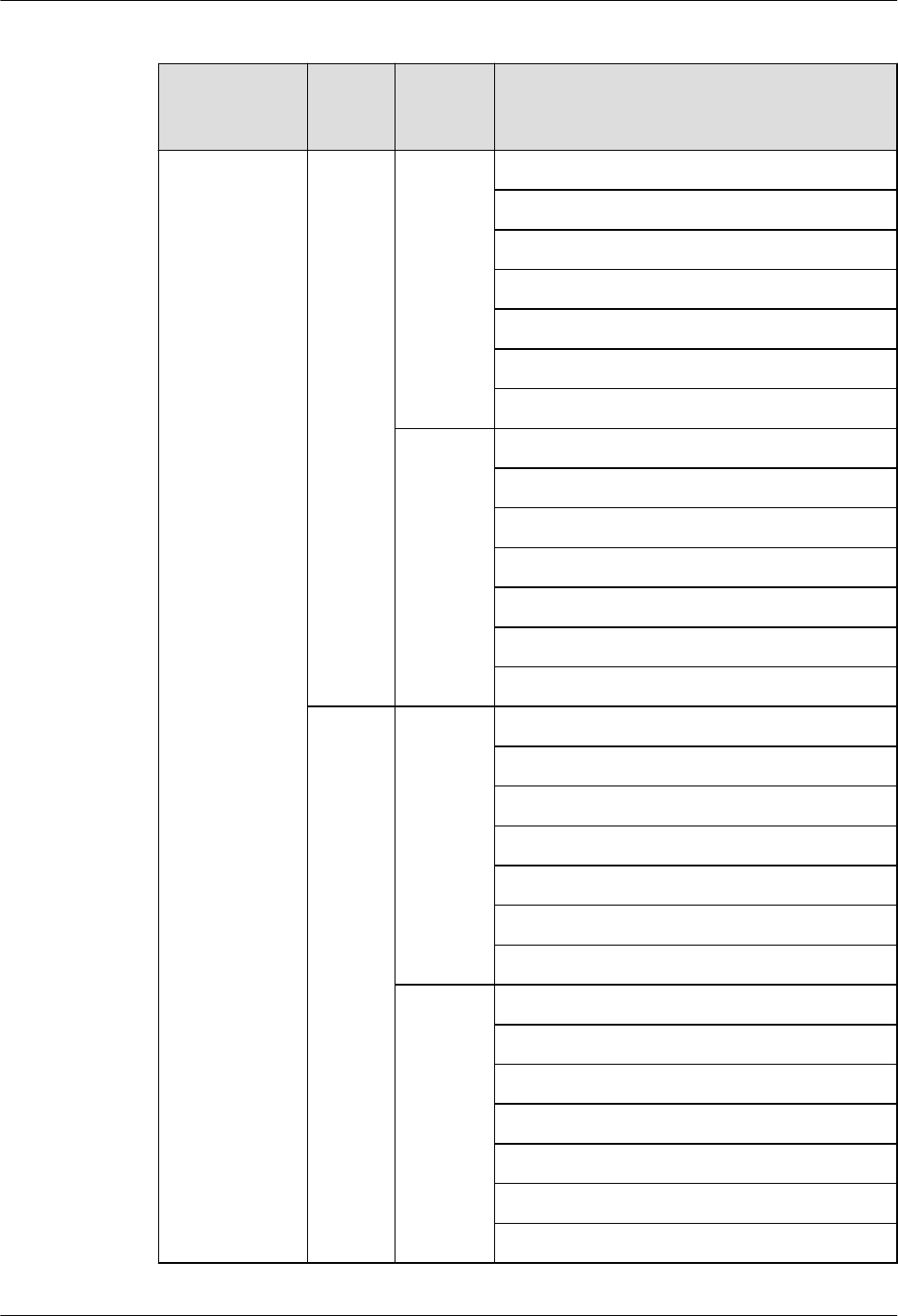
Table 6-3 Regions supported by GaussDB
Instance Type Speci
cation
Type
Billing
Mode
Region
Distributed Dedica
ted
(1:4)
Pay-per-
use
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Yearly/
monthly
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Kunpe
ng
dedicat
ed
(1:8)
Pay-per-
use
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Yearly/
monthly
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 13

Instance Type Speci
cation
Type
Billing
Mode
Region
Genera
l-
purpos
e (1:4)
Pay-per-
use
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Yearly/
monthly
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Primary/
Standby
Dedica
ted
(1:4)
Pay-per-
use
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Yearly/
monthly
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 14

Instance Type Speci
cation
Type
Billing
Mode
Region
Genera
l-
purpos
e (1:4)
Pay-per-
use
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
Yearly/
monthly
AP-Singapore
CN East-Shanghai1
CN North-Beijing4
CN South-Guangzhou
CN Southwest-Guiyang1
AF-Johannesburg
LA-Sao Paulo1
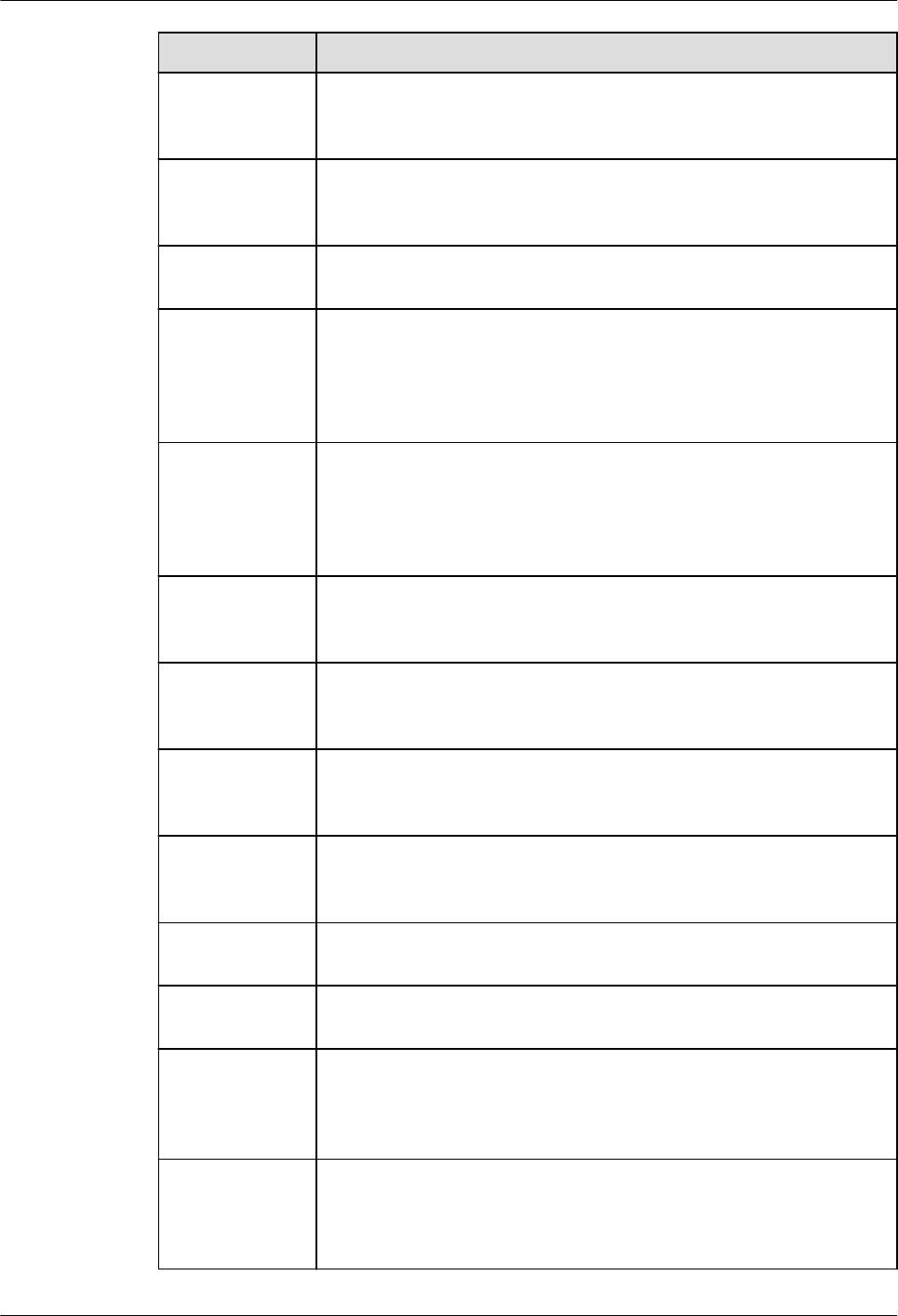
Table 6-4 Instance specications
Serv
ice
Typ
e
DB
Inst
ance
Type
Specication
Type
vCPUs Memory
(GB)
Default
Maximum
Connections
(Per CN)
Ente
rpris
e
editi
on
Distr
ibute
d
Dedicated (1:4)
NOTE
Dedicated (1:4)
is based on the
x86
architecture.
8 32 100
16 64 1,000
32 128 2,000
64 256 4,000
Dedicated (1:8)
NOTE
Dedicated (1:8)
is based on the
x86
architecture.
8 64 1,000
16 128 2,000
32 256 4,000
64 512 8,000
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 15

Serv
ice
Typ
e
DB
Inst
ance
Type
Specication
Type
vCPUs Memory
(GB)
Default
Maximum
Connections
(Per CN)
Kunpeng
dedicated (1:4)
NOTE
Kunpeng
dedicated (1:4)
is based on the
Arm
architecture.
8 32 100
16 64 1,000
32 128 2,000
64 256 4,000
Kunpeng
dedicated (1:8)
NOTE
Kunpeng
dedicated (1:8)
is based on the
Arm
architecture.
8 64 1,000
16 128 2,000
32 256 4,000
60 480 8,000
Prim
ary/
Stan
dby
Dedicated (1:4)
NOTE
Dedicated (1:4)
is based on the
x86
architecture.
4 16 300
8 32 600
16 64 2,048
32 128 5,000
Dedicated (1:8)
NOTE
Dedicated (1:8)
is based on the
x86
architecture.
4 32
NOTE
This
specication
is not
available for
production
environments
, but you can
submit a
service ticket
to request it
at Service
Tickets >
Create
Service
Ticket in the
upper right
corner of the
management
console.
600
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 16

Serv
ice
Typ
e
DB
Inst
ance
Type
Specication
Type
vCPUs Memory
(GB)
Default
Maximum
Connections
(Per CN)
8 64
NOTE
Only
primary/
standby
instances of
version 2.6 or
later can be
used in the
production
environment.
2,048
16 128 5,000
32 256 11,000
64 512 25,000
Kunpeng
dedicated (1:4)
NOTE
Kunpeng
dedicated (1:4)
is based on the
Arm
architecture.
4 16 300
8 32 600
16 64 2,048
32 128 5,000
Kunpeng
dedicated (1:8)
NOTE
Kunpeng
dedicated (1:8)
is based on the
Arm
architecture.
4 32
NOTE
This
specication
is not
available for
production
environments
, but you can
submit a
service ticket
to request it
at Service
Tickets >
Create
Service
Ticket in the
upper right
corner of the
management
console.
600
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 17

Serv
ice
Typ
e
DB
Inst
ance
Type
Specication
Type
vCPUs Memory
(GB)
Default
Maximum
Connections
(Per CN)
8 64
NOTE
Only
primary/
standby
instances of
version 2.6 or
later can be
used in the
production
environment.
2,048
16 128 5,000
32 256 11,000
60 480 24,000
Basi
c
editi
on
Distr
ibute
d
Dedicated (1:4)
NOTE
Dedicated (1:4)
is based on the
x86
architecture.
16 64 200
32 128 350
64 256 900
Dedicated (1:8)
NOTE
Dedicated (1:8)
is based on the
x86
architecture.
16 128 350
32 256 900
64 512 2,000
Kunpeng
dedicated (1:4)
NOTE
Kunpeng
dedicated (1:4)
is based on the
Arm
architecture.
16 64 200
32 128 350
Kunpeng
dedicated (1:8)
NOTE
Kunpeng
dedicated (1:8)
is based on the
Arm
architecture.
16 128 350
32 256 900
60 480 1,800
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 18

Serv
ice
Typ
e
DB
Inst
ance
Type
Specication
Type
vCPUs Memory
(GB)
Default
Maximum
Connections
(Per CN)
Prim
ary/
Stan
dby
General-
purpose (1:4)
NOTE
General-
purpose (1:4) is
based on the
x86
architecture.
4 16 300
8 32 600
Dedicated (1:4)
NOTE
Dedicated (1:4)
is based on the
x86
architecture.
4 16 300
8 32 600
16 64 2,048
32 128 5,000
64 256 11,000
Kunpeng
dedicated (1:4)
NOTE
Kunpeng
dedicated (1:4)
is based on the
Arm
architecture.
4 16 300
8 32 600
16 64 2,048
32 128 5,000
6.3 Instance Storage Types
The database system is generally an important system in the IT system and has
high requirements on storage I/O performance. GaussDB supports ultra-high I/O
and extreme SSD storage types.
● Ultra-high I/O: Ultra-high performance cloud disks excellent for enterprise
mission-critical services as well as workloads demanding high throughput and
low latency The maximum throughput is 800 MB/s.
● Extreme SSD: Superfast disks ideal for workloads demanding ultra-high
bandwidth and ultra-low latency. The maximum throughput is 2,500 MB/s.
NO TE
To apply for the permissions needed for using the extreme SSD storage type, submit an
application by choosing Service Tickets > Create Service Ticket in the upper right corner
of the management console.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 19

6.4 DB Engine Versions
GaussDB Engine Version Description
GaussDB uses version numbers in dot-decimal notation. The format is
A
.
BCD
,
where:
●
A
:
A
designates major versions. Generally, a major version provides
architecture upgrades and major new features.
●
BCD
: The rst digit (
B
) indicates a release that provides major feature
updates, and the last two digits (
C
and
D
) indicate progressively more minor
releases that provide important updates.
Mapping Between GaussDB DB Engine and Kernel Engine Versions
Table 6-5 lists the mapping between GaussDB versions.
For details about how to query the DB engine version and kernel engine version of
a GaussDB instance, see Checking the DB Engine and Kernel Engine Version of
a GaussDB Instance.
Table 6-5 Mapping between GaussDB DB engine and kernel engine versions
DB Engine Version
Kernel Engine Version
8.102.0 505.1.0
3.226.0 503.1.0.SPC2300
3.223.0 503.1.0.SPC2000
3.222.0 503.1.0.SPC1700
3.220.0 503.1.0.SPC1500
3.208.0 503.1.0.SPC1200
3.207.0 503.1.0.SPC1100
3.201.0 503.1.0.SPC0200
Checking the DB Engine and Kernel Engine Version of a GaussDB Instance
1. Log in to the management console.
2. Click
in the upper left corner and select a region and project.
3. Click
in the upper left corner of the page and choose Databases >
GaussDB.
4. On the Instances page, click the name of the target instance to go to the
Basic Information page.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 20

5. On the Basic Information page of the target instance, view the instance
version and kernel version in the DB Engine Version eld and Kernel Engine
Version eld in the DB Information area.
Figure 6-1 Basic information
6.5 DB Instance Types
Table 6-6 lists the instance types of GaussDB.
Table 6-6 Instance types
Inst
anc
e
Typ
e
Deployment Model Scale-
out
Support
ed
Applicatio
n Scenario
Comp
onent
Service
Processing
Dist
ribu
ted
Independent
deployment: Database
components are
deployed on dierent
nodes. This model is
suitable for where high
reliability and stability
are required and the
instance scale is large.
Combined: 3-node
deployment where
there are three shards
and each shard
contains one primary
DN and two standby
DNs.
Yes The data
volume is
large, and
large data
capacity
and high
concurrenc
y are
required.
● O
M
● CM
● GT
M
● ETC
D
● CN
● DN
An application
sends a SQL
query request
to a CN. The
CN uses the
optimizer of
the database
to generate an
execution plan
and sends the
plan to DNs.
Each DN
processes data
based on the
execution
plan. After the
processing is
complete, DNs
return the
result set to
the CN for
summary.
Finally, the CN
returns the
summary
result to the
application.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 21

Inst
anc
e
Typ
e
Deployment Model Scale-
out
Support
ed
Applicatio
n Scenario
Comp
onent
Service
Processing
Pri
mar
y/
Sta
ndb
y
HA (1 primary + 2
standby): 3-node
deployment where
there is a shard. The
shard contains one
primary DN and two
standby DNs.
Single replica: single-
node deployment
where there is only one
CMS component and
one DN. This
deployment model is
not suitable for
production
environments. To
create a single-replica
instance, ensure that
the instance version is
2.2 or later. The
availability (SLA)
cannot be guaranteed
because the instance is
deployed on a single
server.
1 primary + 1 standby
+ 1 log: 3-node
deployment where
there is a shard. The
shard contains one
primary DN, one
standby DN, and one
log-dedicated DN.
No
The data
volume is
small and
stable, and
data
reliability
and service
availability
are
extremely
important.
● O
M
● CM
● ETC
D
● DN
An application
sends a task
directly to the
DN, and the
DN returns the
result to the
application
after
processing the
task.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 22

NO TE
● OM: The Operation Manager (OM) provides management APIs and tools for routine
maintenance and conguration management of the cluster.
● CM: The Cluster Manager (CM) manages and monitors the running status of functional
units and physical resources in a distributed system, ensuring stable running of the
entire system.
● GTM: The Global Transaction Manager (GTM) generates and maintains the global
transaction IDs, transaction snapshots, timestamps, and sequences that must be unique
globally.
● ETCD: The editable text conguration daemon (ETCD) is used for shared conguration
and service discovery (service registry and search).
● CN: A CN receives access requests from applications and returns execution results to
clients. It also splits and distributes tasks to dierent DNs for parallel processing.
● DN: A DN stores service data, performs data queries, and returns execution results.
The following gure shows the logical architecture of a distributed GaussDB
instance.
Figure 6-2 Logical architecture of a distributed instance
The following gure shows the logical architecture of a primary/standby GaussDB
instance.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 23

Figure 6-3 Logical architecture of a primary/standby instance
6.6 DB Instance Parameters
This section describes the GaussDB instance parameters that can be modied.
● Congurable parameters for version 3.
X
– Parameters for distributed instances
– Parameters for primary/standby instances
● Congurable parameters for version 2.
X
– Parameters for distributed instances
– Parameters for primary/standby instances
Congurable Parameters for Version 3.
X
The following table describes parameters that can be modied.
Table 6-7 Parameters for distributed instances
Parameter
Description
audit_system_o
bject
Determines whether to audit the CREATE, DROP, and ALTER
operations on GaussDB Kernel database objects. GaussDB
Kernel database objects include databases, users, schemas,
and tables. You can change the parameter value to audit only
the operations on required database objects. During a forcible
primary/standby failover, set audit_system_object to the
maximum value and audit all DDL objects. If the parameter
value is incorrectly changed, DDL audit logs will be lost.
Contact technical support to change it.
autoanalyze Species whether to automatically collect statistics on tables
without statistics when a plan is generated.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 24

Parameter Description
autoanalyze_ti
meout
Species the autoanalyze timeout period, in seconds. If the
duration of autoanalyze on a table exceeds the value of
autoanalyze_timeout, the autoanalyze operation is
automatically canceled. 0 indicates there is no timeout. The
unit is second.
cn:eective_cac
he_size
Species the size of the disk buer available to the CN
optimizer in a single query. The unit is 8 KB.
cn:enable_hotk
eys_collection
Species whether to collect statistics on accessed key values in
databases.
cn:track_stmt_s
ession_slot
Species the maximum number of full or slow SQL statements
that can be cached in a CN session.
datestyle Species the display format for date and time.
dn:eective_ca
che_size
Species the size of the disk buer available to the DN
optimizer in a single query. The unit is 8 KB.
dn:enable_hotk
eys_collection
Species whether to collect statistics on accessed key values in
databases.
dn:track_stmt_s
ession_slot
Species the maximum number of full or slow SQL statements
that can be cached in a DN session.
enable_seqscan Species whether to enable the optimizer's use of sequential
scan plan types. It is impossible to completely suppress
sequential scans, but setting this parameter to o allows the
optimizer to choose other methods if available.
enable_slot_log Species whether to enable primary/standby synchronization
for logical replication slots.
enable_stream
_operator
Species the query optimizer's use of streams. When this
parameter is set to o, a large number of logs indicating that
the stream plans cannot be pushed down are recorded.
failed_login_att
empts
Species the maximum number of incorrect password
attempts before an account is locked. The account will be
automatically unlocked after the time specied in
password_lock_time elapses. Only the sysadmin user can set
this parameter.
log_min_durati
on_statement
Causes the duration of each completed statement to be
logged if the statement ran for at least the specied number
of milliseconds. The value -1 disables logging statement
durations. If this parameter is set to a small value, the load
throughput may be aected.
max_replicatio
n_slots
Species the number of log replication slots in the primary
node.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 25

Parameter Description
max_wal_send
ers
The following processes occupy walsender threads: standby
DNs connect to primary DNs to obtain physical logs, and
logical replication tools connect to primary DNs to obtain
logical logs. This parameter species the maximum number of
walsender threads that can be created.
password_eec
t_time
Species the validity period of the password, in days.
password_lock_
time
Determines how many days an account is locked.
recovery_time_
target
Species the time for the standby node to write and replay
logs, in seconds.
session_timeou
t
Species how long to wait before a server connection is
disconnected due to inactivity, in seconds. The value 0
indicates there is no time limit.
timezone Species the time zone for displaying and interpreting time
stamps.
track_stmt_stat
_level
Controls the level of statement execution tracking.
update_lockwa
it_timeout
Species the maximum duration, in milliseconds, that a lock
waits for concurrent updates on a row to complete when the
concurrent update feature is enabled. If the lock wait time
exceeds this value, the system will report an error.
wal_level Species the level of information to be written to the WAL.
This is a required value and cannot be commented out.
Determines how much information is written to the WAL.
When this parameter is set to logical, logical logs are
extracted and primary key information is recorded in Xlogs.
cn:audit_thread
_num
Species the number of audit threads. Value range: 1 to 48.
dn:audit_threa
d_num
Species the number of audit threads. Value range: 1 to 48.
cn:qrw_inlist2jo
in_optmode
Determines whether to enable inlist-to-join query rewrite.
dn:qrw_inlist2j
oin_optmode
Determines whether to enable inlist-to-join query rewrite.
cn:audit_xid_inf
o
Determines whether to record the transaction IDs of SQL
statements in detail_info. 0: The transaction IDs are not
recorded. 1: The transaction IDs are recorded.
dn:audit_xid_in
fo
Determines whether to record the transaction IDs of SQL
statements in detail_info. 0: The transaction IDs are not
recorded. 1: The transaction IDs are recorded.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 26

Parameter Description
cn:default_limit
_rows
Limits the estimated number of rows for generating a generic
plan. If this parameter is set to a negative value, the negative
value is converted to a percentage, for example, -5 is
equivalent to 5%, indicating the 5% rows of the total rows are
returned.
dn:default_limi
t_rows
Limits the estimated number of rows for generating a generic
plan. If this parameter is set to a negative value, the negative
value is converted to a percentage, for example, -5 is
equivalent to 5%, indicating the 5% rows of the total rows are
returned.
cn:audit_dml_s
tate_select
Determines whether to audit the SELECT operation.
dn:audit_dml_s
tate_select
Determines whether to audit the SELECT operation.
cn:audit_dml_s
tate
Determines whether to enable the audit of INSERT, UPDATE,
and DELETE operations on a specic table. 0: These operations
are not audited. 1: These operations are audited.
dn:audit_dml_s
tate
Determines whether to enable the audit of INSERT, UPDATE,
and DELETE operations on a specic table. 0: These operations
are not audited. 1: These operations are audited.
cn:random_pag
e_cost
Species the estimated cost for the optimizer to fetch an out-
of-sequence disk page.
dn:random_pa
ge_cost
Species the estimated cost for the optimizer to fetch an out-
of-sequence disk page.
cn:enable_secu
rity_policy
Controls whether unied audit and dynamic data masking
policies are applied.
dn:enable_secu
rity_policy
Controls whether unied audit and dynamic data masking
policies are applied.
cn:audit_set_pa
rameter
Determines whether to audit the SET operation. 0: The SET
operation is not audited. 1: The SET operation is audited.
dn:audit_set_p
arameter
Determines whether to audit the SET operation. 0: The SET
operation is not audited. 1: The SET operation is audited.
cn:enable_pbe_
optimization
Controls whether the optimizer optimizes the query plan for
statements executed in Parse Bind Execute (PBE) mode.
dn:enable_pbe_
optimization
Controls whether the optimizer optimizes the query plan for
statements executed in Parse Bind Execute (PBE) mode.
wdr_snapshot_i
nterval
Species the interval (in minutes) at which the backend
thread Snapshot automatically performs snapshot operations
on the database monitoring data.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 27
Parameter Description
cn:enable_auto
_explain
Species whether to automatically print execution plans. This
parameter is used to locate slow stored procedures or slow
queries.
dn:enable_auto
_explain
Species whether to automatically print execution plans. This
parameter is used to locate slow stored procedures or slow
queries.
enable_wdr_sn
apshot
Species whether to enable WDR snapshots.
cn:max_concur
rent_autonomo
us_transactions
Species the maximum number of autonomous transaction
connections, that is, the maximum number of concurrent
autonomous transactions executed at the same time. If this
parameter is set to 0, autonomous transactions cannot be
executed.
dn:max_concur
rent_autonomo
us_transactions
Species the maximum number of autonomous transaction
connections, that is, the maximum number of concurrent
autonomous transactions executed at the same time. If this
parameter is set to 0, autonomous transactions cannot be
executed.
cn:max_standb
y_archive_delay
Species how long a standby server waits when the queries
that conict with WAL processing and archiving in hot standby
mode. The unit is ms.
dn:max_standb
y_archive_delay
Species how long a standby server waits when the queries
that conict with WAL processing and archiving in hot standby
mode. The unit is ms.
cn:max_standb
y_streaming_de
lay
Species how long a standby node waits before canceling
queries, in milliseconds.
dn:max_standb
y_streaming_de
lay
Species how long a standby node waits before canceling
queries, in milliseconds.
cn:recovery_ma
x_workers
Species the number of concurrent replay threads.
dn:recovery_m
ax_workers
Species the number of concurrent replay threads.
cn:auto_explai
n_log_min_dur
ation
Species how long execution plans are automatically printed
for. Plans can be printed only when the time required to
execute the plans is greater than the value of
auto_explain_log_min_duration. Unit: ms
dn:auto_explai
n_log_min_dur
ation
Species how long execution plans are automatically printed
for. Plans can be printed only when the time required to
execute the plans is greater than the value of
auto_explain_log_min_duration. Unit: ms.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 28

Parameter Description
cn:audit_functi
on_exec
Species whether to record the audit information during the
execution of the stored procedures, anonymous blocks, or
user-dened functions (excluding system functions).
dn:audit_functi
on_exec
Species whether to record the audit information during the
execution of the stored procedures, anonymous blocks, or
user-dened functions (excluding system functions).
cn:local_syscac
he_threshold
Species the size of system catalog cache in a session. Unit:
KB
dn:local_syscac
he_threshold
Species the size of system catalog cache in a session. Unit:
KB
cms:datastorag
e_threshold_val
ue_check
Species the disk usage threshold to put a database node into
read-only mode. If the disk usage of a data directory exceeds
this threshold, the database node is automatically changed to
read-only.
wdr_snapshot_
retention_days
Species how many days database monitoring snapshots are
saved for.
cn:enable_defa
ult_ustore_tabl
e
Determines whether to enable the Ustore storage engine by
default. The value on indicates all created tables are Ustore
tables.
dn:enable_defa
ult_ustore_tabl
e
Determines whether to enable the Ustore storage engine by
default. The value on indicates all created tables are Ustore
tables.
cn:undo_space_
limit_size
Species the undo forcible reclamation threshold. If 80% of
the specied parameter value is reached, forcible reclamation
is triggered. The unit is 8 KB. It is recommended that the value
be at least the value of undo_limit_size_per_transaction.
dn:undo_space
_limit_size
Species the undo forcible reclamation threshold. If 80% of
the specied parameter value is reached, forcible reclamation
is triggered. The unit is 8 KB. It is recommended that the value
be at least the value of undo_limit_size_per_transaction.
cn:undo_limit_s
ize_per_transac
tion
Species the maximum undo space for a single transaction.
The unit is 8 KB. If the undo space of a transaction exceeds
this parameter value, the transaction is rolled back due to an
error. It is recommended that this parameter value be smaller
than the value of undo_space_limit_size. If this parameter
value is larger, the value of undo_space_limit_size will be
used as the maximum undo space.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 29

Parameter Description
dn:undo_limit_
size_per_transa
ction
Species the maximum undo space for a single transaction.
The unit is 8 KB. If the undo space of a transaction exceeds
this parameter value, the transaction is rolled back due to an
error. It is recommended that this parameter value be smaller
than the value of undo_space_limit_size. If this parameter
value is larger, the value of undo_space_limit_size will be
used as the maximum undo space.
cn:enable_recy
clebin
Enables or disables the recycle bin in real time.
dn:enable_recy
clebin
Enables or disables the recycle bin in real time.
cn:recyclebin_r
etention_time
Species how long les will be kept in the recycle bin, in
seconds. Files in the recycle bin will be automatically deleted
after this length of time.
dn:recyclebin_r
etention_time
Species how long les will be kept in the recycle bin, in
seconds. Files in the recycle bin will be automatically deleted
after this length of time.
cn:undo_retenti
on_time
Species how long undo logs are kept, in seconds. This
parameter is only used for ashback query. Note: 1. The undo
space of the local disk increases. 2. In subsequent incremental
backups, the size of the backup set increases, because extra
undo content is retained.
dn:undo_retent
ion_time
Species how long undo logs are kept, in seconds. This
parameter is only used for ashback query. Note: 1. The undo
space of the local disk increases. 2. In subsequent incremental
backups, the size of the backup set increases, because extra
undo content is retained.
cn:cost_model_
version
Species the version of the optimizer cost model. It is a
protective parameter. It prevents new optimizer cost models
from being applied, so you can keep the current model
consistent with the plan of an existing version. If the value of
this parameter is changed, many SQL plans may be changed.
Exercise caution when modifying this parameter.
dn:cost_model_
version
Species the version of the optimizer cost model. It is a
protective parameter. It prevents new optimizer cost models
from being applied, so you can keep the current model
consistent with the plan of an existing version. If the value of
this parameter is changed, many SQL plans may be changed.
Exercise caution when modifying this parameter.
cn:enable_dyna
mic_samplesize
Species whether to dynamically adjust the number of
sampled rows. For a large table with more than one million
rows, the number of sampled rows is dynamically adjusted
during statistics collection to improve statistics accuracy.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 30

Parameter Description
dn:enable_dyn
amic_samplesiz
e
Species whether to dynamically adjust the number of
sampled rows. For a large table with more than one million
rows, the number of sampled rows is dynamically adjusted
during statistics collection to improve statistics accuracy.
cn:resilience_ct
rlslot_available
_maxpercent
Species the maximum percentage of threads in the thread
pool occupied by slow SQL statements. This parameter is only
suitable for SELECT statements executed by non-sysadmin/
monitoradmin users.
dn:resilience_ct
rlslot_available
_maxpercent
Species the maximum percentage of threads in the thread
pool occupied by slow SQL statements. This parameter is only
suitable for SELECT statements executed by non-sysadmin/
monitoradmin users.
cn:resilience_ct
rlstmt_control_
iopslimit
Species the maximum IOPS that can be used by slow SQL
statements after normal SQL statements are marked as slow
SQL statements. This parameter is only suitable for SELECT
statements executed by non-sysadmin/monitoradmin users.
0(None): The IOPS is not limited. 10(LOW): The limit level for
IOPS is LOW. 20(MEDIUM): The limit level for IOPS is
MEDIUM. 50(HIGH): The limit level for IOPS is HIGH.
dn:resilience_ct
rlstmt_control_
iopslimit
Species the maximum IOPS that can be used by slow SQL
statements after normal SQL statements are marked as slow
SQL statements. This parameter is only suitable for SELECT
statements executed by non-sysadmin/monitoradmin users.
0(None): The IOPS is not limited. 10(LOW): The limit level for
IOPS is LOW. 20(MEDIUM): The limit level for IOPS is
MEDIUM. 50(HIGH): The limit level for IOPS is HIGH.
dn:resilience_ct
rlstmt_detect_t
imelimit
Species the execution time of a normal SQL statement that
will be marked as a slow SQL statement. The value 0 indicates
that slow SQL statements are not identied. A value greater
than 0 indicates that a normal SQL statement whose
execution time exceeds the value of this parameter is marked
as a slow SQL statement. This parameter is only suitable for
SELECT statements executed by non-sysadmin/monitoradmin
users. Unit: ms
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 31

Table 6-8 Parameters for primary/standby instances
Parameter Description
audit_system_
object
Determines whether to audit the CREATE, DROP, and ALTER
operations on GaussDB Kernel database objects. GaussDB
Kernel database objects include databases, users, schemas, and
tables. You can change the parameter value to audit only the
operations on required database objects. During a forcible
primary/standby failover, set audit_system_object to the
maximum value and audit all DDL objects. If the parameter
value is incorrectly changed, DDL audit logs will be lost.
Contact technical support to change it.
autoanalyze Species whether to automatically collect statistics on tables
without statistics when a plan is generated.
autoanalyze_ti
meout
Species the autoanalyze timeout period, in seconds. If the
duration of autoanalyze on a table exceeds the value of
autoanalyze_timeout, the autoanalyze operation is
automatically canceled. 0 indicates there is no timeout. The
unit is second.
datestyle Species the display format for date and time.
dn:wal_keep_s
egments
Species the minimum number of transaction log les stored in
the pg_xlog directory. Standby nodes obtain the logs from the
primary node to perform streaming replication.
enable_seqsca
n
Species whether to enable the optimizer's use of sequential
scan plan types. It is impossible to completely suppress
sequential scans, but setting this parameter to o allows the
optimizer to choose other methods if available.
enable_slot_lo
g
Species whether to enable primary/standby synchronization
for logical replication slots.
failed_login_at
tempts
Species the maximum number of incorrect password attempts
before an account is locked. The account will be automatically
unlocked after the time specied in password_lock_time
elapses. Only the sysadmin user can set this parameter.
log_min_durat
ion_statement
Causes the duration of each completed statement to be logged
if the statement ran for at least the specied number of
milliseconds. The value -1 disables logging statement
durations. If this parameter is set to a small value, the load
throughput may be aected.
max_replicatio
n_slots
Species the number of log replication slots in the primary
node.
max_wal_send
ers
The following processes occupy walsender threads: standby
DNs connect to primary DNs to obtain physical logs, and
logical replication tools connect to primary DNs to obtain
logical logs. This parameter species the maximum number of
walsender threads that can be created.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 32

Parameter Description
password_ee
ct_time
Species the validity period of the password, in days.
password_lock
_time
Determines how many days an account is locked.
session_timeo
ut
Species how long to wait before a server connection is
disconnected due to inactivity, in seconds. The value 0 indicates
there is no time limit.
timezone Species the time zone for displaying and interpreting time
stamps.
update_lockw
ait_timeout
Species the maximum duration, in milliseconds, that a lock
waits for concurrent updates on a row to complete when the
concurrent update feature is enabled. If the lock wait time
exceeds this value, the system will report an error.
wal_level Species the level of information to be written to the WAL. This
is a required value and cannot be commented out. Determines
how much information is written to the WAL. When this
parameter is set to logical, logical logs are extracted and
primary key information is recorded in Xlogs.
dn:audit_threa
d_num
Species the number of audit threads. Value range: 1 to 48.
dn:qrw_inlist2j
oin_optmode
Determines whether to enable inlist-to-join query rewrite.
dn:audit_xid_i
nfo
Determines whether to record the transaction IDs of SQL
statements in detail_info. 0: The transaction IDs are not
recorded. 1: The transaction IDs are recorded.
dn:default_lim
it_rows
Limits the estimated number of rows for generating a generic
plan. If this parameter is set to a negative value, the negative
value is converted to a percentage, for example, -5 is
equivalent to 5%, indicating the 5% rows of the total rows are
returned.
dn:audit_dml_
state_select
Determines whether to audit the SELECT operation.
dn:audit_dml_
state
Determines whether to enable the audit of INSERT, UPDATE,
and DELETE operations on a specic table. 0: These operations
are not audited. 1: These operations are audited.
dn:random_pa
ge_cost
Species the estimated cost for the optimizer to fetch an out-
of-sequence disk page.
dn:enable_sec
urity_policy
Controls whether unied audit and dynamic data masking
policies are applied.
dn:audit_set_p
arameter
Determines whether to audit the SET operation. 0: The SET
operation is not audited. 1: The SET operation is audited.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 33

Parameter Description
dn:max_stand
by_streaming_
delay
Species how long a standby node waits before canceling
queries, in milliseconds.
dn:vacuum_de
fer_cleanup_a
ge
Species the number of transactions used by VACUUM.
dn:enable_pbe
_optimization
Controls whether the optimizer optimizes the query plan for
statements executed in Parse Bind Execute (PBE) mode.
wdr_snapshot
_interval
Species the interval (in minutes) at which the backend thread
Snapshot automatically performs snapshot operations on the
database monitoring data.
undo_retentio
n_time
Species how long undo logs are kept, in seconds. This
parameter is only used for ashback query. Note: 1. The undo
space of the local disk increases. 2. In subsequent incremental
backups, the size of the backup set increases, because extra
undo content is retained.
track_stmt_sta
t_level
Controls the level of statement execution tracking.
dn:enable_aut
o_explain
Species whether to automatically print execution plans. This
parameter is used to locate slow stored procedures or slow
queries.
enable_wdr_s
napshot
Species whether to enable WDR snapshots.
dn:max_concu
rrent_autono
mous_transact
ions
Species the maximum number of autonomous transaction
connections, that is, the maximum number of concurrent
autonomous transactions executed at the same time. If this
parameter is set to 0, autonomous transactions cannot be
executed.
dn:max_stand
by_archive_del
ay
Species how long a standby server waits when the queries
that conict with WAL processing and archiving in hot standby
mode. The unit is ms.
dn:max_stand
by_streaming_
delay
Species how long a standby node waits before canceling
queries, in milliseconds.
dn:recovery_m
ax_workers
Species the number of concurrent replay threads.
dn:auto_explai
n_log_min_dur
ation
Species how long execution plans are automatically printed
for. Plans can be printed only when the time required to
execute the plans is greater than the value of
auto_explain_log_min_duration. Unit: ms
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 34

Parameter Description
dn:recovery_ti
me_target
Species the time for the standby node to write and replay
logs. The unit is second.
dn:audit_funct
ion_exec
Species whether to record the audit information during the
execution of the stored procedures, anonymous blocks, or user-
dened functions (excluding system functions).
dn:local_sysca
che_threshold
Species the size of system catalog cache in a session. Unit: KB
cms:datastora
ge_threshold_
value_check
Species the disk usage threshold to put a database node into
read-only mode. If the disk usage of a data directory exceeds
this threshold, the database node is automatically changed to
read-only.
wdr_snapshot
_retention_da
ys
Species how many days database monitoring snapshots are
saved for.
dn:undo_spac
e_limit_size
Species the undo forcible reclamation threshold. If 80% of the
specied parameter value is reached, forcible reclamation is
triggered. The unit is 8 KB. It is recommended that the value be
at least the value of undo_limit_size_per_transaction.
dn:group_conc
at_max_len
Species the maximum permitted result length in bytes for the
GROUP_CONCAT() function.
dn:enable_ext
ension
Controls whether database extension plug-ins can be created.
The extension plug-in is a lab feature and is not recommended.
dn:cost_model
_version
Species the version of the optimizer cost model. It is a
protective parameter. It prevents new optimizer cost models
from being applied, so you can keep the current model
consistent with the plan of an existing version. If the value of
this parameter is changed, many SQL plans may be changed.
Exercise caution when modifying this parameter.
dn:immediate
_analyze_thres
hold
Species the threshold for triggering ANALYZE. When the
amount of inserted data is (Original data amount x This
parameter value) and the total number of rows exceeds 100,
ANALYZE is triggered.
dn:enable_dyn
amic_samplesi
ze
Species whether to dynamically adjust the number of sampled
rows. For a large table with more than one million rows, the
number of sampled rows is dynamically adjusted during
statistics collection to improve statistics accuracy.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 35

Parameter Description
dn:max_io_cap
acity
Species the maximum I/O per second for the backend write
process to ush pages in batches, in KB. Set this parameter
based on the service scenario and the disk I/O capability. If the
RTO is short or the data volume is many times that of the
shared memory and the service access data volume is random,
the value of this parameter cannot be too small. A small value
of max_io_capacity reduces the number of pages ushed by
the backend write process. If a large number of pages are
eliminated due to service triggering, the services are aected.
dn:max_conne
ctions
Species the maximum number of concurrent connections to
DNs.
log_autovacuu
m_min_durati
on
Species the interval which should elapse before autovacuum
operations are logged. Autovacuum operations equal to or
beyond the specied interval will be logged. If it is set to 0, all
autovacuum operations will be logged. If it is set to -1, no
autovacuum operations will be logged.
Congurable Parameters for Version 2.
X
The following table describes parameters that can be modied.
Table 6-9 Parameters for distributed instances
Parameter
Description
audit_system_o
bject
Determines whether to audit the CREATE, DROP, and ALTER
operations on GaussDB Kernel database objects. GaussDB
Kernel database objects include databases, users, schemas,
and tables. You can change the parameter value to audit only
the operations on required database objects. During a forcible
primary/standby failover, set audit_system_object to the
maximum value and audit all DDL objects. If the parameter
value is incorrectly changed, DDL audit logs will be lost.
Contact technical support to change it.
autoanalyze Species whether to automatically collect statistics on tables
without statistics when a plan is generated.
autoanalyze_ti
meout
Species the autoanalyze timeout period, in seconds. If the
duration of autoanalyze on a table exceeds the value of
autoanalyze_timeout, the autoanalyze operation is
automatically canceled. 0 indicates there is no timeout. The
unit is second.
cn:eective_cac
he_size
Species the size of the disk buer available to the CN
optimizer in a single query. The unit is 8 KB.
cn:enable_hotk
eys_collection
Species whether to collect statistics on accessed key values in
databases.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 36

Parameter Description
cn:track_stmt_s
ession_slot
Species the maximum number of full or slow SQL statements
that can be cached in a CN session.
datestyle Species the display format for date and time.
dn:eective_ca
che_size
Species the size of the disk buer available to the DN
optimizer in a single query. The unit is 8 KB.
dn:enable_hotk
eys_collection
Species whether to collect statistics on accessed key values in
databases.
dn:track_stmt_s
ession_slot
Species the maximum number of full or slow SQL statements
that can be cached in a DN session.
enable_seqscan Species whether to enable the optimizer's use of sequential
scan plan types. It is impossible to completely suppress
sequential scans, but setting this parameter to o allows the
optimizer to choose other methods if available.
enable_slot_log Species whether to enable primary/standby synchronization
for logical replication slots.
enable_stream
_operator
Species the query optimizer's use of streams. When this
parameter is set to o, a large number of logs indicating that
the stream plans cannot be pushed down are recorded.
failed_login_att
empts
Species the maximum number of incorrect password
attempts before an account is locked. The account will be
automatically unlocked after the time specied in
password_lock_time elapses. Only the sysadmin user can set
this parameter.
log_min_durati
on_statement
Causes the duration of each completed statement to be
logged if the statement ran for at least the specied number
of milliseconds. The value -1 disables logging statement
durations. If this parameter is set to a small value, the load
throughput may be aected.
max_replicatio
n_slots
Species the number of log replication slots in the primary
node.
max_wal_send
ers
The following processes occupy walsender threads: standby
DNs connect to primary DNs to obtain physical logs, and
logical replication tools connect to primary DNs to obtain
logical logs. This parameter species the maximum number of
walsender threads that can be created.
password_eec
t_time
Species the validity period of the password, in days.
password_lock_
time
Determines how many days an account is locked.
recovery_time_
target
Species the time for the standby node to write and replay
logs, in seconds.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 37

Parameter Description
session_timeou
t
Species how long to wait before a server connection is
disconnected due to inactivity, in seconds. The value 0
indicates there is no time limit.
timezone Species the time zone for displaying and interpreting time
stamps.
track_stmt_stat
_level
Controls the level of statement execution tracking.
update_lockwa
it_timeout
Species the maximum duration, in milliseconds, that a lock
waits for concurrent updates on a row to complete when the
concurrent update feature is enabled. If the lock wait time
exceeds this value, the system will report an error.
wal_level Species the level of information to be written to the WAL.
This is a required value and cannot be commented out.
Determines how much information is written to the WAL.
When this parameter is set to logical, logical logs are
extracted and primary key information is recorded in Xlogs.
cn:audit_thread
_num
Species the number of audit threads. Value range: 1 to 48.
dn:audit_threa
d_num
Species the number of audit threads. Value range: 1 to 48.
cn:qrw_inlist2jo
in_optmode
Determines whether to enable inlist-to-join query rewrite.
dn:qrw_inlist2j
oin_optmode
Determines whether to enable inlist-to-join query rewrite.
cn:audit_xid_inf
o
Determines whether to record the transaction IDs of SQL
statements in detail_info. 0: The transaction IDs are not
recorded. 1: The transaction IDs are recorded.
dn:audit_xid_in
fo
Determines whether to record the transaction IDs of SQL
statements in detail_info. 0: The transaction IDs are not
recorded. 1: The transaction IDs are recorded.
cn:default_limit
_rows
Limits the estimated number of rows for generating a generic
plan. If this parameter is set to a negative value, the negative
value is converted to a percentage, for example, -5 is
equivalent to 5%, indicating the 5% rows of the total rows are
returned.
dn:default_limi
t_rows
Limits the estimated number of rows for generating a generic
plan. If this parameter is set to a negative value, the negative
value is converted to a percentage, for example, -5 is
equivalent to 5%, indicating the 5% rows of the total rows are
returned.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 38

Parameter Description
cn:audit_dml_s
tate_select
Determines whether to audit the SELECT operation.
dn:audit_dml_s
tate_select
Determines whether to audit the SELECT operation.
cn:audit_dml_s
tate
Determines whether to enable the audit of INSERT, UPDATE,
and DELETE operations on a specic table. 0: These operations
are not audited. 1: These operations are audited.
dn:audit_dml_s
tate
Determines whether to enable the audit of INSERT, UPDATE,
and DELETE operations on a specic table. 0: These operations
are not audited. 1: These operations are audited.
cn:random_pag
e_cost
Species the estimated cost for the optimizer to fetch an out-
of-sequence disk page.
dn:random_pa
ge_cost
Species the estimated cost for the optimizer to fetch an out-
of-sequence disk page.
cn:enable_secu
rity_policy
Controls whether unied audit and dynamic data masking
policies are applied.
dn:enable_secu
rity_policy
Controls whether unied audit and dynamic data masking
policies are applied.
cn:audit_set_pa
rameter
Determines whether to audit the SET operation. 0: The SET
operation is not audited. 1: The SET operation is audited.
dn:audit_set_p
arameter
Determines whether to audit the SET operation. 0: The SET
operation is not audited. 1: The SET operation is audited.
cn:enable_pbe_
optimization
Controls whether the optimizer optimizes the query plan for
statements executed in Parse Bind Execute (PBE) mode.
dn:enable_pbe_
optimization
Controls whether the optimizer optimizes the query plan for
statements executed in Parse Bind Execute (PBE) mode.
wdr_snapshot_i
nterval
Species the interval (in minutes) at which the backend
thread Snapshot automatically performs snapshot operations
on the database monitoring data.
enable_wdr_sn
apshot
Species whether to enable WDR snapshots.
cn:max_standb
y_archive_delay
Species how long a standby server waits when the queries
that conict with WAL processing and archiving in hot standby
mode. The unit is ms.
dn:max_standb
y_archive_delay
Species how long a standby server waits when the queries
that conict with WAL processing and archiving in hot standby
mode. The unit is ms.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 39
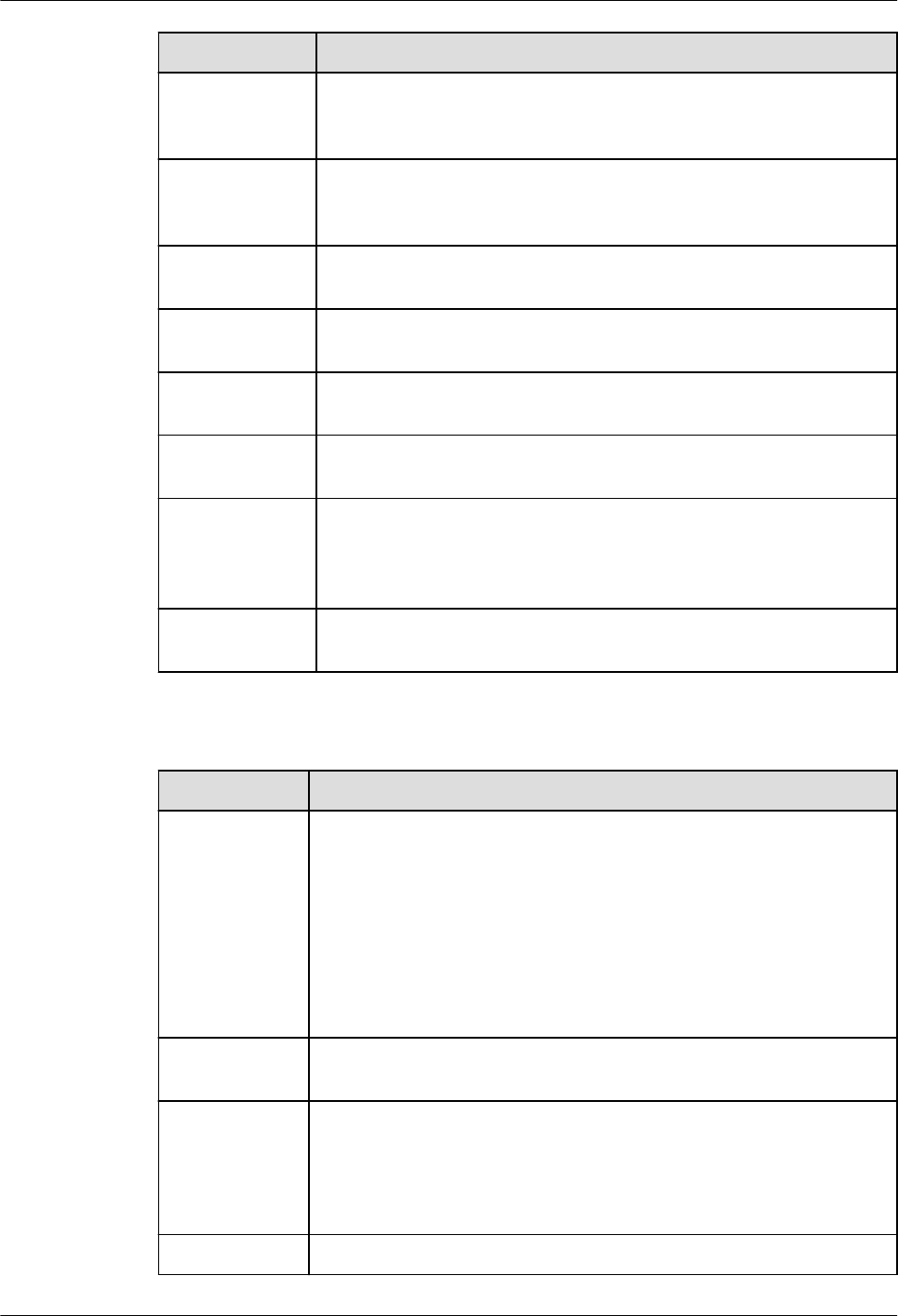
Parameter Description
cn:max_standb
y_streaming_de
lay
Species how long a standby node waits before canceling
queries, in milliseconds.
dn:max_standb
y_streaming_de
lay
Species how long a standby node waits before canceling
queries, in milliseconds.
cn:recovery_ma
x_workers
Species the number of concurrent replay threads.
dn:recovery_m
ax_workers
Species the number of concurrent replay threads.
cn:local_syscac
he_threshold
Species the size of system catalog cache in a session. Unit:
KB
dn:local_syscac
he_threshold
Species the size of system catalog cache in a session. Unit:
KB
cms:datastorag
e_threshold_val
ue_check
Species the disk usage threshold to put a database node into
read-only mode. If the disk usage of a data directory exceeds
this threshold, the database node is automatically changed to
read-only.
wdr_snapshot_
retention_days
Species how many days database monitoring snapshots are
saved for.
Table 6-10 Parameters for primary/standby instances
Parameter
Description
audit_system_
object
Determines whether to audit the CREATE, DROP, and ALTER
operations on GaussDB Kernel database objects. GaussDB
Kernel database objects include databases, users, schemas, and
tables. You can change the parameter value to audit only the
operations on required database objects. During a forcible
primary/standby failover, set audit_system_object to the
maximum value and audit all DDL objects. If the parameter
value is incorrectly changed, DDL audit logs will be lost.
Contact technical support to change it.
autoanalyze Species whether to automatically collect statistics on tables
without statistics when a plan is generated.
autoanalyze_ti
meout
Species the autoanalyze timeout period, in seconds. If the
duration of autoanalyze on a table exceeds the value of
autoanalyze_timeout, the autoanalyze operation is
automatically canceled. 0 indicates there is no timeout. The
unit is second.
datestyle Species the display format for date and time.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 40

Parameter Description
dn:wal_keep_s
egments
Species the minimum number of transaction log les stored in
the pg_xlog directory. Standby nodes obtain the logs from the
primary node to perform streaming replication.
enable_seqsca
n
Species whether to enable the optimizer's use of sequential
scan plan types. It is impossible to completely suppress
sequential scans, but setting this parameter to o allows the
optimizer to choose other methods if available.
enable_slot_lo
g
Species whether to enable primary/standby synchronization
for logical replication slots.
failed_login_at
tempts
Species the maximum number of incorrect password attempts
before an account is locked. The account will be automatically
unlocked after the time specied in password_lock_time
elapses. Only the sysadmin user can set this parameter.
log_min_durat
ion_statement
Causes the duration of each completed statement to be logged
if the statement ran for at least the specied number of
milliseconds. The value -1 disables logging statement
durations. If this parameter is set to a small value, the load
throughput may be aected.
max_replicatio
n_slots
Species the number of log replication slots in the primary
node.
max_wal_send
ers
The following processes occupy walsender threads: standby
DNs connect to primary DNs to obtain physical logs, and
logical replication tools connect to primary DNs to obtain
logical logs. This parameter species the maximum number of
walsender threads that can be created.
password_ee
ct_time
Species the validity period of the password, in days.
password_lock
_time
Determines how many days an account is locked.
session_timeo
ut
Species how long to wait before a server connection is
disconnected due to inactivity, in seconds. The value 0 indicates
there is no time limit.
timezone Species the time zone for displaying and interpreting time
stamps.
update_lockw
ait_timeout
Species the maximum duration, in milliseconds, that a lock
waits for concurrent updates on a row to complete when the
concurrent update feature is enabled. If the lock wait time
exceeds this value, the system will report an error.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 41

Parameter Description
wal_level Species the level of information to be written to the WAL. This
is a required value and cannot be commented out. Determines
how much information is written to the WAL. When this
parameter is set to logical, logical logs are extracted and
primary key information is recorded in Xlogs.
dn:audit_threa
d_num
Species the number of audit threads. Value range: 1 to 48.
dn:qrw_inlist2j
oin_optmode
Determines whether to enable inlist-to-join query rewrite.
dn:audit_xid_i
nfo
Determines whether to record the transaction IDs of SQL
statements in detail_info. 0: The transaction IDs are not
recorded. 1: The transaction IDs are recorded.
dn:default_lim
it_rows
Limits the estimated number of rows for generating a generic
plan. If this parameter is set to a negative value, the negative
value is converted to a percentage, for example, -5 is
equivalent to 5%, indicating the 5% rows of the total rows are
returned.
dn:audit_dml_
state_select
Determines whether to audit the SELECT operation.
dn:audit_dml_
state
Determines whether to enable the audit of INSERT, UPDATE,
and DELETE operations on a specic table. 0: These operations
are not audited. 1: These operations are audited.
dn:random_pa
ge_cost
Species the estimated cost for the optimizer to fetch an out-
of-sequence disk page.
dn:enable_sec
urity_policy
Controls whether unied audit and dynamic data masking
policies are applied.
dn:audit_set_p
arameter
Determines whether to audit the SET operation. 0: The SET
operation is not audited. 1: The SET operation is audited.
dn:max_stand
by_streaming_
delay
Species how long a standby node waits before canceling
queries, in milliseconds.
dn:vacuum_de
fer_cleanup_a
ge
Species the number of transactions used by VACUUM.
dn:enable_pbe
_optimization
Controls whether the optimizer optimizes the query plan for
statements executed in Parse Bind Execute (PBE) mode.
wdr_snapshot
_interval
Species the interval (in minutes) at which the backend thread
Snapshot automatically performs snapshot operations on the
database monitoring data.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 42

Parameter Description
undo_retentio
n_time
Species how long undo logs are kept, in seconds. This
parameter is only used for ashback query. Note: 1. The undo
space of the local disk increases. 2. In subsequent incremental
backups, the size of the backup set increases, because extra
undo content is retained.
track_stmt_sta
t_level
Controls the level of statement execution tracking.
enable_wdr_s
napshot
Species whether to enable WDR snapshots.
dn:max_stand
by_archive_del
ay
Species how long a standby server waits when the queries
that conict with WAL processing and archiving in hot standby
mode. The unit is ms.
dn:max_stand
by_streaming_
delay
Species how long a standby node waits before canceling
queries, in milliseconds.
dn:recovery_m
ax_workers
Species the number of concurrent replay threads.
dn:recovery_ti
me_target
Species the time for the standby node to write and replay
logs. The unit is second.
dn:local_sysca
che_threshold
Species the size of system catalog cache in a session. Unit: KB
cms:datastora
ge_threshold_
value_check
Species the disk usage threshold to put a database node into
read-only mode. If the disk usage of a data directory exceeds
this threshold, the database node is automatically changed to
read-only.
wdr_snapshot
_retention_da
ys
Species how many days database monitoring snapshots are
saved for.
log_autovacuu
m_min_durati
on
Species the interval which should elapse before autovacuum
operations are logged. Autovacuum operations equal to or
beyond the specied interval will be logged. If it is set to 0, all
autovacuum operations will be logged. If it is set to -1, no
autovacuum operations will be logged.
6.7 System Accounts for DB Instances
To provide O&M services, the system automatically creates system accounts when
you create GaussDB instances. These accounts cannot be used by users.
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 43

NO TICE
Attempting to delete, rename, change passwords for, or change privileges for
these accounts will result in an error.
Table 6-11 System accounts
Account Default
Password
Login Permission Description Password
Validity
rdsAdmin Randomly
assigned by
the system
Database
account, which
cannot be used
for login
GaussDB
administrator
account
Permanent
rdsBackup Randomly
assigned by
the system
Database
account, which
cannot be used
for login
Account used
for instance
database
backup
Permanent
rdsRepl Randomly
assigned by
the system
Database
account, which
cannot be used
for login
Account used
to synchronize
data between
primary and
standby nodes
Permanent
root Manually
congured
when a user
buys an
instance
Remote SSH login System
administrator
account
Permanent
rdsMetric Randomly
assigned by
the system
Database
account, which
cannot be used
for login
Account used
to obtain
GaussDB
performance
metrics and
report them to
Cloud Eye for
the tenant to
view the status
of GaussDB.
Permanent
GaussDB
Service Overview 6 DB Instance Description
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 44

7 Compatibility with Oracle
7.1 Distributed Instances
7.1.1 Oracle Compatibility Overview
This chapter compares the Oracle compatibility mode in GaussDB with Oracle
Database 19c. For details about related information and specications, see the
corresponding sections in
Developer Guide
.
GaussDB is compatible with Oracle in terms of data types, SQL functions,
database objects, and PL/SQL in most cases. The underlying framework
implementation of GaussDB is dierent from that of Oracle. Therefore, there are
still some dierences between GaussDB and Oracle. The following lists the
compatibility between GaussDB and Oracle.
7.1.2 Basic SQL Elements
GaussDB is compatible with basic SQL elements, but some of them are dierent.
For details, see the following tables.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 45

7.1.2.1 Data Types
Table 7-1 Numeric types
No. Oracle GaussDB Dierence
1 NUMBER [ ( p [ ,
s ] ) ]
Supported, with
dierences.
The precision and usage are
dierent.
● When NUMBER contains
parameters, the
maximum boundary
values of precision and
scale in GaussDB are
greater than those in
Oracle.
● When NUMBER does not
contain parameters, the
default value of precision
in GaussDB is much
greater than the
maximum boundary value
when NUMBER contains
parameters. In Oracle, the
default value of precision
is equal to the maximum
boundary value when
NUMBER contains
parameters.
● GaussDB does not
support negative scale
values. In Oracle, a
negative scale value is
accurate to the
corresponding integer.
2
FLOAT [ ( p ) ] Supported. -
3 BINARY_FLOAT Not supported. -
4 BINARY_DOUBLE Supported. -
Table 7-2 Date and time types
No.
Oracle GaussDB Dierence
1 DATE Supported, with
dierences.
The precision is
dierent.
GaussDB supports
a larger time
range than
Oracle.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 46

No. Oracle GaussDB Dierence
2 TIMESTAMP
[ ( fractional_seconds_precisio
n ) ]
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 47

No. Oracle GaussDB Dierence
3 TIMESTAMP
[ ( fractional_seconds_precisio
n ) ] WITH TIME ZONE
Supported, with
dierences.
The timestamptz
of GaussDB is
equivalent to the
timestampwithloa
cltimezone of
Oracle. The type
corresponding to
timestamptz of
Oracle is missing.
Time zone
update: In some
countries or
regions, time zone
information is
frequently
updated due to
political,
economic, war, or
other factors.
Therefore, the
database system
often needs to
modify the time
zone le to
ensure that the
time is correct.
Currently, the
GaussDB time
zone type involves
only timestamp
with timezone.
When a new time
zone le takes
eect, the existing
data is not
changed, and the
new data is
adjusted based on
the time zone le
information. The
capability of
processing the
same type of data
in the database is
dierent from
that in the Oracle
database.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 48
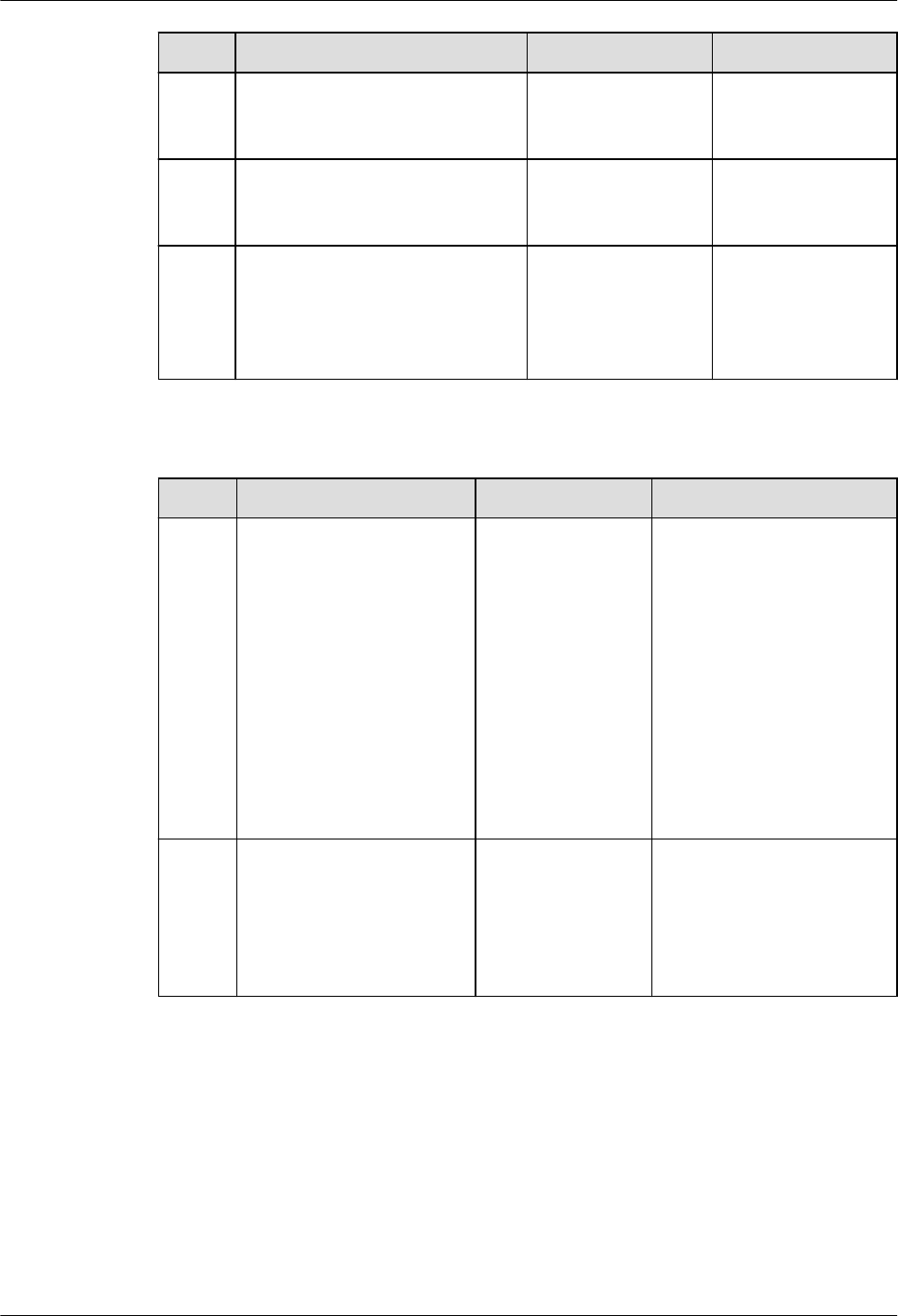
No. Oracle GaussDB Dierence
4 TIMESTAMP
[ ( fractional_seconds_precisio
n ) ] WITH LOCAL TIME ZONE
Not supported. -
5 INTERVAL YEAR
[ ( year_precision ) ] TO
MONTH
Supported. -
6 INTERVAL DAY
[ ( day_precision ) ] TO
SECOND
[ ( fractional_seconds_precisio
n ) ]
Supported. -
Table 7-3 Character types
No. Oracle GaussDB Dierence
1 VARCHAR2 ( size [ BYTE
| CHAR ] )
Supported, with
dierences.
In GaussDB, the unit of
size is byte. That is, only
BYTE is supported. You
cannot select a value
between BYTE and
CHAR. The maximum
size is 10 MB. In Oracle,
however, the unit of size
can be selected between
BYTE and CHAR. The
maximum size depends
on the character set in
use.
2 NVARCHAR2 ( size ) Supported, with
dierences.
In GaussDB,
NVARCHAR2(n) is the
alias of VARCHAR2(n). In
Oracle, NVARCHAR2(n)
is dierent from
VARCHAR2(n).
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 49

No. Oracle GaussDB Dierence
3 CHAR [ ( size [ BYTE |
CHAR ] ) ]
Supported, with
dierences.
In GaussDB, the unit of
size is byte. That is, only
BYTE is supported. You
cannot select a value
between BYTE and
CHAR. The maximum
size is 10 MB. In Oracle,
however, the unit of size
can be selected between
BYTE and CHAR. The
maximum size is 2000
bytes. The actual
number of characters
that can be contained
depends on the
character set in use.
4 NCHAR [ ( size ) ] Supported, with
dierences.
In GaussDB, the unit of
size is byte, and the
maximum size is 10 MB.
In Oracle, however, the
unit of size is character,
and the maximum size
depends on the
character set in use.
5 CLOB Supported, with
dierences.
The locator concept is
not supported.
6 NCLOB Not supported. -
7 LONG Not supported. -
Table 7-4 Binary types
No.
Oracle GaussDB Dierence
1 RAW ( size ) Supported, with
dierences.
In GaussDB, size
indicates the
recommended byte
length and is not used
to verify the byte
length of the input
raw type.
2 LONG RAW Not supported. -
3 BLOB Supported. -
4 BFILE Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 50

Table 7-5 ROWID types
No. Oracle GaussDB
1 ROWID Not supported.
2 UROWID Not supported.
Table 7-6 User-dened types
No. Oracle GaussDB
1 Object types Not supported.
2 REF data types Not supported.
3 Variable arrays Supported.
4 Nested tables Supported.
Table 7-7 Pseudo-types
No.
Oracle GaussDB
1 anytype Not supported.
2 anydata Not supported.
3 anydataset Not supported.
Table 7-8 XML types
No.
Oracle GaussDB Dierence
1 XMLTYPE Supported, with
dierences.
GaussDB does not support
some operations. For
example, the
XMLELEMENT function is
used to convert a character
string to the XML type
instead of the XMLType
type. For details, see "SQL
Reference > Data Type >
XMLTYPE" in
Developer
Guide
.
2 URIType Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 51

Table 7-9 Spatial types
No. Oracle GaussDB
1 SDO_GEOMETRY Not supported.
2 SDO_TOPO_GEOMETRY Not supported.
3 SDO_GEORASTER Not supported.
Table 7-10 Lock modes
Level Oracle GaussDB Remarks
- - NULL NULL of GaussDB indicates
that no lock is assigned, which
corresponds to the level-0 lock
of Oracle.
0 none INVALID INVALID of GaussDB indicates
that an invalid lock is assigned.
An invalid lock is assigned only
when a lock that cannot be
identied by GaussDB occurs
during system running.
1 null AccessShare -
2 RS RowShare -
3 RX RowExclusive -
4 S ShareUpdateExclu-
sive
-
5 SRX Share -
6 \ ShareRowExclusive -
7 X Exclusive -
8 \ AccessExclusive -
7.1.2.2 Data Type Comparison Rules
Data type comparison (collation) rules are followed when values of the same data
type are compared (collated).
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 52

Table 7-11 Comparison rules
No
.
Oracle Gauss
DB
Dierence Rule
Description
1 Numeric values Suppor
ted.
- For
comparison
based on
numeric
values, a
number close
to the
positive
direction of a
number axis
is greater
than a
number close
to the
negative
direction of
the number
axis, for
example, 5 >
3, 1 > –1, and
–1 > –2.
2 Datetime values Suppor
ted.
- For
comparison
based on
datetime
values, the
later date or
timestamp is
greater than
the earlier
date or
timestamp,
for example,
'2000-01-01
12:00:00' >
'2000-01-01
11:59:59'.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 53

No
.
Oracle Gauss
DB
Dierence Rule
Description
3 Binary values Suppor
ted.
- For
comparison
based on
binary values,
a number
close to the
positive
direction of a
number axis
is greater
than a
number close
to the
negative
direction of
the number
axis, for
example,
1001 0101 >
1001 0011.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 54

No
.
Oracle Gauss
DB
Dierence Rule
Description
4 Character values Suppor
ted,
with
diere
nces.
● The following contents
are dierent:
– GaussDB and
Oracle support
dierent
comparison rules,
and the names of
the same
comparison rules
may be dierent.
– GaussDB and
Oracle dier in
specifying
comparison rules.
For example, table-
level comparison
rules cannot be
specied in
GaussDB, but can
be specied in
Oracle.
– GaussDB and
Oracle dier in the
syntax for
specifying
comparison rules.
For example, in
GaussDB, the
ENCODING,
LC_CTYPE, and
LC_COLLATE
parameters are
used to specify the
character set,
character type, and
comparison rules
used during
database creation.
For details, see
"SQL Reference >
SQL Syntax > C >
CREATE
DATABASE" in
Developer Guide
. In
Oracle, comparison
rules at dierent
levels are usually
specied by a series
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 55

No
.
Oracle Gauss
DB
Dierence Rule
Description
of parameters with
the NLS prex.
● The following contents
are the same:
– In GaussDB and
Oracle, character
strings are
compared character
by character
starting from the
rst character. If
the rst character is
the same, the next
character is
compared until
dierent characters
appear or a
character string
ends. If all
characters of two
strings are the
same, they are
considered equal.
Otherwise, the size
relationship of the
rst found dierent
characters is used
for comparison. In
addition, for some
data types, such as
CHAR, spaces are
added to the
shorter string until
two strings have
the same length,
and then the
strings are collated.
– For single-character
comparison,
common
comparison rules
include binary
collation based on
the character set
and monolingual
collation. If the
default character
set and comparison
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 56

No
.
Oracle Gauss
DB
Dierence Rule
Description
rules are used, both
GaussDB and
Oracle use
monolingual
collation.
– In GaussDB and
Oracle, the
comparison rules of
character types are
closely related to
character sets. For
example, most
non-Unicode
character sets do
not support
monolingual
collation. Therefore,
binary collation is
used by default.
5 Object values Not
suppor
ted.
- -
6 Varrays and nested
tables
Suppor
ted,
with
diere
nces.
Both GaussDB and Oracle
support the comparison
of varrays. Dierent from
Oracle, GaussDB not only
supports the comparison
of the number of
elements in two varrays,
but also supports the
comparison between
varrays of the same type.
-
7 Data type
precedence
Suppor
ted.
- -
8 Explicit/Implicit data
conversion
Suppor
ted.
- -
7.1.2.3 Literals
Table 7-12 Literals
No.
Oracle GaussDB
1 Text literals Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 57

No. Oracle GaussDB
2 Numeric literals Supported.
3 Datetime literals Supported.
4 Interval literals Supported.
7.1.2.4 Format Models
Table 7-13 Formats
No. Oracle GaussDB Dierence
1 Number formats Supported,
with
dierences.
GaussDB supports the $, C, TM,
TM9, TME, and U formats only
when a_format_version is set to
10c and a_format_dev_version is
set to s1. In addition, this
parameter does not support the
TH, PL, or SG format.
For details about GaussDB, see
the fmt parameter of the
number type table in "SQL
Reference > Functions and
Operators > Type Conversion
Functions" in
Developer Guide
.
2 Datetime formats Supported,
with
dierences.
GaussDB: Parameters used for
time truncation and rounding are
valid only when
a_format_version is set to 10c
and a_format_dev_version is set
to s1.
For details about GaussDB
support, see formats for
formatting date and time in "SQL
References > Functions and
Operators > Date and Time
Processing Functions and
Operators" in
Developer Guide
.
3 Format model
modiers
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 58

No. Oracle GaussDB Dierence
4 String-to-date
conversion rules
Supported,
with
dierences.
GaussDB: The to_timestamp_tz
function is valid only when
a_format_version is set to 10c
and a_format_dev_version is set
to s1.
For details about GaussDB, see
to_date, to_timestamp, and
to_timestamp_tz in "SQL
Reference > Functions and
Operators > Type Conversion
Functions" in
Developer Guide
.
5 XML format
models
Not
supported.
-
7.1.2.5 Nulls
Table 7-14 Nulls
No.
Oracle GaussDB
1 IS NULL and IS NOT NULL Supported.
2 NULLS in conditions Supported.
7.1.2.6 Comments
Table 7-15 Comments
No.
Oracle GaussDB Dierence
1 A slash and
an asterisk
(/*)
Supported. -
2 Two hyphens
(--)
Supported. -
3 COMMENT
command
Supported. -
4 HINT Supported, with
dierences.
GaussDB does not support the
'--+' hint format.
For details, see "SQL Tuning
Guide > Tuning Using Plan
Hints" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 59

7.1.2.7 Database Objects
Table 7-16 Schema objects
No. Oracle GaussDB Dierence
1 Analytic views Not
supported.
-
2 Attribute
dimensions
Not
supported.
-
3 Clusters Supported. -
4 Constraints Supported. -
5 Database links Supported. -
6 Database
triggers
Supported. -
7 Dimensions Supported. -
8 External
procedure
libraries
Not
supported.
-
9 Hierarchies Not
supported.
-
10 Index-organized
tables
Not
supported.
-
11 Indexes Supported. -
12 Index types Not
supported.
-
13 Java classes Not
supported.
-
14 Java resources Not
supported.
-
15 Java source code Not
supported.
-
16 Join groups Not
supported.
-
17 Materialized
views
Supported. -
18 Materialized
view logs
Not
supported.
-
19 Mining models Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 60

No. Oracle GaussDB Dierence
20 Object tables Not
supported.
-
21 Object types Not
supported.
-
22 Object views Not
supported.
-
23 Operators Supported. -
24 Packages Supported. -
25 Sequences Supported. -
26 Storage
functions
Supported. -
27 Stored
procedures
Supported. -
28 Synonyms Supported,
with
dierences.
The names of Oracle objects in the
same namespace must be unique. In
GaussDB, the name of a synonym can
be the same as that of a table, view,
function, or package in the same
namespace. In this case, GaussDB
preferentially accesses the object with
the original name. If the object with
the original name is not found,
GaussDB searches for the object to
which the synonym points. PUBLIC
synonyms are searched only when the
schema name is a username.
29 Tables Supported. -
30 Views Supported. -
31 Zone map Not
supported.
-
Table 7-17 Nonschema objects
No.
Oracle GaussDB
1 Contexts Not supported.
2 Directories Supported.
3 Editions Not supported.
4 Flashback archives Not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 61

No. Oracle GaussDB
5 Lockdown proles Not supported.
6 Proles Not supported.
7 Restore points Supported.
8 Roles Supported.
9 Rollback segments ● Ustore supports rollback
segments.
● Astore does not support
rollback segments.
10 Tablespaces Supported.
11 Tablespace sets Not supported.
12 Unied audit policies Supported.
13 Users Supported.
7.1.2.8 Database Object Names and Qualiers
Table 7-18 Naming rules
No.
Oracle GaussDB Dierence
1 Database object naming rules Supported,
with
dierences.
GaussDB uses
lowercase letters
by default.
2 Schema object naming rules Supported. -
7.1.2.9 Syntax for Schema Objects and Parts in SQL Statements
Table 7-19 Object reference
No.
Oracle GaussDB
1 General syntax for referring to an
object
Supported.
2 Resolving a reference to an object Supported.
3 Referring to objects in other
schemas
Supported.
4 Referring to objects in remote
databases
Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 62

No. Oracle GaussDB
5 Referring to partitions and
subpartitions of tables and indexes
Supported.
7.1.3 Pseudocolumns
GaussDB is compatible with sequence and rownum pseudocolumns. Other
pseudocolumns are not supported.
Sequence Pseudocolumns
Table 7-20 Sequences
No. Oracle GaussDB Dierence
1 currval Supported, with
dierences.
It is implemented as a
function in GaussDB.
The call mode is
compatible with
Oracle.
2 nextval Supported, with
dierences.
It is implemented as a
function in GaussDB.
The call mode is
compatible with
Oracle.
ROWNUM Pseudocolumn
Table 7-21 rownum
No.
Oracle GaussDB Dierence
1 rownum Supported, with
dierences.
When Oracle uses
rownum in the left, right,
and full join conditions
for ltering, the
performance varies
according to the
conditions. The rownum
condition may be ignored
or partially ignored.
However, GaussDB lters
the results after left,
right, and full join.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 63

XMLDATA Pseudocolumn
Table 7-22 xmldata
No. Oracle GaussDB
1 xmldata Not supported
7.1.4 Operators
GaussDB is compatible with operators except hierarchical query.
SQL Operators
Table 7-23 SQL operators
No. Oracle GaussDB
1 Unary and binary operators Supported
2 Operator precedence Supported
Arithmetic Operators
Table 7-24 Arithmetic operators
No.
Oracle GaussDB
1 Unary operators: positive (+) and
negative (–).
Supported
2 Binary operators: addition (+) and
subtraction (–).
Supported
3 Binary operators: multiplication (*)
and division (/).
Supported
COLLATE Operator
Table 7-25 COLLATE operator
No.
Oracle GaussDB
1 COLLATE collation_name Supported
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 64

Connection Operators
Table 7-26 Connection operators
No. Oracle GaussDB
1 || Supported
Set Operators
Table 7-27 Set operators
No. Oracle GaussDB
1 union Supported
2 union all Supported
3 intersect Supported
4 minus Supported
Multiset Operators
Table 7-28 Multiset operators
No.
Oracle GaussDB
1 multiset except Supported
2 multiset intersect Supported
3 multiset union Supported
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 65

User-dened Operators
Table 7-29 User-dened operators
No. Oracle GaussDB Dierence
1 CREATE
OPERATOR
Supported. ● Oracle provides
CONTEXT_CLAUSE to
dene functional
evaluation functions,
which is dierent from
GaussDB that constrains
selectivity evaluation
functions. GaussDB does
not support user-dened
functional evaluation
functions.
● Optional parameters in
GaussDB dier greatly
from those in Oracle. For
details, see the GaussDB
parameter description in
"SQL Reference > SQL
Syntax > C > CREATE
OPERATOR" in
Developer
Guide
.
Comparison Operators
No.
Oracle GaussDB
1 < = Supported.
2 < > Supported.
3 > = Supported.
4 ^ = Supported.
5 ! = Not supported. For !=,
if there is a space
between an
exclamation mark (!)
and an equal sign (=),
the exclamation mark
will be identied as
factorial.
For comparison operators <=, <>, >=, and ^=, if there is a space between two
symbols, it does not aect normal operations. For !=, if there is a space between
an exclamation mark (!) and an equal sign (=), the exclamation mark will be
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 66

identied as factorial, which may cause the result to be inconsistent with the
expected result.
7.1.5 Expressions
GaussDB is compatible with most database expressions.
Table 7-30 Expressions
No. Oracle GaussDB Dierence
1 Simple
expressions
Supported. -
2 Analytic view
expressions
Not
supported.
-
3 Compound
expressions
Supported. -
4 CASE
expressions
Supported. -
5 Column
expressions
Supported. -
6 CURSOR
expressions
Not
supported.
-
7 Datetime
expressions
Supported,
with
dierences.
GaussDB command output does not
contain time zone information, but
Oracle contains time zone information
similar to "PM AMERICA/
LOS_ANGELES."
8 Function
expressions
Supported. -
9 Interval
expressions
Partially
supported.
GaussDB supports statements in the
format of "SELECT INTERVAL
'999999999 23:59:59.999' day(9) to
second FROM DUAL;" but does not
support statements in the format of
"SELECT(SYSDATE-SYSDATE) DAY TO
SECOND FROM DUAL;". They are
supported in Oracle.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 67

No. Oracle GaussDB Dierence
10 JSON object
access
expressions
Partially
supported,
with
dierences.
● GaussDB can extract values from
JSON objects in "->'key'" mode,
while Oracle can extract values in
".key" mode.
● For JSONARRY objects, Oracle can
extract values corresponding to all
keys at a time in ".key" mode.
However, GaussDB does not
support this function.
11 Model
expressions
Not
supported.
-
12 Object
expressions
Not
supported.
-
13 Placeholder
expressions
Partially
supported.
GaussDB supports general placeholder
expressions such as ":var", but does
not support the combination of two
general placeholder expressions using
the INDICATOR keyword.
14 Scalar
subquery
expressions
Supported. -
15 Type
constructor
expressions
Partially
supported.
GaussDB cannot specify the NEW
keyword before the type constructor,
but Oracle can.
16 Expression
lists
Supported. -
7.1.6 Conditions
GaussDB is compatible with most Oracle conditions.
Table 7-31 Conditions
No.
Oracle GaussDB Dierence
1 Comparison
conditions
Supported,
with
dierences.
Dierences exist when statements
contain the ANY, SOME, and ALL
operators. Oracle supports operations
on list objects, but GaussDB needs to
convert list objects into array
expressions before performing
operations.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 68

No. Oracle GaussDB Dierence
2 Floating-point
conditions
Not
supported.
-
3 Logical
conditions
Supported. -
4 Model
conditions
Not
supported.
-
5 Multiset
conditions
Not
supported.
-
6 Pattern-
matching
conditions
Supported. -
7 NULL
conditions
Supported. -
8 XML
conditions
Not
supported.
-
9 SQL/JSON
conditions
Partially
supported,
with
dierences.
● GaussDB does not support the IS
JSON and JSON_TEXTCONTAINS
conditions.
● The JSONB_EQ condition in
GaussDB is the same as the
JSON_EQUAL condition in Oracle.
However, GaussDB does not
support the ERROR clause.
● The JSONB_EXISTS condition in
GaussDB is the same as the
JSON_EXISTS condition in Oracle.
However, GaussDB does not
support the ERROR, EMPTY, or
PASSING clauses.
10 Compound
conditions
Supported. -
11 BETWEEN
condition
Supported. -
12 EXISTS
condition
Supported. -
13 IN condition Supported. -
14 IS OF TYPE
condition
Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 69

7.1.7 Common SQL DDL Clauses
GaussDB is compatible with some DDL clauses.
Table 7-32 Common SQL DDL clauses
No. Oracle GaussDB Dierence
1 allocate_exten
t_clause
Not
supported.
-
2 constraint Supported. -
3 deallocate_un
used_clause
Not
supported.
-
4 le_specicati
on
Not
supported.
-
5 logging_claus
e
Partially
supported,
with
dierences.
● GaussDB does not support the
LOGGING and
FILESYSTEM_LIKE_LOGGING
constraint clauses.
● GaussDB supports only table-level
UNLOGGED constraints and does
not support column-level
UNLOGGED constraints.
● GaussDB uses logging clauses only
in the CREATE TABLE, CREATE
TABLE AS, and SELECT INTO
statements.
6 parallel_claus
e
Not
supported.
-
7 physical_attri
butes_clause
Partially
supported,
with
dierences.
● GaussDB does not support
PCTUSED.
● GaussDB uses physical attribute
clauses only in the CREATE TABLE
and CREATE INDEX statements.
8 size_clause Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 70

No. Oracle GaussDB Dierence
9 storage_claus
e
Partially
supported,
with
dierences.
● In Oracle, storage parameters are
specied by the STORAGE clause. In
GaussDB, storage parameters are
specied by the WITH clause.
● Optional storage parameters in
GaussDB are greatly dierent from
those in Oracle. For details, see the
GaussDB parameter description in
"SQL Reference > SQL Syntax > C >
CREATE TABLE" in
Developer Guide
.
WITH ({storage_parameter =
value} [, ...]) describes the storage
parameters supported by the
CREATE TABLE statement.
7.1.8 SQL Queries and Subqueries
GaussDB is compatible with SQL queries and subqueries except hierarchical
queries.
Table 7-33 SQL queries and subqueries
No.
Oracle GaussDB Dierence
1 Creating
simple
queries
Supported. -
2 Hierarchical
queries
Not
supported.
-
3 UNION [ALL],
INTERSECT,
MINUS
Supported. -
4 Sorting query
results
Supported,
with
dierences.
If the GaussDB query does not contain
groups and the target column contains
both an aggregate function and a set
return function, the sorting of the set
return function column is not ignored.
5 Joins Supported,
with
dierences.
GaussDB supports only the same join
types as Oracle, such as left/right, self,
natural, and full outer join. Join
optimization methods such as IN-
MEMORY JOIN GROUPS are not
supported.
6 Using
subqueries
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 71

No. Oracle GaussDB Dierence
7 Unnesting of
nested
subqueries
Supported,
with
dierences.
HASH_AJ or MERGE_AJ cannot be
explicitly specied in GaussDB.
8 Distributed
queries
Supported,
with
dierences.
GaussDB requires explicit database link
query.
9 Aggregate
function
nesting
Supported. -
7.1.9 PL/SQL Language
GaussDB is compatible with PL/SQL operators, expressions, control statements,
collections, and records, but does not support predened PL/SQL constants, types,
and subtypes.
7.1.9.1 Basic PL/SQL Syntax
Table 7-34 PL/SQL operators
No.
Oracle GaussDB
1 + Supported.
2 := Supported.
3 => Supported.
4 % Supported.
5 ' Supported.
6 . Supported.
7 || Supported.
8 / Supported.
9 ** Not supported.
10 ( Supported.
11 ) Supported.
12 : Supported.
13 , Supported.
14 << Supported.
15 >> Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 72

No. Oracle GaussDB
16 /* Supported.
17 */ Supported.
18 * Supported.
19 " Supported.
20 .. Supported.
21 = Supported.
22 <> Supported.
23 != Supported.
24 ~= Supported.
25 ^= Supported.
26 < Supported.
27 > Supported.
28 <= Supported.
29 >= Supported.
30 @ Supported.
31 -- Supported.
32 ; Supported.
33 - Supported.
Table 7-35 Logical operators
No.
Oracle GaussDB
1 NOT Supported.
2 AND Supported.
3 OR Supported.
Table 7-36 Comparison expressions
No.
Oracle GaussDB
1 IS [NOT] NULL Supported.
2 LIKE Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 73

No. Oracle GaussDB
3 BETWEEN Supported.
4 IN Supported.
Table 7-37 CASE expressions
No. Oracle GaussDB
1 simple CASE Supported.
2 searched CASE Supported.
Table 7-38 Parameters related to variable declaration
No. Oracle GaussDB Dierence
1 %TYPE Supported,
with
dierences.
● GaussDB does not support
record
%type
.
● GaussDB does not support pkg.
record
%type
and schema.pkg.
record%type
as the input and output parameter
types.
● In GaussDB,
Table/
View
.column.
column%type
or
schema.
Table/View
.column.
column
%type
cannot be nested with one or
more layers as variable types or input/
output parameter type.
● In GaussDB,
record
.column.
column
%type
and pkg.
record
.column.
column
%TYPE
cannot be nested with a
column type of records at one or more
layers as the variable type or input/
output parameter type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 74

No. Oracle GaussDB Dierence
2 %ROWTYP
E
Supported,
with
dierences.
● When GaussDB has multiple CNs, the
%ROWTYPE and %TYPE attributes of
the temporary table cannot be
declared in a stored procedure. The
temporary table is valid only in the
current session. During compilation,
other CNs cannot view the temporary
table of the current CN. Therefore, if
there are multiple CNs, the system
displays a message indicating that the
temporary table does not exist.
● GaussDB does not support
view
%rowtype
and schema.
view%rowtype
as the input and output parameter
types.
● GaussDB does not support the
package.
cursor%rowtype
as the input
and output parameter types.
7.1.9.2 Data Type Compatibility
Table 7-39 Other PL/SQL data types
No.
Oracle GaussDB Dierence
1 CHARACTER Supported,
with
dierences.
● GaussDB: The length ranges from 1
to 10485760 bytes.
● Oracle: The length ranges from 1 to
32767 bytes.
2 VARCHAR Supported,
with
dierences.
● GaussDB: The length ranges from 1
to 10485760 bytes.
● Oracle: The length ranges from 1 to
32767 bytes.
3 STRING Not
supported.
-
4 PLS_INTEGER Not
supported.
In GaussDB, you can use the INT type.
5 BINARY_INTE
GER
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 75

7.1.9.3 Control Statements
Table 7-40 Conditional statements
No. Oracle GaussDB
1 IF THEN Supported.
2 IF THEN ELSE Supported.
3 IF THEN ELSIF Supported.
4 simple CASE:
CASE selector
WHEN selector_value_1 THEN
statements_1
WHEN selector_value_2 THEN
statements_2
...
WHEN selector_value_n THEN
statements_n
[ ELSE
else_statements
END CASE;]
Supported.
5 searched CASE:
CASE
WHEN condition_1 THEN statements_1
WHEN condition_2 THEN statements_2
...
WHEN condition_n THEN statements_n
[ ELSE
else_statements
END CASE;]
Supported.
Table 7-41 LOOP statements
No.
Oracle GaussDB
1 [ label ] LOOP
statements
END LOOP [ label ];
Supported.
2 EXIT; Supported.
3 EXIT WHEN; Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 76

No. Oracle GaussDB
4 CONTINUE; Supported.
5 CONTINUE WHEN; Supported.
Table 7-42 FOR LOOP statements
No. Oracle GaussDB Dierence
1 [ label ] FOR index IN
[ REVERSE ]
lower_bound..upper_bo
und LOOP
statements
END LOOP [ label ];
Supported
, with
dierence
s.
When the keyword REVERSE is
used in GaussDB, the lower
bound must be greater than or
equal to the upper bound;
otherwise, the loop body is not
executed.
2 EXIT WHEN; Supported
.
-
3 CONTINUE WHEN; Supported
.
-
Table 7-43 WHILE LOOP statement
No.
Oracle GaussDB
1 [ label ] WHILE condition LOOP
statements
END LOOP [ label ];
Supported.
Table 7-44 GOTO statement
No.
Oracle GaussDB
1 GOTO Supported.
Table 7-45 NULL statement
No.
Oracle GaussDB
1 NULL Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 77

7.1.9.4 Collections and Records
Table 7-46 Types
No. Oracle GaussDB
1 Associative array (or index-by
table)
Supported.
2 VARRAY (variable-size array) Supported.
3 Nested table Supported.
4 record Supported.
Table 7-47 Syntax
N
o.
Types Oracle GaussDB Dierence
1 Associative
array (or
index-by table)
TABLE OF datatype
[ NOT NULL ]
INDEX BY
{ PLS_INTEGER |
BINARY_INTEGER |
VARCHAR2 ( v_size ) |
data_type }
Supporte
d, with
dierenc
es.
● GaussDB does not
support the
PLS_INTEGER
type. In GaussDB,
the value of
data_type can be
a base data type
or a record type,
collection type, or
array type dened
in a stored
procedure. The ref
cursor type is not
supported.
● In GaussDB, NOT
NULL does not
take eect in the
syntax. That is,
the system does
not check whether
an element is
NULL.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records >
Collections" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 78

N
o.
Types Oracle GaussDB Dierence
2 VARRAY
(variable-size
array)
{ VARRAY |
[ VARYING ] ARRAY }
( size_limit )
OF datatype [ NOT
NULL ]
Supporte
d, with
dierenc
es.
● GaussDB does not
support the NOT
NULL syntax.
● In GaussDB,
datatype cannot
be set to varray
(varray cannot be
nested).
● To make the
size_limit function
take eect, enable
the
varray_compat
parameter in the
behavior_compat
_options GUC
parameter.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records > Arrays"
in
Developer
Guide
.
3
Nested table TABLE OF datatype
[ NOT NULL ]
Supporte
d, with
dierenc
es.
● In GaussDB, NOT
NULL does not
take eect in the
syntax.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records >
Collections" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 79

N
o.
Types Oracle GaussDB Dierence
4 record TYPE record_type IS
RECORD
( eld_denition [,
eld_denition]... ) ;
Supporte
d.
● Record columns
can be dened as
NOT NULL or a
default value can
be specied. If the
record type is
nested in other
types, the default
value and NOT
NULL of the
record type do not
take eect. If a
record variable is
created using the
package.record_ty
pe access type,
the default value
and NOT NULL of
the record
variable do not
take eect.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records >
Records" in
Developer Guide
.
Table 7-48 Constructor
No.
Oracle GaussDB
1 collection_type ( [ value [,
value ]... ] )
Supported.
Table 7-49 Variable assignment
No.
Oracle GaussDB Dierence
1 Associative array (or
index-by table)
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 80

No. Oracle GaussDB Dierence
2 VARRAY (variable-size
array)
Supported, with
dierences.
● Values of
dierent
VARRAY data
in GaussDB
can be
assigned to
each other,
depending on
whether
elements in the
data can be
implicitly
converted to
each other.
● For details, see
"Stored
Procedure >
Arrays,
Collections,
and Records >
Arrays" in
Developer
Guide
.
3
Nested table Supported. -
4 record Supported, with
dierences.
● Values of
dierent record
data in
GaussDB can
be assigned to
each other,
depending on
whether
columns can
be implicitly
converted.
● For details, see
"Stored
Procedure >
Arrays,
Collections,
and Records >
Records" in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 81
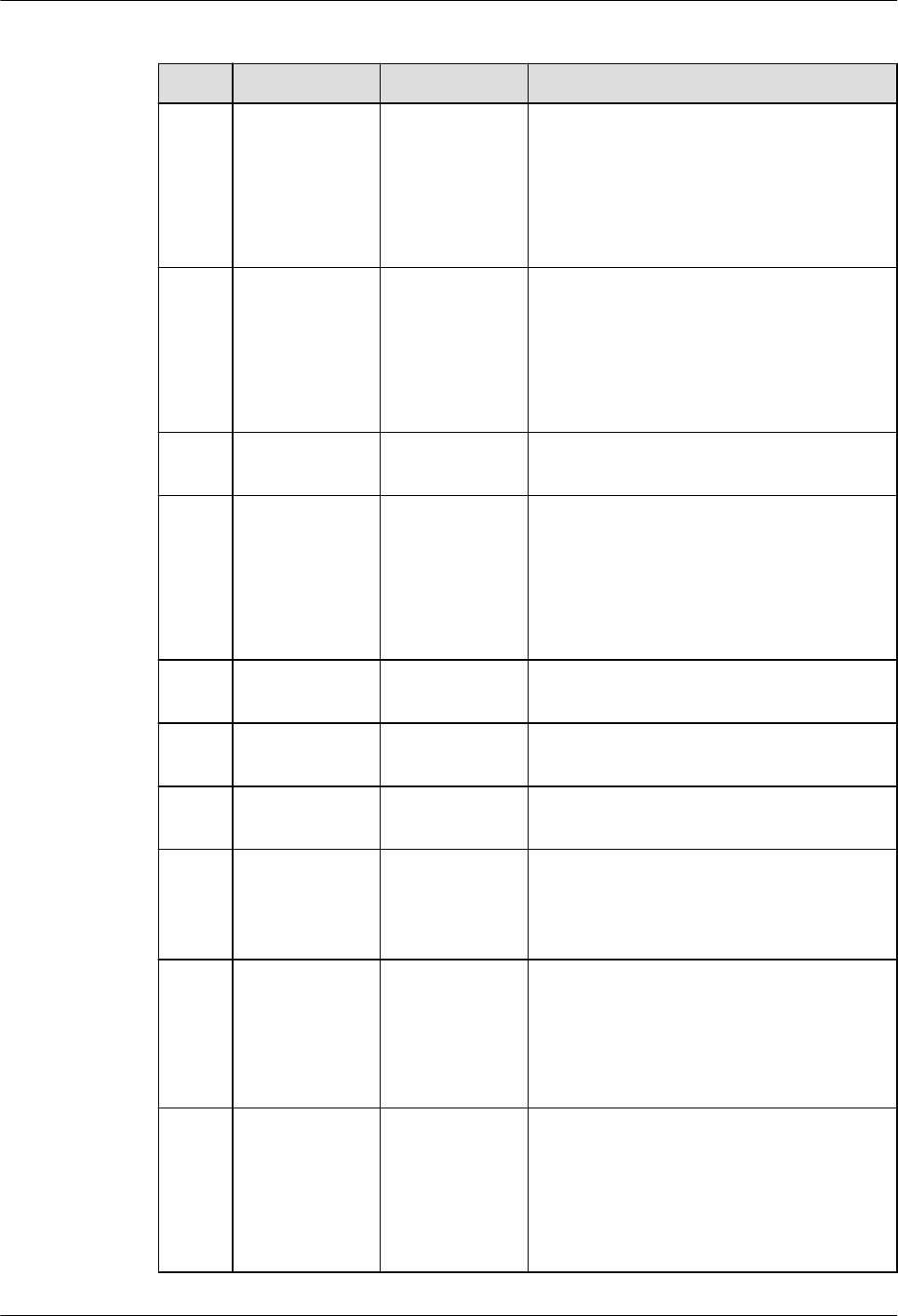
Table 7-50 Collection operators
No. Oracle GaussDB Dierence
1 = Supported,
with
dierences.
● Oracle: The sequence of collection
members is ignored during
comparison.
● GaussDB: The comparison is
performed strictly based on the
sequence of collection members.
2 <> Supported,
with
dierences.
● Oracle: The sequence of collection
members is ignored during
comparison.
● GaussDB: The comparison is
performed strictly based on the
sequence of collection members.
3 IS[NOT]
NULL
Supported. -
4 ^= Supported,
with
dierences.
● Oracle: The sequence of collection
members is ignored during
comparison.
● GaussDB: The comparison is
performed strictly based on the
sequence of collection members.
5 ~= Not
supported.
-
6 IS[NOT] A
SET
Not
supported.
-
7 IS [NOT]
EMPTY
Not
supported.
-
8 expr [ NOT ]
MEMBER
[ OF ]
nested_table
Not
supported.
-
9 nested_table1
[ NOT ]
SUBMULTISET
[ OF ]
nested_table2
Not
supported.
-
10 [NOT] IN Supported. ● Oracle: The sequence of collection
members is ignored during
comparison.
● GaussDB: The comparison is
performed strictly based on the
sequence of collection members.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 82

Table 7-51 MULTISET functions
No. Oracle GaussDB
1 MULTISET UNION [ALL |
DISTINCT]
Supported.
2 MULTISET EXCEPT [ALL |
DISTINCT]
Supported.
3 MULTISET INTERSECT [ALL |
DISTINCT]
Supported.
Table 7-52 Collection type functions
No. Oracle GaussDB Dierence
1 exists(idx) Supported. -
2 extend[(count[,
idx])]
Supported,
with
dierences.
GaussDB supports only nested
tables.
3 delete[(idx1[,
idx2])]
Supported. -
4 trim[(n)] Supported,
with
dierences.
GaussDB supports only nested
tables.
5 count Supported. -
6 rst Supported. -
7 last Supported. -
8 prior(idx) Supported. -
9 next(idx) Supported. -
10 limit Supported,
with
dierences.
In GaussDB, the maximum
number of elements that can
be stored in a nested-table
collection is returned. This
function applies only to the
array type. The return value is
null.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 83

Table 7-53 Record variable operations
No. Oracle GaussDB
1 Constructors Supported.
2 %ROWTYPE to declare a
variable
Supported.
3 Dening constants Not supported.
Table 7-54 Collection-related functions
No. Oracle GaussDB
1 unnest_table(anynesttable
)
Supported.
2 unnest_table(anyindexbyt
able)
Supported.
7.1.9.5 Static SQL Statements
Table 7-55 Static query SQL statements
No.
Oracle GaussDB Dierence
1 SELECT Supported,
with
dierences.
GaussDB and Oracle are dierent in
some scenarios.
In GaussDB, FOR SHARE adds a shared
lock to the retrieved rows. The shared
locks of dierent transactions do not
block each other. If data is locked by
FOR SHARE in one transaction and
SELECT FOR SHARE SKIP LOCKED is
used in another transaction, SKIP
LOCKED does not skip the lock.
Table 7-56 Static DML SQL statements
No.
Oracle GaussDB
1 INSERT Supported.
2 UPDATE Supported.
3 DELETE Supported.
4 MERGE Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 84

No. Oracle GaussDB
5 LOCK TABLE Supported.
Table 7-57 Static TCL SQL statements
No. Oracle GaussDB Dierence
1 COMMIT Supported. -
2 ROLLBACK Supported. -
3 SAVEPOINT Supported. -
4 SET
TRANSACTIO
N
Supported,
with
dierences.
GaussDB does not support the NAME
string and USE ROLLBACK SEGMENT
rollback_segment syntax.
Table 7-58 Pseudocolumns
No.
Oracle GaussDB Dierence
1 CURRVAL and
NEXTVAL
Supported
.
-
2 LEVEL Not
supported.
-
3 OBJECT_VALUE Not
supported.
-
4 ROWID Not
supported.
-
5 ROWNUM Supported
, with
dierence
s.
It is not recommended that the
ROWNUM condition be used in the
JOIN ON clause.
In GaussDB, when the ROWNUM
condition is used in the JOIN ON
clause, the behavior in the LEFT JOIN,
RIGHT JOIN, FULL JOIN, and MERGE
INTO scenarios is dierent from that
in other databases, causing risks in
service migration.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 85
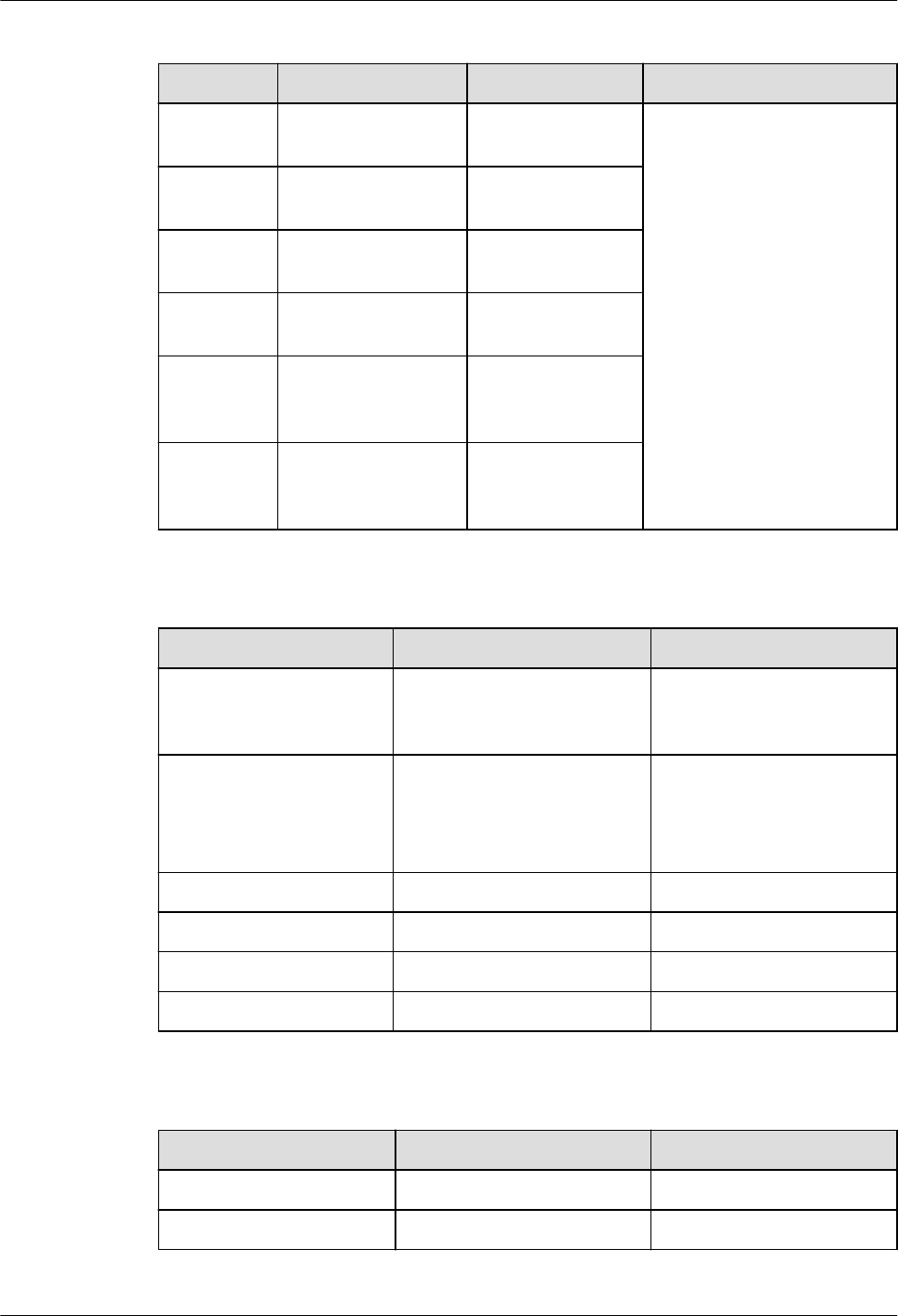
Table 7-59 Implicit cursor attributes
No. Oracle GaussDB Dierence
1 SQL%FOUND Supported, with
dierences.
GaussDB does not update
the implicit cursor result
after COMMIT or
ROLLBACK. Oracle
updates the implicit
cursor result after
COMMIT or ROLLBACK.
2 SQL%NOTFOUND Supported, with
dierences.
3 SQL%ROWCOUNT Supported, with
dierences.
4 SQL%ISOPEN Supported, with
dierences.
5 SQL
%BULK_ROWCOU
NT
Not supported.
6 SQL
%BULK_EXCEPTIO
NS
Not supported.
Table 7-60 Explicit cursor syntax and keywords
No.
Oracle GaussDB
1 CURSOR cursor_name
[ parameter_list ] RETURN
return_type;
Supported.
2 CURSOR cursor_name
[ parameter_list ]
[ RETURN return_type ]
IS select_statement;
Supported.
3 OPEN Supported.
4 CLOSE Supported.
5 FETCH Supported.
6 CURRENT OF CURSOR Supported.
Table 7-61 Explicit cursor attributes
No.
Oracle GaussDB
1 SQL%FOUND Supported.
2 SQL%NOTFOUND Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 86

No. Oracle GaussDB
3 SQL%ROWCOUNT Supported.
4 SQL%ISOPEN Supported.
Table 7-62 Cursor loop
No. Oracle GaussDB
1 FOR LOOP Supported.
Table 7-63 Scenarios supported by autonomous transactions
No. Oracle GaussDB
1 Stored procedures Supported.
2 Anonymous blocks Supported.
3 Functions Supported.
4 Packages Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 87

7.1.9.6 Dynamic SQL Statements
Table 7-64 Dynamic SQL statement execution modes
No. Oracle GaussDB Dierence
1 EXECUTE
IMMEDIATE
Supported,
with
dierences.
● GaussDB uses the
dynamic_sql_compat parameter to
determines whether variables with
the same name read the same
parameter and check whether the
input and output parameter types
of the bound parameters are the
same as those of the statement
parameters when the stored
procedure is called.
● GaussDB does not support
scenarios where some bound
parameters in anonymous blocks
are called. For example, when
dynamic statements are nested in
anonymous blocks, expressions are
used to bind parameters. For
details, see "Stored Procedure >
Dynamic Statements > Dynamically
Calling Anonymous Blocks" in
Developer Guide
.
● GaussDB does not support
RETURNING or RETURN INTO.
2
OPEN FOR,
FETCH, CLOSE
Supported. -
7.1.9.7 Triggers
Table 7-65 Trigger types
No.
Oracle GaussDB Dierence
1 DML TRIGGER Supported, with
dierences.
GaussDB: Compound
DML triggers are not
supported.
2 SYSTEM TRIGGER Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 88

Table 7-66 CREATE triggers
Syntax Type Oracle GaussDB Dierence
CREATE CREATE [ OR
REPLACE ]
[ EDITIONABLE |
NONEDITIONABLE ]
TRIGGER
plsql_trigger_source
Supported, with
dierences.
GaussDB does not
support OR
REPLACE or
EDITIONABLE |
NONEDITIONABL
E, but supports
some behaviors of
plsql_trigger_sour
ce.
plsql_trigger
_source ::=
[schema.]
trigger_name
[ sharing_clause ]
[ default_collation_cl
ause ]
{ simple_dml_trigger
|
instead_of_dml_trigg
er
|
compound_dml_trigg
er
| system_trigger
}
Supported, with
dierences.
GaussDB: The
schema,
sharing_clause,
and
default_collation_
clause are not
supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 89
Syntax Type Oracle GaussDB Dierence
simple_dml_
trigger ::=
{ BEFORE | AFTER }
dml_event_clause
[ referencing_clause
] [ FOR EACH ROW ]
[ trigger_edition_cla
use ]
[ trigger_ordering_cl
ause ]
[ ENABLE |
DISABLE ] [ WHEN
( condition ) ]
trigger_body
Supported, with
dierences.
GaussDB does not
support
referencing_clause
,
referencing_clause
(instead, the from
referencing_table
is used),
trigger_edition_cla
use,
trigger_ordering_c
lause, and
ENABLE |
DISABLE. It
supports some
behaviors of
trigger_body.
No error is
reported in
GaussDB when a
statement-level
BEFORE/AFTER
TRIGGER is
created in a view
without INSTEAD
OF TRIGGER. An
error is reported
when DML is
executed.
dml_event_c
lause ::=
{ DELETE | INSERT |
UPDATE [ OF
column [,
column ]... ] }
[ OR { DELETE |
INSERT | UPDATE
[ OF column [,
column]... ] }...
ON [ schema.]
{ table | view }
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 90

Syntax Type Oracle GaussDB Dierence
trigger_body
::=
{ plsql_block | CALL
routine_clause }
Supported, with
dierences.
GaussDB: The
plsql_block is not
supported. A
function can be
executed only in
EXECUTE
PROCEDURE
function_name
( arguments );
mode. In addition,
the function
needs to be
dened by users
and declared that
it does not
contain
parameters and
the return type is
trigger. It is
executed when a
trigger is
triggered.
instead_of_d
ml_trigger ::
=
INSTEAD OF
{ DELETE | INSERT |
UPDATE } [ OR
{ DELETE | INSERT |
UPDATE } ]...
ON [ NESTED TABLE
nested_table_column
OF ] [ schema. ]
noneditioning_view
[ referencing_clause
] [ FOR EACH ROW ]
[ trigger_edition_cla
use ]
[ trigger_ordering_cl
ause ]
[ ENABLE |
DISABLE ]
trigger_body
Supported, with
dierences.
GaussDB: The
NESTED TABLE
nested_table_colu
mn OF,
referencing_clause
,
trigger_edition_cla
use,
trigger_ordering_c
lause, and
ENABLE | DISABLE
are not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 91

Syntax Type Oracle GaussDB Dierence
compound_d
ml_trigger ::
=
CREATE trigger FOR
dml_event_clause
ON view
COMPOUND
TRIGGER
INSTEAD OF EACH
ROW IS BEGIN
statement;
END INSTEAD OF
EACH ROW;
Not supported. -
system_trigg
er ::=
{ BEFORE | AFTER |
INSTEAD OF }
{ ddl_event [OR
ddl_event]... |
database_event [OR
database_event ]... }
ON { [schema.]
SCHEMA |
[ PLUGGABLE ]
DATABASE }
[ trigger_ordering_cl
ause ] [ ENABLE |
DISABLE ]
trigger_body
Not supported. -
Table 7-67 ALTER trigger
No.
Oracle GaussDB Dierence
1 ALTER TRIGGER [ schema. ]
trigger_name
{ trigger_compile_clause
| { ENABLE | DISABLE }
| RENAME TO new_name
| { EDITIONABLE |
NONEDITIONABLE }
} ;
Supported, with
dierences.
GaussDB: The
schema,
trigger_compile_cl
ause, { ENABLE |
DISABLE }, and
{ EDITIONABLE |
NONEDITIONABL
E } are not
supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 92

Table 7-68 drop trigger
No. Oracle GaussDB Dierence
1 DROP
TRIGGER
[ schema. ]
trigger ;
Supported,
with
dierences.
GaussDB does not support schemas.
You need to add ON table_name to
the end of trigger_name.
The *_TRIGGERS views in Oracle collect information about triggers. The views in
GaussDB are dierent from those in Oracle. For details, see sections
"DB_TRIGGERS", "ADM_TRIGGERS", and "MY_TRIGGERS" in "System Catalogs and
System Views > System Views > Other System Views" in
Developer Guide
.
Table 7-69 Compatibilities of nested, package, and standalone subprograms
No. Oracle GaussDB Dierence
1 Nested subprogram
(subblock)
Supported, with
dierences.
GaussDB does not
support
overloading.
GaussDB does not
support the
denition of
autonomous
transactions.
GaussDB does not
support SETOF.
Only one qualier
can reference
nested
subprograms or
variables of
nested
subprograms.
2 package subprogram Supported. -
3 Standalone
subprogram
(including function &
procedure)
Supported. -
4 Anonymous block Supported. -
Table 7-70 RETURN statements
No.
Oracle GaussDB
1 Function Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 93

No. Oracle GaussDB
2 Procedure Supported.
3 Anonymous block Supported.
Table 7-71 Function-related parameters
No. Oracle GaussDB Dierence
1 DETERMINISTIC Supported, with
dierences.
In GaussDB, it is
IMMUTABLE.
2 PARALLEL_ENABLE Not supported. -
3 PIPELINED Not supported. -
4 RESULT_CACHE Not supported. -
Table 7-72 Parameter formats
No.
Oracle GaussDB
1 IN Supported.
2 OUT Supported.
3 IN OUT Supported.
Table 7-73 CREATE statements
No.
Oracle GaussDB Dierence
1 CREATE
FUNCTION
Supported,
with
dierences.
GaussDB does not support the IF NOT
EXISTS syntax, sharing_clause, or
keywords [ EDITIONABLE |
NONEDITIONABLE ]. Only some
clauses that specify the function
attribute are supported (only the
invoker_rights_clause clause is
supported).
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > C >
CREATE FUNCTION" in
Developer
Guide
.
2 CREATE
LIBRARY
Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 94

No. Oracle GaussDB Dierence
3 CREATE
PACKAGE
Supported,
with
dierences.
GaussDB does not support the IF NOT
EXISTS syntax, sharing_clause, or
keywords [ EDITIONABLE |
NONEDITIONABLE ]. Only some
clauses that specify the package
attribute are supported (only the
invoker_rights_clause clause is
supported).
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > C >
CREATE PACKAGE" in
Developer Guide
.
4 CREATE
PACKAGE
BODY
Supported,
with
dierences.
GaussDB does not support the IF NOT
EXISTS syntax, sharing_clause, or
keywords [ EDITIONABLE |
NONEDITIONABLE ].
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > C >
CREATE PACKAGE" in
Developer Guide
.
5 CREATE
PROCEDURE
Supported,
with
dierences.
GaussDB does not support the IF NOT
EXISTS syntax, sharing_clause, or
keywords [ EDITIONABLE |
NONEDITIONABLE ].
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > C >
CREATE PROCEDURE" in
Developer
Guide
.
6 CREATE
TRIGGER
Supported,
with
dierences.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > C >
CREATE TRIGGER" in
Developer Guide
.
7 CREATE TYPE Supported,
with
dierences.
GaussDB does not support the varray,
object type, and UNDER syntax.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > C >
CREATE TYPE" in
Developer Guide
.
8 CREATE TYPE
BODY
Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 95

Table 7-74 ALTER statements
No. Oracle GaussDB Dierence
1 ALTER
FUNCTION
Supported,
with
dierences.
GaussDB does not support keywords
[ EDITIONABLE | NONEDITIONABLE ],
REUSE, SETTINGS, and DEBUG.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > A >
ALTER FUNCTION" in
Developer Guide
.
2 ALTER
LIBRARY
Not
supported.
-
3 ALTER
PACKAGE
Supported,
with
dierences.
GaussDB does not support keywords
[ EDITIONABLE | NONEDITIONABLE ],
REUSE, SETTINGS, and DEBUG.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > A >
ALTER PACKAGE" in
Developer Guide
.
4 ALTER
PROCEDURE
Supported,
with
dierences.
GaussDB does not support keywords
[ EDITIONABLE | NONEDITIONABLE ],
REUSE, SETTINGS, and DEBUG.
5 ALTER
TRIGGER
Supported,
with
dierences.
In GaussDB, only the trigger name can
be modied.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > A >
ALTER TRIGGER" in
Developer Guide
.
6 ALTER TYPE Supported,
with
dierences.
GaussDB supports only some
statements.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > A >
ALTER TYPE" in
Developer Guide
.
Table 7-75 DROP statements
No.
Oracle GaussDB Dierence
1 DROP
FUNCTION
Supported. -
2 DROP
LIBRARY
Not
supported.
-
3 DROP
PACKAGE
Supported. -
4 DROP
PROCEDURE
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 96
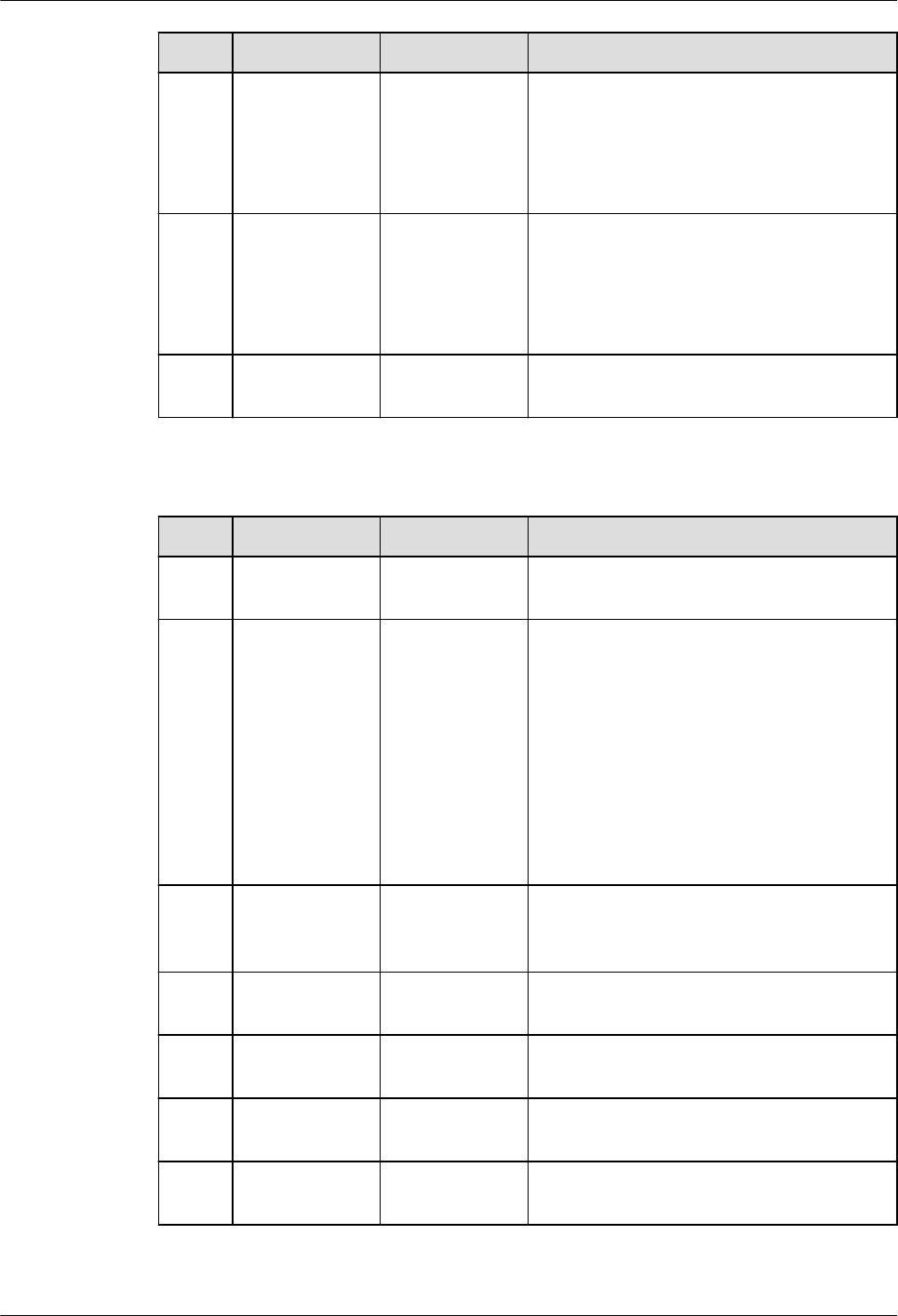
No. Oracle GaussDB Dierence
5 DROP
TRIGGER
Supported,
with
dierences.
The syntax of GaussDB is dierent
from that of Oracle.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > D >
DROP TRIGGER" in
Developer Guide
.
6 DROP TYPE Supported,
with
dierences.
GaussDB does not support keywords
FORCE and VALIDATE.
For details about GaussDB syntax, see
"SQL Reference > SQL Syntax > D >
DROP TYPE" in
Developer Guide
.
7 DROP TYPE
BODY
Not
supported.
-
Table 7-76 Keywords related to functions, procedures, and anonymous blocks
No. Oracle GaussDB Dierence
1 ACCESSIBLE
BY
Not
supported.
-
2 AGGREGATE Supported,
with
dierences.
● GaussDB does not support Oracle's
aggregate using [schema.]
implementation_type.
● For details about GaussDB syntax,
see "SQL Reference > SQL Syntax >
C > CREATE AGGREGATE" in
Developer Guide
.
The syntax is dierent, but the
implementation functions are the
same.
3 DETERMINIST
IC
Supported,
with
dierences.
GaussDB supports the keyword
DETERMINISTIC only in syntax, but
does not support this function.
4 PIPE ROW Not
supported.
-
5 PIPELINED Not
supported.
-
6 SQL_MACRO Not
supported.
-
7 RESTRICT_REF
ERENCES
Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 97

No. Oracle GaussDB Dierence
8 INLINE Not
supported.
-
Table 7-77 Keywords related to exception handling
No. Oracle GaussDB Dierence
1 EXCEPTION_INIT Supported, with
dierences.
Binding with
system error
codes is not
supported in
GaussDB.
2 Exception Supported. -
3 Exception Handler Supported. -
4 SQLCODE Supported. -
5 SQLERRM Supported. -
Table 7-78 Other PL/SQL keywords
No.
Oracle GaussDB Dierence
1 COVERAGE Not supported. -
2 COLLATION Supported. -
3 DEPRECATE Not supported. -
4 FORALL Supported. -
5 NOCOPY Not supported. -
6 RETURNING Supported. -
7 SERIALLY_REUSAB
LE
Not supported. -
8 SHARING Not supported. -
9 BULK COLLECT Supported. -
7.1.10 System Functions
Compatible functions are classied into single-row functions, user-dened
functions, aggregate functions, analytic functions, object reference functions,
model functions, and OLAP functions.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 98

7.1.10.1 Single-row Functions
No. Oracle GaussDB
1 Numeric functions Supported, with
dierences.
2 Character functions returning
character values
Supported, with
dierences.
3 Character functions returning
number values
Supported, with
dierences.
4 Character set functions Not supported.
5 Collation functions Not supported.
6 Datetime functions Supported, with
dierences.
7 General comparison functions Supported, with
dierences.
8 Conversion functions Supported, with
dierences.
9 Large object functions Supported, with
dierences.
10 Collection functions Not supported.
11 Hierarchical functions Supported.
12 Data mining functions Not supported.
13 XML functions Supported, with
dierences.
14 JSON functions Not supported.
15 Encoding and decoding
functions
Supported, with
dierences.
16 Null-related functions Supported.
17 Environment and identier
functions
Supported, with
dierences.
Table 7-79 Numeric functions
No.
Oracle GaussDB Dierence
1 ABS Supported. -
2 ACOS Supported. -
3 ASIN Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 99

No. Oracle GaussDB Dierence
4 ATAN Supported. -
5 ATAN2 Supported. -
6 BITAND Supported. -
7 CEIL Supported. -
8 COS Supported. -
9 COSH Supported. -
10 EXP Supported. -
11 FLOOR Supported. -
12 LN Supported. -
13 LOG Supported. -
14 MOD Supported,
with
dierences.
● The return types are inconsistent. In
Oracle, the return types include
BINARY_DOUBLE, BINARY_FLOAT,
and NUMBER. In GaussDB, the
return types include int2, int4, int8,
and numeric.
● If one of the two input parameters
is of the int type, the other
parameter must be of the int,
numeric, or literal integer type (a
valid number without a decimal
point, for example, '12').
15 NANVL Supported,
with
dierences.
GaussDB: NaN cannot be obtained by
directly declaring or dividing a
oating-point number by 0.
16 POWER Supported. -
17 REMAINDER Supported,
with
dierences.
If one of the two input parameters is
of the int type, the other parameter
must be of the int, numeric, or literal
integer type (a valid number without a
decimal point, for example, '12').
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 100

No. Oracle GaussDB Dierence
18 ROUND Supported,
with
dierences.
● For the rst parameter n of the
oat type, GaussDB has precision
loss, and the precision is lower than
that of Oracle.
● The returned types are dierent.
For round(n, integer), Oracle
returns the NUMBER type, and
GaussDB returns the numeric type.
For round(n), Oracle returns the
data type of n, and GaussDB
returns only the oat8 and numeric
types. The oat4 return type is
missing.
● The logic for the GaussDB to
determine that the input parameter
is null and the execution framework
to return null is dierent from that
in Oracle.
SELECT round(NULL,'q');
Oracle reports null, and GaussDB
reports the error: invalid input
syntax for integer: "q".
19
SIGN Supported. -
20 SIN Supported. -
21 SINH Supported. -
22 SQRT Supported. -
23 TAN Supported. -
24 TANH Supported,
with
dierences.
The returned results of integers or
integers enclosed in quotation marks
(for example, '12') are dierent.
25 TRUNC Supported. -
26 WIDTH_BUCK
ET
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 101

Table 7-80 Character functions returning character values
No. Oracle GaussDB Dierence
1 CHR Supported, with
dierences.
● If the entered number does not
comply with the existing character
set, GaussDB reports an error in
JDBC and Oracle returns garbled
characters.
● If you enter 0 or 256, Oracle returns
characters whose ASCII code is 0,
and GaussDB truncates the
characters at '\0;.
2 CONCAT Supported. -
3 INITCAP Supported, with
dierences.
The returned value is restricted by the
database character set. As a result, the
returned result is dierent from that in
Oracle.
4 LOWER Supported, with
dierences.
● The return value types are dierent.
The data types of Oracle are the
same as the input types.
● The time format is implicitly
converted. When the time type is
entered, the time type is implicitly
converted to a character string and
then the lower operation is
performed.
SELECT LOWER(TO_DATE('2012-12-10','YYYY-
MM-DD'));
Oracle returns 10-DEC-12, and
GaussDB returns 2012-12-10
00:00:00.
● The returned value is restricted by
the database character set. As a
result, the returned result is dierent
from that in Oracle.
5 LPAD Supported. -
6 LTRIM Supported, with
dierences.
The return value types are dierent.
If the input is of the character data
type, Oracle returns the VARCHAR2
type. If the input is of the national
character set specied during database
creation, Oracle returns the
NVARCHAR2 type. If the input is of the
LOB type, Oracle returns the LOB type.
GaussDB returns the TEXT type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 102

No. Oracle GaussDB Dierence
7 NCHR Supported, with
dierences.
● The byte length of the return value
is dierent from that of Oracle.
● The returned value is restricted by
the database character set. As a
result, the returned result is dierent
from that in Oracle.
● When the byte array corresponding
to the input parameter is returned, a
question mark (?) is returned if a
single byte ranges from 0x80 to 0xFF.
In Oracle, a question mark (?) is
returned, no output is returned, or
an error is reported.
8 NLS_LOWE
R
Supported, with
dierences.
● The return value types are dierent.
If the input is of the character data
type, Oracle returns the VARCHAR2
type. If the input is of the LOB type,
Oracle returns the LOB type.
GaussDB returns the TEXT type.
● In Oracle, the nlsparam parameter
can be of a type except nls_sort, and
no error is reported. GaussDB
supports only nls_sort.
● The returned value is restricted by
the database character set. As a
result, the returned result is dierent
from that in Oracle.
9 NLS_UPPER Supported, with
dierences.
● The return value types are dierent.
If the input is of the character data
type, Oracle returns the VARCHAR2
type. If the input is of the LOB type,
Oracle returns the LOB type.
GaussDB returns the TEXT type.
● In Oracle, the nlsparam parameter
can be of a type except nls_sort, and
no error is reported. GaussDB
supports only nls_sort.
● The returned value is restricted by
the database character set. As a
result, the returned result is dierent
from that in Oracle.
10 NLSSORT Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 103
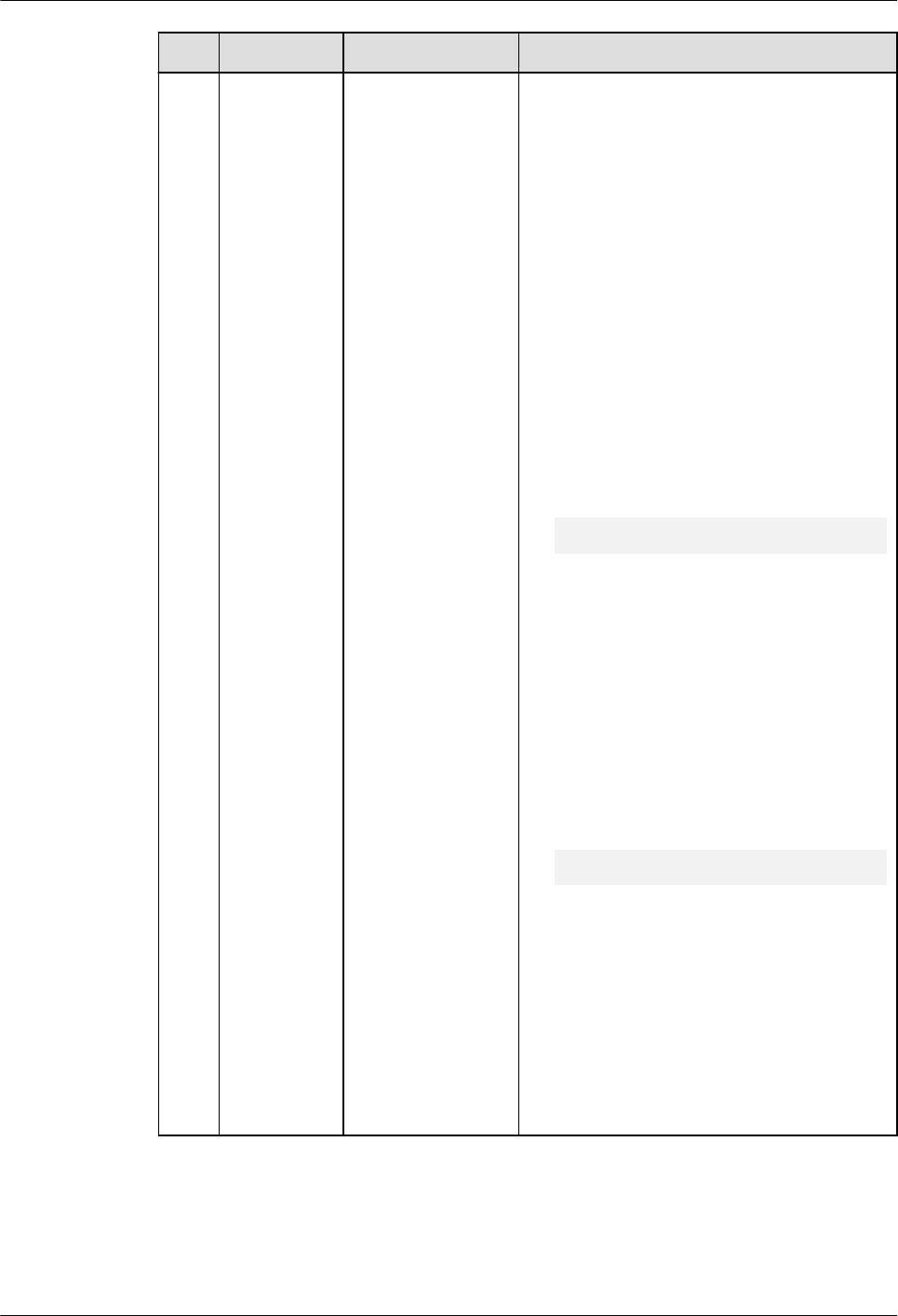
No. Oracle GaussDB Dierence
11 REGEXP_RE
PLACE
Supported, with
dierences.
● GaussDB input parameter
source_char does not support the
NCLOB type.
● The meaning of the 'n' option in the
match_param input parameter is
dierent. In GaussDB, the 'n' option
has the same meaning as the 'm'
option, indicating that the multi-row
matching mode is used. In Oracle, it
indicates that the dot (.) can match
the '\n' character. If this option is not
specied, the '\n' character cannot
be matched by default. In GaussDB,
the dot (.) matches '\n' by default.
You do not need to specify the
option.
● The matching results of some
regular expressions may be dierent.
SELECT REGEXP_REPLACE('abc01234xyz', '(.*?)
(\d+)(.*)', '#', 'g') FROM DUAL;
Oracle reports an error, and GaussDB
returns #####xyz.
● The matching results may be
dierent when Chinese characters
are entered in the UTF-8 encoding
character set. Oracle needs to
implement regular expression
matching for Chinese character
strings in the GBK character set.
● The matching results of regular
expressions that contain some
escape characters may be dierent.
SELECT REGEXP_REPLACE('abcabc', '\abc', '#',
'g') FROM DUAL;
Oracle reports an error, and GaussDB
returns abcabc.
● The matching rules are aected by
the aformat_regexp_match
parameter. For details about the
aected specications, see the
REGEXP_REPLACE function in "SQL
Reference > Functions and Operators
> Character Processing Functions
and Operators" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 104

No. Oracle GaussDB Dierence
12 REGEXP_SU
BSTR
Supported, with
dierences.
The matching rules are aected by the
aformat_regexp_match parameter. For
details about the aected specications,
see the REGEXP_SUBSTR function in
"SQL Reference > Functions and
Operators > Character Processing
Functions and Operators" in
Developer
Guide
.
13 REPLACE Supported. -
14 RPAD Supported. -
15 RTRIM Supported. -
16 SUBSTR Supported. -
17 TRANSLAT
E
Supported. -
18 TRIM Supported. -
19 UPPER Supported, with
dierences.
● The return value types are dierent.
The data types of Oracle are the
same as the input types. GaussDB
returns the TEXT type.
● The time format is implicitly
converted. When the time type is
entered, the time type is implicitly
converted to a character string and
then the upper operation is
performed.
SELECT UPPER(TO_DATE('2012-12-10','YYYY-
MM-DD'));
Oracle returns 10-DEC-12, and
GaussDB returns 2012-12-10
00:00:00.
● The returned value is restricted by
the database character set. As a
result, the returned result is dierent
from that in Oracle.
20 INSTRB Supported. -
Table 7-81 Character functions returning number values
No.
Oracle GaussDB Dierence
1 ASCII Supported,
with
dierences.
The return value types are dierent.
Oracle returns the uint4 type, while
GaussDB returns the int4 type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 105

No. Oracle GaussDB Dierence
2 INSTR Supported. -
3 LENGTH Supported. -
4 REGEXP_COU
NT
Supported,
with
dierences.
● GaussDB input parameter
source_char does not support the
NCLOB type.
● The meaning of the 'n' option in
the match_param input parameter
is dierent. In GaussDB, the 'n'
option has the same meaning as
the 'm' option, indicating that the
multi-row matching mode is used.
In Oracle, it indicates that the dot
(.) can match the '\n' character. If
this option is not specied, the '\n'
character cannot be matched by
default. In GaussDB, the dot (.)
matches '\n' by default. You do not
need to specify the option.
● The matching results of some
regular expressions may be
dierent.
● The matching results may be
dierent when Chinese characters
are entered in the UTF-8 encoding
character set. Oracle needs to
implement regular expression
matching for Chinese character
strings in the GBK character set.
● The matching results of regular
expressions that contain some
escape characters may be dierent.
● The matching rules are aected by
the aformat_regexp_match
parameter. For details about the
aected specications, see the
REGEXP_COUNT function in "SQL
Reference > Functions and
Operators > Character Processing
Functions and Operators" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 106

No. Oracle GaussDB Dierence
5 REGEXP_INST
R
Supported,
with
dierences.
The matching rules are aected by the
aformat_regexp_match parameter.
For details about the aected
specications, see the REGEXP_INSTR
function in "SQL Reference > Functions
and Operators > Character Processing
Functions and Operators" in
Developer
Guide
.
Table 7-82 Datetime functions
No. Oracle GaussDB Dierence
1 ADD_MONTH
S
Supported, with
dierences.
● From A.D. to B.C., the
dierence between
GaussDB and Oracle is one
year.
● The earliest year can be –
4714 in GaussDB and –4713
in Oracle.
2 CURRENT_DA
TE
Supported, with
dierences.
GaussDB: The
nls_date_format parameter
cannot be used to set the time
display format.
3 CURRENT_TI
MESTAMP
Supported, with
dierences.
The value ranges from 0 to 9
in Oracle.
The value ranges from 0 to 6
in GaussDB. The trailing zeros
in microseconds are not
displayed.
4 DBTIMEZONE Supported, with
dierences.
GaussDB: The timestamp API
with the built-in tz cannot be
called.
5 EXTRACT Supported. -
6 LAST_DAY Supported, with
dierences.
The return value types are
dierent.
7 LOCALTIMEST
AMP
Supported, with
dierences.
The value ranges from 0 to 9
in Oracle.
The value ranges from 0 to 6
in GaussDB. The trailing zeros
in microseconds are not
displayed.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 107

No. Oracle GaussDB Dierence
8 MONTHS_BET
WEEN
Supported, with
dierences.
The input parameter types are
dierent.
9 NEW_TIME Supported, with
dierences.
When the rst input
parameter of the new_time
function is a literal, the literal
format and the return value
type of the function are
dierent from those in Oracle.
10 NEXT_DAY Supported. -
11 NUMTODSIN
TERVAL
Supported, with
dierences.
GaussDB: The dsinterval type
is not supported. Currently,
interval is used to be
compatible with the dsinterval
type.
12 NUMTOYMIN
TERVAL
Supported, with
dierences.
GaussDB: The yminterval type
is not supported. Currently,
interval is used to be
compatible with the
yminterval type.
13 SESSIONTIME
ZONE
Supported, with
dierences.
● The assignment syntax is
dierent. In GaussDB, the
SET SESSION TIME ZONE 8
syntax is used. In Oracle,
alter session set time_zone=
'+08:00' is used.
● The default values are
dierent. GaussDB: The
time zone name is
displayed, for example,
PRC. The oset is used in
Oracle, for example, +08:00.
14 SYS_EXTRACT
_UTC
Supported. -
15 SYSDATE Supported, with
dierences.
The return value types are
dierent.
16 TO_CHAR Supported, with
dierences.
The fmt '5' is not included in
the Oracle documents and is
not adapted.
17 TO_DSINTERV
AL
Supported, with
dierences.
GaussDB: The dsinterval type
is not supported. Currently,
interval is used to be
compatible with the dsinterval
type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 108

No. Oracle GaussDB Dierence
18 TO_TIMESTA
MP
Supported, with
dierences.
GaussDB supports only six
digits for millisecond
calculation, and Oracle
supports nine digits.
19 TO_TIMESTA
MP_TZ
Supported, with
dierences.
The timestamptz of GaussDB
is equivalent to the
timestampwithloacltimezone
of Oracle. The type
corresponding to timestamptz
of Oracle is missing. The value
of nls_date_language can
only be ENGLISH or
AMERICAN.
20 TO_YMINTER
VAL
Supported, with
dierences.
GaussDB: The yminterval type
is not supported. Currently,
interval is used to be
compatible with the
yminterval type.
21 TZ_OFFSET Supported, with
dierences.
When a time zone name is
received as an input
parameter, the types of the
time zone name are less than
those of Oracle.
Table 7-83 General comparison functions
No.
Oracle GaussDB Dierence
1 GREATEST Supported, with
dierences.
● GaussDB: The comparison mode
specied by the NLS_SORT parameter
is not supported. Only binary
comparison is supported.
● GaussDB: Expressions in multiple
languages are not supported.
2 LEAST Supported, with
dierences.
● GaussDB: The comparison mode
specied by the NLS_SORT parameter
is not supported. Only binary
comparison is supported.
● GaussDB: Expressions in multiple
languages are not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 109

Table 7-84 Conversion functions
No. Oracle GaussDB Dierence
1 ASCIISTR Supported. -
2 CAST Supported, with
dierences.
● GaussDB: The MULTISET clause is
not supported.
● GaussDB: The nlsparam
parameter is not supported.
3 HEXTORAW Supported. -
4 RAWTOHEX Supported. -
5 TO_BINARY_D
OUBLE
Supported, with
dierences.
GaussDB: The nlsparam parameter is
not supported.
6 TO_BINARY_FL
OAT
Supported, with
dierences.
GaussDB: The nlsparam parameter is
not supported.
7 TO_BLOB Supported, with
dierences.
● GaussDB: The long raw type is not
supported.
● GaussDB: The ble and mime_type
types are not supported.
8 TO_CLOB Supported. -
9 TO_DATE Supported, with
dierences.
● Multi-language parameters are
not supported.
● The returned types are dierent.
● The control parameter
NLS_DATE_FORMAT is missing.
● Some formats are not supported.
● fmt = 'j'. The output before
October 15, 1582 in Oracle is
inconsistent with that in GaussDB.
● If there is no separator, the value
may be dierent from that in
Oracle. Take
to_date('220725','yymmdd') as an
example. If yy/rr is parsed based
on the xed length 4, the year is
parsed as 2207 and the month is
parsed as 25. The month 25 is
invalid, and an error will be
reported.
10 TO_MULTI_BYT
E
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 110

No. Oracle GaussDB Dierence
11 TO_NCHAR Supported, with
dierences.
● GaussDB: The input parameter
type is converted to text.
● Oracle: The input parameter type
is converted to the national
character set.
12 TO_NUMBER Supported, with
dierences.
GaussDB: The nlsparam parameter is
not supported.
13 TO_SINGLE_BY
TE
Supported. -
14 TREAT Supported, with
dierences.
GaussDB: The period (.) operator
cannot be used to obtain values, and
the values cannot be converted to the
object type.
15 UNISTR Supported, with
dierences.
GaussDB supports only UTF-8
encoding. Oracle supports UTF-8 and
UTF-16 encodings.
Table 7-85 Large object functions
No.
Oracle GaussDB Dierence
1 EMPTY_BLOB Supported. -
2 EMPTY_CLOB Supported, with
dierences.
GaussDB: The CLOB type does
not support the locator
concept in Oracle.
Table 7-86 Hierarchical functions
No.
Oracle GaussDB
1 SYS_CONNECT_BY_PATH Not supported.
Table 7-87 XML functions
No.
Oracle GaussDB Dierence
1 EXISTSNODE Supported, with
dierences.
If the input parameter has a
namespace, aliases must be dened
for both the XPath and namespace.
2 EXTRACTVAL
UE
Supported, with
dierences.
Currently, only XPath 1.0 is
supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 111

No. Oracle GaussDB Dierence
3 SYS_XMLAGG Supported, with
dierences.
This is an alias of xmlagg and can be
replaced with xmlagg.
4 XMLAGG Supported. -
5 XMLCOMME
NT
Supported. -
6 XMLCONCAT Supported. -
7 XMLELEMEN
T
Supported, with
dierences.
For xmlelement and xmlattributes,
when the value of name is NULL,
the database behavior is dierent
from that in Oracle.
● When the name column of
xmlelement is set to NULL, the
name information is empty and
the attribute information is not
displayed.
● When the name column of
xmlattributes is set to NULL, the
attribute information is not
displayed.
8 XMLEXISTS Supported, with
dierences.
GaussDB input parameter is of the
XML type.
9 XMLFOREST Supported, with
dierences.
GaussDB return value is of the XML
type.
GaussDB does not support the
EVALNAME syntax.
10 XMLPARSE Supported, with
dierences.
GaussDB return value is of the XML
type.
GaussDB does not support the
WELLFORMED syntax.
11 XMLROOT Supported, with
dierences.
GaussDB return value is of the XML
type.
12 JSON_OBJECT Supported. -
13 XMLTABLE Supported, with
dierences.
GaussDB: The XPath 1.0 expression is
used to select data from the XML
le. The default namespace cannot
be declared, multiple groups of
inputs and aliases cannot be
obtained, the passing_clause clause
of the input data cannot be omitted,
and the RETURNING SEQUENCE BY
REF and ( SEQUENCE ) BY REF
clauses are not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 112

No. Oracle GaussDB Dierence
14 GETSTRINGV
AL
Supported -
15 GETCLOBVAL Supported -
16 XMLSEQUEN
CE
Supported -
Table 7-88 Encoding and decoding functions
No. Oracle GaussDB Dierence
1 DECODE Supported. -
2 DUMP Supported, with
dierences.
The returned results of the numeric
and time types in GaussDB are
inconsistent with those in Oracle due
to dierent storage formats. In
GaussDB, select dump(123); returns
Typ=23 Len=4: 123,0,0,0. In Oracle,
select dump(123) from dual; returns
Typ=2 Len=3: 194,2,24.
3 ORA_HASH Supported, with
dierences.
GaussDB has the following behaviors:
● The input parameter of the time
type is converted into the character
string type and then hashed.
● The maxbucket parameter is not
supported.
4 VSIZE Supported, with
dierences.
The returned results of the numeric
and time types in GaussDB are
inconsistent with those in Oracle due
to dierent storage formats. In
GaussDB, select vsize(999); returns 4.
In Oracle, select vsize(999) from dual;
returns 3.
Table 7-89 Null-related functions
No.
Oracle GaussDB Dierence
1 COALESCE Supported. -
2 LNNVL Supported. -
3 NULLIF Supported. -
4 NVL Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 113

No. Oracle GaussDB Dierence
5 NVL2 Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 114

Table 7-90 Environment and identier functions
No. Oracle GaussDB Dierence
1 SYS_CONTEXT Supported, with
dierences.
GaussDB returns NULL for
unsupported parameters.
The following parameters
are not supported:
● 'action'
● 'is_application_root'
● 'is_application_pdb'
● 'audited_cursorid'
● 'authenticated_identity'
● 'authentication_data'
● 'authentication_method'
● 'cdb_domain'
● 'cdb_name'
● 'client_identier'
● 'con_id'
● 'con_name'
● 'current_sql_length'
● 'db_domain'
● 'db_supplemental_log_le
vel'
● 'dblink_info'
● 'drain_status'
● 'entryid'
● 'enterprise_identity'
● 'fg_job_id'
● 'global_uid'
● 'identication_type'
● 'instance'
● 'is_dg_rolling_upgrade'
● 'ldap_server_type'
● 'module'
● 'network_protocol'
● 'nls_calendar'
● 'nls_sort'
● 'nls_territory'
● 'oracle_home'
● 'os_user'
● 'platform_slash'
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 115

No. Oracle GaussDB Dierence
● 'policy_invoker'
● 'proxy_enterprise_identit
y'
● 'proxy_user'
● 'proxy_userid'
● 'scheduler_job'
● 'session_edition_id'
● 'session_edition_name'
● 'sessionid'
● 'statementid'
● 'terminal'
● 'unied_audit_sessionid'
● 'session_default_collation
'
● 'client_info'
● 'bg_job_id'
● 'client_program_name'
● 'current_bind'
● 'global_context_memory'
● 'host'
● 'current_sqln'
2
SYS_GUID Supported. -
3 USER Supported, with
dierences.
The return value types are
dierent.
7.1.10.2 Other Functions
No.
Oracle GaussDB
1 Aggregate functions Supported.
2 Analytic functions Supported.
3 Object reference
functions
Not supported.
4 Models functions Not supported.
5 OLAP functions Not supported.
6 Data cartridge functions Not supported.
7 User-dened functions Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 116

Table 7-91 Aggregate functions
No. Oracle GaussDB Dierence
1 AVG Supported. -
2 CORR Supported. -
3 COUNT Supported. -
4 COVAR_POP Supported. -
5 COVAR_SAMP Supported. -
6 CUME_DIST Supported. -
7 DENSE_RANK Supported. -
8 FIRST Supported. -
9 GROUPING Supported. -
10 LAST Supported. -
11 LISTAGG Supported. -
12 MAX Supported. -
13 MEDIAN Supported. -
14 MIN Supported. -
15 PERCENT_RA
NK
Supported. -
16 PERCENTILE_
CONT
Supported. -
17 RANK Supported. -
18 REGR_ (Linear
Regression)
Supported. -
19 STDDEV Supported. -
20 STDDEV_POP Supported. -
21 STDDEV_SAM
P
Supported. -
22 SUM Supported. -
23 VAR_POP Supported. -
24 VAR_SAMP Supported. -
25 VARIANCE Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 117

No. Oracle GaussDB Dierence
26 WM_CONCAT Supported, with
dierences.
The LISTAGG and
STRING_AGG functions
used in GaussDB are
compatible with Oracle.
Table 7-92 Analytic functions
No. Oracle GaussDB
1 FIRST_VALUE Supported.
2 LAG Supported.
3 LAST_VALUE Supported.
4 LEAD Supported.
5 NTH_VALUE Supported.
6 NTILE Supported.
7 ROW_NUMBER Supported.
8 RATIO_TO_REPORT Supported.
7.1.11 System Views
GaussDB is compatible with some Oracle system views, as shown in the following
table.
For details about columns in system views, see "System Views" in
Developer
Guide
.
Table 7-93 Supported system views
No.
Oracle GaussDB
1 ALL_ALL_TABLES DB_ALL_TABLES
2 ALL_COL_PRIVS DB_COL_PRIVS
3 ALL_COLL_TYPES DB_COLL_TYPES
4 ALL_IND_COLUMNS DB_IND_COLUMNS
5 ALL_COL_COMMENTS DB_COL_COMMENTS
6 ALL_CONS_COLUMNS DB_CONS_COLUMNS
7 ALL_CONSTRAINTS DB_CONSTRAINTS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 118
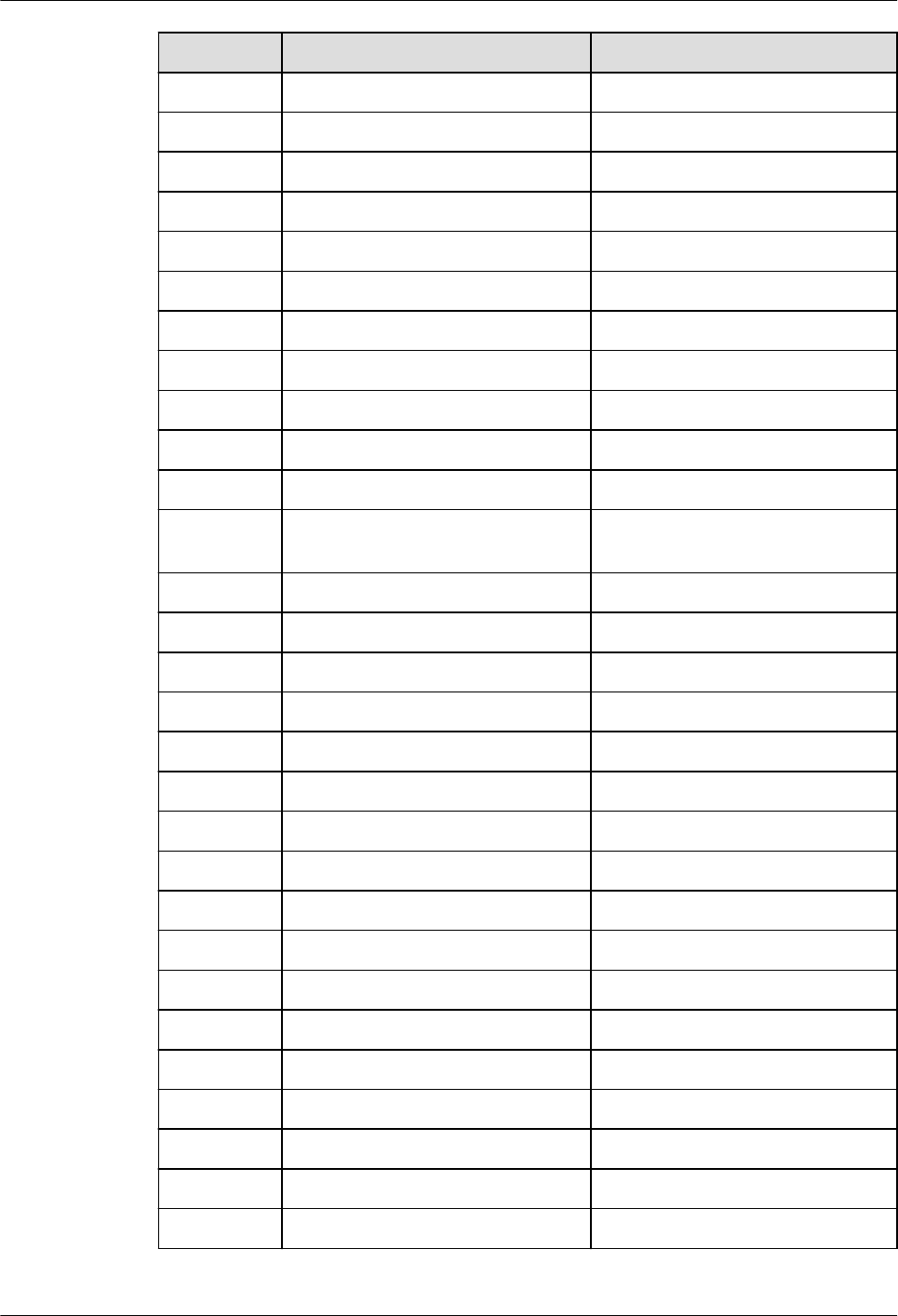
No. Oracle GaussDB
8 ALL_DEPENDENCIES DB_DEPENDENCIES
9 ALL_DIRECTORIES DB_DIRECTORIES
10 ALL_IND_EXPRESSIONS DB_IND_EXPRESSIONS
11 ALL_IND_PARTITIONS DB_IND_PARTITIONS
12 ALL_INDEXES DB_INDEXES
13 ALL_IND_SUBPARTITIONS DB_IND_SUBPARTITIONS
14 ALL_OBJECTS DB_OBJECTS
15 ALL_PART_COL_STATISTICS DB_PART_COL_STATISTICS
16 ALL_PART_KEY_COLUMNS DB_PART_KEY_COLUMNS
17 ALL_PART_TABLES DB_PART_TABLES
18 ALL_SCHEDULER_JOB_ARGS DB_SCHEDULER_JOB_ARGS
19 ALL_SCHEDULER_PROGRAM_AR
GS
DB_SCHEDULER_PROGRAM_AR
GS
20 ALL_SEQUENCES DB_SEQUENCES
21 ALL_SUBPART_KEY_COLUMNS DB_SUBPART_KEY_COLUMNS
22 ALL_SYNONYMS DB_SYNONYMS
23 ALL_TAB_COL_STATISTICS DB_TAB_COL_STATISTICS
24 ALL_TAB_COMMENTS DB_TAB_COMMENTS
25 ALL_TAB_HISTOGRAMS DB_TAB_HISTOGRAMS
26 ALL_TAB_STATS_HISTORY DB_TAB_STATS_HISTORY
27 ALL_TYPES DB_TYPES
28 ALL_PROCEDURES DB_PROCEDURES
29 ALL_SOURCE DB_SOURCE
30 ALL_TAB_COLUMNS DB_TAB_COLUMNS
31 ALL_TAB_PARTITIONS DB_TAB_PARTITIONS
32 ALL_TAB_SUBPARTITIONS DB_TAB_SUBPARTITIONS
33 ALL_TABLES DB_TABLES
34 ALL_TRIGGERS DB_TRIGGERS
35 ALL_USERS DB_USERS
36 ALL_VIEWS DB_VIEWS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 119
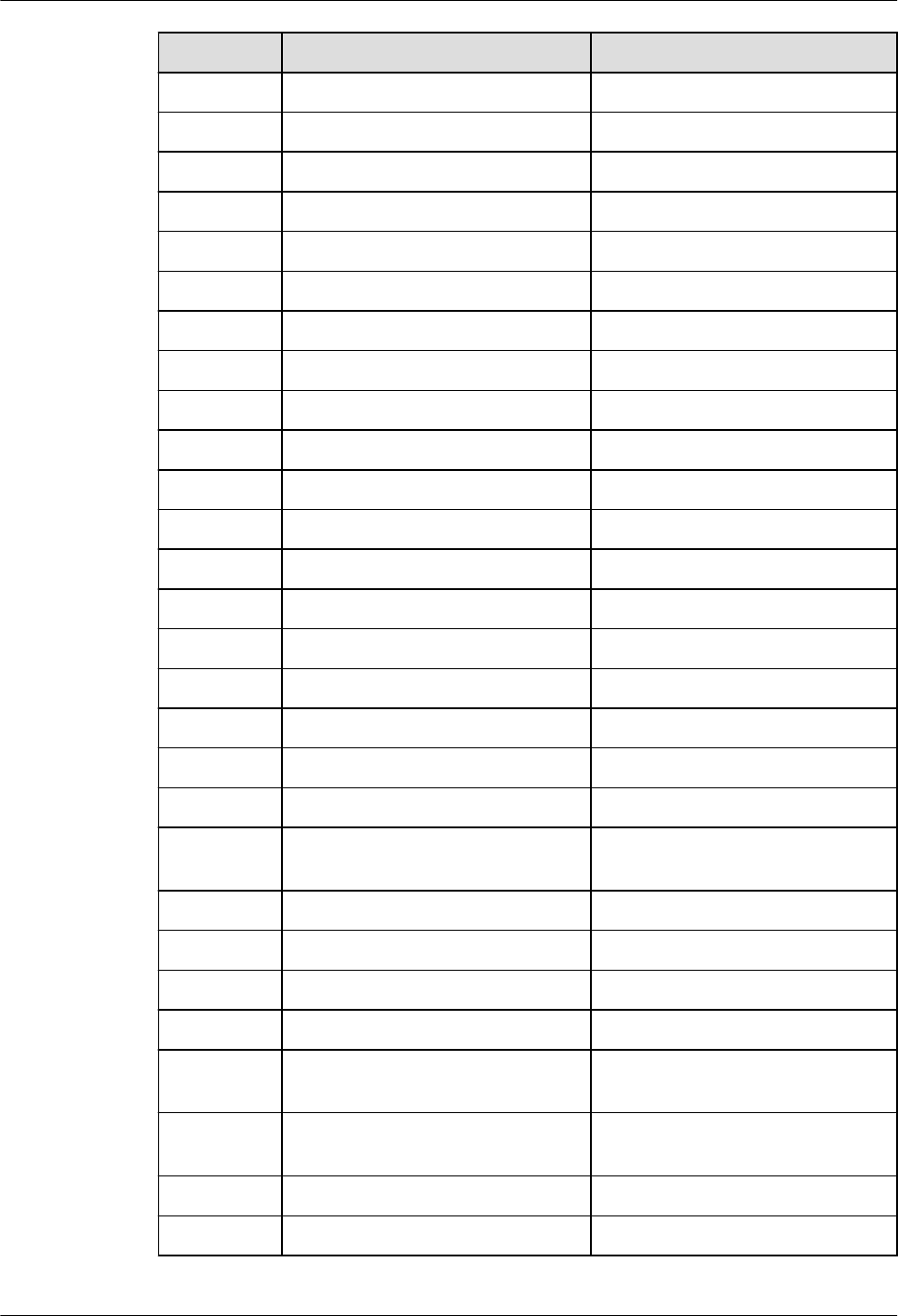
No. Oracle GaussDB
37 DBA_AUDIT_OBJECT ADM_AUDIT_OBJECT
38 DBA_AUDIT_SESSION ADM_AUDIT_SESSION
39 DBA_AUDIT_STATEMENT ADM_AUDIT_STATEMENT
40 DBA_AUDIT_TRAIL ADM_AUDIT_TRAIL
41 DBA_COL_COMMENTS ADM_COL_COMMENTS
42 DBA_COL_PRIVS ADM_COL_PRIVS
43 DBA_COLL_TYPES ADM_COLL_TYPES
44 DBA_ARGUMENTS ADM_ARGUMENTS
45 DBA_CONSTRAINTS ADM_CONSTRAINTS
46 DBA_DATA_FILES ADM_DATA_FILES
47 DBA_CONS_COLUMNS ADM_CONS_COLUMNS
48 DBA_DEPENDENCIES ADM_DEPENDENCIES
49 DBA_DIRECTORIES ADM_DIRECTORIES
50 DBA_PART_COL_STATISTICS ADM_PART_COL_STATISTICS
51 DBA_PART_TABLES ADM_PART_TABLES
52 DBA_ROLE_PRIVS ADM_ROLE_PRIVS
53 DBA_ROLES ADM_ROLES
54 DBA_SCHEDULER_JOB_ARGS ADM_SCHEDULER_JOB_ARGS
55 DBA_SCHEDULER_PROGRAMS ADM_SCHEDULER_PROGRAMS
56 DBA_SCHEDULER_PROGRAM_A
RGS
ADM_SCHEDULER_PROGRAM_
ARGS
57 DBA_HIST_SNAPSHOT ADM_HIST_SNAPSHOT
58 DBA_HIST_SQL_PLAN ADM_HIST_SQL_PLAN
59 DBA_HIST_SQLSTAT ADM_HIST_SQLSTAT
60 DBA_HIST_SQLTEXT ADM_HIST_SQLTEXT
61 DBA_ILMDATAMOVEMENTPO-
LICIES
GS_ADM_ILMDATAMOVEMENT
POLICIES
62 DBA_ILMEVALUATIONDETAILS GS_ADM_ILMEVALUATIONDE-
TAILS
63 DBA_ILMOBJECTS GS_ADM_ILMOBJECTS
64 DBA_ILMPARAMETERS GS_ADM_ILMPARAMETERS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 120

No. Oracle GaussDB
65 DBA_ILMPOLICIES GS_ADM_ILMPOLICIES
66 DBA_ILMRESULTS GS_ADM_ILMRESULTS
67 DBA_ILMTASKS GS_ADM_ILMTASKS
68 DBA_IND_COLUMNS ADM_IND_COLUMNS
69 DBA_IND_EXPRESSIONS ADM_IND_EXPRESSIONS
70 DBA_IND_PARTITIONS ADM_IND_PARTITIONS
71 DBA_INDEXES ADM_INDEXES
72 DBA_OBJECTS ADM_OBJECTS
73 DBA_PART_INDEXES ADM_PART_INDEXES
74 DBA_PROCEDURES ADM_PROCEDURES
75 DBA_SCHEDULER_JOBS ADM_SCHEDULER_JOBS
76 DBA_SCHEDULER_RUNNING_JO
BS
ADM_SCHEDULER_RUNNING_J
OBS
77 DBA_SEGMENTS ADM_SEGMENTS
78 DBA_SEQUENCES ADM_SEQUENCES
79 DBA_SOURCE ADM_SOURCE
80 DBA_IND_SUBPARTITIONS ADM_IND_SUBPARTITIONS
81 DBA_SUBPART_KEY_COLUMNS ADM_SUBPART_KEY_COLUMNS
82 DBA_SYS_PRIVS ADM_SYS_PRIVS
83 DBA_TAB_COL_STATISTICS ADM_TAB_COL_STATISTICS
84 DBA_TAB_HISTOGRAMS ADM_TAB_HISTOGRAMS
85 DBA_TAB_STATISTICS ADM_TAB_STATISTICS
86 DBA_TAB_STATS_HISTORY ADM_TAB_STATS_HISTORY
87 DBA_TABLESPACES ADM_TABLESPACES
88 DBA_TYPES ADM_TYPES
89 DBA_USERS ADM_USERS
90 DBA_SYNONYMS ADM_SYNONYMS
91 DBA_TAB_COLS ADM_TAB_COLS
92 DBA_TAB_COLUMNS ADM_TAB_COLUMNS
93 DBA_TAB_COMMENTS ADM_TAB_COMMENTS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 121

No. Oracle GaussDB
94 DBA_TABLES ADM_TABLES
95 DBA_TAB_PARTITIONS ADM_TAB_PARTITIONS
96 DBA_TAB_SUBPARTITIONS ADM_TAB_SUBPARTITIONS
97 DBA_TRIGGERS ADM_TRIGGERS
98 DBA_TYPE_ATTRS ADM_TYPE_ATTRS
99 DBA_VIEWS ADM_VIEWS
100 ROLE_ROLE_PRIVS ROLE_ROLE_PRIVS
101 ROLE_SYS_PRIVS ROLE_SYS_PRIVS
102 ROLE_TAB_PRIVS ROLE_TAB_PRIVS
103 USER_COL_COMMENTS MY_COL_COMMENTS
104 USER_COL_PRIVS MY_COL_PRIVS
105 USER_COLL_TYPES MY_COLL_TYPES
106 USER_CONSTRAINTS MY_CONSTRAINTS
107 USER_DEPENDENCIES MY_DEPENDENCIES
108 DICT DICT
109 DICTIONARY DICTIONARY
110 DUAL DUAL
111 NLS_DATABASE_PARAMETERS NLS_DATABASE_PARAMETERS
112 NLS_INSTANCE_PARAMETERS NLS_INSTANCE_PARAMETERS
113 PLAN_TABLE PLAN_TABLE
114 USER_ILMDATAMOVEMENTPO-
LICIES
GS_MY_ILMDATAMOVEMENT-
POLICIES
115 USER_ILMEVALUATIONDETAILS GS_MY_ILMEVALUATIONDE-
TAILS
116 USER_ILMOBJECTS GS_MY_ILMOBJECTS
117 USER_ILMPOLICIES GS_MY_ILMPOLICIES
118 USER_ILMRESULTS GS_MY_ILMRESULTS
119 USER_ILMTASKS GS_MY_ILMTASKS
120 USER_IND_COLUMNS MY_IND_COLUMNS
121 USER_IND_EXPRESSIONS MY_IND_EXPRESSIONS
122 USER_IND_PARTITIONS MY_IND_PARTITIONS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 122

No. Oracle GaussDB
123 USER_IND_SUBPARTITIONS MY_IND_SUBPARTITIONS
124 USER_INDEXES MY_INDEXES
125 USER_JOBS MY_JOBS
126 USER_OBJECTS MY_OBJECTS
127 USER_PART_COL_STATISTICS MY_PART_COL_STATISTICS
128 USER_PART_INDEXES MY_PART_INDEXES
129 USER_PART_TABLES MY_PART_TABLES
130 USER_PROCEDURES MY_PROCEDURES
131 USER_SCHEDULER_JOB_ARGS MY_SCHEDULER_JOB_ARGS
132 USER_SCHEDULER_PROGRAM_
ARGS
MY_SCHEDULER_PROGRAM_AR
GS
133 USER_SEQUENCES MY_SEQUENCES
134 USER_SOURCE MY_SOURCE
135 USER_SUBPART_KEY_COLUMNS MY_SUBPART_KEY_COLUMNS
136 USER_SYNONYMS MY_SYNONYMS
137 USER_SYS_PRIVS MY_SYS_PRIVS
138 USER_TAB_COL_STATISTICS MY_TAB_COL_STATISTICS
139 USER_TAB_COLUMNS MY_TAB_COLUMNS
140 USER_TAB_COMMENTS MY_TAB_COMMENTS
141 USER_TAB_HISTOGRAMS MY_TAB_HISTOGRAMS
142 USER_TAB_PARTITIONS MY_TAB_PARTITIONS
143 USER_TAB_STATISTICS MY_TAB_STATISTICS
144 USER_TAB_STATS_HISTORY MY_TAB_STATS_HISTORY
145 USER_TABLES MY_TABLES
146 USER_TABLESPACES MY_TABLESPACES
147 USER_TRIGGERS MY_TRIGGERS
148 USER_TYPE_ATTRS MY_TYPE_ATTRS
149 USER_TYPES MY_TYPES
150 USER_VIEWS MY_VIEWS
151 V$NLS_PARAMETERS V$NLS_PARAMETERS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 123

No. Oracle GaussDB
152 V$SESSION_WAIT V$SESSION_WAIT
153 V$SYSSTAT V$SYSSTAT
154 V$SYSTEM_EVENT V$SYSTEM_EVENT
155 V$VERSION V$VERSION
156 V$INSTANCE V_INSTANCE
157 GV$INSTANCE GV_INSTANCE
158 V$MYSTAT V_MYSTAT
159 V$SESSION V_SESSION
160 GV$SESSION GV_SESSION
161 V$SESSION_LONGOPS DV_SESSION_LONGOPS
162 V$SESSION DV_SESSIONS
163 ALL_ARGUMENTS DB_ARGUMENTS
164 USER_CONS_COLUMNS MY_CONS_COLUMNS
165 USER_PART_KEY_COLUMNS MY_PART_KEY_COLUMNS
166 USER_ROLE_PRIVS MY_ROLE_PRIVS
167 DBA_TAB_PRIVS ADM_TAB_PRIVS
168 USER_SCHEDULER_JOBS MY_SCHEDULER_JOBS
169 V$LOCK V$LOCK
170 V$DBLINK V$DBLINK
171 V$GLOBAL_TRANSACTION V$GLOBAL_TRANSACTION
172 V$OPEN_CURSOR V$OPEN_CURSOR
173 V$GLOBAL_OPEN_CURSOR V$GLOBAL_OPEN_CURSOR
174 ALL_TAB_PRIVS DB_TAB_PRIVS
175 ALL_TAB_MODIFICATIONS DB_TAB_MODIFICATIONS
176 USER_TAB_MODIFICATIONS MY_TAB_MODIFICATIONS
177 USER_AUDIT_TRAIL MY_AUDIT_TRAIL
7.1.12 Advanced Packages
GaussDB is compatible with some Oracle advanced packages, as shown in the
following table.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 124

For more information about the advanced packages, see "Advanced Packages" in
Developer Guide
.
Table 7-94 Supported advanced packages
No. Oracle GaussDB Dierence
1 DBMS_LOB DBE_LOB For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_LOB" in
Developer Guide
.
2 DBMS_RANDOM DBE_RANDOM For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_RANDOM"
in
Developer
Guide
.
3 DBMS_OUTPUT DBE_OUTPUT For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_OUTPUT"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 125
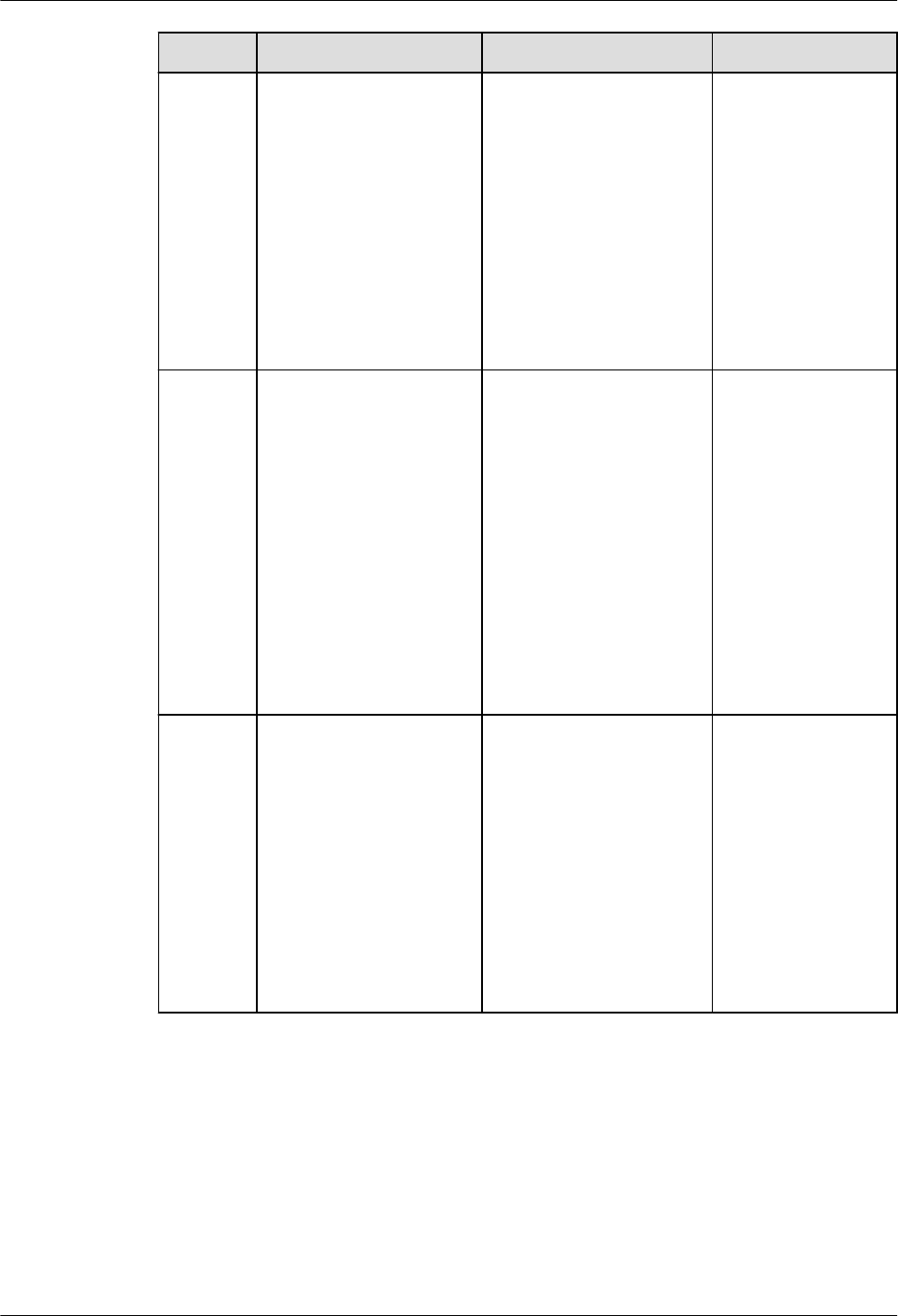
No. Oracle GaussDB Dierence
4 UTL_RAW DBE_RAW For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_RAW" in
Developer Guide
.
5 DBMS_SCHEDULER DBE_SCHEDULER For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_SCHEDULER"
in
Developer
Guide
.
6 DBMS_UTILITY DBE_UTILITY For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_UTILITY" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 126
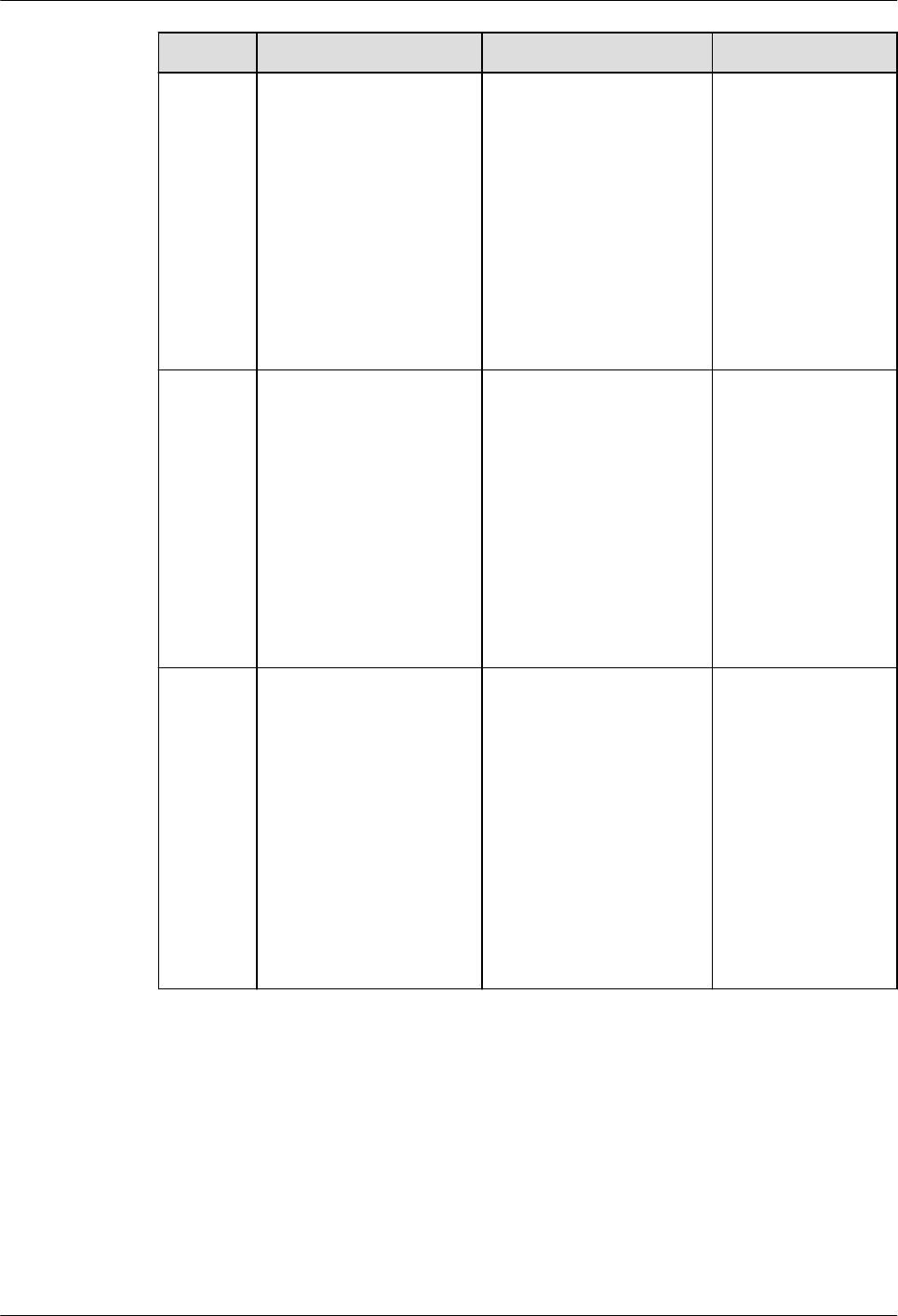
No. Oracle GaussDB Dierence
7 DBMS_SQL DBE_SQL For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_SQL" in
Developer Guide
.
8 UTL_FILE DBE_FILE For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_FILE" in
Developer Guide
.
9 DBMS_SESSION DBE_SESSION For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_SESSION"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 127

No. Oracle GaussDB Dierence
10 UTL_MATCH DBE_MATCH For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_MATCH" in
Developer Guide
.
11 DBMS_APPLICATION_
INFO
DBE_APPLICATION_INF
O
For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_APPLICATIO
N_INFO" in
Developer Guide
.
12 DBMS_XMLDOM DBE_XMLDOM For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_XMLDOM"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 128

No. Oracle GaussDB Dierence
13 DBMS_XMLPARSER DBE_XMLPARSER For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_XMLPARSER"
in
Developer
Guide
.
14 DBMS_ILM DBE_ILM For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_ILM" in
Developer Guide
.
15 DBMS_ILM_ADMIN DBE_ILM_ADMIN For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_ILM_ADMIN"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 129

No. Oracle GaussDB Dierence
16 DBMS_COMPRESSIO
N
DBE_COMPRESSION For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_COMPRESSI
ON" in
Developer
Guide
.
17 DBMS_HEAT_MAP DBE_HEAT_MAP For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_HEAT_MAP"
in
Developer
Guide
.
18 DBMS_DESCRIBE DBE_DESCRIBE For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_DESCRIPBE"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 130

No. Oracle GaussDB Dierence
19 DBMS_XMLGEN DBE_XMLGEN For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_XMLGEN"
in
Developer
Guide
.
20 DBMS_STATS DBE_STATS For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_STATS" in
Developer Guide
.
Table 7-95 DBMS_LOB compatibility
No.
Oracle GaussDB Dierence
1 APPEND Procedures APPEND Procedures -
2 CLOB2FILE Procedure Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 131

No. Oracle GaussDB Dierence
3 CLOSE Procedure BFILECLOSE
Procedure
GaussDB: The
parameter
type is BFILE,
and no
function
overloading
exists.
Oracle: There
are three
overloaded
procedures.
The
procedures
have three
parameters
lob_loc,
lob_loc, and
le_loc,
which are of
the BLOB,
CLOB
CHARACTER
SET ANY_CS,
and BFILE
types,
respectively.
4
COMPARE Functions COMPARE
Functions
GaussDB:
There are
three
overloaded
functions. The
third
parameter
(len) is of the
BIGINT type.
Oracle: There
are three
overloaded
functions. The
third
parameter
(amount) is
of the
INTEGER type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 132

No. Oracle GaussDB Dierence
5 CONVERTTOBLOB
Procedure
LOB_CONVERTTOB
LOB Procedure
GaussDB: This
procedure has
ve
parameters,
and the third,
fourth, and
fth
parameters
are of the
BIGINT type.
Oracle: This
procedure has
eight
parameters.
In addition to
all GaussDB
parameters,
the blob_csid,
lang_context,
and warning
parameters
are added,
which are of
the NUMBER,
INTEGER, and
INTEGER
types,
respectively.
The third,
fourth, and
fth
parameters
are of the
INTEGER type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 133

No. Oracle GaussDB Dierence
6 CONVERTTOCLOB
Procedure
LOB_CONVERTTOC
LOB Procedure
GaussDB: This
procedure has
ve
parameters.
The third,
fourth, and
fth
parameters
are of the
BIGINT type.
Oracle: This
procedure has
eight
parameters.
The third,
fourth, and
fth
parameters
are of the
INTEGER type.
In addition to
all GaussDB
parameters,
this procedure
in Oracle adds
three
parameters:
blob_csid,
lang_context,
and warning,
which are of
NUMBER,
INTEGER, and
INTEGER
types,
respectively.
7
COPY Procedures LOB_COPY
Functions
-
8 COPY_DBFS_LINK
Procedures
Not supported -
9 COPY_FROM_DBFS_LINK Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 134
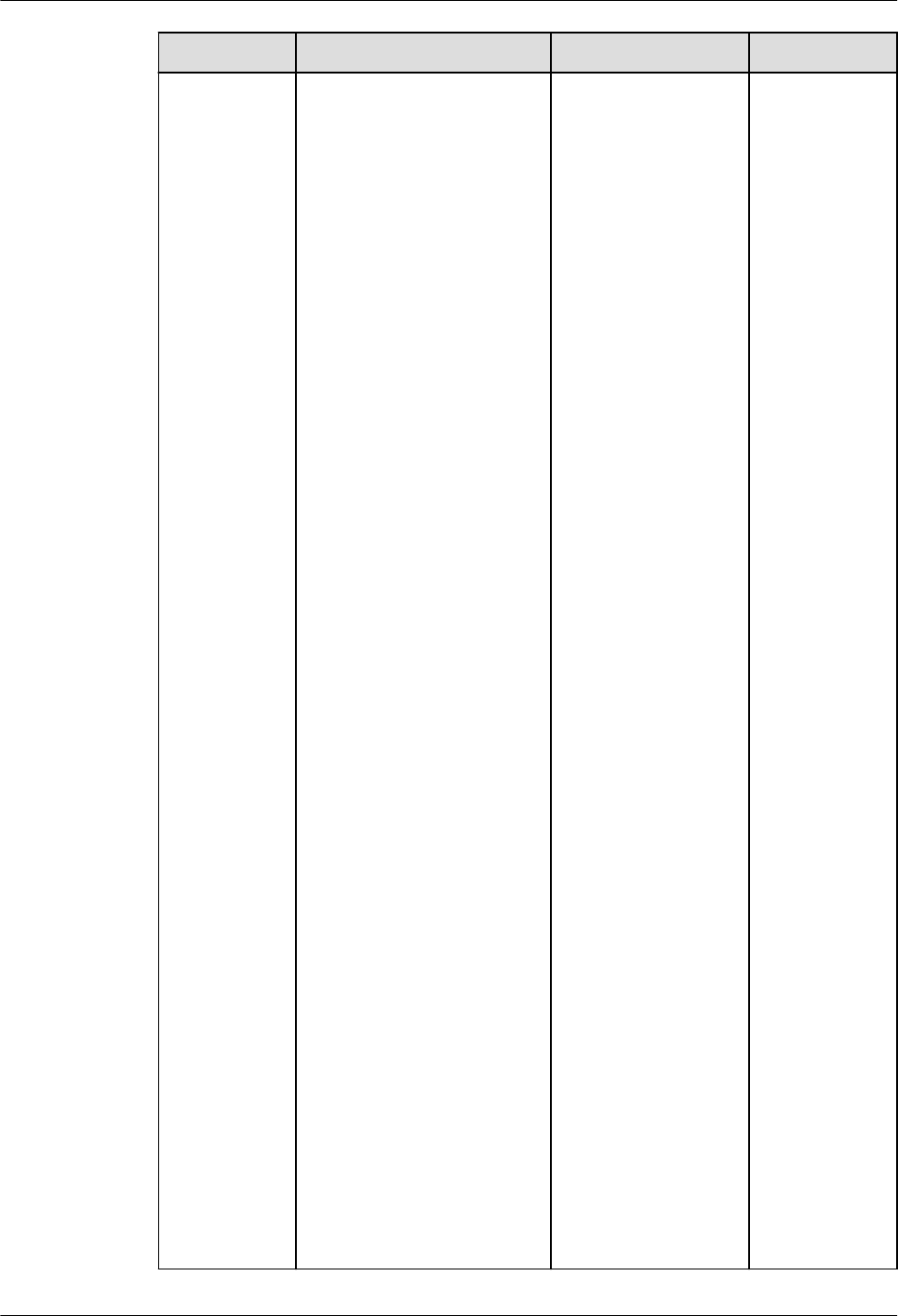
No. Oracle GaussDB Dierence
10 CREATETEMPOracleRY
Procedures
CREATE_TEMPOracl
eRY Procedures
GaussDB:
There are two
overloaded
procedures.
The rst
parameter
(lob_loc) of
the rst
overloaded
procedure is
of the BLOB
type, and the
rst
parameter
(lob_loc) of
the second
overloaded
procedure is
of the CLOB
type. The
third
parameter
(dur) of the
two
overloaded
procedures is
of the
INTEGER type,
and the
default value
is 10.
Oracle: There
are two
overloaded
procedures.
The rst
parameter
(lob_loc) of
the rst
overloaded
procedure is
of the BLOB
type. The rst
parameter
(lob_loc) of
the second
overloaded
procedure is
of the CLOB
type. The
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 135

No. Oracle GaussDB Dierence
third
parameter
(dur) of the
two
overloaded
procedures is
of the
PLS_INTEGER
type. The
default value
of dur of the
rst
overloaded
procedure is
DBMS_LOB.S
ESSION, and
the default
value of dur
of the second
overloaded
procedure is
10.
11
DBFS_LINK_GENERATE_P
ATH Functions
Not supported -
12 ERASE Procedures LOB_ERASE
Procedures
-
13 FILECLOSE Procedure Not supported -
14 FILECLOSEALL Procedure Not supported -
15 FILEEXISTS Function Not supported -
16 FILEGETNAME Procedure Not supported -
17 FILEISOPEN Function Not supported -
18 FILEOPEN Procedure Not supported -
19 FRAGMENT_DELETE
Procedure
Not supported -
20 FRAGMENT_INSERT
Procedures
Not supported -
21 FRAGMENT_MOVE
Procedure
Not supported -
22 FRAGMENT_REPLACE
Procedures
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 136

No. Oracle GaussDB Dierence
23 FREETEMPOracleRY
Procedures
Not supported -
24 GET_DBFS_LINK Functions Not supported -
25 GET_DBFS_LINK_STATE
Procedures
Not supported -
26 GETCHUNKSIZE Functions GETCHUNKSIZE
Functions
-
27 GETCONTENTTYPE
Functions
Not supported -
28 GETLENGTH Functions Not supported -
29 GETOPTIONS Functions Not supported -
30 GET_STOracleGE_LIMIT
Function
Not supported -
31 INSTR Functions MATCH Functions GaussDB:
There are
three
overloaded
functions. The
third and
fourth
parameters of
the three
overloaded
functions are
of the BIGINT
type.
Oracle: There
are three
overloaded
functions. The
third and
fourth
parameters of
the three
overloaded
functions are
of the
INTEGER type.
32
ISOPEN Functions Not supported -
33 ISREMOTE Function Not supported -
34 ISSECUREFILE Function Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 137

No. Oracle GaussDB Dierence
35 ISTEMPOracleRY
Functions
Not supported -
36 LOADBLOBFROMFILE
Procedure
LOADBLOBFROMFI
LE Procedure
-
37 LOADCLOBFROMFILE
Procedure
LOADCLOBFROMFI
LE Procedure
-
38 LOADFROMFILE
Procedure
LOADFROMFILE
Procedure
-
39 MOVE_TO_DBFS_LINK
Procedures
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 138
No. Oracle GaussDB Dierence
40 OPEN Procedures BFILEOPEN
Procedure
GaussDB:
There is no
overloaded
procedure.
The rst
parameter
(ble) is of
the
DBE_LOB.BFIL
E type, and
the second
parameter
(open_mode)
is of the TEXT
type. Only the
read mode is
supported.
Oracle: There
are three
overloaded
procedures. In
the rst
overloaded
procedure,
the rst
parameter
(lob_loc) is of
the NOCOPY
BLOB type,
and the
second
parameter
(openmode)
is of the
BINARY_INTE
GER type. In
the second
overloaded
procedure,
the rst
parameter
(lob_loc) is of
the NOCOPY
CLOB
CHARACTER
SET ANY_CS
type, and the
second
parameter
(openmode)
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 139

No. Oracle GaussDB Dierence
is of the
BINARY_INTE
GER type. In
the third
overloaded
procedure,
the rst
parameter
(le_loc) is of
the NOCOPY
BFILE type,
and the
second
parameter
(openmode)
is of the
BINARY_INTE
GER type, and
the value can
only be
le_readonly.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 140

No. Oracle GaussDB Dierence
41 READ Procedures READ Procedures GaussDB:
There are two
overloaded
procedures.
Oracle: There
are three
overloaded
procedures.
The rst two
overloaded
procedures
are the same
as those in
GaussDB. The
third
overloaded
procedure
includes four
parameters:
le_loc,
amount,
oset, and
buer, which
are of the
BFILE,
NOCOPY
INTEGER,
INTEGER, and
RAW types,
respectively.
42
SET_DBFS_LINK
Procedures
Not supported -
43 SETCONTENTTYPE
Procedure
Not supported -
44 SETOPTIONS Procedures Not supported -
45 SUBSTR Functions LOB_SUBSTR
Functions
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 141

No. Oracle GaussDB Dierence
46 TRIM Procedures STRIP Functions GaussDB:
There are two
overloaded
procedures.
The second
parameter
(newlen) of
the two
overloaded
procedures is
of the BIGINT
type.
Oracle: There
are two
overloaded
procedures.
The second
parameter
(newlen) of
the two
overloaded
procedures is
of the
INTEGER type.
47
WRITE Procedures WRITE Functions -
48 WRITEAPPEND
Procedures
WRITEAPPEND
Functions
-
Table 7-96 DBMS_RANDOM compatibility
No.
Oracle GaussDB Dierence
1 INITIALIZE Procedure Not supported -
2 NORMAL Function Not supported -
3 RANDOM Function Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 142

No. Oracle GaussDB Dierence
4 SEED Procedures DBE_RANDOM.SET_
SEED Function
GaussDB:
There is no
overloaded
function. The
parameter is
of the
INTEGER
type.
Oracle: There
are two
overloaded
procedures.
The
parameter
types of the
two
overloaded
procedures
are
VARCHAR2
and
BINARY_INTE
GER,
respectively.
5
STRING Function Not supported -
6 TERMINATE Procedure Not supported -
7 VALUE Functions DBE_RANDOM.GET
_VALUE Function
GaussDB:
There is no
overloaded
function.
Oracle: The
VALUE
function
without
parameters is
overloaded,
and the
return type is
NUMBER.
Table 7-97 DBMS_OUTPUT compatibility
No.
Oracle GaussDB Dierence
1 DISABLE Procedure DISABLE Function -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 143

No. Oracle GaussDB Dierence
2 ENABLE Procedure ENABLE Function -
3 GET_LINE Procedure GET_LINE Function
GaussDB:
There is no
overloaded
function. The
rst
parameter
(lines) is of
the
VARCHAR[]
type.
Oracle: There
are two
overloaded
procedures.
The rst
parameters
(lines) of the
two
overloaded
procedures
are of the
CHARARR
and
DBMSOUTPU
T_LINESARRA
Y types,
respectively.
4
GET_LINES Procedure GET_LINES Function -
5 NEW_LINE Procedure NEW_LINE Function -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 144

No. Oracle GaussDB Dierence
6 PUT Procedure PUT Function GaussDB: If
the character
set of the
database
server
(server_enco
ding) is not
encoded in
UTF-8 and
the character
encoding of
the input
parameter is
valid UTF-8,
this function
converts
character
encoding
based on the
relationship
"UTF8 >
server_encodi
ng" and then
outputs the
result
regardless of
the data type
of the input
parameter.
Oracle: If the
character set
of the
database
server
(server_enco
ding) is not
encoded in
UTF-8, the
character
encoding of
the input
parameter is
valid UTF-8,
and the input
parameter
type is
NVARCHAR2,
this
procedure
coverts the
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 145

No. Oracle GaussDB Dierence
character
encoding
based on the
relationship
"UTF8 >
server_encodi
ng" and then
outputs the
result. If the
input
parameter is
of other
character
types, the
character
encoding is
regarded as
an invalid
character and
output as a
placeholder.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 146

No. Oracle GaussDB Dierence
7 PUT_LINE Procedure PUT_LINE Function GaussDB: If
the character
set of the
database
server
(server_enco
ding) is not
encoded in
UTF-8 and
the character
encoding of
the input
parameter is
valid UTF-8,
this function
converts
character
encoding
based on the
relationship
"UTF8 >
server_encodi
ng" and then
outputs the
result
regardless of
the data type
of the input
parameter.
Oracle: If the
character set
of the
database
server
(server_enco
ding) is not
encoded in
UTF-8, the
character
encoding of
the input
parameter is
valid UTF-8,
and the input
parameter
type is
NVARCHAR2,
this
procedure
coverts the
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 147

No. Oracle GaussDB Dierence
character
encoding
based on the
relationship
"UTF8 >
server_encodi
ng" and then
outputs the
result. If the
input
parameter is
of other
character
types, the
character
encoding is
regarded as
an invalid
character and
output as a
placeholder.
Table 7-98 UTL_RAW compatibility
No.
Oracle GaussDB Dierence
1 BIT_AND
Function
BIT_AND Function -
2 BIT_COMPLE
MENT
Function
BIT_COMPLEMENT
Function
-
3 BIT_OR
Function
BIT_OR Function GaussDB: The two parameters
are dened as the TEXT type
and returned as the TEXT
type.
Oracle: The two parameters
are of the RAW type and
returned as the RAW type.
4 BIT_XOR
Function
BIT_XOR Function -
5 CAST_FROM_
BINARY_DOU
BLE Function
CAST_FROM_BINARY_
DOUBLE_TO_RAW
Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 148

No. Oracle GaussDB Dierence
6 CAST_FROM_
BINARY_FLOA
T Function
CAST_FROM_BINARY_
FLOAT_TO_RAW
Function
GaussDB: The n parameter is
of the FLOAT4 type.
Oracle: The n parameter is of
the FLOAT type.
7 CAST_FROM_
BINARY_INTE
GER Function
CAST_FROM_BINARY_I
NTEGER_TO_RAW
Function
GaussDB: The value
parameter is of the BIGINT
type.
Oracle: The value parameter
is of the INTEGER type.
8 CAST_FROM_
NUMBER
Function
CAST_FROM_NUMBER
_TO_RAW Function
GaussDB: The n parameter is
of the NUMERIC type.
Oracle: The n parameter is of
the NUMBER type.
9 CAST_TO_BIN
ARY_DOUBLE
Function
CAST_FROM_RAW_TO
_BINARY_DOUBLE
Function
-
10 CAST_TO_BIN
ARY_FLOAT
Function
CAST_FROM_RAW_TO
_BINARY_FLOAT
Function
GaussDB: The function returns
the FLOAT4 type.
Oracle: The function returns
the FLOAT type.
11 CAST_TO_BIN
ARY_INTEGER
Function
CAST_FROM_RAW_TO
_BINARY_INTEGER
Function
GaussDB: The endianess
parameter is of the INTEGER
type, and the function returns
the INTEGER type.
Oracle: The endianess
parameter is of the
PLS_INTEGER type, and the
function returns the
BINARY_INTEGER type.
12 CAST_TO_NU
MBER
Function
CAST_FROM_RAW_TO
_NUMBER Function
GaussDB: The function returns
the NUMERIC type.
Oracle: The function returns
the NUMBER type.
13 CAST_TO_NV
ARCHAR2
Function
CAST_FROM_RAW_TO
_NVARCHAR2
Function
-
14 CAST_TO_RA
W Function
CAST_FROM_VARCHA
R2_TO_RAW Function
-
15 CAST_TO_VAR
CHAR2
Function
CAST_TO_VARCHAR2
Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 149

No. Oracle GaussDB Dierence
16 COMPARE
Function
COMPARE Function GaussDB: The function returns
the INTEGER type.
Oracle: The function returns
the NUMBER type.
17 CONCAT
Function
CONCAT Function -
18 CONVERT
Function
CONVERT Function -
19 COPIES
Function
COPIES Function GaussDB: The n parameter is
of the NUMERIC type.
Oracle: The n parameter is of
the NUMBER type.
20 LENGTH
Function
GET_LENGTH Function -
21 OVERLAY
Function
OVERLAY Function -
22 REVERSE
Function
REVERSE Function -
23 SUBSTR
Function
SUBSTR Function GaussDB: The lob_loc
parameter is of the BLOB
type. The o_set parameter is
of the INTEGER type and its
default value is 1. The
amount parameter is of the
INTEGER type and its default
value is 32767.
Oracle: The r parameter is of
the RAW type. The pos
parameter is of the
BINARY_INTEGER type and
has no default value. The len
parameter is of the
BINARY_INTEGER type and its
default value is NULL.
24 TRANSLATE
Function
TRANSLATE Function -
25 TRANSLITERA
TE Function
TRANSLITERATE
Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 150

No. Oracle GaussDB Dierence
26 XRANGE
Function
XRANGE Function GaussDB: The start_byte and
end_byte parameters do not
have default values.
Oracle: The default values of
the start_byte and end_byte
parameters are NULL.
Table 7-99 DBMS_SCHEDULER compatibility
No. Oracle GaussDB
1 ADD_EVENT_QUEUE_SUBSCRIBE
R Procedure
Not supported.
2 ADD_GROUP_MEMBER
Procedure
Not supported.
3 ADD_JOB_EMAIL_NOTIFICATION
Procedure
Not supported.
4 ADD_TO_INCOMPATIBILITY
Procedure
Not supported.
5 ALTER_CHAIN Procedure Not supported.
6 ALTER_RUNNING_CHAIN
Procedure
Not supported.
7 CLOSE_WINDOW Procedure Not supported.
8 COPY_JOB Procedure Not supported.
9 CREATE_CHAIN Procedure Not supported.
10 CREATE_CREDENTIAL Procedure CREATE_CREDENTIAL
Procedure
11 CREATE_DATABASE_DESTINATI
ON Procedure
Not supported.
12 CREATE_EVENT_SCHEDULE
Procedure
Not supported.
13 CREATE_FILE_WATCHER
Procedure
Not supported.
14 CREATE_GROUP Procedure Not supported.
15 CREATE_INCOMPATIBILITY
Procedure
Not supported.
16 CREATE_JOB Procedure CREATE_JOB Procedure
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 151

No. Oracle GaussDB
17 CREATE_JOB_CLASS Procedure CREATE_JOB_CLASS
Procedure
18 CREATE_JOBS Procedure Not supported.
19 CREATE_PROGRAM Procedure CREATE_PROGRAM
Procedure
20 CREATE_RESOURCE Procedure Not supported.
21 CREATE_SCHEDULE Procedure CREATE_SCHEDULE
Procedure
22 CREATE_WINDOW Procedure Not supported.
23 DEFINE_ANYDATA_ARGUMENT
Procedure
Not supported.
24 DEFINE_CHAIN_EVENT_STEP
Procedure
Not supported.
25 DEFINE_CHAIN_RULE Procedure Not supported.
26 DEFINE_CHAIN_STEP Procedure Not supported.
27 DEFINE_METADATA_ARGUMENT
Procedure
Not supported.
28 DEFINE_PROGRAM_ARGUMENT
Procedure
DEFINE_PROGRAM_ARGU
MENT Procedure
29 DISABLE Procedure DISABLE Procedure
30 DROP_AGENT_DESTINATION
Procedure
Not supported.
31 DROP_CHAIN Procedure Not supported.
32 DROP_CHAIN_RULE Procedure Not supported.
33 DROP_CHAIN_STEP Procedure Not supported.
34 DROP_CREDENTIAL Procedure DROP_CREDENTIAL
Procedure
35 DROP_DATABASE_DESTINATION
Procedure
Not supported.
36 DROP_FILE_WATCHER Procedure Not supported.
37 DROP_GROUP Procedure Not supported.
38 DROP_INCOMPATIBILITY
Procedure
Not supported.
39 DROP_JOB Procedure DROP_JOB Procedure
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 152

No. Oracle GaussDB
40 DROP_JOB_CLASS Procedure DROP_JOB_CLASS
Procedure
41 DROP_PROGRAM Procedure DROP_PROGRAM
Procedure
42 DROP_PROGRAM_ARGUMENT
Procedure
Not supported.
43 DROP_SCHEDULE Procedure DROP_SCHEDULE
Procedure
44 DROP_WINDOW Procedure Not supported.
45 ENABLE Procedure ENABLE Procedure
46 END_DETACHED_JOB_RUN
Procedure
Not supported.
47 EVALUATE_CALENDAR_STRING
Procedure
EVALUATE_CALENDAR_ST
RING Procedure
48 EVALUATE_RUNNING_CHAIN
Procedure
Not supported.
49 GENERATE_JOB_NAME Function GENERATE_JOB_NAME
Function
50 GET_AGENT_INFO Function Not supported.
51 GET_AGENT_VERSION Function Not supported.
52 GET_ATTRIBUTE Procedure Not supported.
53 GET_FILE Procedure Not supported.
54 GET_SCHEDULER_ATTRIBUTE
Procedure
Not supported.
55 OPEN_WINDOW Procedure Not supported.
56 PURGE_LOG Procedure Not supported.
57 PUT_FILE Procedure Not supported.
58 REMOVE_EVENT_QUEUE_SUBSC
RIBER Procedure
Not supported.
59 REMOVE_FROM_INCOMPATIBILI
TY Procedure
Not supported.
60 REMOVE_GROUP_MEMBER
Procedure
Not supported.
61 REMOVE_JOB_EMAIL_NOTIFICA
TION Procedure
Not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 153

No. Oracle GaussDB
62 RESET_JOB_ARGUMENT_VALUE
Procedure
Not supported.
63 RUN_CHAIN Procedure Not supported.
64 RUN_JOB Procedure RUN_JOB Procedure
65 SET_AGENT_REGISTRATION_PAS
S Procedure
Not supported.
66 SET_ATTRIBUTE Procedure SET_ATTRIBUTE
Procedure
67 SET_ATTRIBUTE_NULL
Procedure
Not supported.
68 SET_JOB_ANYDATA_VALUE
Procedure
Not supported.
69 SET_JOB_ARGUMENT_VALUE
Procedure
SET_JOB_ARGUMENT_VAL
UE Procedure
70 SET_JOB_ATTRIBUTES Procedure Not supported.
71 SET_RESOURCE_CONSTRAINT
Procedure
Not supported.
72 SET_SCHEDULER_ATTRIBUTE
Procedure
Not supported.
73 STOP_JOB Procedure STOP_JOB Procedure
Table 7-100 DBMS_UTILITY compatibility
No.
Oracle GaussDB Dierence
1 ACTIVE_INSTANCES
Procedure
Not supported -
2 ANALYZE_DATABASE
Procedure
Not supported -
3 ANALYZE_PART_OBJECT
Procedure
Not supported -
4 ANALYZE_SCHEMA
Procedure
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 154

No. Oracle GaussDB Dierence
5 CANONICALIZE
Procedure
CANONICALIZE
Procedure
GaussDB: The
default size of the
canon_len
parameter is 1024
bytes.
Oracle: The
canon_len
parameter has no
default value.
6 COMMA_TO_TABLE
Procedures
COMMA_TO_TABLE
Procedures
GaussDB: The tab
parameter is a
VARCHAR2 array.
Oracle: There are
two overloaded
procedures. The
tab parameter can
be of the
uncl_array or
lname_array type.
7 COMPILE_SCHEMA
Procedure
Not supported -
8 CREATE_ALTER_TYPE_ER
ROR_TABLE Procedure
Not supported -
9 CURRENT_INSTANCE
Function
Not supported -
10 DATA_BLOCK_ADDRESS_
BLOCK Function
Not supported -
11 DATA_BLOCK_ADDRESS_
FILE Function
Not supported -
12 DB_VERSION Procedure DB_VERSION
Procedure
GaussDB: There is
only the version
parameter, which is
of the VARCHAR2
type. Oracle: There
are the version
and compatibility
parameters, which
are of the
VARCHAR2 type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 155

No. Oracle GaussDB Dierence
13 EXEC_DDL_STATEMENT
Procedure
EXEC_DDL_STATEM
ENT Function
GaussDB: The
parse_string
parameter is of the
TEXT type.
Oracle: The
parse_string
parameter is of the
VARCHAR2 type.
14 EXPAND_SQL_TEXT
Procedure
EXPAND_SQL_TEXT
Function
GaussDB: The
output_sql_text
parameter is of the
CLOB type.
Oracle: The
output_sql_text
parameter is of the
NOCOPY CLOB
type. The OUT
parameter is
transferred by
reference.
15 FORMAT_CALL_STACK
Function
FORMAT_CALL_STA
CK Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
16 FORMAT_ERROR_BACKT
RACE Function
FORMAT_ERROR_B
ACKTRACE Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
17 FORMAT_ERROR_STACK
Function
FORMAT_ERROR_S
TACK Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 156
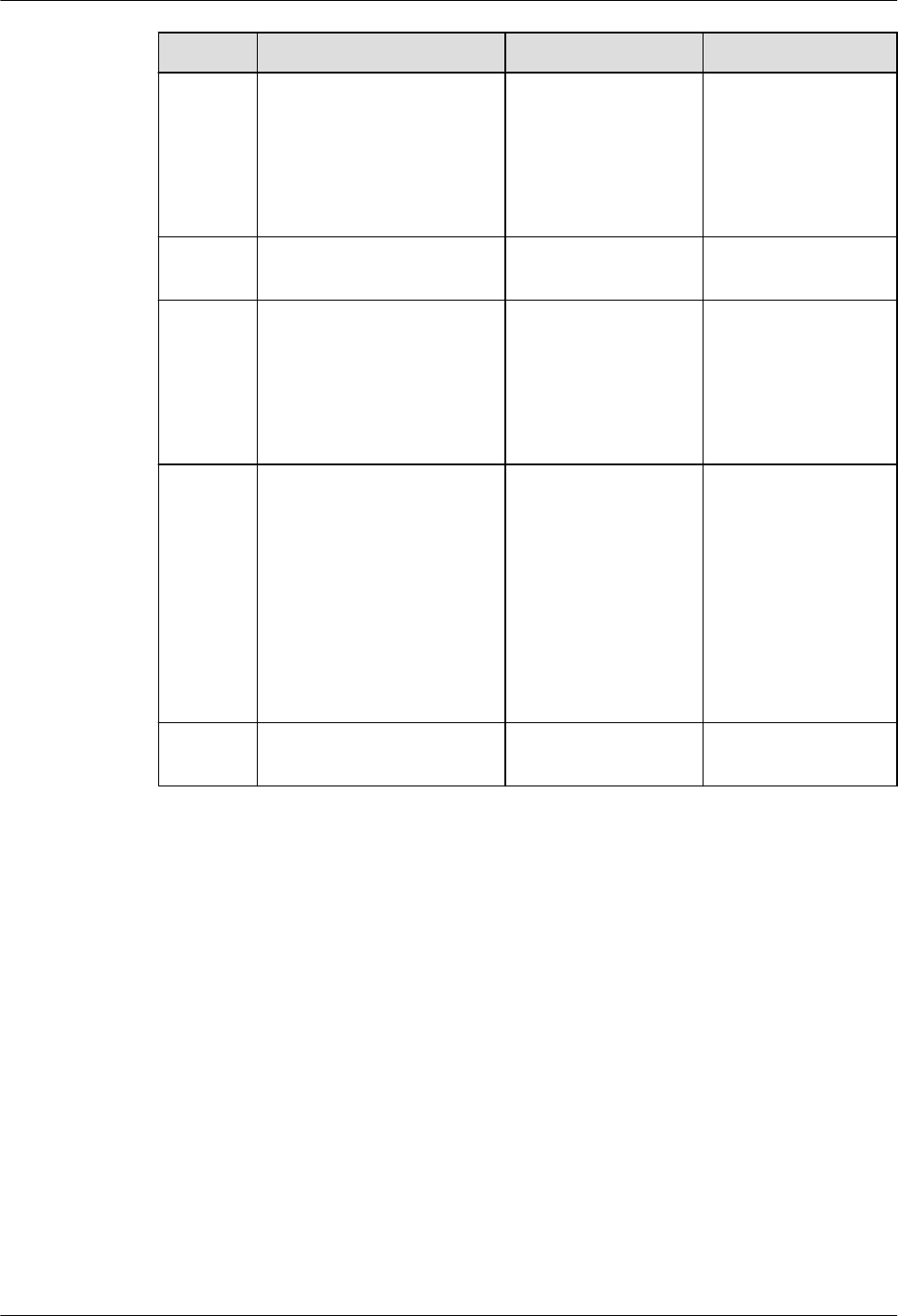
No. Oracle GaussDB Dierence
18 GET_CPU_TIME Function GET_CPU_TIME
Function
GaussDB: The
function returns
the BIGINT type.
Oracle: The
function returns
the NUMBER type.
19 GET_DEPENDENCY
Procedure
Not supported -
20 GET_ENDIANNESS
Function
GET_ENDIANNESS
Function
GaussDB: The
function returns
the INTEGER type.
Oracle: The
function returns
the NUMBER type.
21 GET_HASH_VALUE
Function
GET_HASH_VALUE
Function
GaussDB: The base
and hash_size
parameters and
the return types
are all INTEGER.
Oracle: The base
and hash_size
parameters and
the return types
are all NUMBER.
22 GET_PARAMETER_VALUE
Function
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 157

No. Oracle GaussDB Dierence
23 GET_SQL_HASH Function GET_SQL_HASH
Function
GaussDB: The
last4bytes
parameter of the
BIGINT type
species the last
four bytes of an
MD5 hash value
and is displayed as
an unsigned
integer. The
function returns
the BIGINT type.
Oracle: The
pre10ihash
parameter of the
NUMBER type is
used to store the
4-byte hash value
among the 16
bytes calculated by
MD5.
24
GET_TIME Function GET_TIME Function GaussDB: The
function returns
the BIGINT type.
Oracle: The
function returns
the NUMBER type.
25 GET_TZ_TRANSITIONS
Procedure
Not supported -
26 INVALIDATE Procedure Not supported -
27 IS_BIT_SET Function IS_BIT_SET Function GaussDB: The n
parameter and
return value type
are both INTEGER.
Oracle: The n
parameter and
return value type
are both NUMBER.
28 IS_CLUSTER_DATABASE
Function
IS_CLUSTER_DATAB
ASE Function
-
29 MAKE_DATA_BLOCK_AD
DRESS Function
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 158

No. Oracle GaussDB Dierence
30 NAME_RESOLVE
Procedure
NAME_RESOLVE
Procedure
GaussDB: The
context and
part1_type
parameters are of
the INTEGER type,
and the
object_number
parameter is of the
OID type. GaussDB
does not support
implicit conversion
from NUMBER to
OID.
Oracle: The
context,
part1_type, and
object_number
parameters are of
the NUMBER type.
31 NAME_TOKENIZE
Procedure
NAME_TOKENIZE
Procedure
GaussDB: The
nextpos parameter
is of the INTEGER
type.
Oracle: The
nextpos parameter
is of the
BINARY_INTEGER
type.
32 OLD_CURRENT_SCHEMA
Function
OLD_CURRENT_SC
HEMA Function
GaussDB: The
function returns
the VARCHAR type.
Oracle: The
function returns
the VARCHAR2
type.
33 OLD_CURRENT_USER
Function
OLD_CURRENT_US
ER Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
34 PORT_STRING Function Not supported -
35 SQLID_TO_SQLHASH
Function
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 159

No. Oracle GaussDB Dierence
36 TABLE_TO_COMMA
Procedures
TABLE_TO_COMMA
Procedures
GaussDB: The tab
parameter is a
VARCHAR2 array.
Oracle: There are
two overloaded
stored procedures.
The tab parameter
can be of the
uncl_array or
lname_array type.
37 VALIDATE Procedure Not supported -
38 WAIT_ON_PENDING_DM
L Function
Not supported -
Table 7-101 DBMS_SQL compatibility
No. Oracle GaussDB Dierence
1 BIND_ARRAY Procedures SQL_BIND_ARRAY
Function
-
2 BIND_VARIABLE
Procedures
SQL_BIND_VARIABLE
Function
-
3 BIND_VARIABLE_PKG
Procedure
Not supported -
4 CLOSE_CURSOR
Procedure
SQL_UNREGISTER_C
ONTEXT Function
-
5 COLUMN_VALUE
Procedure
GET_RESULT
Procedure
-
6 COLUMN_VALUE_LONG
Procedure
Not supported -
7 DEFINE_ARRAY Procedure SET_RESULTS_TYPE
Procedure
-
8 DEFINE_COLUMN
Procedures
SET_RESULT_TYPE
Procedure
-
9 DEFINE_COLUMN_CHAR
Procedure
Not supported -
10 DEFINE_COLUMN_LONG
Procedure
Not supported -
11 DEFINE_COLUMN_RAW
Procedure
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 160

No. Oracle GaussDB Dierence
12 DEFINE_COLUMN_ROWI
D Procedure
Not supported -
13 DESCRIBE_COLUMNS
Procedure
DESCRIBE_COLUMNS
Procedure
-
14 DESCRIBE_COLUMNS2
Procedure
Not supported -
15 DESCRIBE_COLUMNS3
Procedure
Not supported -
16 EXECUTE Function SQL_RUN Function -
17 EXECUTE_AND_FETCH
Function
RUN_AND_NEXT
Function
-
18 FETCH_ROWS Function NEXT_ROW Function -
19 GET_NEXT_RESULT
Procedures
Not supported -
20 IS_OPEN Function IS_ACTIVE Function -
21 LAST_ERROR_POSITION
Function
Not supported -
22 LAST_ROW_COUNT
Function
LAST_ROW_COUNT
Function
-
23 LAST_ROW_ID Function Not supported -
24 LAST_SQL_FUNCTION_C
ODE Function
Not supported -
25 OPEN_CURSOR Functions REGISTER_CONTEXT
Function
-
26 PARSE Procedures Supported, with
dierences.
In GaussDB,
the
SQL_SET_S
QL function
does not
support
overloading.
27 RETURN_RESULT
Procedures
Not supported -
28 TO_CURSOR_NUMBER
Function
Not supported -
29 TO_REFCURSOR Function Not supported -
30 VARIABLE_VALUE
Procedures
GET_VARIABLE_RESU
LT Procedures
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 161
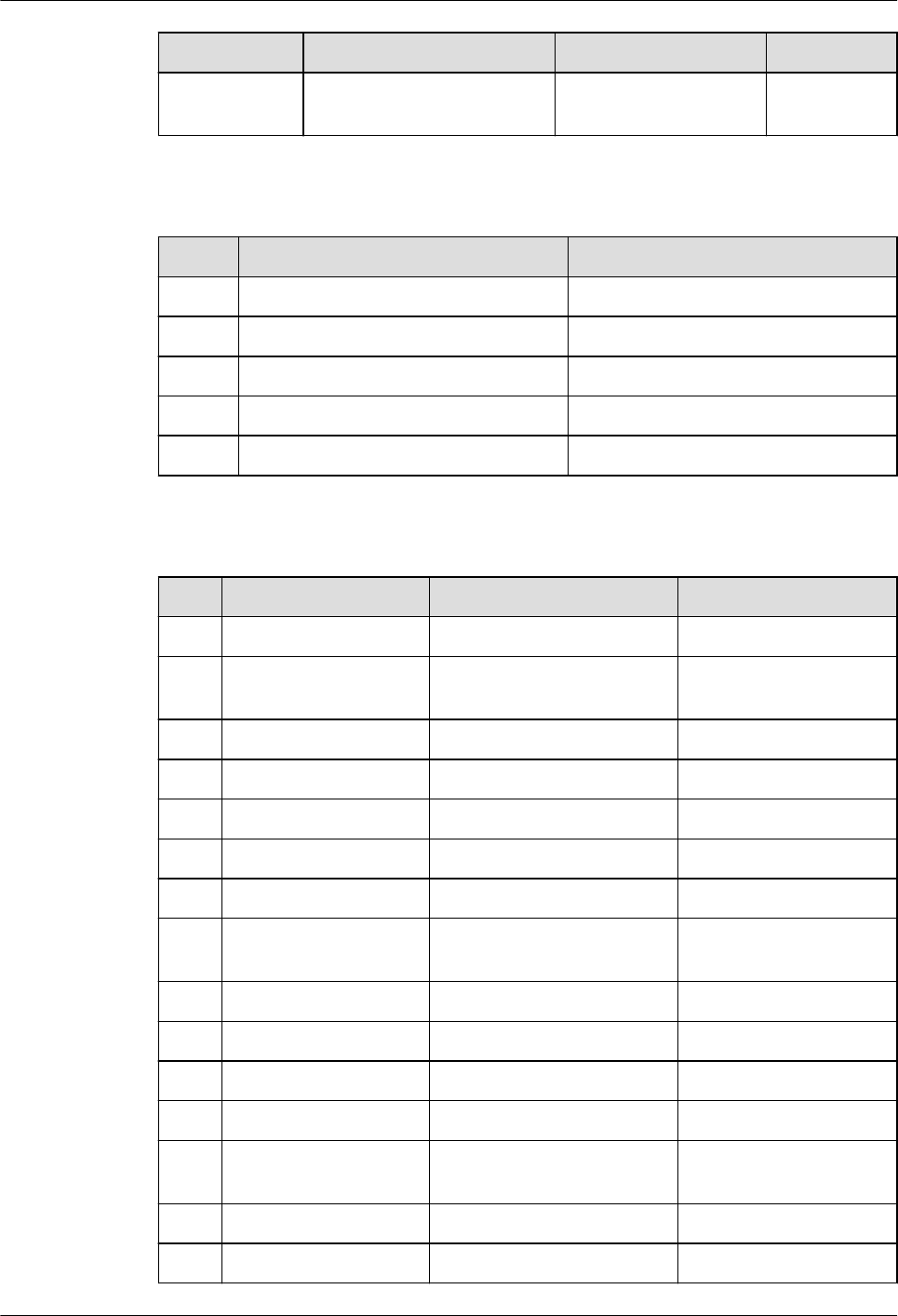
No. Oracle GaussDB Dierence
31 VARIABLE_VALUE_PKG
Procedure
Not supported -
Table 7-102 DBMS_SQL data type compatibility
No. Oracle GaussDB
1 DBMS_SQL DESC_REC DBE_SQL.DESC_REC
2 DBMS_SQL DATE_TABLE DBE_SQL.DATE_TABLE
3 DBMS_SQL NUMBER_TABLE DBE_SQL.NUMBER_TABLE
4 DBMS_SQL VARCHAR2_TABLE DBE_SQL.VARCHAR2_TABLE
5 DBMS_SQL BLOB_TABLE DBE_SQL.BLOB_TABLE
Table 7-103 UTL_FILE compatibility
No.
Oracle GaussDB Dierence
1 FCLOSE Procedure CLOSE Procedure -
2 FCLOSE_ALL
Procedure
CLOSE_ALL Procedure -
3 FCOPY Procedure COPY Procedure -
4 FFLUSH Procedure FLUSH Procedure -
5 FGETATTR Procedure GET_ATTR Procedure -
6 FGETPOS Function GET_POS Function -
7 FOPEN Function FOPEN Function -
8 FOPEN_NCHAR
Function
FOPEN_NCHAR Function -
9 FREMOVE Procedure REMOVE Procedure -
10 FRENAME Procedure RENAME Procedure -
11 FSEEK Procedure SEEK Procedure -
12 GET_LINE Procedure READ_LINE Procedure -
13 GET_LINE_NCHAR
Procedure
READ_LINE_NCHAR
Procedure
-
14 GET_RAW Procedure GET_RAW Procedure -
15 IS_OPEN Function IS_OPEN Function -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 162

No. Oracle GaussDB Dierence
16 NEW_LINE
Procedure
Supported, with
dierences in the
NEW_LINE function
GaussDB denes the
interface as function
due to performance
reasons.
17 PUT Procedure Supported, with
dierences in the WRITE
function
GaussDB denes the
interface as function
due to performance
reasons.
18 PUT_LINE Procedure Supported, with
dierences in the
WRITE_LINE function
GaussDB denes the
interface as function
due to performance
reasons.
19 PUT_LINE_NCHAR
Procedure
Supported, with
dierences in the
WRITE_LINE_NCHAR
function
GaussDB denes the
interface as function
due to performance
reasons.
20 PUT_NCHAR
Procedure
Supported, with
dierences in the
WRITE_NCHAR function
GaussDB denes the
interface as function
due to performance
reasons.
21 PUTF Procedure Supported, with
dierences in the
FORMAT_WRITE function
GaussDB denes the
interface as function
due to performance
reasons.
22 PUTF_NCHAR
Procedure
Supported, with
dierences in the
FORMAT_WRITE_NCHAR
function
GaussDB denes the
interface as function
due to performance
reasons.
23 PUT_RAW Procedure Supported, with
dierences in the
PUT_RAW function
GaussDB denes the
interface as function
due to performance
reasons.
Table 7-104 DBMS_SESSION compatibility
No.
Oracle GaussDB Dierence
1 CLEAR_ALL_CONTEX
T Procedure
Not supported -
2 CLEAR_CONTEXT
Procedure
CLEAR_CONTEXT
Function
-
3 CLEAR_IDENTIFIER
Procedure
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 163

No. Oracle GaussDB Dierence
4 CLOSE_DATABASE_L
INK Procedure
Not supported -
5 CURRENT_IS_ROLE_
ENABLED Function
Not supported -
6 FREE_UNUSED_USE
R_MEMORY
Procedure
Not supported -
7 GET_PACKAGE_MEM
ORY_UTILIZATION
Procedure
Not supported -
8 IS_ROLE_ENABLED
Function
Not supported -
9 IS_SESSION_ALIVE
Function
Not supported -
10 LIST_CONTEXT
Procedures
Not supported -
11 MODIFY_PACKAGE_
STATE Procedure
MODIFY_PACKAGE_ST
ATE Procedure
GaussDB: The scenario
where ags is set to 1 is
supported.
Oracle: The scenario
where ags is set to 1
or 2 is supported.
12 RESET_PACKAGE
Procedure
Not supported -
13 SESSION_IS_ROLE_E
NABLED Function
Not supported -
14 SESSION_TRACE_DIS
ABLE Procedure
Not supported -
15 SESSION_TRACE_EN
ABLE Procedure
Not supported -
16 SET_CONTEXT
Procedure
SET_CONTEXT
Function
GaussDB: There are the
namspace, attribute,
and value parameters of
the TEXT type.
Oracle: There are the
namspace, attribute,
value, username, and
client_id parameters of
the VARCHAR2 type.
17 SET_EDITION_DEFER
RED Procedure
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 164

No. Oracle GaussDB Dierence
18 SET_IDENTIFIER
Procedure
Not supported -
19 SET_NLS Procedure Not supported -
20 SET_ROLE Procedure Not supported. -
21 SET_SQL_TRACE
Procedure
Not supported -
22 SLEEP Procedure Not supported -
23 SWITCH_CURRENT_
CONSUMER_GROUP
Procedure
Not supported -
24 UNIQUE_SESSION_I
D Function
Not supported -
Table 7-105 UTL_MATCH compatibility
N
o.
Oracle GaussDB Dierence
1 EDIT_DISTANCE
Function
Not supported -
2 EDIT_DISTANCE
_SIMILARITY
Function
EDIT_DISTANCE_
SIMILARITY
Function
GaussDB: The str1 and str2
parameters are of the TEXT type, and
the function returns the INTEGER
type.
Oracle: The s1 and s2 parameters are
of the VARCHAR2 type, and the
function returns the PLS_INTEGER
type.
3 JARO_WINKLER
Function
Not supported -
4 JARO_WINKLER
_SIMILARITY
Function
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 165

Table 7-106 DBMS_APPLICATION_INFO compatibility
No. Oracle GaussDB Dierence
1 READ_CLIENT_IN
FO Function
READ_CLIENT_
INFO
Procedure
GaussDB: The client_info parameter
is of the TEXT type.
Oracle: The client_info parameter is
of the VARCHAR2 type.
2 READ_MODULE
Procedure
READ_MODUL
E Procedure
GaussDB: The module_name and
action_name parameters are of the
TEXT type.
Oracle: The module_name and
action_name parameters are of the
VARCHAR2 type.
3 SET_ACTION
Procedure
SET_ACTION
Procedure
GaussDB: The action_name
parameter is of the TEXT type.
Oracle: The action_name parameter
is of the VARCHAR2 type.
4 SET_CLIENT_INFO
Function
SET_CLIENT_IN
FO Procedure
GaussDB: The str parameter is of
the TEXT type, and the return type is
VOID.
Oracle: The client_info parameter is
of the VARCHAR2 type and no value
is returned. Both of them are
written to the client. The maximum
length is 64 bytes. If the length
exceeds 64 bytes, it will be
truncated.
5 SET_MODULE
Procedure
SET_MODULE
Procedure
GaussDB: The module_name and
action_name parameters are of the
TEXT type.
Oracle: The module_name and
action_name parameters are of the
VARCHAR2 type.
6 SET_SESSION_LO
NGOPS Procedure
Not supported -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 166

Table 7-107 DBMS_XMLDOM compatibility
No. Oracle GaussDB Dierence
1 DBMS_XMLDO
M.APPENDCHI
LD
DBE_XMLDOM.APP
ENDCHILD
● GaussDB: The error message
"operation not support" is
displayed for the APPEND ATTR
node under the DOCUMENT
node.
Oracle: No error is reported in
this scenario, but the mounting
fails.
● GaussDB: The error message
"operation not support" is
displayed for the APPEND ATTR
node under the ATTR node.
Oracle: No error is reported in
this scenario, but the mounting
fails.
● GaussDB: When multiple child
nodes of the ATTR type are
added to a parent node, the
child nodes with the same key
value cannot exist under the
same parent node.
Oracle: Subnodes with the same
key value can exist under the
same parent node.
2
DBMS_XMLDO
M.CREATEELE
MENT
DBE_XMLDOM.CRE
ATEELEMENT
-
3 DBMS_XMLDO
M.CREATETEX
TNODE
DBE_XMLDOM.CRE
ATETEXTNODE
-
4 DBMS_XMLDO
M.FREEDOCU
MENT
Supported, with
dierences in
DBE_XMLDOM.FRE
EDOCUMENT
GaussDB: Objects are not released
immediately. They are released
after a certain number of objects
are accumulated. All nodes in the
document are invalid.
Oracle: The object is released
immediately.
5 DBMS_XMLDO
M.FREEELEME
NT
DBE_XMLDOM.FRE
EELEMENT
-
6 DBMS_XMLDO
M.FREENODE
DBE_XMLDOM.FRE
ENODE
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 167

No. Oracle GaussDB Dierence
7 DBMS_XMLDO
M.FREENODEL
IST
Supported, with
dierences in
DBE_XMLDOM.FRE
ENODELIST
GaussDB: The nodelist will be
released.
Oracle: After the nodelist is
released, it can still be queried in
the original document.
8 DBMS_XMLDO
M.GETATTRIB
UTE
DBE_XMLDOM.GET
ATTRIBUTE
-
9 DBMS_XMLDO
M.GETATTRIB
UTES
DBE_XMLDOM.GET
ATTRIBUTES
-
10 DBMS_XMLDO
M.GETCHILDN
ODES
DBE_XMLDOM.GET
CHILDNODES
GaussDB: When the document
node is used, DTD is included.
Oracle: DTD is not included.
11 DBMS_XMLDO
M.GETCHILDR
ENBYTAGNAM
E
DBE_XMLDOM.GET
CHILDRENBYTAGN
AME
GaussDB: The ns parameter of the
DBE_XMLDOM.GETCHILDRENBYTA
GNAME interface does not support
the asterisk (*) parameter. To
obtain all attributes of a node, use
the
DBE_XMLDOM.GETCHILDNODES
interface.
Oracle: The input parameter * is
supported.
12 DBMS_XMLDO
M.GETDOCUM
ENTELEMENT
DBE.XMLDOM.GET
DOCUMENTELEME
NT
-
13 DBMS_XMLDO
M.GETFIRSTC
HILD
DBE_XMLDOM.GET
FIRSTCHILD
-
14 DBMS_XMLDO
M.GETLASTCH
ILD
DBE_XMLDOM.GET
LASTCHILD
-
15 DBMS_XMLDO
M.GETLENGT
H
DBE_XMLDOM.GET
LENGTH
-
16 DBMS_XMLDO
M.GETLOCALN
AME
DBE_XMLDOM.GET
LOCALNAME
-
17 DBMS_XMLDO
M.GETNAMED
ITEM
DBE_XMLDOM.GET
NAMEDITEM
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 168

No. Oracle GaussDB Dierence
18 DBMS_XMLDO
M.GETNEXTSI
BLING
DBE_XMLDOM.GET
NEXTSIBLING
-
19 DBMS_XMLDO
M.GETNODEN
AME
DBE_XMLDOM.GET
NODENAME
-
20 DBMS_XMLDO
M.GETNODET
YPE
DBE_XMLDOM.GET
NODETYPE
-
21 DBMS_XMLDO
M.GETTAGNA
ME
DBE_XMLDOM.GET
TAGNAME
-
22 DBMS_XMLDO
M.IMPORTNO
DE
DBE_XMLDOM.IMP
ORTNODE
-
23 DBMS_XMLDO
M.ISNULL
DBE_XMLDOM.ISN
ULL
GaussDB: When the input
parameter is of the
DOMNODELIST type, an error is
reported if the object does not
exist in the hash table.
Oracle: No error is reported.
24 DBMS_XMLDO
M.ITEM
DBE_XMLDOM.ITE
M
-
25 DBMS_XMLDO
M.MAKENODE
DBE_XMLDOM.MA
KENODE
GaussDB: This function cannot be
directly returned as the function
return value.
Oracle: It is directly returned as the
function return value.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 169

No. Oracle GaussDB Dierence
26 DBMS_XMLDO
M.NEWDOMD
OCUMENT
DBE_XMLDOM.NE
WDOMDOCUMEN
T
● GaussDB: The size of the input
parameter must be less than 1
GB.
Oracle: The size is the same as
that of the CLOB type.
● Currently, external DTD parsing
is not supported in GaussDB.
Oracle: External DTD can be
parsed.
● GaussDB: The default character
set of doc created by
newdomdocument is UTF-8.
Oracle: It is generated based on
the character set of the server.
● GaussDB: Each doc parsed from
the same xmltype instance is
independent, and the
modication of the doc does
not aect the xmltype.
Oracle: Each doc parsed from
the same xmltype instance is
not independent but associated.
● GaussDB: The version column
supports only 1.0. If 1.0 to 1.9
are parsed, a warning is
reported but the execution is
normal. For versions later than
1.9, an error is reported.
Oracle: No error is reported.
● DTD verication dierence
between GaussDB and Oracle: !
ATTLIST to type (CHECK|
check|Check) "Ch..." reports an
error because the default value
"Ch..." is not an enumerated
value in the brackets. However,
Oracle does not report this
error. <!ENTITY baidu
"www.baidu.com">......
&Baidu;&writer reports an
error. Baidu cannot correspond
to baidu because the letters are
case-sensitive.
Oracle: No error is reported.
● Namespace verication
dierence between GaussDB
and Oracle: Undeclared
namespace tags are parsed in
GaussDB.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 170

No. Oracle GaussDB Dierence
Oracle: An error is reported.
27 DBMS_XMLDO
M.SETATTRIBU
TE
DBE_XMLDOM.SET
ATTRIBUTE
GaussDB: The attribute key cannot
be null or an empty string.
Oracle: The attribute key can be
null or an empty string.
28 DBMS_XMLDO
M.SETCHARSE
T
DBE_XMLDOM.SET
CHARSET
Currently, the following character
sets are supported in GaussDB:
UTF-8, UTF-16, UCS-4, UCS-2,
ISO-8859-1, ISO-8859-2,
ISO-8859-3, ISO-8859-4,
ISO-8859-5, ISO-8859-6,
ISO-8859-7, ISO-8859-8,
ISO-8859-9, ISO-2022-JP, Shift_JIS,
EUC-JP, and ASCII. If you enter
other character sets, an error is
reported or garbled characters may
be displayed.
29 DBMS_XMLDO
M.SETDOCTYP
E
DBE_XMLDOM.SET
DOCTYPE
GaussDB: The total length of
name, sysid, and pubid cannot
exceed 32,500 bytes.
Oracle: The maximum size is
32,767 bytes.
30 DBMS_XMLDO
M.WRITETOBU
FFER
Supported, with
dierences in
DBE_XMLDOM.WR
ITETOBUFFER
● GaussDB: The writetobuer
output buer is limited to less
than 1 GB.
Oracle: The maximum size is
32,767 bytes.
● GaussDB: The output doc will
contain the XML declaration
version and encoding.
Oracle: It is not contained
unless being specied by users.
● GaussDB: If the input parameter
is of the domnode type and the
node is converted from a doc,
the output node contains the
XML declaration version and
encoding.
Oracle: It is not contained
unless being specied by users.
● GaussDB: By default, XML les
are output in the UTF-8
character set.
Oracle: It is generated based on
the database character set.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 171

No. Oracle GaussDB Dierence
31 DBMS_XMLDO
M.WRITETOCL
OB
DBE_XMLDOM.WR
ITETOCLOB
● GaussDB: The writetoclob size
cannot exceed 1 GB.
Oracle: The supported size
depends on the CLOB size.
● GaussDB: The output doc will
contain the XML declaration
version and encoding.
Oracle: It is not contained
unless being specied by users.
● GaussDB: If the input parameter
is of the domnode type and the
node is converted from a doc,
the output node contains the
XML declaration version and
encoding.
Oracle: It is not contained
unless being specied by users.
● GaussDB: By default, XML les
are output in the UTF-8
character set.
Oracle: It is generated based on
the database character set.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 172

No. Oracle GaussDB Dierence
32 DBMS_XMLDO
M.WRITETOFIL
E
DBE_XMLDOM.WR
ITETOFILE
● GaussDB document input
parameter. The length of
lename cannot exceed 255
bytes. For details about charset,
see the dbe_xmldom.setcharset
API.
Oracle: The length of lename
is aected by the OS and is
greater than 255 bytes.
● GaussDB DOMNode input
parameter. The length of
lename cannot exceed 255
bytes. For details about charset,
see the dbe_xmldom.setcharset
API.
Oracle: The length of lename
is aected by the OS and is
greater than 255 bytes.
● GaussDB: This function adds
content such as indentation to
format the output. The output
doc will contain the XML
declaration version and
encoding. If the input
parameter is of the domnode
type and the node is converted
from a doc, the output node
contains the XML declaration
version and encoding.
Oracle: It is not contained
unless being specied by users.
● GaussDB: If
newdomdocument() is used to
create a doc without
parameters, no error is reported
when charset is not specied.
The UTF-8 character set is used
by default.
Oracle: An error is reported.
● GaussDB: The lename must be
in the path created in
pg_directory. The backslash (\)
in the lename will be
converted to a slash (/). Only
one slash (/) is allowed. The le
name must be in the
pg_directory_name/le_name
format.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 173
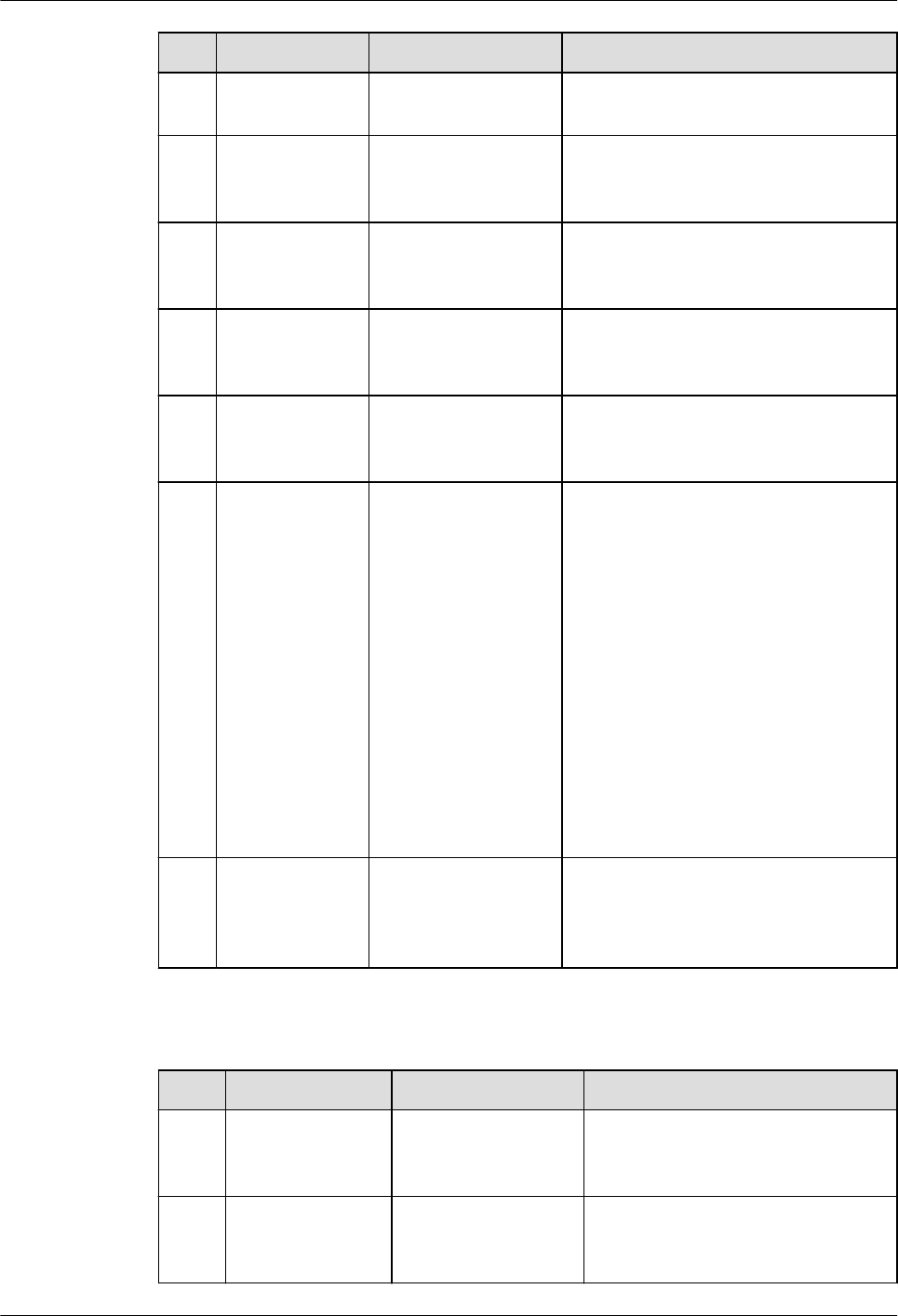
No. Oracle GaussDB Dierence
Oracle: User input is not
escaped.
33 DBMS_XMLDO
M.GETNODEV
ALUE
DBE_XMLDOM.GET
NODEVALUE
-
34 DBMS_XMLDO
M.GETPARENT
NODE
DBE_XMLDOM.GET
PARENTNODE
-
35 DBMS_XMLDO
M.HASCHILDN
ODES
DBE_XMLDOM.HA
SCHILDNODES
-
36 DBMS_XMLDO
M.MAKEELEM
ENT
DBE_XMLDOM.MA
KEELEMENT
-
37 DBMS_XMLDO
M.SETNODEV
ALUE
DBE_XMLDOM.SET
NODEVALUE
● GaussDB: Input parameter of
nodeValue. You can enter an
empty string or NULL, but the
node value will not be changed.
Oracle: If you enter an empty
string or NULL, the node value
is set to an empty string.
● GaussDB: Input parameter of
nodeValue. The escape
character '&' is not supported. If
the character string contains
the escape character, the node
value will be cleared.
Oracle: Escape characters are
supported.
38 DBMS_XMLDO
M.GETELEME
NTSBYTAGNA
M
DBE_XMLDOM.GET
ELEMENTSBYTAGN
AME
-
Table 7-108 DBMS_XMLPARSER compatibility
No.
Oracle GaussDB Dierence
1 DBMS_XMLPAR
SER.FREEPARSE
R
DBE_XMLPARSER.F
REEPARSER
-
2 DBMS_XMLPAR
SER.GETDOCU
MENT
DBE_XMLPARSER.G
ETDOCUMENT
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 174

No. Oracle GaussDB Dierence
3 DBMS_XMLPAR
SER.GETVALIDA
TIONMODE
DBE_XMLPARSER.G
ETVALIDATIONMO
DE
-
4 DBMS_XMLPAR
SER.NEWPARSE
R
Supported, with
dierences in
DBE_XMLPARSER.
NEWPARSER
The maximum number of parser
objects in GaussDB is
16,777,215, and that in Oracle is
about 100 million.
5 DBMS_XMLPAR
SER.PARSEBUFF
ER
Supported, with
dierences in
DBE_XMLPARSER.P
ARSEBUFFER
● Dierence in parsing
columns: Only UTF-8 is
supported in terms of
character encoding, and
version can only be set to
1.0. If versions 1.0 to 1.9 are
parsed, a warning appears
but the execution is normal.
For versions later than 1.9, an
error is reported.
● Namespace validation
dierence: Undeclared
namespace tags are parsed.
However, Oracle reports an
error.
● Dierence in parsing XML
predened entities: '
and " are parsed and
translated into ' and ".
However, predened entities
in Oracle are not translated
into characters.
● DTD validation dierences:
– !ATTLIST to type (CHECK|
check|Check) "Ch..."
reports an error because
the default value "Ch..." is
not an enumerated value
in the brackets. However,
Oracle does not report this
error.
– <!ENTITY baidu
"www.baidu.com">......
&Baidu;&writer reports
an error because the
letters are case sensitive.
Baidu cannot correspond
to baidu. However, Oracle
does not report this error.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 175

No. Oracle GaussDB Dierence
6 DBMS_XMLPAR
SER.PARSECLOB
Supported, with
dierences in
DBE_XMLPARSER.P
ARSECLOB
● PARSECLOB cannot parse
CLOBs greater than or equal
to 2 GB.
● Dierence in parsing
columns: Only UTF-8 is
supported in terms of
character encoding, and
version can only be set to
1.0. If versions 1.0 to 1.9 are
parsed, a warning appears
but the execution is normal.
For versions later than 1.9, an
error is reported.
● Namespace validation
dierence: Undeclared
namespace tags are parsed.
However, Oracle reports an
error.
● Dierence in parsing XML
predened entities: '
and " are parsed and
translated into ' and ".
However, predened entities
in Oracle are not translated
into characters.
● DTD validation dierences:
– !ATTLIST to type (CHECK|
check|Check) "Ch..."
reports an error because
the default value "Ch..." is
not an enumerated value
in the brackets. However,
Oracle does not report this
error.
– <!ENTITY baidu
"www.baidu.com">......
&Baidu;&writer reports
an error because the
letters are case sensitive.
Baidu cannot correspond
to baidu. However, Oracle
does not report this error.
7
DBMS_XMLPAR
SER.SETVALIDA
TIONMODE
DBE_XMLPARSER.S
ETVALIDATIONMO
DE
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 176

Table 7-109 DBMS_ILM compatibility
No. Oracle GaussDB Dierence
1 DBMS_ILM.ADD
_TO_ILM
Not supported. -
2 DBMS_ILM.ARC
HIVESTATENAM
E
Not supported. -
3 DBMS_ILM.EXEC
UTE_ILM
DBE_ILM.EXECUTE
_ILM
● The input parameter schema
in GaussDB corresponds to
owner in Oracle.
● GaussDB does not support
the operation of specifying
ilm_scope (specifying
multiple objects at a time).
4 DBMS_ILM.EXEC
UTE_ILM_TASK
Not supported. -
5 DBMS_ILM.PRE
VIEW_ILM
Not supported. -
6 DBMS_ILM.REM
OVE_FROM_ILM
Not supported. -
7 DBMS_ILM.STO
P_ILM
DBE_ILM.STOP_IL
M
-
Table 7-110 DBMS_ILM_ADMIN compatibility
No.
Oracle GaussDB Dierence
1 DBMS_ILM_AD
MIN.CLEAR_HE
AT_MAP_ALL
Not supported. -
2 DBMS_ILM_AD
MIN.CLEAR_HE
AT_MAP_TABLE
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 177
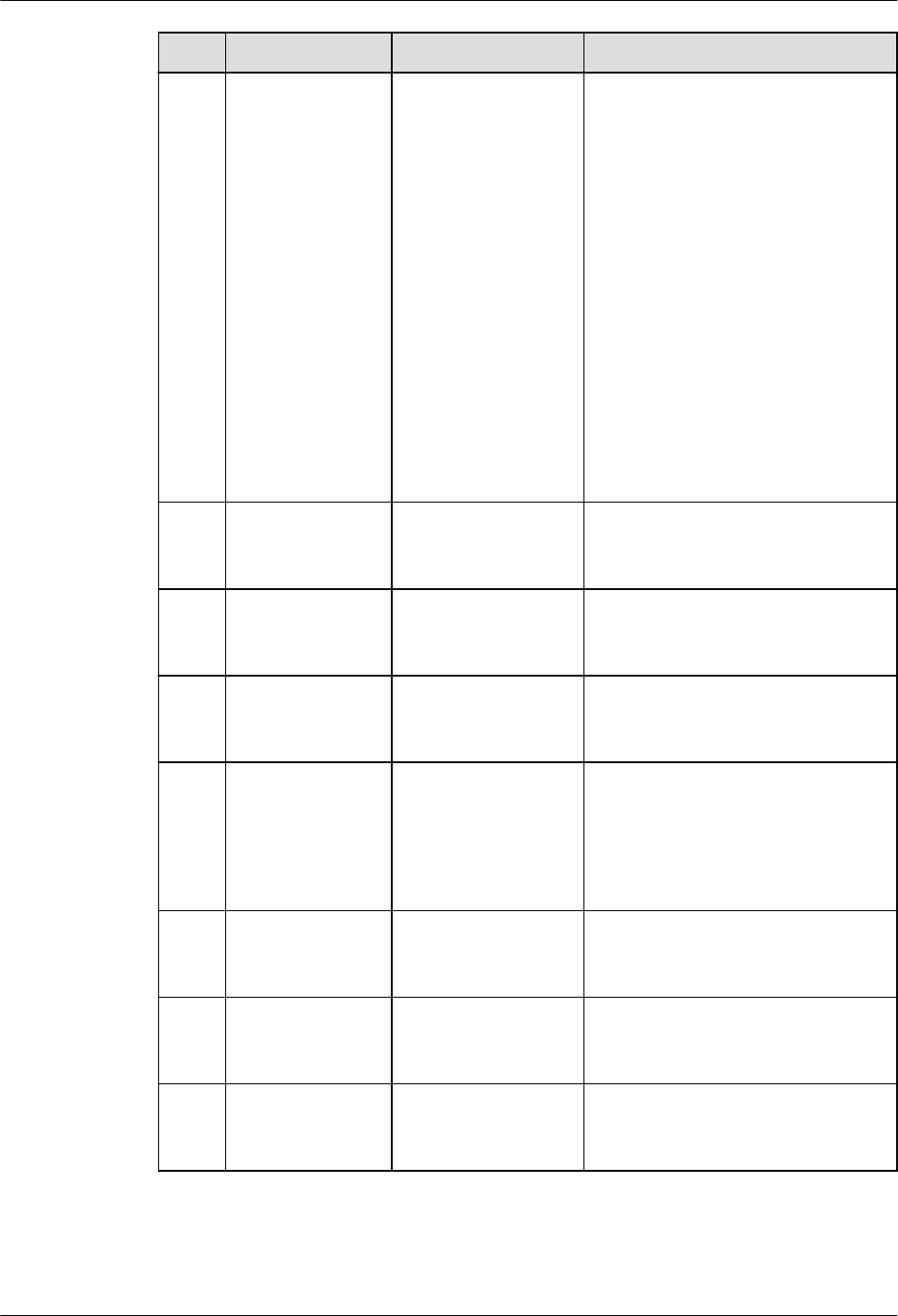
No. Oracle GaussDB Dierence
3 DBMS_ILM_AD
MIN.CUSTOMIZ
E_ILM
DBE_ILM_ADMIN.C
USTOMIZE_ILM
The feature parameters
corresponding to the values of
input parameters are dierent.
● The value of param in
GaussDB can be 1, 2, 7, 11,
12, 13, 14, or 15.
● When the value of param in
GaussDB is 14, the
corresponding feature
parameter is
WIND_DURATION which is
used to control the duration
of the execution window in
automatic scheduling.
However, Oracle does not
have the corresponding
feature parameter.
4 DBMS_ILM_AD
MIN.DISABLE_IL
M
DBE_ILM_ADMIN.
DISABLE_ILM
-
5 DBMS_ILM_AD
MIN.ENABLE_A
UTO_OPTIMIZE
Not supported. -
6 DBMS_ILM_AD
MIN.ENABLE_IL
M
DBE_ILM_ADMIN.E
NABLE_ILM
-
7 DBMS_ILM_AD
MIN.
IGNORE_AUTO_
OPTIMIZE_
CRITERIA
Not supported. -
8 DBMS_ILM_AD
MIN.SET_HEAT_
MAP_ALL
Not supported. -
9 DBMS_ILM_AD
MIN.SET_HEAT_
MAP_START
Not supported. -
10 DBMS_ILM_AD
MIN.SET_HEAT_
MAP_TABLE
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 178

Table 7-111 DBMS_COMPRESSION compatibility
No. Oracle GaussDB Dierence
1 DBMS_COMPRE
SSION.GET_COM
PRESSION_RATI
O
DBE_COMPRESSIO
N.GET_COMPRESS
ION_RATIO
● GaussDB cannot obtain
compression rates of LOBs.
● For obtaining a compression
rate of a single object:
– The value of the input
parameter comptype in
GaussDB can only be 1
(uncompressed) or 2
(advanced compression)
while Oracle also supports
values such as 1024 and
2048.
– The value of the input
parameter objtype in
GaussDB can only be 1
(table object) while Oracle
also supports the value 2
(index object).
– Oracle uses the
subset_numrows
parameter to directly
determine the number of
rows to be sampled (that
is, the value of the
parameter). GaussDB uses
sample_ratio (sampling
rate) to indirectly
determine the number of
rows to be sampled.
2
DBMS_COMPRE
SSION.GET_COM
PRESSION_TYPE
DBE_COMPRESSIO
N.GET_COMPRESS
ION_TYPE
● Oracle uses a row ID to
specify the row whose
compression type is to be
obtained, while GaussDB uses
a CTID to specify the row.
● The value of comptype is
returned. The value
dierence is the same as that
of
GET_COMPRESSION_RATIO.
● In GaussDB, this API can be
called only on DNs. For
details, see "Stored Procedure
> Advanced Packages >
Secondary Encapsulation
Interfaces (Recommended) >
DBE_COMPRESSION" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 179
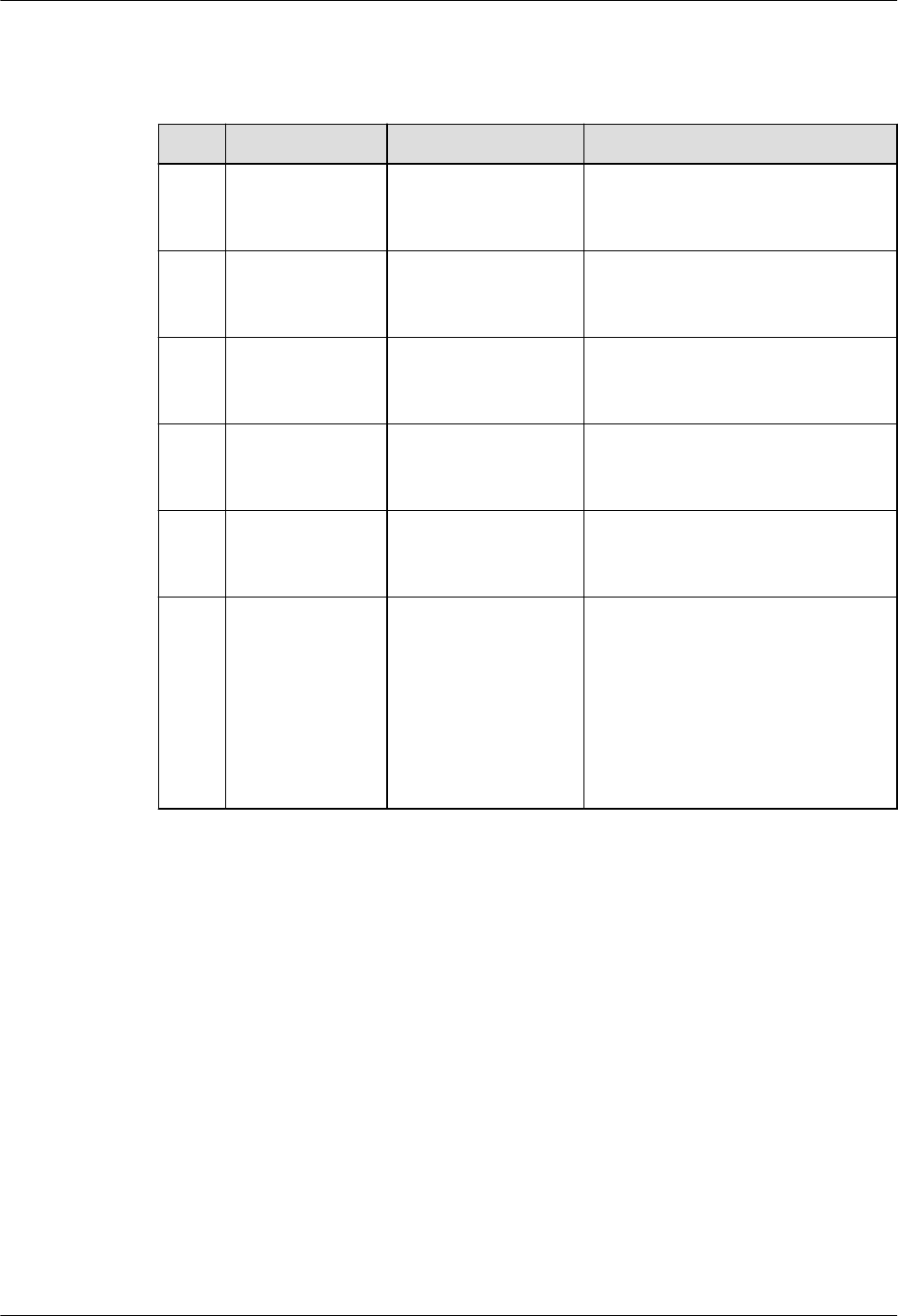
Table 7-112 DBMS_HEAT_MAP compatibility
No. Oracle GaussDB Dierence
1 DBMS_HEAT_M
AP.BLOCK_HEA
T_MAP
Not supported. -
2 DBMS_HEAT_M
AP.EXTENT_HE
AT_MAP
Not supported. -
3 DBMS_HEAT_M
AP.OBJECT_HEA
T_MAP
Not supported. -
4 DBMS_HEAT_M
AP.SEGMENT_H
EAT_MAP
Not supported. -
5 DBMS_HEAT_M
AP.TABLESPACE
_HEAT_MAP
Not supported. -
6 Not supported. DBE_HEAT_MAP.RO
W_HEAT_MAP
In GaussDB, this API can be
called only on DNs. For details,
see "Stored Procedure >
Advanced Packages > Secondary
Encapsulation Interfaces
(Recommended) >
DBE_HEAT_MAP" in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 180

Table 7-113 DBMS_DESCRIBE compatibility
No. Oracle GaussDB Dierence
1 DBMS_DESCRI
BE.DESCRIBE_
PROCEDURE
DBE_DESCRIBE.DES
CRIBE_PROCEDURE
● The datatype parameter is
dierent from Oracle. GaussDB
returns the OID of the data
type, and Oracle returns the ID
of the data type in Oracle.
● The datalength, dataprecision,
and scale parameters are set to
0 because type constraints
(such as number (7,2) and
varchar2(20)) cannot be
retained when GaussDB creates
stored procedures or functions.
Oracle can use the %type
method to obtain constrained
data types.
● For details about information in
GaussDB, see "Stored Procedure
> Advanced Packages >
Secondary Encapsulation
Interfaces (Recommended) >
DBE_DESCRIBE" in
Developer
Guide
.
Table 7-114 DBMS_STATS compatibility
Oracle
GaussDB Dierence
DBMS_STATS.ALTER_STA
TS_HISTORY_RETENTION
Not supported. -
DBMS_STATS.CANCEL_A
DVISOR_TASK
Not supported. -
DBMS_STATS.CONFIGUR
E_ADVISOR_FILTER
Not supported. -
DBMS_STATS.CONFIGUR
E_ADVISOR_OBJ_FILTER
Not supported. -
DBMS_STATS.CONFIGUR
E_ADVISOR_OPR_FILTER
Not supported. -
DBMS_STATS.CONFIGUR
E_ADVISOR_RULE_FILTER
Not supported. -
DBMS_STATS.CREATE_A
DVISOR_TASK
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 181
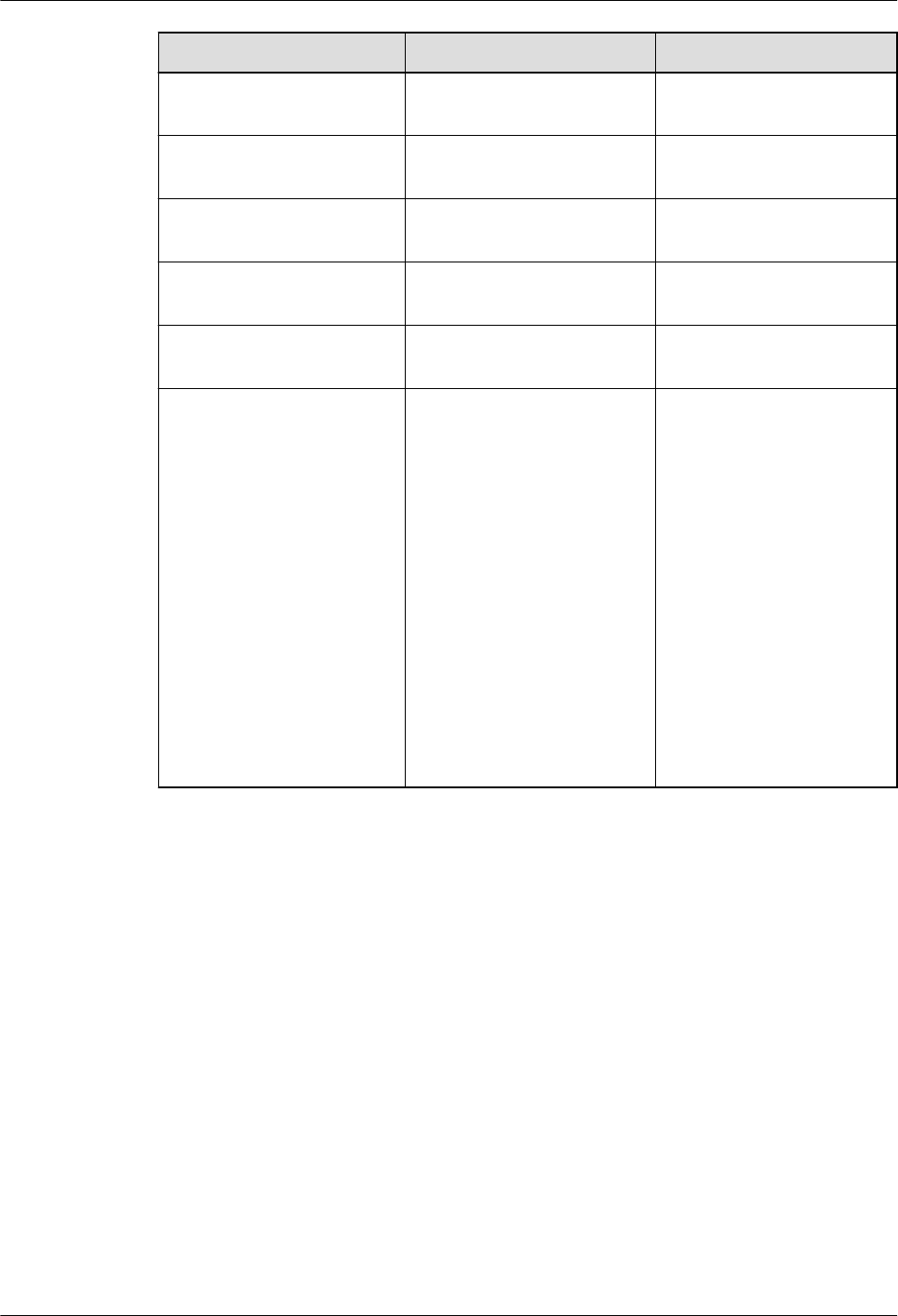
Oracle GaussDB Dierence
DBMS_STATS.CONVERT_
RAW_VALUE
Not supported. -
DBMS_STATS.CONVERT_
RAW_VALUE_NVARCHAR
Not supported. -
DBMS_STATS.CONVERT_
RAW_VALUE_ROWID
Not supported. -
DBMS_STATS.COPY_TABL
E_STATS
Not supported. -
DBMS_STATS.CREATE_EX
TENDED_STATS
Not supported. -
DBMS_STATS.CREATE_ST
AT_TABLE
DBE_STATS.CREATE_STAT
_TABLE
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 182
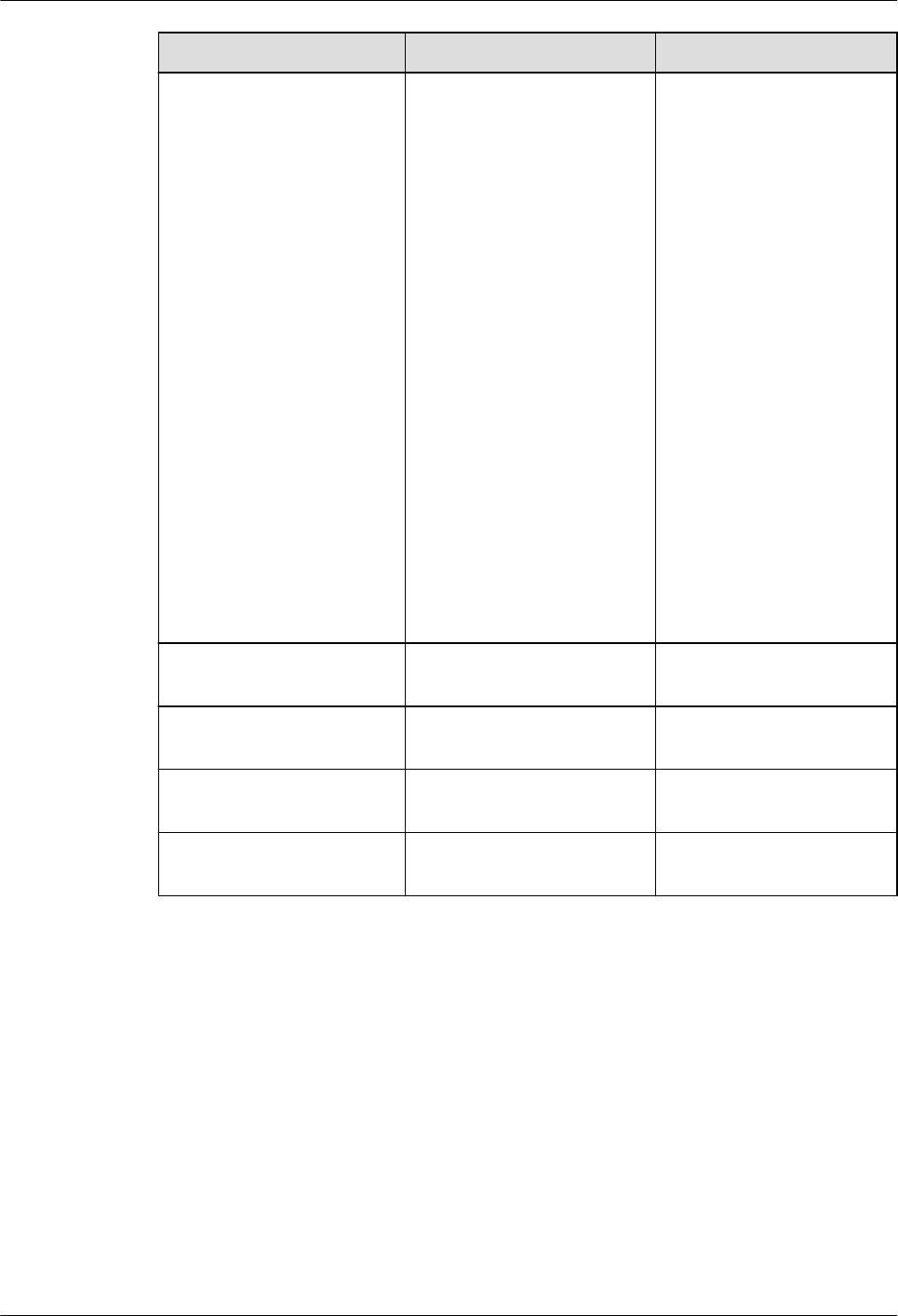
Oracle GaussDB Dierence
DBMS_STATS.DELETE_CO
LUMN_STATS
DBE_STATS.DELETE_COL
UMN_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In GaussDB, this API
can be used to set
expression statistics,
but tabname must
be set to an index
name corresponding
to the expression.
DBMS_STATS.DELETE_DA
TABASE_PREFS
Not supported. -
DBMS_STATS.DELETE_DA
TABASE_STATS
Not supported. -
DEDBMS_STATS.DELETE_
DICTIONARY_STATS
Not supported. -
DBMS_STATS.DELETE_FIX
ED_OBJECTS_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 183

Oracle GaussDB Dierence
DBMS_STATS.DELETE_IN
DEX_STATS
DBE_STATS.DELETE_INDE
X_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
DBMS_STATS.DELETE_PE
NDING_STATS
Not supported. -
DBMS_STATS.DELETE_PR
OCESSING_RATE
Not supported. -
DBMS_STATS.DELETE_SC
HEMA_PREFS
Not supported. -
DBMS_STATS.DELETE_SC
HEMA_STATS
DBE_STATS.DELETE_SCHE
MA_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
DBMS_STATS.DELETE_SY
STEM_STATS
Not supported. -
DBMS_STATS.DELETE_TA
BLE_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 184

Oracle GaussDB Dierence
DBMS_STATS.DELETE_TA
BLE_STATS
DBE_STATS.DELETE_TABL
E_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
DBMS_STATS.DIFF_TABL
E_STATS_IN_HISTORY
Not supported. -
DBMS_STATS.DIFF_TABL
E_STATS_IN_PENDING
Not supported. -
DBMS_STATS.DIFF_TABL
E_STATS_IN_STATTAB
Not supported. -
DBMS_STATS.DROP_ADV
ISOR_TASK
Not supported. -
DBMS_STATS.DROP_EXT
ENDED_STATS
Not supported. -
DBMS_STATS.DROP_STA
T_TABLE
DBE_STATS.DROP_STAT_T
ABLE
-
DBMS_STATS.EXECUTE_A
DVISOR_TASK
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 185

Oracle GaussDB Dierence
DBMS_STATS.EXPORT_C
OLUMN_STATS
DBE_STATS.EXPORT_COL
UMN_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● The exported
column-level
statistics are
consistent with those
in the pg_statistic
catalog. Multiple
columns are
consistent with those
in the pg_statistic_ext
catalog.
● Index expression
statistics can be
exported. tabname
must be set to an
index name, and
colname must be set
to an index
expression name.
● Permission: You must
have the analyze
permission to query
tables and the siud
permission on the
stattab table.
DBMS_STATS.EXPORT_D
ATABASE_PREFS
Not supported. -
DBMS_STATS.EXPORT_D
ATABASE_STATS
Not supported. -
DBMS_STATS.EXPORT_DI
CTIONARY_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 186
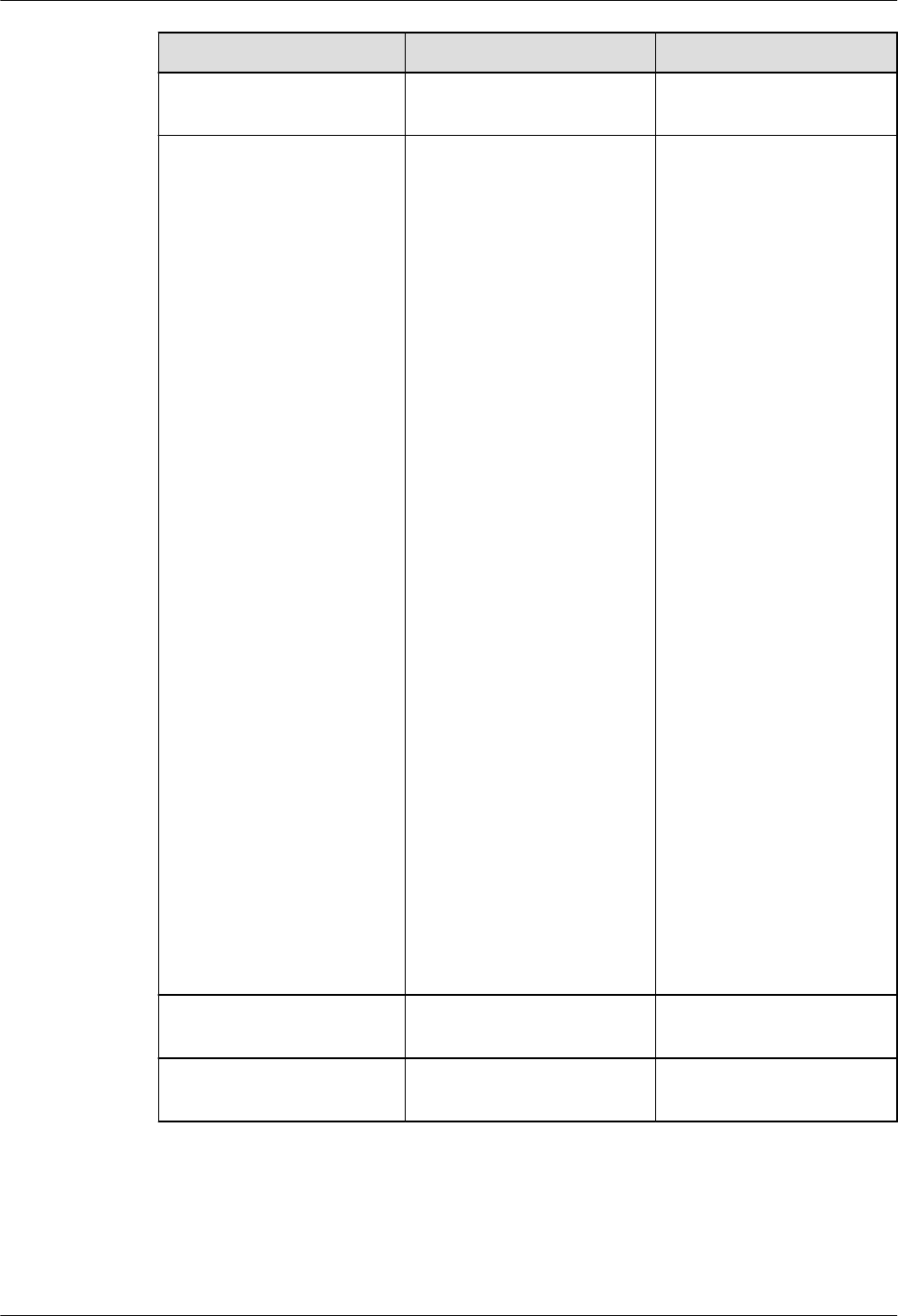
Oracle GaussDB Dierence
DBMS_STATS.EXPORT_FI
XED_OBJECTS_STATS
Not supported. -
DBMS_STATS.EXPORT_IN
DEX_STATS
DBE_STATS.EXPORT_INDE
X_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In the stattab table,
the exported table-
level and partition-
level statistics are
numrows,
numblocks, and
relallvisible, which
correspond to
reltuples, relpages,
and relallvisible in
the pg_class and
pg_partition system
catalogs, respectively.
● Permission: You must
have the analyze
permission to query
tables and the siud
permission on the
stattab table.
DBMS_STATS.EXPORT_PE
NDING_STATS
Not supported. -
DBMS_STATS.EXPORT_SC
HEMA_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 187
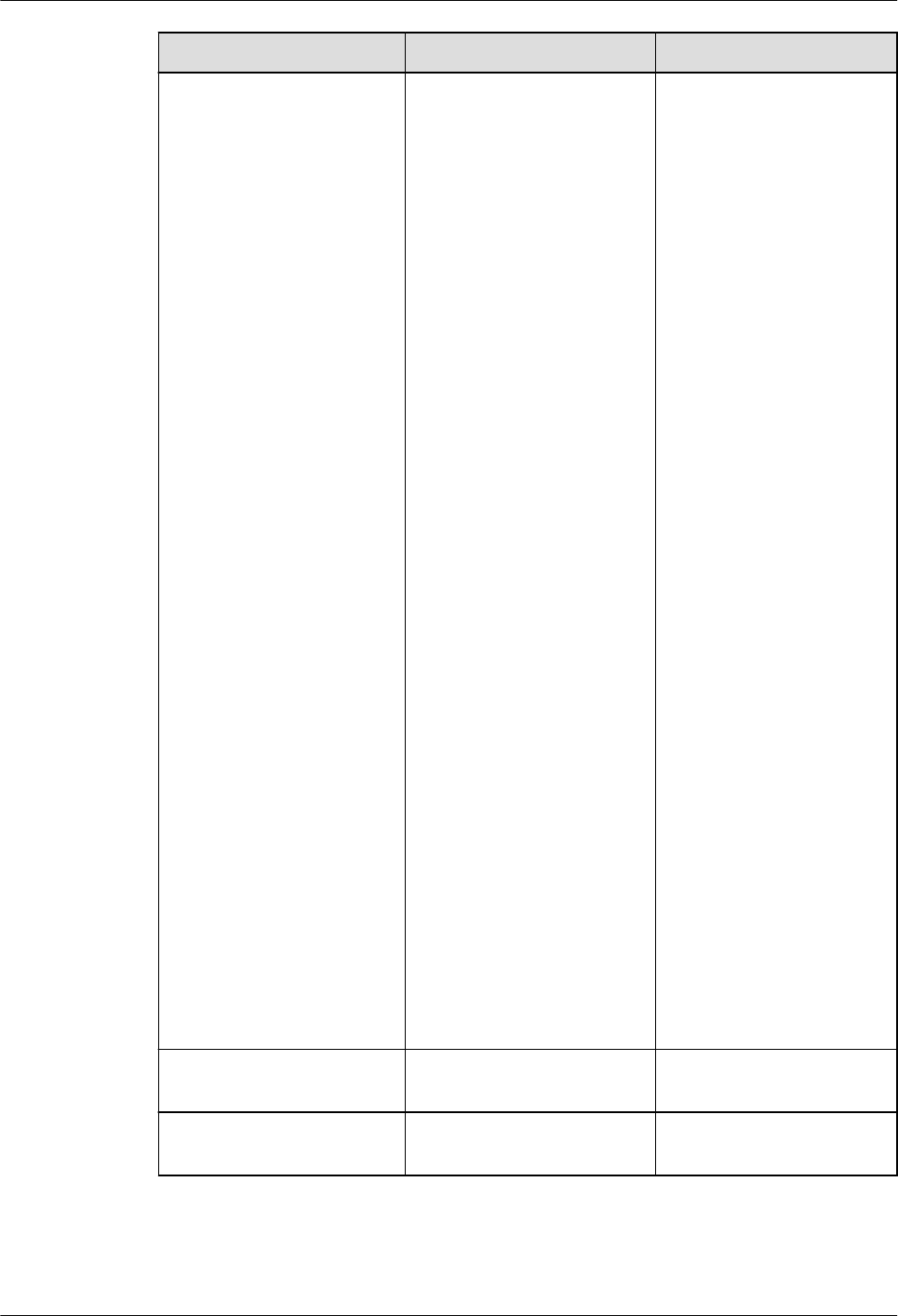
Oracle GaussDB Dierence
DBMS_STATS.EXPORT_SC
HEMA_STATS
DBE_STATS.EXPORT_SCH
EMA_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In the stattab table,
the exported table-
level and partition-
level statistics are
numrows,
numblocks, and
relallvisible, which
correspond to
reltuples, relpages,
and relallvisible in
the pg_class and
pg_partition system
catalogs, respectively.
The column-level
statistics of the
exported table are
consistent with those
of the pg_statistic
and pg_statistic_ext
catalogs.
● Permission: You must
have the siud
permission on the
stattab table.
DBMS_STATS.EXPORT_SY
STEM_STATS
Not supported. -
DBMS_STATS.EXPORT_TA
BLE_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 188

Oracle GaussDB Dierence
DBMS_STATS.EXPORT_TA
BLE_STATS
DBE_STATS.EXPORT_TABL
E_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In the stattab table,
the exported table-
level and partition-
level statistics are
numrows,
numblocks, and
relallvisible, which
correspond to
reltuples, relpages,
and relallvisible in
the pg_class and
pg_partition system
catalogs, respectively.
The column-level
statistics exported in
cascading mode are
consistent with those
in the pg_statistic
and pg_statistic_ext
catalogs.
● Permission: You must
have the analyze
permission to query
tables and the siud
permission on the
stattab table.
DBMS_STATS.FLUSH_DA
TABASE_MONITORING_I
NFO
Not supported. -
DBMS_STATS.GATHER_D
ATABASE_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 189

Oracle GaussDB Dierence
DBMS_STATS.GATHER_DI
CTIONARY_STATS
Not supported. -
DBMS_STATS.GATHER_FI
XED_OBJECTS_STATS
Not supported. -
DBMS_STATS.GATHER_I
NDEX_STATS
Not supported. -
DBMS_STATS.GATHER_P
ROCESSING_RATE
Not supported. -
DBMS_STATS.GATHER_S
CHEMA_STATS
Not supported. -
DBMS_STATS.GATHER_S
YSTEM_STATS
Not supported. -
DBMS_STATS.GATHER_T
ABLE_STATS
Not supported. -
DBMS_STATS.GENERATE
_STATS
Not supported. -
DBMS_STATS.GET_ADVIS
OR_OPR_FILTER
Not supported. -
DBMS_STATS.GET_ADVIS
OR_RECS
Not supported. -
DBMS_STATS.GET_COLU
MN_STATS
Not supported. -
DBMS_STATS.GET_INDEX
_STATS
Not supported. -
DBMS_STATS.GET_PARA
M
Not supported. -
DBMS_STATS.GET_PREFS Not supported. -
DBMS_STATS.GET_STATS
_HISTORY_AVAILABILITY
DBE_STATS.GET_STATS_H
ISTORY_AVAILABILITY
GaussDB queries the
collection time of the
earliest historical
statistics in the entire
database.
DBMS_STATS.GET_STATS
_HISTORY_RETENTION
DBE_STATS.GET_STATS_H
ISTORY_RETENTION
-
DBMS_STATS.GET_SYSTE
M_STATS
Not supported. -
DBMS_STATS.GET_TABLE
_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 190

Oracle GaussDB Dierence
DBMS_STATS.IMPLEMEN
T_ADVISOR_TASK
Not supported. -
DBMS_STATS.IMPORT_C
OLUMN_STATS
DBE_STATS.IMPORT_COL
UMN_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● The exported single-
column col statistics
are the same as
those in the
pg_statistic catalog.
The exported multi-
column ext-col
statistics are
consistent with those
in the pg_statistic_ext
catalog.
● Index expression
statistics can be
imported. tabname
must be set to an
index name, and
colname must be set
to an index
expression name.
● Permission: You must
have the ANALYZE
permission to query
tables and the siud
permission on the
stattab table.
DBMS_STATS.IMPORT_D
ATABASE_PREFS
Not supported. -
DBMS_STATS.IMPORT_D
ATABASE_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 191

Oracle GaussDB Dierence
DBMS_STATS.IMPORT_DI
CTIONARY_STATS
Not supported. -
DBMS_STATS.IMPORT_FI
XED_OBJECTS_STATS
Not supported. -
DBMS_STATS.IMPORT_IN
DEX_STATS
DBE_STATS.IMPORT_IND
EX_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In the stattab table,
the imported table-
level and partition-
level statistics are
numrows,
numblocks, and
relallvisible, which
correspond to
reltuples, relpages,
and relallvisible in
the pg_class and
pg_partition system
catalogs, respectively.
● Permission: You must
have the analyze
permission to query
tables and the siud
permission on the
stattab table.
DBMS_STATS.IMPORT_S
CHEMA_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 192

Oracle GaussDB Dierence
DBMS_STATS.IMPORT_S
CHEMA_STATS
DBE_STATS.IMPORT_SCH
EMA_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In the stattab table,
the imported table-
level and partition-
level statistics are
numrows,
numblocks, and
relallvisible, which
correspond to
reltuples, relpages,
and relallvisible in
the pg_class and
pg_partition system
catalogs, respectively.
The column-level
statistics of the
imported table are
consistent with those
of the pg_statistic
and pg_statistic_ext
catalogs.
● Permission: You must
have the siud
permission on the
stattab table.
DBMS_STATS.IMPORT_SY
STEM_STATS
Not supported. -
DBMS_STATS.IMPORT_T
ABLE_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 193

Oracle GaussDB Dierence
DBMS_STATS.IMPORT_T
ABLE_STATS
DBE_STATS.IMPORT_TABL
E_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● In the stattab table,
the imported table-
level and partition-
level statistics are
numrows,
numblocks, and
relallvisible, which
correspond to
reltuples, relpages,
and relallvisible in
the pg_class and
pg_partition system
catalogs, respectively.
The column-level
statistics imported in
cascading mode are
consistent with those
in the pg_statistic
and pg_statistic_ext
catalogs.
● Permission: You must
have the analyze
permission to query
tables and the siud
permission on the
stattab table.
DBMS_STATS.INTERRUPT
_ADVISOR_TASK
Not supported. -
DBMS_STATS.LOCK_PART
ITION_STATS
DBE_STATS.LOCK_PARTITI
ON_STATS
● In GaussDB,
ownname must be
set to a schema
name.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 194

Oracle GaussDB Dierence
DBMS_STATS.LOCK_SCH
EMA_STATS
DBE_STATS.LOCK_SCHEM
A_STATS
● In GaussDB,
ownname must be
set to a schema
name.
DBMS_STATS.LOCK_TABL
E_STATS
DBE_STATS.LOCK_TABLE_
STATS
● In GaussDB,
ownname must be
set to a schema
name.
DBMS_STATS.MERGE_CO
L_USAGE
Not supported. -
DBMS_STATS.PREPARE_C
OLUMN_VALUES
Not supported. -
DBMS_STATS.PREPARE_C
OLUMN_VALUES_ROWID
Not supported. -
DBMS_STATS.PUBLISH_P
ENDING_STATS
Not supported. -
DBMS_STATS.PURGE_STA
TS
DBE_STATS.PURGE_STATS -
DBMS_STATS.REMAP_ST
AT_TABLE
Not supported. -
DBMS_STATS.REPORT_A
DVISOR_TASK
Not supported. -
DBMS_STATS.REPORT_C
OL_USAGE
Not supported. -
DBMS_STATS.REPORT_G
ATHER_AUTO_STATS
Not supported. -
DBMS_STATS.REPORT_G
ATHER_DATABASE_STAT
S
Not supported. -
DBMS_STATS.REPORT_G
ATHER_DICTIONARY_STA
TS
Not supported. -
DBMS_STATS.REPORT_G
ATHER_FIXED_OBJ_STAT
S
Not supported. -
DBMS_STATS.REPORT_G
ATHER_SCHEMA_STATS
Not supported. -
DBMS_STATS.REPORT_ST
ATS_OPERATIONS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 195

Oracle GaussDB Dierence
DBMS_STATS.RESET_ADV
ISOR_TASK
Not supported. -
DBMS_STATS.RESET_COL
_USAGE
Not supported. -
DBMS_STATS.RESET_GLO
BAL_PREF_DEFAULTS
Not supported. -
DBMS_STATS.RESET_PAR
AM_DEFAULTS
Not supported. -
DBMS_STATS.RESTORE_
DICTIONARY_STATS
Not supported. -
DBMS_STATS.RESTORE_F
IXED_OBJECTS_STATS
Not supported. -
DBMS_STATS.RESTORE_S
CHEMA_STATS
DBE_STATS.RESTORE_SC
HEMA_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
DBMS_STATS.RESTORE_S
YSTEM_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 196

Oracle GaussDB Dierence
DBMS_STATS.RESTORE_T
ABLE_STATS
DBE_STATS.RESTORE_TAB
LE_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
DBMS_STATS.RESUME_A
DVISOR_TASK
Not supported. -
DBMS_STATS.SCRIPT_AD
VISOR_TASK
Not supported. -
DBMS_STATS.SEED_COL_
USAGE
Not supported. -
DBMS_STATS.SET_ADVIS
OR_TASK_PARAMETER
Not supported. -
DBMS_STATS.SET_COLU
MN_STATS
DBE_STATS.SET_COLUMN
_STATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
DBMS_STATS.SET_DATAB
ASE_PREFS
Not supported. -
DBMS_STATS.SET_GLOBA
L_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 197

Oracle GaussDB Dierence
DBMS_STATS.SET_INDEX
_STATS
DBE_STATS.SET_INDEX_S
TATS
● In GaussDB,
ownname must be
set to a schema
name. GaussDB
supports only some
input parameter
functions. For details,
see "Stored
Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● The relallvisible
input parameter is
added to GaussDB.
DBMS_STATS.SET_PARA
M
Not supported. -
DBMS_STATS.SET_PROCE
SSING_RATE
Not supported. -
DBMS_STATS.SET_SCHE
MA_PREFS
Not supported. -
DBMS_STATS.SET_SYSTE
M_STATS
Not supported. -
DBMS_STATS.SET_TABLE
_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 198

Oracle GaussDB Dierence
DBMS_STATS.SET_TABLE
_STATS
DBE_STATS.SET_TABLE_S
TATS
● In GaussDB,
ownname must be
set to a schema
name.
● GaussDB supports
only some input
parameter functions.
For details, see
"Stored Procedure >
Advanced Package >
Secondary
Encapsulation
Interfaces
(Recommended) >
DBE_STATS" in
Developer Guide
.
● The relallvisible
input parameter is
added to GaussDB.
DBMS_STATS.SHOW_EXT
ENDED_STATS_NAME
Not supported. -
DBMS_STATS.TRANSFER_
STATS
Not supported. -
DBMS_STATS.UNLOCK_P
ARTITION_STATS
DBE_STATS.UNLOCK_PAR
TITION_STATS
In GaussDB, ownname
must be set to a schema
name.
DBMS_STATS.UNLOCK_S
CHEMA_STATS
DBE_STATS.UNLOCK_SCH
EMA_STATS
In GaussDB, ownname
must be set to a schema
name.
DBMS_STATS.UNLOCK_T
ABLE_STATS
DBE_STATS.UNLOCK_TAB
LE_STATS
In GaussDB, ownname
must be set to a schema
name.
DBMS_STATS.UPGRADE_
STAT_TABLE
Not supported. -
Table 7-115 DBMS_XMLGEN compatibility
Oracle
GaussDB Dierence
DBMS_XMLGEN.
CONVERT
DBE_XMLGEN.CONV
ERT
-
DBMS_XMLGEN.
NEWCONTEXT
DBE_XMLGEN.NEW
CONTEXT
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 199

Oracle GaussDB Dierence
DBMS_XMLGEN.
NEWCONTEXTF
ROMHIERARCHY
DBE_XMLGEN.NEW
CONTEXTFROMHIE
RARCHY
● The maximum depth of recursive
XML les generated by GaussDB
cannot exceed 50 million layers.
● XML les generated by the
CONNECT BY statement in Oracle's
newcontextfromhierarchy method
contain XML headers. However, the
directly constructed data does not
contain the XML header. In
GaussDB, the les contain XML
headers.
DBMS_XMLGEN.
SETCONVERTSP
ECIALCHARS
DBE_XMLGEN.SETC
ONVERTSPECIALCH
ARS
-
DBMS_XMLGEN.
SETNULLHANDL
ING
DBE_XMLGEN.SETN
ULLHANDLING
-
DBMS_XMLGEN.
SETROWSETTAG
DBE_XMLGEN.SETR
OWSETTAG
-
DBMS_XMLGEN.
SETROWTAG
DBE_XMLGEN.SETR
OWTAG
-
DBMS_XMLGEN.
USENULLATTRIB
UTEINDICATOR
DBE_XMLGEN.USEN
ULLATTRIBUTEINDI-
CATOR
-
DBMS_XMLGEN.
USEITEMTAGSF
ORCOLL
DBE_XMLGEN.USEIT
EMTAGSFORCOLL
-
DBMS_XMLGEN.
GETNUMROWSP
ROCESSED
DBE_XMLGEN.GETN
UMROWSPROCESSE
D
-
DBMS_XMLGEN.
SETMAXROWS
DBE_XMLGEN.SETM
AXROWS
-
DBMS_XMLGEN.
SETSKIPROWS
DBE_XMLGEN.SETSK
IPROWS
-
DBMS_XMLGEN.
RESTARTQUERY
DBE_XMLGEN.RESTA
RTQUERY
In distributed GaussDB, the cursor
cannot be moved reversely. Therefore,
the restartquery function is
unavailable.
DBMS_XMLGEN.
GETXMLTYPE
DBE_XMLGEN.GETX
MLTYPE
-
DBMS_XMLGEN.
GETXML
DBE_XMLGEN.GETX
ML
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 200
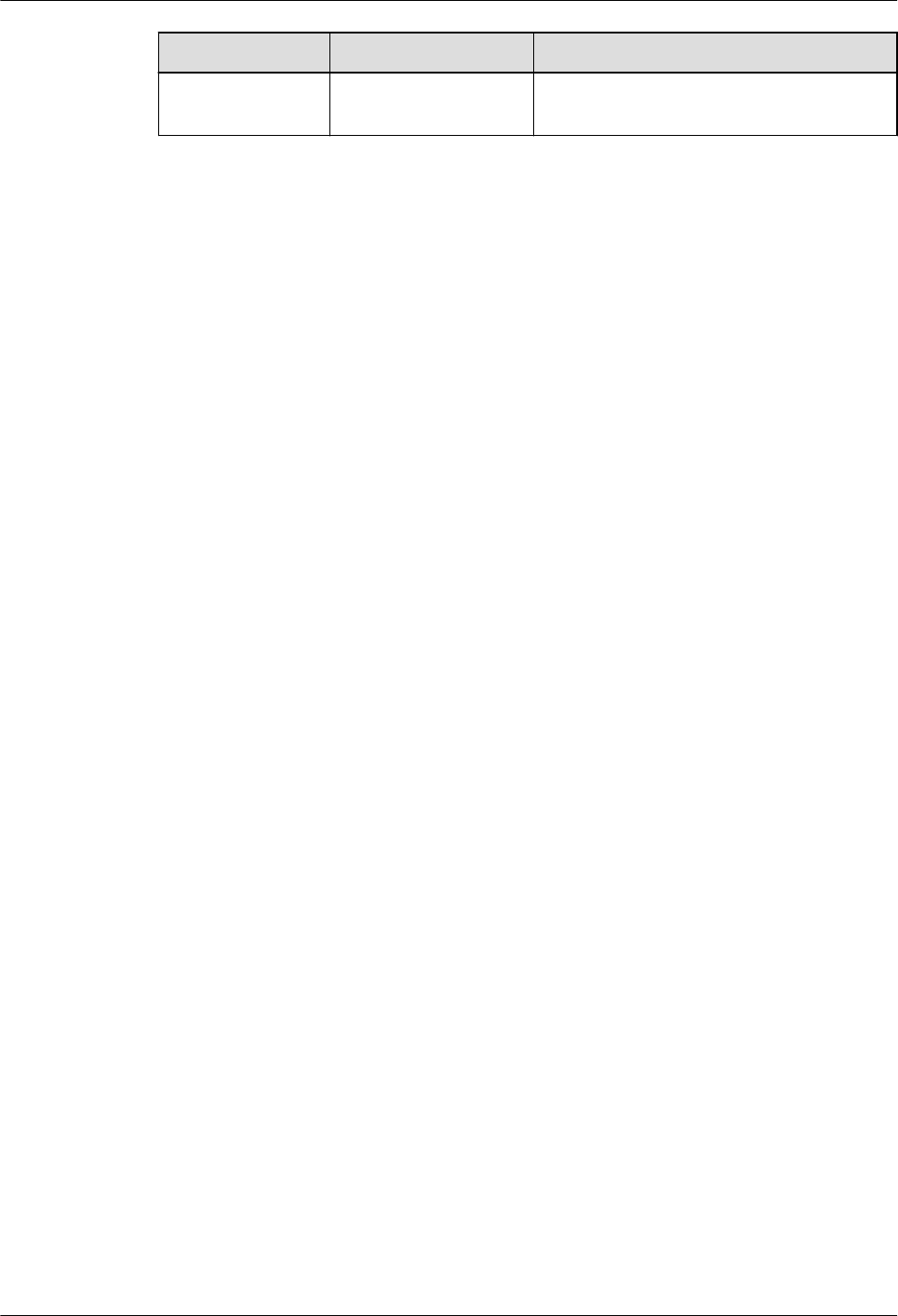
Oracle GaussDB Dierence
DBMS_XMLGEN.
CLOSECONTEXT
DBE_XMLGEN.CLOS
ECONTEXT
-
7.2 Primary/Standby Instances
7.2.1 Oracle Compatibility Overview
This chapter compares the Oracle compatibility mode in GaussDB with Oracle
Database 19c. For details about related information and specications, see the
corresponding sections in
Developer Guide
.
GaussDB is compatible with Oracle in terms of data types, SQL functions,
database objects, and PL/SQL in most cases. The underlying framework
implementation of the GaussDB is dierent from that of Oracle. Therefore, there
are still some dierences between GaussDB and Oracle. The following lists the
compatibility between GaussDB and Oracle.
7.2.2 Basic SQL Elements
GaussDB is compatible with basic SQL elements, but some of them are dierent.
For details, see the following tables.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 201

7.2.2.1 Data Types
Table 7-116 Numeric types
No. Oracle GaussDB Dierence
1 NUMBER [ ( p [ ,
s ] ) ]
Supported, with
dierences.
The precision and
usage are dierent.
● When NUMBER
contains
parameters, the
maximum
boundary values
of precision and
scale in
GaussDB are
greater than
those in Oracle.
● When NUMBER
does not
contain
parameters, the
default value of
precision in
GaussDB is
much greater
than the
maximum
boundary value
when NUMBER
contains
parameters. In
Oracle, the
default value of
precision is
equal to the
maximum
boundary value
when NUMBER
contains
parameters.
● GaussDB does
not support
negative scale
values. In
Oracle, a
negative scale
value is
accurate to the
corresponding
integer.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 202

No. Oracle GaussDB Dierence
2 FLOAT [ ( p ) ] Supported. -
3 BINARY_FLOAT Not supported. -
4 BINARY_DOUBLE Supported. -
Table 7-117 Date and time types
No. Oracle GaussDB Dierence
1 DATE Supported, with
dierences.
The precision is
dierent. GaussDB
supports a larger
time range than
Oracle.
2 TIMESTAMP
[ ( fractional_seconds_pre
cision ) ]
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 203

No. Oracle GaussDB Dierence
3 TIMESTAMP
[ ( fractional_seconds_pre
cision ) ] WITH TIME
ZONE
Supported, with
dierences.
The timestamptz of
GaussDB is
equivalent to the
timestampwithloacl
timezone of Oracle.
The type
corresponding to
timestamptz of
Oracle is missing.
Time zone update:
In some countries
or regions, time
zone information is
frequently updated
due to political,
economic, war, or
other factors.
Therefore, the
database system
needs to modify
the time zone le
to ensure that the
time is correct.
Currently, the
GaussDB time zone
type involves only
timestamp with
timezone. When a
new time zone le
takes eect, the
existing data is not
changed, and the
new data is
adjusted based on
the time zone le
information. The
capability of
processing the
same type of data
in the database is
dierent from that
in the Oracle
database.
4
TIMESTAMP
[ ( fractional_seconds_pre
cision ) ] WITH LOCAL
TIME ZONE
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 204

No. Oracle GaussDB Dierence
5 INTERVAL YEAR
[ ( year_precision ) ] TO
MONTH
Supported. -
6 INTERVAL DAY
[ ( day_precision ) ] TO
SECOND
[ ( fractional_seconds_pre
cision ) ]
Supported. -
Table 7-118 Character types
No. Oracle GaussDB Dierence
1 VARCHAR2 ( size [ BYTE |
CHAR ] )
Supported, with
dierences.
In GaussDB, the
unit of size is byte.
That is, only BYTE
is supported. You
cannot select a
value between
BYTE and CHAR.
The maximum size
is 10 MB. In Oracle,
however, the unit
of size can be
selected between
BYTE and CHAR.
The maximum size
depends on the
character set in
use.
2 NVARCHAR2 ( size ) Supported, with
dierences.
In GaussDB,
NVARCHAR2(n) is
the alias of
VARCHAR2(n). In
Oracle,
NVARCHAR2(n) is
dierent from
VARCHAR2(n).
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 205

No. Oracle GaussDB Dierence
3 CHAR [ ( size [ BYTE |
CHAR ] ) ]
Supported, with
dierences.
In GaussDB, the
unit of size is byte.
That is, only BYTE
is supported. You
cannot select a
value between
BYTE and CHAR.
The maximum size
is 10 MB. In Oracle,
however, the unit
of size can be
selected between
BYTE and CHAR.
The maximum size
is 2000 bytes. The
actual number of
characters that can
be contained
depends on the
character set in
use.
4 NCHAR [ ( size ) ] Supported, with
dierences.
In GaussDB, the
unit of size is byte,
and the maximum
size is 10 MB. In
Oracle, however,
the unit of size is
character, and the
maximum size
depends on the
character set in
use.
5 CLOB Supported, with
dierences.
The locator
concept is not
supported.
6 NCLOB Not supported. -
7 LONG Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 206

Table 7-119 Binary types
No. Oracle GaussDB Dierence
1 RAW ( size ) Supported, with
dierences.
In GaussDB, size
indicates the
recommended byte
length and is not
used to verify the
byte length of the
input raw type.
2 LONG RAW Not supported. -
3 BLOB Supported. -
4 BFILE Not supported. -
Table 7-120 ROWID types
No. Oracle GaussDB
1 ROWID Not supported.
2 UROWID Not supported.
Table 7-121 User-dened types
No.
Oracle GaussDB
1 Object types Not supported.
2 REF data types Not supported.
3 Variable arrays Supported.
4 Nested tables Supported.
Table 7-122 Pseudo-types
No.
Oracle GaussDB
1 anytype Not supported.
2 anydata Not supported.
3 anydataset Not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 207

Table 7-123 XML types
No. Oracle GaussDB Dierence
1 XMLTYPE Supported, with
dierences.
GaussDB does not
support some
operations. For
example, the
XMLELEMENT
function is used to
convert a
character string to
the XML type
instead of the
XMLType type. For
details, see "SQL
Reference > Data
Type > XMLTYPE"
in
Developer
Guide
.
2 URIType Not supported. -
Table 7-124 Spatial types
No.
Oracle GaussDB
1 SDO_GEOMETRY Not supported.
2 SDO_TOPO_GEOMETRY Not supported.
3 SDO_GEORASTER Not supported.
Table 7-125 Lock modes
Level
Oracle GaussDB Remarks
- - NULL NULL of GaussDB indicates
that no lock is assigned, which
corresponds to the level-0 lock
of Oracle.
0 none INVALID INVALID of GaussDB indicates
that an invalid lock is assigned.
An invalid lock is assigned only
when a lock that cannot be
identied by GaussDB occurs
during system running.
1 null AccessShare -
2 RS RowShare -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 208

Level Oracle GaussDB Remarks
3 RX RowExclusive -
4 S ShareUpdateExclu-
sive
-
5 SRX Share -
6 \ ShareRowExclusive -
7 X Exclusive -
8 \ AccessExclusive -
7.2.2.2 Data Type Comparison Rules
Data type comparison (collation) rules are followed when values of the same data
type are compared (collated).
Table 7-126 Comparison rules
N
o.
Oracle Gauss
DB
Dierence Rule Description
1 Numeric
values
Suppo
rted.
- For comparison based
on numeric values, a
number close to the
positive direction of a
number axis is greater
than a number close
to the negative
direction of the
number axis, for
example, 5 > 3, 1 > –1,
and –1 > –2.
2 Datetime
values
Suppo
rted.
- For comparison based
on datetime values,
the later date or
timestamp is greater
than the earlier date
or timestamp, for
example, '2000-01-01
12:00:00' >
'2000-01-01 11:59:59'.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 209
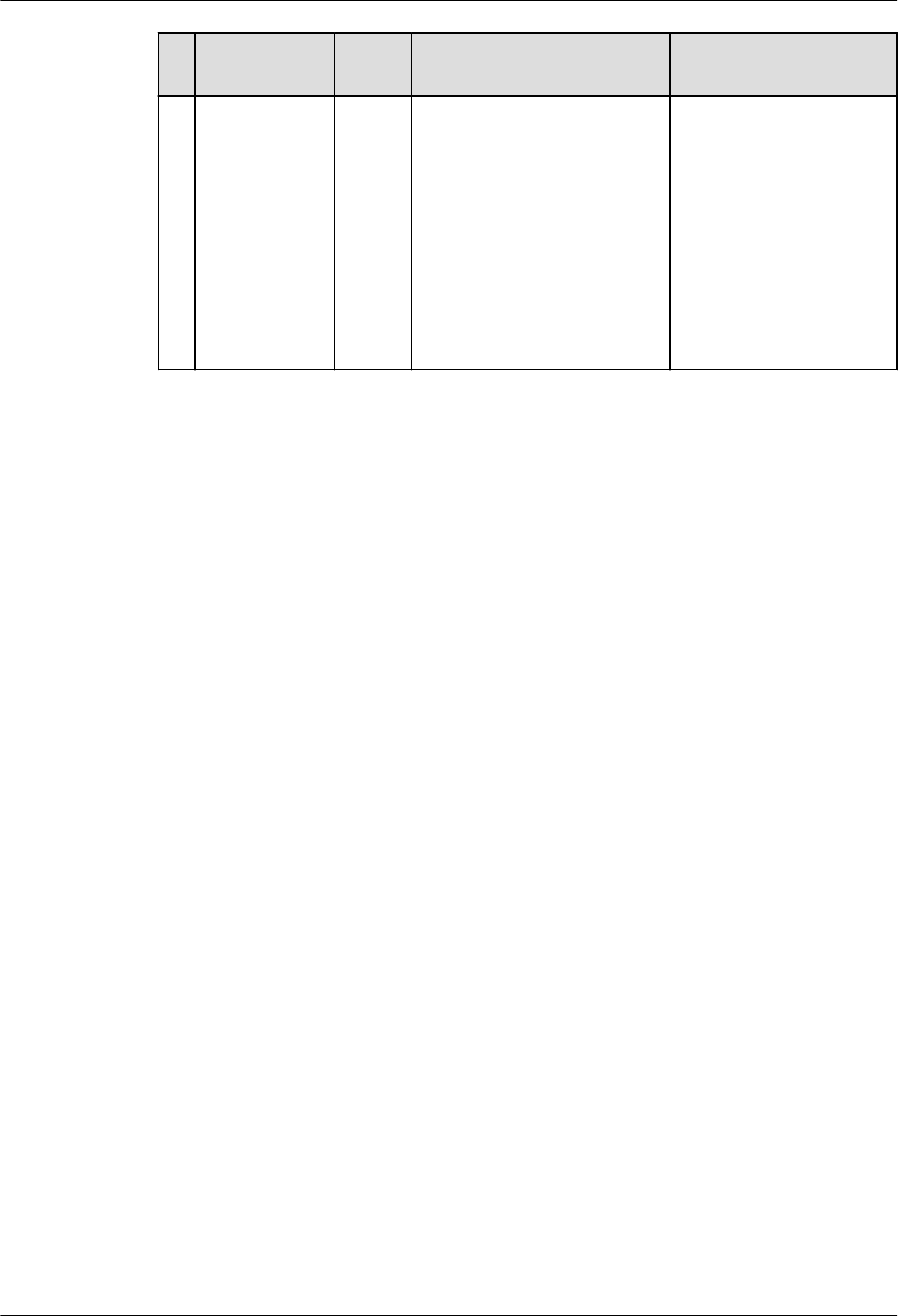
N
o.
Oracle Gauss
DB
Dierence Rule Description
3 Binary values Suppo
rted.
- For comparison based
on binary values, a
number close to the
positive direction of a
number axis is greater
than a number close
to the negative
direction of the
number axis, for
example, 1001 0101 >
1001 0011.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 210

N
o.
Oracle Gauss
DB
Dierence Rule Description
4 Character
values
Suppo
rted,
with
diere
nces.
● The following contents
are dierent:
– GaussDB and Oracle
support dierent
comparison rules,
and the names of
the same
comparison rules
may be dierent.
– GaussDB and Oracle
dier in specifying
comparison rules.
For example, table-
level comparison
rules cannot be
specied in
GaussDB, but can be
specied in Oracle.
– GaussDB and Oracle
dier in the syntax
for specifying
comparison rules.
For example, in
GaussDB, the
ENCODING,
LC_CTYPE, and
LC_COLLATE
parameters are used
to specify the
character set,
character type, and
comparison rules
used during
database creation.
For details, see "SQL
Reference > SQL
Syntax > C >
CREATE DATABASE"
in
Developer Guide
.
In Oracle,
comparison rules at
dierent levels are
usually specied by
a series of
parameters with the
NLS prex.
● The following contents
are the same:
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 211

N
o.
Oracle Gauss
DB
Dierence Rule Description
– In GaussDB and
Oracle, character
strings are
compared character
by character starting
from the rst
character. If the rst
character is the
same, the next
character is
compared until
dierent characters
appear or a
character string
ends. If all
characters of two
strings are the
same, they are
considered equal.
Otherwise, the size
relationship of the
rst found dierent
characters is used
for comparison. In
addition, for some
data types, such as
CHAR, spaces are
added to the shorter
string until two
strings have the
same length, and
then the strings are
collated.
– For single-character
comparison,
common
comparison rules
include binary
collation based on
the character set
and monolingual
collation. If the
default character set
and comparison
rules are used, both
GaussDB and Oracle
use monolingual
collation.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 212

N
o.
Oracle Gauss
DB
Dierence Rule Description
– In GaussDB and
Oracle, the
comparison rules of
character types are
closely related to
character sets. For
example, most non-
Unicode character
sets do not support
monolingual
collation. Therefore,
binary collation is
used by default.
5 Object
values
Not
suppo
rted.
- -
6 Varrays and
nested tables
Suppo
rted,
with
diere
nces.
Both Oracle and GaussDB
support the comparison of
varrays. Dierent from
Oracle, GaussDB not only
supports the comparison
of the number of
elements in two varrays,
but also supports the
comparison between
varrays of the same type.
-
7 Data type
precedence
Suppo
rted.
- -
8 Explicit/
Implicit data
conversion
Suppo
rted.
- -
7.2.2.3 Literals
Table 7-127 Literals
No.
Oracle GaussDB
1 Text literals Supported.
2 Numeric literals Supported.
3 Datetime literals Supported.
4 Interval literals Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 213

7.2.2.4 Format Models
Table 7-128 Formats
No. Oracle GaussDB Dierence
1 Number
formats
Supported
, with
dierence
s.
GaussDB supports the $, C, TM,
TM9, TME, and U formats only
when a_format_version is set to
10c and a_format_dev_version is
set to s1. In addition, the fmt
parameter cannot be set to TH, PL,
or SG in this case.
For details about GaussDB, see the
fmt parameter of the number
type table in "SQL Reference >
Functions and Operators > Type
Conversion Functions" in
Developer
Guide
.
2 Datetime
formats
Supported
, with
dierence
s.
GaussDB: Parameters used for time
truncation and rounding are valid
only when a_format_version is set
to 10c and a_format_dev_version is
set to s1.
For details about GaussDB support,
see formats for formatting date and
time in "SQL References > Functions
and Operators > Date and Time
Processing Functions and
Operators" in
Developer Guide
.
3 Format model
modiers
Supported
.
-
4 String-to-date
conversion
rules
Supported
, with
dierence
s.
GaussDB: The to_timestamp_tz
function is valid only when
a_format_version is set to 10c and
a_format_dev_version is set to s1.
For details about GaussDB, see
to_date, to_timestamp, and
to_timestamp_tz in "SQL Reference
> Functions and Operators > Type
Conversion Functions" in
Developer
Guide
.
5 XML format
models
Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 214

7.2.2.5 Nulls
Table 7-129 Nulls
No. Oracle GaussDB
1 IS NULL and IS NOT NULL Supported.
2 NULLS in conditions Supported.
7.2.2.6 Comments
Table 7-130 Comments
No. Oracle GaussDB Dierence
1 A slash and an
asterisk (/*)
Supported. -
2 Two hyphens
(--)
Supported. -
3 COMMENT
command
Supported. -
4 HINT Supported,
with
dierences.
GaussDB does not support the
'--+' hint format.
For details, see "SQL Tuning
Guide > Tuning Using Plan
Hints" in
Developer Guide
.
7.2.2.7 Database Objects
Table 7-131 Schema objects
No.
Oracle GaussDB Dierence
1 Analytic views Not
supported.
-
2 Attribute
dimensions
Not
supported.
-
3 Clusters Supported. -
4 Constraints Supported. -
5 Database links Supported. -
6 Database
triggers
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 215

No. Oracle GaussDB Dierence
7 Dimensions Supported. -
8 External
procedure
libraries
Not
supported.
-
9 Hierarchies Not
supported.
-
10 Index-
organized
tables
Not
supported.
-
11 Indexes Supported. -
12 Index types Not
supported.
-
13 Java classes Not
supported.
-
14 Java resources Not
supported.
-
15 Java source
code
Not
supported.
-
16 Join groups Not
supported.
-
17 Materialized
views
Supported. -
18 Materialized
view logs
Not
supported.
-
19 Mining models Not
supported.
-
20 Object tables Not
supported.
-
21 Object types Not
supported.
-
22 Object views Not
supported.
-
23 Operators Supported. -
24 Packages Supported. -
25 Sequences Supported. -
26 Storage
functions
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 216

No. Oracle GaussDB Dierence
27 Stored
procedures
Supported. -
28 Synonyms Supported,
with
dierences.
The names of Oracle objects in the
same namespace must be unique.
In GaussDB, the name of a
synonym can be the same as that
of a table, view, function, or
package in the same namespace. In
this case, GaussDB preferentially
accesses the object with the
original name. If the object with
the original name is not found,
GaussDB searches for the object to
which the synonym points. PUBLIC
synonyms are searched only when
the schema name is a username.
29 Tables Supported. -
30 Views Supported. -
31 Zone map Not
supported.
-
Table 7-132 Nonschema objects
No.
Oracle GaussDB
1 Contexts Not supported.
2 Directories Supported.
3 Editions Not supported.
4 Flashback archives Not supported.
5 Lockdown proles Not supported.
6 Proles Not supported.
7 Restore points Supported.
8 Roles Supported.
9 Rollback segments ● Ustore supports rollback
segments.
● Astore does not support
rollback segments.
10 Tablespaces Supported.
11 Tablespace sets Not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 217

No. Oracle GaussDB
12 Unied audit policies Supported.
13 Users Supported.
7.2.2.8 Database Object Names and Qualiers
Table 7-133 Naming rules
No. Oracle GaussDB Dierence
1 Database object naming
rules
Supported, with
dierences.
GaussDB uses
lowercase
letters by
default.
2 Schema object naming
rules
Supported. -
7.2.2.9 Syntax for Schema Objects and Parts in SQL Statements
Table 7-134 Object reference
No.
Oracle GaussDB
1 General syntax for referring to an
object
Supported.
2 Resolving a reference to an object Supported.
3 Referring to objects in other
schemas
Supported.
4 Referring to objects in remote
databases
Supported.
5 Referring to partitions and
subpartitions of tables and indexes
Supported.
7.2.3 Pseudocolumns
GaussDB is compatible with hierarchical query pseudocolumns, sequence
pseudocolumns, and rownum pseudocolumns. Other pseudocolumns are not
supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 218

Hierarchical Query Pseudocolumns
Table 7-135 Hierarchical query pseudocolumns
No. Oracle GaussDB
1 connect_by_iscycle Supported.
2 connect_by_isleaf Supported.
3 LEVEL pseudocolumn Supported.
Sequence Pseudocolumns
Table 7-136 Sequences
No. Oracle GaussDB Dierence
1 currval Supported, with
dierences.
It is implemented as a
function in GaussDB.
The call mode is
compatible with
Oracle.
2 nextval Supported, with
dierences.
It is implemented as a
function in GaussDB.
The call mode is
compatible with
Oracle.
ROWNUM Pseudocolumn
Table 7-137 rownum
No.
Oracle GaussDB Dierence
1 rownum Supported, with
dierences.
When Oracle uses rownum in
the left, right, and full join
conditions for ltering, the
performance varies according to
the conditions. The rownum
condition may be ignored or
partially ignored. However,
GaussDB lters the results after
left, right, and full join.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 219

7.2.4 Operators
GaussDB is basically compatible with Oracle operators.
SQL Operators
Table 7-138 SQL operators
No. Oracle GaussDB
1 Unary and binary operators Supported.
2 Operator precedence Supported.
Arithmetic Operators
Table 7-139 Arithmetic operators
No. Oracle GaussDB
1 Unary operators: positive (+) and
negative (–).
Supported.
2 Binary operators: addition (+) and
subtraction (–).
Supported.
3 Binary operators: multiplication (*)
and division (/).
Supported.
COLLATE Operator
Table 7-140 COLLATE operator
No.
Oracle GaussDB
1 COLLATE collation_name Supported.
Connection Operators
Table 7-141 Connection operators
No.
Oracle GaussDB
1 || Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 220

Hierarchical Query Operators
Table 7-142 Hierarchical query operators
No. Oracle GaussDB Dierence
1 prior Supported,
with
dierences
.
GaussDB: Only common columns
can be called. Functions cannot be
called.
2 connect_by_ro
ot
Supported,
with
dierences
.
GaussDB: When connect_by_root is
called, if parentheses are used to
modify the operation value, the
behavior is the same as that of
Oracle. If parentheses are not
used, this operator can be called
only for common columns.
Set Operators
Table 7-143 Set operators
No.
Oracle GaussDB
1 union Supported.
2 union all Supported.
3 intersect Supported.
4 minus Supported.
Multiset Operators
Table 7-144 Multiset operators
No.
Oracle GaussDB
1 multiset except Supported.
2 multiset intersect Supported.
3 multiset union Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 221

User-dened Operators
Table 7-145 User-dened operators
No. Oracle GaussDB Dierence
1 CREATE OPERATOR Supported, with
dierences.
● Oracle
provides
CONTEXT_C
LAUSE to
dene
functional
evaluation
functions,
which is
dierent
from
GaussDB
that
constrains
selectivity
evaluation
functions.
GaussDB
does not
support
user-dened
functional
evaluation
functions.
● Optional
parameters
in Oracle
dier
greatly from
those in
GaussDB.
For details,
see the
GaussDB
parameter
description
in "SQL
Reference >
SQL Syntax
> C >
CREATE
OPERATOR"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 222

Comparison Operators
No. Oracle GaussDB
1 < = Supported.
2 < > Supported.
3 > = Supported.
4 ^ = Supported.
5 ! = Not supported. For !=,
if there is a space
between an
exclamation mark (!)
and an equal sign (=),
the exclamation mark
will be identied as
factorial.
For comparison operators <=, <>, >=, and ^=, if there is a space between two
symbols, it does not aect normal operations. For !=, if there is a space between
an exclamation mark (!) and an equal sign (=), the exclamation mark will be
identied as factorial, which may cause the result to be inconsistent with the
expected result.
7.2.5 Expressions
GaussDB is compatible with most Oracle expressions.
Table 7-146 Expressions
No.
Oracle GaussDB Dierence
1 Simple expressions Supported. -
2 Analytic view expressions Not supported. -
3 Compound expressions Supported. -
4 CASE expressions Supported. -
5 Column expressions Supported. -
6 CURSOR expressions Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 223

No. Oracle GaussDB Dierence
7 Datetime expressions Supported, with
dierences.
GaussDB
command
output does
not contain
time zone
information,
but Oracle
contains time
zone
information
similar to
"PM
AMERICA/
LOS_ANGELE
S."
8 Function expressions Supported. -
9 Interval expressions Partially supported. GaussDB
supports
statements in
the format of
"SELECT
INTERVAL
'999999999
23:59:59.999'
day(9) to
second
FROM
DUAL;" but
does not
support
statements in
the format of
"SELECT(SYS
DATE-
SYSDATE)
DAY TO
SECOND
FROM
DUAL;". They
are
supported in
Oracle.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 224

No. Oracle GaussDB Dierence
10 JSON object access
expressions
Partially supported,
with dierences.
1. GaussDB
can extract
values from
JSON objects
in "->'key'"
mode, while
Oracle can
extract values
in ".key"
mode.
2. For
JSONARRY
objects,
Oracle can
extract values
correspondin
g to all keys
at a time in
".key" mode.
However,
GaussDB
does not
support this
function.
11
Model expressions Not supported. -
12 Object expressions Not supported. -
13 Placeholder expressions Partially supported. GaussDB
supports
general
placeholder
expressions
such as
":var", but
does not
support the
combination
of two
general
placeholder
expressions
using the
INDICATOR
keyword.
14 Scalar subquery
expressions
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 225
No. Oracle GaussDB Dierence
15 Type constructor
expressions
Partially supported. The NEW
keyword
cannot be
specied
before the
type
constructor
in GaussDB,
but it can be
specied
before the
type
constructor
in Oracle.
16 Expression lists Supported. -
7.2.6 Conditions
GaussDB is compatible with most Oracle conditions.
Table 7-147 Conditions
No.
Oracle GaussDB Dierence
1 Comparison conditions Supported, with
dierences.
Dierences
exist when
statements
contain the
ANY, SOME,
and ALL
operators.
Oracle
supports
operations
on list
objects, but
GaussDB
needs to
convert list
objects into
array
expressions
before
performing
operations.
2 Floating-point conditions Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 226

No. Oracle GaussDB Dierence
3 Logical conditions Supported. -
4 Model conditions Not supported. -
5 Multiset conditions Not supported. -
6 Pattern-matching
conditions
Supported. -
7 NULL conditions Supported. -
8 XML conditions Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 227

No. Oracle GaussDB Dierence
9 SQL/JSON conditions Partially supported,
with dierences.
● GaussDB
does not
support
the IS
JSON and
JSON_TEX
TCONTAI
NS
conditions
.
● The
JSONB_EQ
condition
in
GaussDB
is the
same as
the
JSON_EQ
UAL
condition
in Oracle.
However,
GaussDB
does not
support
the
ERROR
clause.
● The
JSONB_EX
ISTS
condition
in
GaussDB
is the
same as
the
JSON_EXI
STS
condition
in Oracle.
However,
GaussDB
does not
support
the
ERROR,
EMPTY, or
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 228

No. Oracle GaussDB Dierence
PASSING
clauses.
10 Compound conditions Supported. -
11 BETWEEN condition Supported. -
12 EXISTS condition Supported. -
13 IN condition Supported. -
14 IS OF TYPE condition Not supported. -
7.2.7 Common SQL DDL Clauses
GaussDB is compatible with some DDL clauses.
Table 7-148 Common SQL DDL clauses
No. Oracle GaussDB Dierence
1 allocate_extent_clause Not
supported.
-
2 constraint Supported
.
-
3 deallocate_unused_claus
e
Not
supported.
-
4 le_specication Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 229

No. Oracle GaussDB Dierence
5 logging_clause Partially
supported,
with
dierence
s.
● GaussDB does not
support the
LOGGING and
FILESYSTEM_LIKE_LO
GGING constraint
clauses.
● GaussDB supports
only table-level
UNLOGGED
constraints and does
not support column-
level UNLOGGED
constraints.
● GaussDB uses
logging clauses only
in the CREATE
TABLE, CREATE
TABLE AS, and
SELECT INTO
statements.
6 parallel_clause Not
supported.
-
7 physical_attributes_claus
e
Partially
supported,
with
dierence
s.
● GaussDB does not
support PCTUSED.
● GaussDB uses
physical attribute
clauses only in the
CREATE TABLE and
CREATE INDEX
statements.
8 size_clause Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 230

No. Oracle GaussDB Dierence
9 storage_clause Partially
supported,
with
dierence
s.
● In Oracle, storage
parameters are
specied by the
STORAGE clause. In
GaussDB, storage
parameters are
specied by the
WITH clause.
● Optional storage
parameters in
GaussDB are greatly
dierent from those
in Oracle. For details,
see the GaussDB
parameter
description in "SQL
Reference > SQL
Syntax > C > CREATE
TABLE" in
Developer
Guide
. WITH
({storage_paramete
r = value} [, ...])
describes the storage
parameters
supported by the
CREATE TABLE
statement.
10
Aggregate function
nesting
Supported
.
-
7.2.8 SQL Queries and Subqueries
GaussDB is compatible with SQL queries and subqueries except hierarchical
queries.
Table 7-149 SQL queries and subqueries
No.
Oracle GaussDB Dierence
1 Creating simple
queries
Supported. -
2 Hierarchical
queries
Supported,
with
dierences.
GaussDB supports only
Oracle's
CONNECT_BY_FILTERING
and does not support
CONNECT_BY_NOFILTERI
NG.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 231

No. Oracle GaussDB Dierence
3 UNION [ALL],
INTERSECT,
MINUS
Supported. -
4 Sorting query
results
Supported,
with
dierences.
If the GaussDB query does
not contain groups and
the target column
contains both an
aggregate function and a
set return function, the
sorting of the set return
function column is not
ignored.
5 Joins Supported,
with
dierences.
GaussDB supports only
join types with Oracle,
such as left/right, self,
natural, and full outer
join. Join optimization
methods such as IN-
MEMORY JOIN GROUP
are not supported.
6 Using subqueries Supported. -
7 Unnesting of
nested subqueries
Supported,
with
dierences.
HASH_AJ or MERGE_AJ
cannot be explicitly
specied in GaussDB.
8 Distributed
queries
Supported,
with
dierences.
GaussDB needs to
explicitly specify a
database link for query.
9 Aggregate
function nesting
Supported. -
7.2.9 PL/SQL Language
GaussDB is compatible with PL/SQL operators, expressions, control statements,
collections, and records, but does not support predened PL/SQL constants, types,
and subtypes.
7.2.9.1 Basic PL/SQL Syntax
Table 7-150 PL/SQL operators
No.
Oracle GaussDB
1 + Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 232

No. Oracle GaussDB
2 := Supported.
3 => Supported.
4 % Supported.
5 ' Supported.
6 . Supported.
7 || Supported.
8 / Supported.
9 ** Not supported.
10 ( Supported.
11 ) Supported.
12 : Supported.
13 , Supported.
14 << Supported.
15 >> Supported.
16 /* Supported.
17 */ Supported.
18 * Supported.
19 " Supported.
20 .. Supported.
21 = Supported.
22 <> Supported.
23 != Supported.
24 ~= Supported.
25 ^= Supported.
26 < Supported.
27 > Supported.
28 <= Supported.
29 >= Supported.
30 @ Supported.
31 -- Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 233

No. Oracle GaussDB
32 ; Supported.
33 - Supported.
Table 7-151 Logical operators
No. Oracle GaussDB
1 NOT Supported.
2 AND Supported.
3 OR Supported.
Table 7-152 Comparison expressions
No. Oracle GaussDB
1 IS [NOT] NULL Supported.
2 LIKE Supported.
3 BETWEEN Supported.
4 IN Supported.
Table 7-153 CASE expressions
No.
Oracle GaussDB
1 simple CASE Supported.
2 searched CASE Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 234

Table 7-154 Parameters related to variable declaration
No. Oracle GaussDB Dierence
1 %TYPE Supported, with
dierences.
● GaussDB does not
support
record%type
.
● GaussDB does not
support pkg.
record
%type
and
schema.pkg.
record
%type
as the input
and output
parameter types.
● In GaussDB,
Table/
View
.column.
column
%type
or
schema.
Table/
View
.column.
column
%type
cannot be
nested with one or
more layers as
variable types or
input/output
parameter type.
● In GaussDB,
record
.column.
colum
n%type
and
pkg.
record
.column.
c
olumn%TYPE
cannot
be nested with a
column type of
records at one or
more layers as the
variable type or
input/output
parameter type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 235

No. Oracle GaussDB Dierence
2 %ROWTYPE Supported, with
dierences.
● When GaussDB has
multiple CNs, the
%ROWTYPE and
%TYPE attributes of
the temporary table
cannot be declared in
a stored procedure.
The temporary table
is valid only in the
current session.
During compilation,
other CNs cannot
view the temporary
table of the current
CN. Therefore, if
there are multiple
CNs, the system
displays a message
indicating that the
temporary table does
not exist.
● GaussDB does not
support
view
%rowtype
and
schema.
view
%rowtype
as the
input and output
parameter types.
● GaussDB does not
support the
package.
cursor
%rowtype
as the
input and output
parameter types.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 236
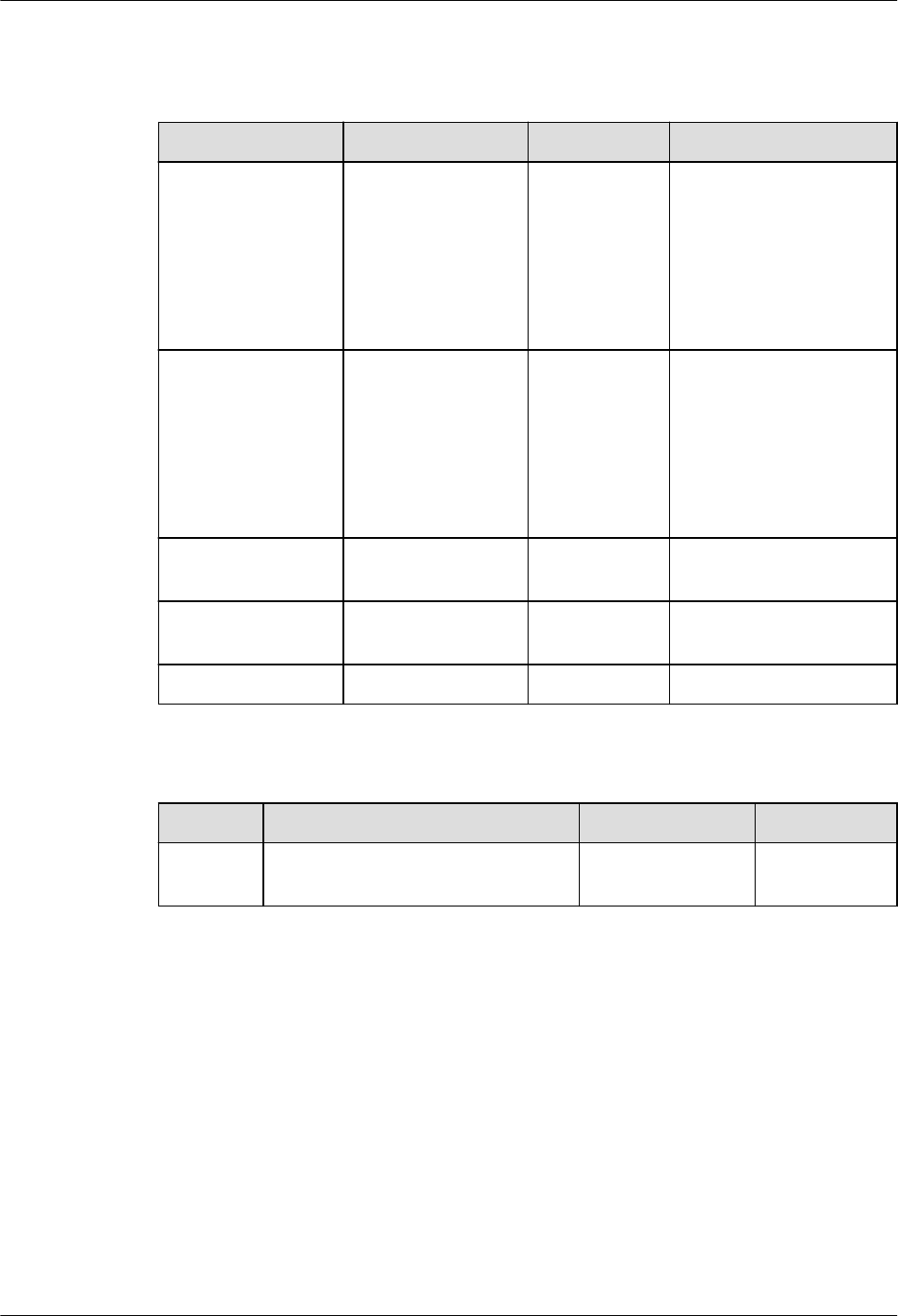
7.2.9.2 Data Type Compatibility
Table 7-155 Other PL/SQL data types
No. Oracle GaussDB Dierence
1 CHARACTER Supported,
with
dierences.
● GaussDB: The
length ranges from
1 to 10485760
bytes.
● Oracle: The length
ranges from 1 to
32767 bytes.
2 VARCHAR Supported,
with
dierences.
● GaussDB: The
length ranges from
1 to 10485760
bytes.
● Oracle: The length
ranges from 1 to
32767 bytes.
3 STRING Not
supported.
-
4 PLS_INTEGER Not
supported.
In GaussDB, you can
use the INT type.
5 BINARY_INTEGER Supported. -
Table 7-156 User-dened PL/SQL subtypes
No.
Oracle GaussDB Dierence
1 SUBTYPE subtype_name IS
base_type
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 237
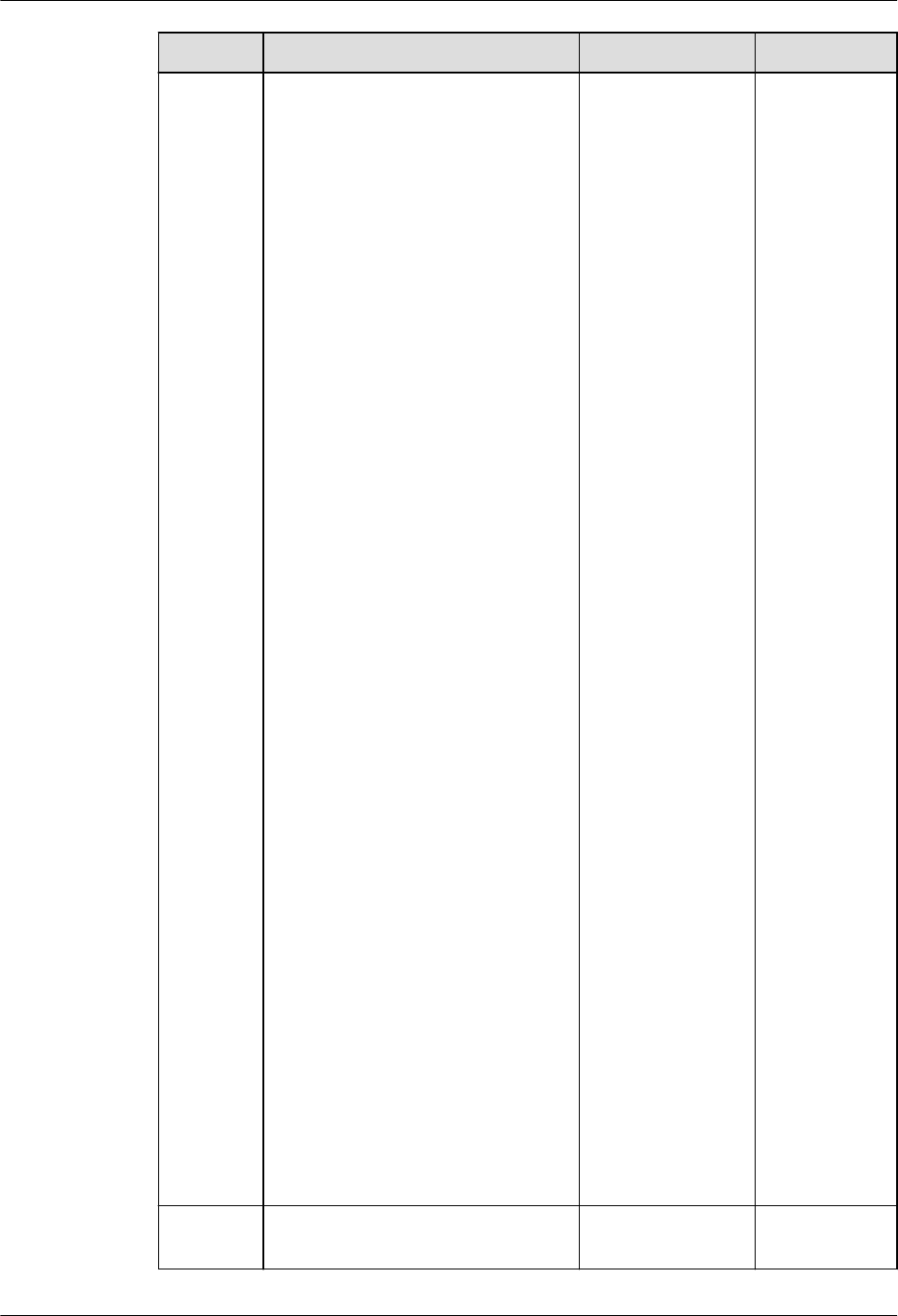
No. Oracle GaussDB Dierence
2 SUBTYPE subtype_name IS
base_type
{ precision [, scale ] | RANGE
low_value .. high_value } [ NOT
NULL ]
Supported, with
dierences.
● In
GaussDB,
only the
INT type
supports
the
RANGE
constraint.
In Oracle,
only
PLS_INTE
GER,
BINARY_I
NTEGER,
and their
predened
subtypes
support
the
RANGE
constraint.
● In
GaussDB,
the
RANGE
constraint
cannot be
specied
when
variables
are
dened.
● In
GaussDB,
the
character
set
informatio
n cannot
be
specied
when the
base type
of subtype
is the
character
data type.
3
SUBTYPE subtype_name IS
base_type [ NOT NULL ]
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 238

7.2.9.3 Control Statements
Table 7-157 Conditional statements
No. Oracle GaussDB
1 IF THEN Supported.
2 IF THEN ELSE Supported.
3 IF THEN ELSIF Supported.
4 simple CASE:
CASE selector
WHEN selector_value_1 THEN
statements_1
WHEN selector_value_2 THEN
statements_2
...
WHEN selector_value_n THEN
statements_n
[ ELSE
else_statements
END CASE;]
Supported.
5 searched CASE:
CASE
WHEN condition_1 THEN statements_1
WHEN condition_2 THEN statements_2
...
WHEN condition_n THEN statements_n
[ ELSE
else_statements
END CASE;]
Supported.
Table 7-158 LOOP statements
No.
Oracle GaussDB
1 [ label ] LOOP
statements
END LOOP [ label ];
Supported.
2 EXIT; Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 239

No. Oracle GaussDB
3 EXIT WHEN; Supported.
4 CONTINUE; Supported.
5 CONTINUE WHEN; Supported.
Table 7-159 FOR LOOP statements
No. Oracle GaussDB Dierence
1 [ label ] FOR index IN
[ REVERSE ]
lower_bound..upper_bound
LOOP
statements
END LOOP [ label ];
Supported, with
dierences.
When the
keyword
REVERSE is
used in
GaussDB, the
lower bound
must be
greater than
or equal to
the upper
bound;
otherwise,
the loop
body is not
executed.
2 EXIT WHEN; Supported. -
3 CONTINUE WHEN; Supported. -
Table 7-160 WHILE LOOP statement
No.
Oracle GaussDB
1 [ label ] WHILE condition LOOP
statements
END LOOP [ label ];
Supported.
Table 7-161 GOTO statement
No.
Oracle GaussDB
1 GOTO Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 240

Table 7-162 NULL statement
No. Oracle GaussDB
1 NULL Supported.
7.2.9.4 Collections and Records
Table 7-163 Types
No. Oracle GaussDB
1 Associative array (or index-by
table)
Supported.
2 VARRAY (variable-size array) Supported.
3 Nested table Supported.
4 record Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 241

Table 7-164 Syntax
Type Oracle GaussDB Dierence
Associative
array (or
index-by table)
TABLE OF datatype
[ NOT NULL ]
INDEX BY
{ PLS_INTEGER |
BINARY_INTEGER |
VARCHAR2 ( v_size )
| data_type }
Supported,
with
dierences.
● GaussDB does not
support the
PLS_INTEGER
type. In GaussDB,
the value of
data_type can be
a base data type
or a record type,
collection type, or
array type dened
in a stored
procedure. The ref
cursor type is not
supported.
● In GaussDB, NOT
NULL does not
take eect in the
syntax. That is,
the system does
not check
whether an
element is NULL.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records >
Collections" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 242
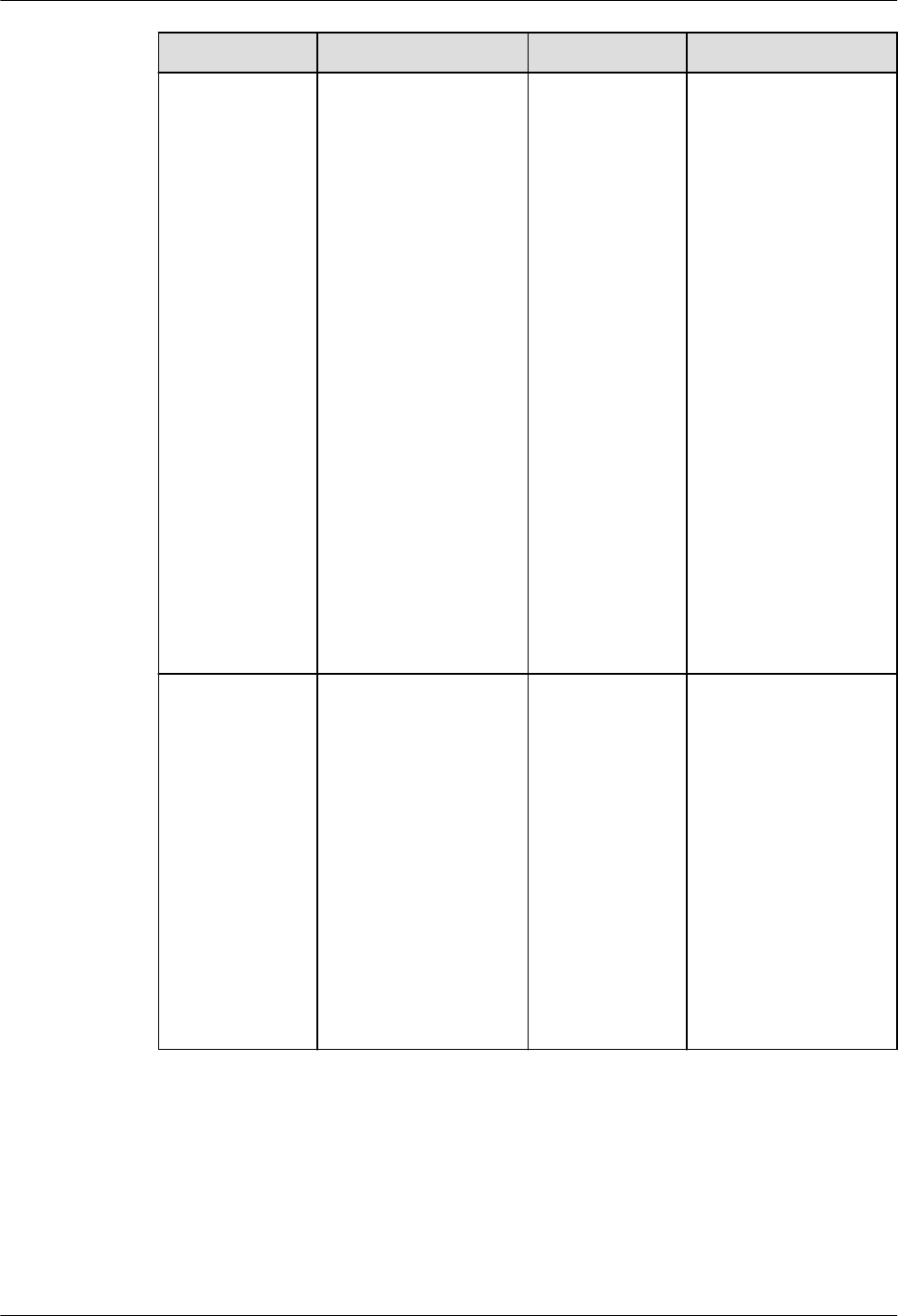
Type Oracle GaussDB Dierence
VARRAY
(variable-size
array)
{ VARRAY |
[ VARYING ] ARRAY }
( size_limit )
OF datatype [ NOT
NULL ]
Supported,
with
dierences.
● GaussDB does not
support the NOT
NULL syntax.
● In GaussDB,
datatype cannot
be set to varray
(varray cannot be
nested).
● To make the
size_limit function
take eect,
enable the
varray_compat
parameter in the
GUC parameter
behavior_compat
_options.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records > Arrays"
in
Developer
Guide
.
Nested table
TABLE OF datatype
[ NOT NULL ]
Supported,
with
dierences.
● In GaussDB, NOT
NULL does not
take eect in the
syntax. That is,
the system does
not check
whether an
element is NULL.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records >
Collections" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 243
Type Oracle GaussDB Dierence
record TYPE record_type IS
RECORD
( eld_denition [,
eld_denition]... ) ;
Supported. ● Record columns
can be dened as
NOT NULL or a
default value can
be specied. If the
record type is
nested in other
types, the default
value and NOT
NULL of the
record type do
not take eect. If
a record variable
is created using
the
package.record_ty
pe access type,
the default value
and NOT NULL of
the record
variable do not
take eect.
● For details, see
"Stored Procedure
> Arrays,
Collections, and
Records >
Records" in
Developer Guide
.
Table 7-165 Constructor
No.
Oracle GaussDB
1 collection_type ( [ value [,
value ]... ] )
Supported.
Table 7-166 Variable assignment
No.
Oracle GaussDB Dierence
1 Associative array (or
index-by table)
Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 244
No. Oracle GaussDB Dierence
2 VARRAY (variable-
size array)
Supported, with
dierences.
● Values of
dierent VARRAY
data in GaussDB
can be assigned
to each other,
depending on
whether
elements in the
data can be
implicitly
converted to
each other.
● For details, see
"Stored
Procedure >
Arrays,
Collections, and
Records > Arrays"
in
Developer
Guide
.
3 Nested table Supported. -
4 record Supported, with
dierences.
● Values of
dierent record
data in GaussDB
can be assigned
to each other,
depending on
whether columns
can be implicitly
converted.
● For details, see
"Stored
Procedure >
Arrays,
Collections, and
Records >
Records" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 245

Table 7-167 Collection operators
No. Oracle GaussDB Dierence
1 = Supported, with
dierences.
Oracle: The
sequence of
collection members
is ignored during
comparison.
GaussDB: The
comparison is
performed strictly
based on the
sequence of
collection members.
2 <> Supported, with
dierences.
Oracle: The
sequence of
collection members
is ignored during
comparison.
GaussDB: The
comparison is
performed strictly
based on the
sequence of
collection members.
3 IS[NOT] NULL Supported. -
4 ^= Supported, with
dierences.
Oracle: The
sequence of
collection members
is ignored during
comparison.
GaussDB: The
comparison is
performed strictly
based on the
sequence of
collection members.
5 ~= Not supported. -
6 IS[NOT] A SET Not supported. -
7 IS [NOT] EMPTY Not supported. -
8 expr [ NOT ]
MEMBER [ OF ]
nested_table
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 246
No. Oracle GaussDB Dierence
9 nested_table1
[ NOT ]
SUBMULTISET [ OF ]
nested_table2
Not supported. -
10 [NOT] IN Supported, with
dierences.
Oracle: The
sequence of
collection members
is ignored during
comparison.
GaussDB: The
comparison is
performed strictly
based on the
sequence of
collection members.
Table 7-168 MULTISET functions
No.
Oracle GaussDB
1 MULTISET UNION [ALL |
DISTINCT]
Supported.
2 MULTISET EXCEPT [ALL |
DISTINCT]
Supported.
3 MULTISET INTERSECT [ALL |
DISTINCT]
Supported.
Table 7-169 Collection type functions
No.
Oracle GaussDB Dierence
1 exists(idx) Supported. -
2 extend[(count[,
idx])]
Supported, with
dierences.
GaussDB supports
only nested tables.
3 delete[(idx1[,
idx2])]
Supported. -
4 trim[(n)] Supported, with
dierences.
GaussDB supports
only nested tables.
5 count Supported. -
6 rst Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 247

No. Oracle GaussDB Dierence
7 last Supported. -
8 prior(idx) Supported. -
9 next(idx) Supported. -
10 limit Supported, with
dierences.
In GaussDB, the
maximum number
of elements that
can be stored in a
nested-table
collection is
returned. This
function applies
only to the array
type. The return
value is null.
Table 7-170 Record variable operations
No.
Oracle GaussDB
1 Constructors Supported.
2 %ROWTYPE to declare a
variable
Supported.
3 Dening constants Not supported.
Table 7-171 Collection-related functions
No.
Oracle GaussDB
1 unnest_table(anynesttable) Supported.
2 unnest_table(anyindexbytabl
e)
Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 248

7.2.9.5 Static SQL Statements
Table 7-172 Static query SQL statements
No. Oracle GaussDB Dierence
1 SELECT Supported, with
dierences.
GaussDB and
Oracle are
dierent in some
scenarios.
GaussDB: Shared
locks in dierent
transactions do
not block each
other in the
following
scenarios:
SELECT FOR
SHARE - SELECT
FOR SHARE;
SELECT FOR
SHARE - SELECT
FOR KEY SHARE;
SELECT FOR KEY
SHARE - SELECT
FOR KEY SHARE;
SELECT FOR KEY
SHARE - SELECT
FOR NO KEY
UPDATE;
In the preceding
scenarios, because
there is no
blocking between
locks, the lock will
not be skipped
when SKIP
LOCKED is
specied for data
that has non-
blocking locks in
other
transactions.
Table 7-173 Static DML SQL statements
No.
Oracle GaussDB
1 INSERT Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 249

No. Oracle GaussDB
2 UPDATE Supported.
3 DELETE Supported.
4 MERGE Supported.
5 LOCK TABLE Supported.
Table 7-174 Static TCL SQL statements
No. Oracle GaussDB Dierence
1 COMMIT Supported. -
2 ROLLBACK Supported. -
3 SAVEPOINT Supported. -
4 SET
TRANSACTION
Supported, with
dierences.
GaussDB does not
support the
NAME string and
USE ROLLBACK
SEGMENT
rollback_segment
syntax.
Table 7-175 Pseudocolumns
No.
Oracle GaussDB Dierence
1 CURRVAL and
NEXTVAL
Supported. -
2 LEVEL Supported. -
3 OBJECT_VALUE Not supported. -
4 ROWID Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 250

No. Oracle GaussDB Dierence
5 ROWNUM Supported, with
dierences.
It is not
recommended
that the
ROWNUM
condition be used
in the JOIN ON
clause. In
GaussDB, when
the ROWNUM
condition is used
in the JOIN ON
clause, the
behavior in the
LEFT JOIN, RIGHT
JOIN, FULL JOIN,
and MERGE INTO
scenarios is
dierent from
that in other
databases,
causing risks in
service migration.
Table 7-176 Implicit cursor attributes
No.
Oracle GaussDB Dierence
1 SQL%FOUND Supported, with
dierences.
GaussDB does not
update the implicit
cursor result after
COMMIT or
ROLLBACK. Oracle
updates the implicit
cursor result after
COMMIT or
ROLLBACK.
2 SQL
%NOTFOUND
Supported, with
dierences.
3 SQL
%ROWCOUNT
Supported, with
dierences.
4 SQL%ISOPEN Supported, with
dierences.
5 SQL
%BULK_ROWCO
UNT
Not supported.
6 SQL
%BULK_EXCEPTI
ONS
Supported, with
dierences.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 251

Table 7-177 Explicit cursor syntax and keywords
No. Oracle GaussDB
1 CURSOR cursor_name
[ parameter_list ]
RETURN return_type;
Supported.
2 CURSOR cursor_name
[ parameter_list ]
[ RETURN return_type ]
IS select_statement;
Supported.
3 OPEN Supported.
4 CLOSE Supported.
5 FETCH Supported.
6 CURRENT OF CURSOR Supported.
Table 7-178 Explicit cursor attributes
No.
Oracle GaussDB
1 SQL%FOUND Supported.
2 SQL%NOTFOUND Supported.
3 SQL%ROWCOUNT Supported.
4 SQL%ISOPEN Supported.
Table 7-179 Cursor loop
No.
Oracle GaussDB
1 FOR LOOP Supported.
Table 7-180 Scenarios supported by autonomous transactions
No.
Oracle GaussDB
1 Stored procedures Supported.
2 Anonymous blocks Supported.
3 Functions Supported.
4 Packages Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 252

7.2.9.6 Dynamic SQL Statements
Table 7-181 Dynamic SQL statement execution modes
No. Oracle GaussDB Dierence
1 EXECUTE
IMMEDIATE
Supported, with
dierences.
● GaussDB uses
the
dynamic_sql_c
ompat
parameter to
determines
whether
variables with
the same
name read the
same
parameter and
check whether
the input and
output
parameter
types of the
bound
parameters are
the same as
those of the
statement
parameters
when the
stored
procedure is
called.
● GaussDB does
not support
scenarios
where some
bound
parameters in
anonymous
blocks are
called. For
example, when
dynamic
statements are
nested in
anonymous
blocks,
expressions are
used to bind
parameters.
For details, see
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 253
No. Oracle GaussDB Dierence
"Stored
Procedure >
Dynamic
Statements >
Dynamically
Calling
Anonymous
Blocks" in
Developer
Guide
.
● GaussDB does
not support
RETURNING/
RETURN INTO.
2 OPEN FOR,
FETCH, CLOSE
Supported. -
7.2.9.7 Triggers
Table 7-182 Trigger types
No.
Oracle GaussDB Dierence
1 DML TRIGGER Supported, with
dierences.
GaussDB:
Compound DML
triggers are not
supported.
2 SYSTEM TRIGGER Not supported. -
Table 7-183 CREATE triggers
Syntax
Type
Oracle GaussDB Dierence
CREATE CREATE [ OR
REPLACE ]
[ EDITIONABLE |
NONEDITIONABLE ]
TRIGGER
plsql_trigger_source
Supported, with
dierences.
GaussDB does not
support
EDITIONABLE |
NONEDITIONABL
E, but supports
some behaviors of
plsql_trigger_sour
ce.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 254

Syntax
Type
Oracle GaussDB Dierence
plsql_trigg
er_source ::
=
[schema.]
trigger_name
[ sharing_clause ]
[ default_collation_cla
use ]
{ simple_dml_trigger
|
instead_of_dml_trigge
r
|
compound_dml_trigg
er
| system_trigger
}
Supported, with
dierences.
GaussDB: The
schema,
sharing_clause,
and
default_collation_
clause are not
supported.
simple_dml
_trigger ::=
{ BEFORE | AFTER }
dml_event_clause
[ referencing_clause ]
[ FOR EACH ROW ]
[ trigger_edition_claus
e ]
[ trigger_ordering_cla
use ]
[ ENABLE | DISABLE ]
[ WHEN
( condition ) ]
trigger_body
Supported, with
dierences.
GaussDB does not
support
referencing_clause
,
referencing_clause
(instead, the from
referencing_table
is used),
trigger_edition_cla
use,
trigger_ordering_c
lause, and
ENABLE |
DISABLE. It
supports some
behaviors of
trigger_body.
No error is
reported in
GaussDB when a
statement-level
BEFORE/AFTER
TRIGGER is
created in a view
without INSTEAD
OF TRIGGER. An
error is reported
when DML is
executed.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 255

Syntax
Type
Oracle GaussDB Dierence
dml_event_
clause ::=
{ DELETE | INSERT |
UPDATE [ OF column
[, column ]... ] }
[ OR { DELETE |
INSERT | UPDATE
[ OF column [,
column]... ] }...
ON [ schema.] { table
| view }
Not supported. -
trigger_bod
y ::=
{ plsql_block | CALL
routine_clause }
Supported, with
dierences.
In GaussDB,
plsql_block cannot
be declared as
PRAGMA
AUTONOMOUS_T
RANSACTION. For
the second
branch, similar
syntax is
supported. That is,
a function is
executed in
EXECUTE
PROCEDURE
function_name
( arguments );
mode. The
function needs to
be dened by
users. The
function must be
declared without
parameters and
the return type
must be trigger.
The function is
executed when
the trigger is
enabled.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 256

Syntax
Type
Oracle GaussDB Dierence
instead_of_
dml_trigge
r ::=
INSTEAD OF
{ DELETE | INSERT |
UPDATE } [ OR
{ DELETE | INSERT |
UPDATE } ]...
ON [ NESTED TABLE
nested_table_column
OF ] [ schema. ]
noneditioning_view
[ referencing_clause ]
[ FOR EACH ROW ]
[ trigger_edition_claus
e ]
[ trigger_ordering_cla
use ]
[ ENABLE | DISABLE ]
trigger_body
Supported, with
dierences.
GaussDB: The
NESTED TABLE
nested_table_colu
mn OF,
referencing_clause
,
trigger_edition_cla
use,
trigger_ordering_c
lause, and
ENABLE | DISABLE
are not supported.
compound
_dml_trigg
er ::=
CREATE trigger FOR
dml_event_clause ON
view
COMPOUND
TRIGGER
INSTEAD OF EACH
ROW IS BEGIN
statement;
END INSTEAD OF
EACH ROW;
Not supported. -
system_trig
ger ::=
{ BEFORE | AFTER |
INSTEAD OF }
{ ddl_event [OR
ddl_event]... |
database_event [OR
database_event ]... }
ON { [schema.]
SCHEMA |
[ PLUGGABLE ]
DATABASE }
[ trigger_ordering_cla
use ] [ ENABLE |
DISABLE ]
trigger_body
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 257

Table 7-184 ALTER trigger
No. Oracle GaussDB Dierence
1 ALTER TRIGGER
[ schema. ]
trigger_name
{ trigger_compile_clau
se
| { ENABLE |
DISABLE }
| RENAME TO
new_name
| { EDITIONABLE |
NONEDITIONABLE }
} ;
Supported, with
dierences.
GaussDB: The
schema,
trigger_compile_cl
ause, { ENABLE |
DISABLE }, and
{ EDITIONABLE |
NONEDITIONABL
E } are not
supported.
Table 7-185 drop trigger
No. Oracle GaussDB Dierence
1 DROP TRIGGER
[ schema. ] trigger ;
Supported, with
dierences.
GaussDB does not
support schemas.
You need to add
ON table_name
to the end of
trigger_name.
The *_TRIGGERS views in Oracle collect information about triggers. The views in
GaussDB are dierent from those in Oracle. For details, see sections
"DB_TRIGGERS", "ADM_TRIGGERS", "MY_TRIGGERSDB_TRIGGERS",
"ADM_TRIGGERS", and "MY_TRIGGERS" in "System Catalogs and System Views >
System Views > Other System Views" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 258

Table 7-186 Compatibilities of nested, package, and standalone subprograms
No. Oracle GaussDB Dierence
1 Nested subprogram
(subblock)
Supported, with
dierences.
Overloading,
denition of
autonomous
transactions, and
SETOF are not
supported. Only
one qualier can
reference nested
subprograms or
variables of
nested
subprograms.
2 package subprogram Supported. -
3 Standalone
subprogram (including
function & procedure)
Supported. -
4 Anonymous block Supported. -
Table 7-187 RETURN statements
No.
Oracle GaussDB
1 Function Supported.
2 Procedure Supported.
3 Anonymous block Supported.
Table 7-188 Function-related parameters
No.
Oracle GaussDB Dierence
1 DETERMINISTIC Supported, with
dierences.
In GaussDB, it is
IMMUTABLE.
2 PARALLEL_ENABLE Not supported. -
3 PIPELINED Not supported. -
4 RESULT_CACHE Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 259

Table 7-189 Parameter formats
No. Oracle GaussDB
1 IN Supported.
2 OUT Supported.
3 IN OUT Supported.
Table 7-190 CREATE statements
No. Oracle GaussDB Dierence
1 CREATE FUNCTION Supported,
with
dierences.
GaussDB does not
support the IF NOT
EXISTS syntax.
The sharing_clause is
not supported. Only
the
invoker_rights_clause
with the function
attribute is supported.
The keyword
[ EDITIONABLE |
NONEDITIONABLE ]
is not supported.
For details about the
syntax, see "SQL
Reference > SQL
Syntax > C > CREATE
FUNCTION" in
Developer Guide
.
2 CREATE LIBRARY Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 260

No. Oracle GaussDB Dierence
3 CREATE PACKAGE Supported,
with
dierences.
GaussDB does not
support the IF NOT
EXISTS syntax.
The sharing_clause is
not supported. Only
the
invoker_rights_clause
with the package
attribute is supported.
The keyword
[ EDITIONABLE |
NONEDITIONABLE ]
is not supported.
For details about the
syntax, see "SQL
Reference > SQL
Syntax > C > CREATE
PACKAGE" in
Developer Guide
.
4 CREATE PACKAGE
BODY
Supported,
with
dierences.
GaussDB does not
support the IF NOT
EXISTS syntax.
The sharing_clause
and keyword
[ EDITIONABLE |
NONEDITIONABLE ]
are not supported.
For details about the
syntax, see "SQL
Reference > SQL
Syntax > C > CREATE
PACKAGE" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 261
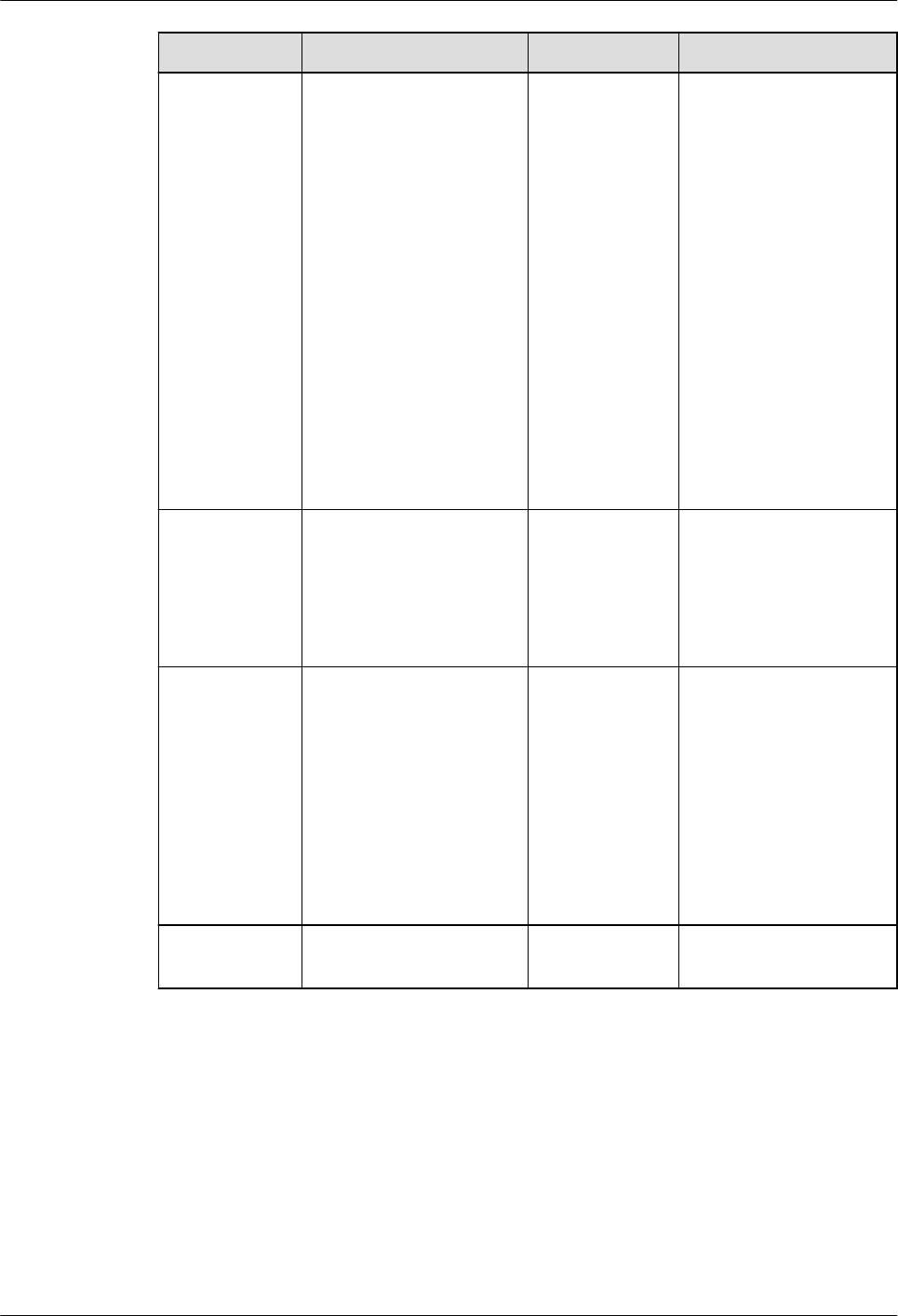
No. Oracle GaussDB Dierence
5 CREATE PROCEDURE Supported,
with
dierences.
GaussDB does not
support the IF NOT
EXISTS syntax.
The sharing_clause
and its following
clauses are not
supported. The
keyword
[ EDITIONABLE |
NONEDITIONABLE ]
is not supported.
For details about the
syntax, see "SQL
Reference > SQL
Syntax > C > CREATE
PROCEDURE" in
Developer Guide
.
6 CREATE TRIGGER Supported,
with
dierences.
For details about
GaussDB syntax, see
"SQL Reference > SQL
Syntax > C > CREATE
TRIGGER" in
Developer Guide
.
7 CREATE TYPE Supported,
with
dierences.
GaussDB does not
support the varray,
object type, and
UNDER syntax.
For details about the
syntax, see "SQL
Reference > SQL
Syntax > C > CREATE
TYPE" in
Developer
Guide
.
8 CREATE TYPE BODY Not
supported.
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 262

Table 7-191 ALTER statements
No. Oracle GaussDB Dierence
1 ALTER FUNCTION Supported, with
dierences.
GaussDB does not
support keywords
[ EDITIONABLE |
NONEDITIONABL
E ], REUSE,
SETTINGS, and
DEBUG.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > A >
ALTER
FUNCTION" in
Developer Guide
.
2 ALTER LIBRARY Not supported. -
3 ALTER PACKAGE Supported, with
dierences.
GaussDB does not
support keywords
[ EDITIONABLE |
NONEDITIONABL
E ], REUSE,
SETTINGS, and
DEBUG.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > A >
ALTER PACKAGE"
in
Developer
Guide
.
4 ALTER PROCEDURE Supported, with
dierences.
GaussDB does not
support keywords
[ EDITIONABLE |
NONEDITIONABL
E ], REUSE,
SETTINGS, and
DEBUG.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > A >
ALTER
PROCEDURE" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 263

No. Oracle GaussDB Dierence
5 ALTER TRIGGER Supported, with
dierences.
In GaussDB, only
the trigger name
can be modied.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > A >
ALTER TRIGGER"
in
Developer
Guide
.
6 ALTER TYPE Supported, with
dierences.
GaussDB supports
only some
statements.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > A >
ALTER TYPE" in
Developer Guide
.
Table 7-192 DROP statements
No.
Oracle GaussDB Dierence
1 DROP FUNCTION Supported. -
2 DROP LIBRARY Not supported. -
3 DROP PACKAGE Supported. -
4 DROP PROCEDURE Supported. -
5 DROP TRIGGER Supported, with
dierences.
The syntax in
GaussDB is
dierent.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > D >
DROP TRIGGER"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 264

No. Oracle GaussDB Dierence
6 DROP TYPE Supported, with
dierences.
GaussDB does not
support keywords
FORCE and
VALIDATE.
For details about
the syntax, see
"SQL Reference >
SQL Syntax > D >
DROP TYPE" in
Developer Guide
.
7 DROP TYPE BODY Not supported. -
Table 7-193 Keywords related to functions, procedures, and anonymous blocks
No. Oracle GaussDB Dierence
1 ACCESSIBLE BY Not
supported.
-
2 AGGREGATE Supported,
with
dierences.
● GaussDB does not
support Oracle's
aggregate using
[schema.]
implementation_ty
pe.
● For details about
GaussDB syntax,
see "SQL
Reference > SQL
Syntax > C >
CREATE
AGGREGATE" in
Developer Guide
.
The syntax is
dierent, but the
implementation
functions are the
same.
3 DETERMINISTIC Supported,
with
dierences.
GaussDB supports the
keyword
DETERMINISTIC only
in syntax, but does
not support this
function.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 265

No. Oracle GaussDB Dierence
4 PIPE ROW Not
supported.
-
5 PIPELINED Not
supported.
-
6 SQL_MACRO Not
supported.
-
7 RESTRICT_REFERENCE
S
Not
supported.
-
8 INLINE Not
supported.
-
Table 7-194 Keywords related to exception handling
No. Oracle GaussDB Dierence
1 EXCEPTION_INIT Supported, with
dierences.
Binding with
system error
codes is not
supported in
GaussDB.
2 Exception Supported. -
3 Exception Handler Supported. -
4 SQLCODE Supported. -
5 SQLERRM Supported. -
Table 7-195 Other PL/SQL keywords
No.
Oracle GaussDB Dierence
1 COVERAGE Not supported. -
2 COLLATION Supported. -
3 DEPRECATE Not supported. -
4 FORALL Supported. -
5 NOCOPY Not supported. -
6 RETURNING Supported. -
7 SERIALLY_REUSABLE Not supported. -
8 SHARING Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 266

No. Oracle GaussDB Dierence
9 BULK COLLECT Supported. -
7.2.10 System Functions
Compatible functions are classied into single-row functions, user-dened
functions, aggregate functions, analytic functions, object reference functions,
model functions, and OLAP functions.
7.2.10.1 Single-Row Functions
No. Oracle GaussDB
1 Numeric functions Supported, with
dierences.
2 Character functions returning character
values
Supported, with
dierences.
3 Character functions returning number
values
Supported, with
dierences.
4 Character set functions Not supported.
5 Collation functions Not supported.
6 Datetime functions Supported, with
dierences.
7 General comparison functions Supported, with
dierences.
8 Conversion functions Supported, with
dierences.
9 Large object functions Supported, with
dierences.
10 Collection functions Not supported.
11 Hierarchical functions Supported.
12 Data mining functions Not supported.
13 XML functions Supported, with
dierences.
14 JSON functions Not supported.
15 Encoding and decoding functions Supported, with
dierences.
16 Null-related functions Supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 267

No. Oracle GaussDB
17 Environment and identier functions Supported, with
dierences.
Table 7-196 Numeric functions
No. Oracle GaussDB Dierence
1 ABS Supported. -
2 ACOS Supported. -
3 ASIN Supported. -
4 ATAN Supported. -
5 ATAN2 Supported. -
6 BITAND Supported. -
7 CEIL Supported. -
8 COS Supported. -
9 COSH Supported. -
10 EXP Supported. -
11 FLOOR Supported. -
12 LN Supported. -
13 LOG Supported. -
14 MOD Supported, with
dierences.
● The return types are
inconsistent. In Oracle,
the return types include
BINARY_DOUBLE,
BINARY_FLOAT, and
NUMBER. In GaussDB,
the return types include
int2, int4, int8, and
numeric.
● If one of the two input
parameters is of the int
type, the other
parameter must be of
the int, numeric, or
literal integer type (a
valid number without a
decimal point, for
example, '12').
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 268

No. Oracle GaussDB Dierence
15 NANVL Supported, with
dierences.
GaussDB: NaN cannot be
obtained by directly
declaring or dividing a
oating-point number by
0.
16 POWER Supported. -
17 REMAINDER Supported, with
dierences.
If one of the two input
parameters is of the int
type, the other parameter
must be of the int,
numeric, or literal integer
type (a valid number
without a decimal point,
for example, '12').
18 ROUND Supported, with
dierences.
● For the rst parameter
n of the oat type,
GaussDB has precision
loss, and the precision
is lower than that of
Oracle.
● The returned types are
dierent. For round(n,
integer), Oracle returns
the NUMBER type, and
GaussDB returns the
numeric type. For
round(n), Oracle
returns the data type of
n, and GaussDB returns
only the oat8 and
numeric types. The
oat4 return type is
missing.
● The logic for the
GaussDB to determine
that the input
parameter is null and
the execution
framework to return
null is dierent from
that in Oracle.
SELECT round(NULL,'q');
Oracle reports null, and
GaussDB reports the
error: invalid input
syntax for integer: "q".
19
SIGN Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 269

No. Oracle GaussDB Dierence
20 SIN Supported. -
21 SINH Supported. -
22 SQRT Supported. -
23 TAN Supported. -
24 TANH Supported, with
dierences.
The precision of the return
value is dierent.
25 TRUNC Supported. -
26 WIDTH_BUCKET Supported. -
Table 7-197 Character functions returning character values
No. Oracle GaussDB Dierence
1 CHR Supported, with
dierences.
● If the entered number
does not comply with
the existing character
set, GaussDB reports
an error in JDBC and
Oracle returns garbled
characters.
● If you enter 0 or 256,
Oracle returns
characters whose ASCII
code is 0, and GaussDB
truncates the
characters at '\0;.
2 CONCAT Supported. -
3 INITCAP Supported, with
dierences.
The returned value is
restricted by the database
character set. As a result,
the returned result is
dierent from that in
Oracle.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 270

No. Oracle GaussDB Dierence
4 LOWER Supported, with
dierences.
● The return value types
are dierent. The data
types of Oracle are the
same as the input
types.
● The time format is
implicitly converted.
When the time type is
entered, the time type
is implicitly converted
to a character string
and then the lower
operation is performed.
SELECT
LOWER(TO_DATE('2012-12-10'
,'YYYY-MM-DD'));
Oracle returns 10-
DEC-12, and GaussDB
returns 2012-12-10
00:00:00.
● The returned value is
restricted by the
database character set.
As a result, the
returned result is
dierent from that in
Oracle.
5
LPAD Supported. -
6 LTRIM Supported, with
dierences.
The return value types are
dierent. If the input is of
the character data type,
Oracle returns the
VARCHAR2 type. If the
input is of the national
character set specied
during database creation,
Oracle returns the
NVARCHAR2 type. If the
input is of the LOB type,
Oracle returns the LOB
type. GaussDB returns the
TEXT type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 271

No. Oracle GaussDB Dierence
7 NCHR Supported, with
dierences.
● The byte length of the
return value is dierent
from that of Oracle.
● The returned value is
restricted by the
database character set.
As a result, the
returned result is
dierent from that in
Oracle.
● When the byte array
corresponding to the
input parameter is
returned, a question
mark (?) is returned if
a single byte ranges
from 0x80 to 0xFF. In
Oracle, a question
mark (?) is returned,
no output is returned,
or an error is reported.
8
NLS_LOWER Supported, with
dierences.
● The return value types
are dierent. If the
input is of the
character data type,
Oracle returns the
VARCHAR2 type. If the
input is of the LOB
type, Oracle returns the
LOB type. GaussDB
returns the TEXT type.
● In Oracle, the
nlsparam parameter
can be of a type except
nls_sort, and no error is
reported. GaussDB
supports only nls_sort.
● The returned value is
restricted by the
database character set.
As a result, the
returned result is
dierent from that in
Oracle.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 272

No. Oracle GaussDB Dierence
9 NLS_UPPER Supported, with
dierences.
● The return value types
are dierent. If the
input is of the
character data type,
Oracle returns the
VARCHAR2 type. If the
input is of the LOB
type, Oracle returns the
LOB type. GaussDB
returns the TEXT type.
● In Oracle, the
nlsparam parameter
can be of a type except
nls_sort, and no error is
reported. GaussDB
supports only nls_sort.
● The returned value is
restricted by the
database character set.
As a result, the
returned result is
dierent from that in
Oracle.
10
NLSSORT Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 273

No. Oracle GaussDB Dierence
11 REGEXP_REPLACE Supported, with
dierences.
● GaussDB input
parameter source_char
does not support the
NCLOB type.
● The meaning of the 'n'
option in the
match_param input
parameter is dierent.
In GaussDB, the 'n'
option has the same
meaning as the 'm'
option, indicating that
the multi-row
matching mode is used.
In Oracle, it indicates
that the dot (.) can
match the '\n'
character. If this option
is not specied, the '\n'
character cannot be
matched by default. In
GaussDB, the dot (.)
matches '\n' by default.
You do not need to
specify the option.
● The matching results of
some regular
expressions may be
dierent.
SELECT
REGEXP_REPLACE('abc01234xy
z', '(.*?)(\d+)(.*)', '#', 'g')
FROM DUAL;
Oracle reports an error,
and GaussDB returns
#####xyz.
● The matching results
may be dierent when
Chinese characters are
entered in the UTF-8
character set. Oracle
needs to implement
regular expression
matching for Chinese
character strings in the
GBK character set.
● The matching results of
regular expressions
that contain some
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 274

No. Oracle GaussDB Dierence
escape characters may
be dierent.
SELECT
REGEXP_REPLACE('abcabc',
'\abc', '#', 'g') FROM DUAL;
Oracle reports an error,
and GaussDB returns
abcabc.
● The matching rules are
aected by the
aformat_regexp_matc
h parameter. For
details about the
aected specications,
see the
REGEXP_REPLACE
function in "SQL
Reference > Functions
and Operators >
Character Processing
Functions and
Operators" in
Developer Guide
.
12
REGEXP_SUBSTR Supported, with
dierences.
The matching rules are
aected by the
aformat_regexp_match
parameter. For details
about the aected
specications, see the
REGEXP_SUBSTR function
in "SQL Reference >
Functions and Operators >
Character Processing
Functions and Operators"
in
Developer Guide
.
13 REPLACE Supported. -
14 RPAD Supported. -
15 RTRIM Supported. -
16 SUBSTR Supported. -
17 TRANSLATE Supported. -
18 TRIM Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 275

No. Oracle GaussDB Dierence
19 UPPER Supported, with
dierences.
● The return value types
are dierent. The data
types of Oracle are the
same as the input
types. GaussDB returns
the TEXT type.
● The time format is
implicitly converted.
When the time type is
entered, the time type
is implicitly converted
to a character string
and then the upper
operation is performed.
SELECT
UPPER(TO_DATE('2012-12-10',
'YYYY-MM-DD'));
Oracle returns 10-
DEC-12, and GaussDB
returns 2012-12-10
00:00:00.
● The returned value is
restricted by the
database character set.
As a result, the
returned result is
dierent from that in
Oracle.
20
INSTRB Supported. -
Table 7-198 Character functions returning number values
No.
Oracle GaussDB Dierence
1 ASCII Supported, with
dierences.
The return value
types are
dierent. Oracle
returns the uint4
type, while
GaussDB returns
the int4 type.
2 INSTR Supported. -
3 LENGTH Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 276

No. Oracle GaussDB Dierence
4 REGEXP_COUNT Supported, with
dierences.
● GaussDB input
parameter
source_char
does not
support the
NCLOB type.
● The meaning
of the 'n'
option in the
match_param
input
parameter is
dierent. In
GaussDB, the
'n' option has
the same
meaning as the
'm' option,
indicating that
the multi-row
matching
mode is used.
In Oracle, it
indicates that
the dot (.) can
match the '\n'
character. If
this option is
not specied,
the '\n'
character
cannot be
matched by
default. In
GaussDB, the
dot (.) matches
'\n' by default.
You do not
need to specify
the option.
● The matching
results of some
regular
expressions
may be
dierent.
● The matching
results may be
dierent when
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 277

No. Oracle GaussDB Dierence
Chinese
characters are
entered in the
UTF-8
character set.
Oracle needs
to implement
regular
expression
matching for
Chinese
character
strings in the
GBK character
set.
● The matching
results of
regular
expressions
that contain
some escape
characters may
be dierent.
● The matching
rules are
aected by the
aformat_regex
p_match
parameter. For
details about
the aected
specications,
see the
REGEXP_COUN
T function in
"SQL Reference
> Functions
and Operators
> Character
Processing
Functions and
Operators" in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 278

No. Oracle GaussDB Dierence
5 REGEXP_INSTR Supported, with
dierences.
The matching
rules are aected
by the
aformat_regexp_
match parameter.
For details about
the aected
specications, see
the
REGEXP_INSTR
function in "SQL
Reference >
Functions and
Operators >
Character
Processing
Functions and
Operators" in
Developer Guide
.
Table 7-199 Datetime functions
No.
Oracle GaussDB Dierence
1 ADD_MONTHS Supported, with
dierences.
● From A.D. to B.C., the
dierence between
GaussDB and Oracle is
one year.
● The earliest year can be
–4714 in GaussDB and
–4713 in Oracle.
2 CURRENT_DATE Supported, with
dierences.
GaussDB: The
nls_date_format
parameter cannot be used
to set the time display
format.
3 CURRENT_TIMEST
AMP
Supported, with
dierences.
The value ranges from 0
to 9 in Oracle.
The value ranges from 0
to 6 in GaussDB. The
trailing zeros in
microseconds are not
displayed.
4 DBTIMEZONE Supported, with
dierences.
GaussDB: The timestamp
API with the built-in tz
cannot be called.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 279

No. Oracle GaussDB Dierence
5 EXTRACT Supported. -
6 LAST_DAY Supported, with
dierences.
The return value types are
dierent. The return value
type in GaussDB is
timestamp without time
zone, and that in Oracle is
date.
7 LOCALTIMESTAMP Supported, with
dierences.
The value ranges from 0
to 9 in Oracle.
The value ranges from 0
to 6 in GaussDB. The
trailing zeros in
microseconds are not
displayed.
8 MONTHS_BETWEE
N
Supported, with
dierences.
The input parameter types
are dierent. GaussDB
input parameters are of
the timestamp without
time zone type, and
Oracle input parameters
are of the date type.
9 NEW_TIME Supported, with
dierences.
When the rst input
parameter of the
new_time function is a
literal, the literal format
and the return value type
of the function are
dierent from those in
Oracle.
10 NEXT_DAY Supported. -
11 NUMTODSINTERV
AL
Supported, with
dierences.
GaussDB: The dsinterval
type is not supported.
Currently, interval is used
to be compatible with the
dsinterval type.
12 NUMTOYMINTERV
AL
Supported, with
dierences.
GaussDB: The yminterval
type is not supported.
Currently, interval is used
to be compatible with the
yminterval type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 280

No. Oracle GaussDB Dierence
13 SESSIONTIMEZON
E
Supported, with
dierences.
● Dierence in the value
assignment syntax: In
GaussDB, the SET
SESSION TIME ZONE 8
syntax is used. In
Oracle, alter session set
time_zone= '+08:00' is
used.
● Default value
dierence: The time
zone name is used in
GaussDB, for example,
PRC. The oset is used
in Oracle, for example,
+08:00.
14 SYS_EXTRACT_UTC Supported. -
15 SYSDATE Supported, with
dierences.
The return value types are
dierent. The return value
type in GaussDB is
timestamp without time
zone, and that in Oracle is
date.
16 TO_CHAR Supported, with
dierences.
The fmt '5' is not included
in the Oracle documents
and is not adapted.
17 TO_DSINTERVAL Supported, with
dierences.
GaussDB: The dsinterval
type is not supported.
Currently, interval is used
to be compatible with the
dsinterval type.
18 TO_TIMESTAMP Supported, with
dierences.
GaussDB supports only six
digits for millisecond
calculation, and Oracle
supports nine digits.
19 TO_TIMESTAMP_T
Z
Supported, with
dierences.
The timestamptz of
GaussDB is equivalent to
the timestampwithloaclti-
mezone of Oracle. The
type corresponding to
timestamptz of Oracle is
missing. The value of
nls_date_language can
only be ENGLISH or
AMERICAN.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 281
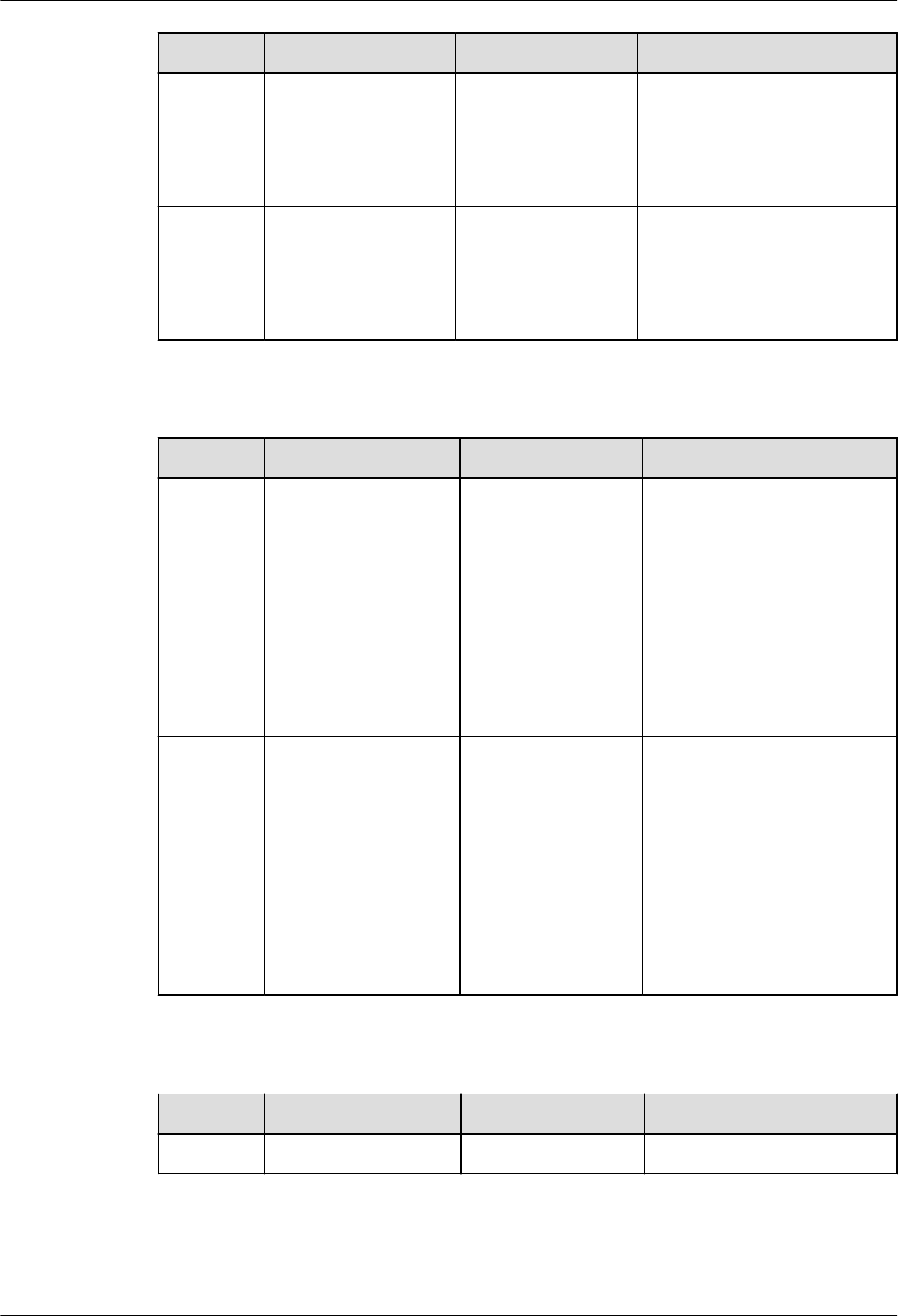
No. Oracle GaussDB Dierence
20 TO_YMINTERVAL Supported, with
dierences.
GaussDB: The yminterval
type is not supported.
Currently, interval is used
to be compatible with the
yminterval type.
21 TZ_OFFSET Supported, with
dierences.
When a time zone name is
received as an input
parameter, the types of
the time zone name are
less than those of Oracle.
Table 7-200 General comparison functions
No. Oracle GaussDB Dierence
1 GREATEST Supported, with
dierences.
● GaussDB: The
comparison mode
specied by the
NLS_SORT parameter
is not supported. Only
binary comparison is
supported.
● GaussDB: Expressions
in multiple languages
are not supported.
2 LEAST Supported, with
dierences.
● GaussDB: The
comparison mode
specied by the
NLS_SORT parameter
is not supported. Only
binary comparison is
supported.
● GaussDB: Expressions
in multiple languages
are not supported.
Table 7-201 Conversion functions
No.
Oracle GaussDB Dierence
1 ASCIISTR Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 282

No. Oracle GaussDB Dierence
2 CAST Supported, with
dierences.
● GaussDB: The
MULTISET clause is not
supported.
● GaussDB: The
nlsparam parameter is
not supported.
3 HEXTORAW Supported. -
4 RAWTOHEX Supported. -
5 TO_BINARY_DOUB
LE
Supported, with
dierences.
GaussDB: The nlsparam
parameter is not
supported.
6 TO_BINARY_FLOAT Supported, with
dierences.
GaussDB: The nlsparam
parameter is not
supported.
7 TO_BLOB Supported, with
dierences.
● GaussDB: The long raw
type is not supported.
● GaussDB: The ble and
mime_type types are
not supported.
8 TO_CLOB Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 283
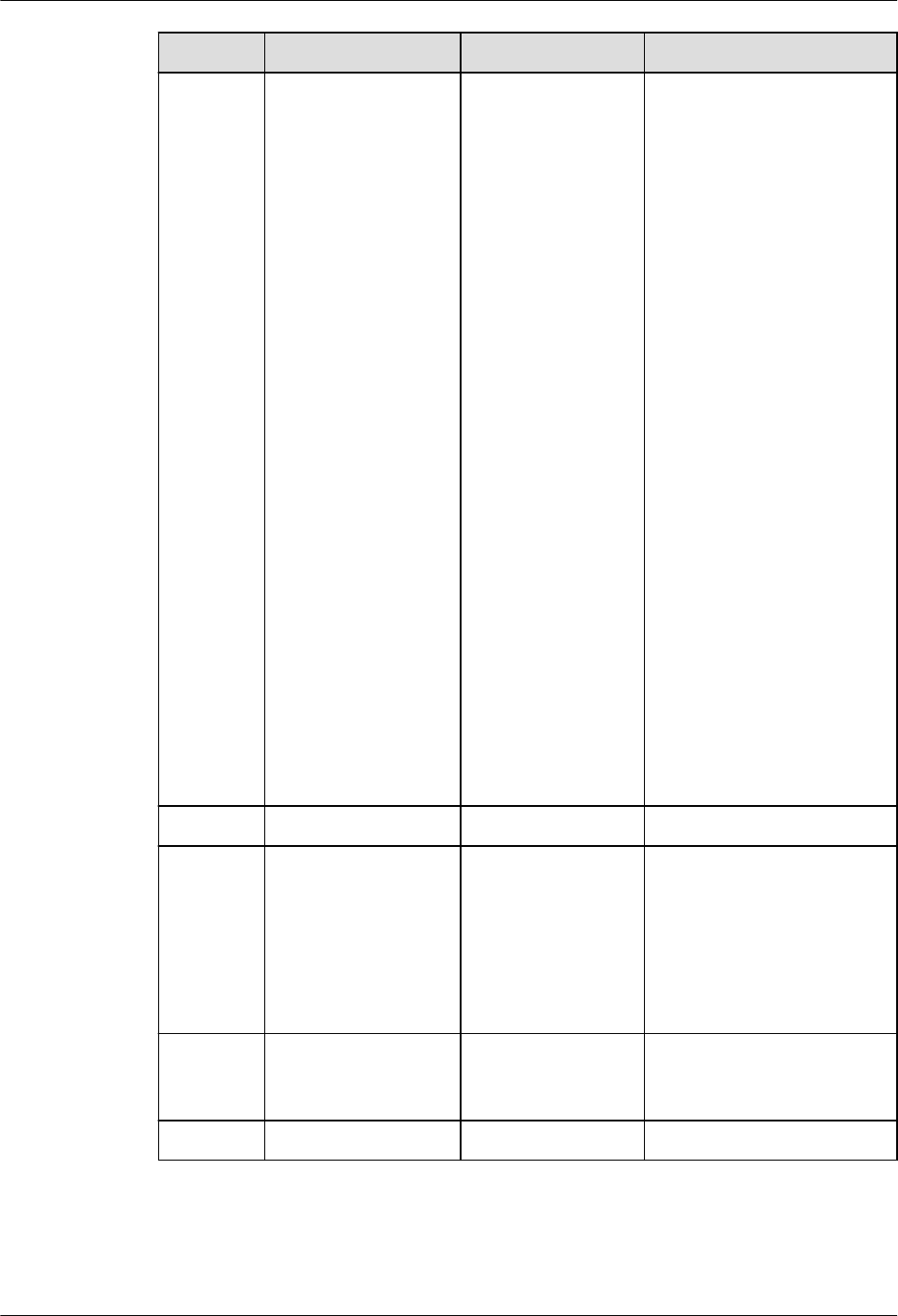
No. Oracle GaussDB Dierence
9 TO_DATE Supported, with
dierences.
● Multi-language
parameters are not
supported.
● The returned types are
dierent.
● The control parameter
NLS_DATE_FORMAT
is missing.
● Some formats are not
supported.
● fmt = 'j'. The output
before October 15,
1582 in Oracle is
inconsistent with that
in GaussDB.
● If there is no separator,
the value may be
dierent from that in
Oracle. Take
to_date('220725','yym
mdd') as an example.
If yy/rr is parsed based
on the xed length 4,
the year is parsed as
2207 and the month is
parsed as 25. The
month 25 is invalid,
and an error will be
reported.
10
TO_MULTI_BYTE Supported. -
11 TO_NCHAR Supported, with
dierences.
GaussDB: The input
parameter type is
converted to text.
Oracle: The input
parameter type is
converted to the national
character set.
12 TO_NUMBER Supported, with
dierences.
GaussDB: The nlsparam
parameter is not
supported.
13 TO_SINGLE_BYTE Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 284

No. Oracle GaussDB Dierence
14 TREAT Supported, with
dierences.
GaussDB: The period (.)
operator cannot be used
to obtain values, and the
values cannot be
converted to the object
type.
15 UNISTR Supported, with
dierences.
GaussDB supports only
UTF-8 encoding. Oracle
supports UTF-8 and
UTF-16 encodings.
Table 7-202 Large object functions
No. Oracle GaussDB Dierence
1 EMPTY_BLOB Supported. -
2 EMPTY_CLOB Supported, with
dierences.
The CLOB type in
GaussDB does not
support the locator
concept in Oracle.
Table 7-203 Hierarchical functions
No.
Oracle GaussDB Dierence
1 SYS_CONNECT_BY_P
ATH
Supported, with
dierences.
GaussDB: The column
specied by the rst
input parameter can
only be the CHAR,
VARCHAR,
NVARCHAR2, or TEXT
type.
Table 7-204 XML functions
No.
Oracle GaussDB Dierence
1 EXISTSNODE Supported, with
dierences.
If the input parameter
has a namespace,
aliases must be
dened for both the
XPath and
namespace.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 285

No. Oracle GaussDB Dierence
2 EXTRACTVALUE Supported, with
dierences.
Currently, only XPath
1.0 is supported.
3 SYS_XMLAGG Supported, with
dierences.
This is an alias of
xmlagg and can be
replaced with xmlagg.
4 XMLAGG Supported. -
5 XMLCOMMENT Supported. -
6 XMLCONCAT Supported. -
7 XMLELEMENT Supported, with
dierences.
For xmlelement and
xmlattributes, when
the value of name is
NULL, the database
behavior is dierent
from that in Oracle.
When the name
column of
xmlelement is set to
NULL, the name
information is empty
and the attribute
information is not
displayed. When the
name column of
xmlattributes is set
to NULL, the attribute
information is not
displayed.
8 XMLEXISTS Supported, with
dierences.
GaussDB input
parameter is of the
XML type.
9 XMLFOREST Supported, with
dierences.
GaussDB return value
is of the XML type.
GaussDB does not
support the
EVALNAME syntax.
10 XMLPARSE Supported, with
dierences.
GaussDB return value
is of the XML type.
GaussDB does not
support the
WELLFORMED syntax.
11 XMLROOT Supported, with
dierences.
GaussDB return value
is of the XML type.
12 JSON_OBJECT Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 286

No. Oracle GaussDB Dierence
13 XMLTABLE Supported, with
dierences.
GaussDB: The XPath
1.0 expression is used
to select data from
the XML le. The
default namespace
cannot be declared,
multiple groups of
inputs and aliases
cannot be obtained,
the passing_clause
clause of the input
data cannot be
omitted, and the
RETURNING
SEQUENCE BY REF
and ( SEQUENCE ) BY
REF clauses are not
supported.
14 GETSTRINGVAL Supported. -
15 GETCLOBVAL Supported. -
16 XMLSEQUENCE Supported. -
Table 7-205 Encoding and decoding functions
No.
Oracle GaussDB Dierence
1 DECODE Supported. -
2 DUMP Supported, with
dierences.
The returned results
of the numeric and
time types in
GaussDB are
inconsistent with
those in Oracle due to
dierent storage
formats. For example:
● In GaussDB,
SELECT
dump(123);
returns Typ=23
Len=4: 123,0,0,0.
● In Oracle, SELECT
dump(123) FROM
dual; returns
Typ=2 Len=3:
194,2,24.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 287
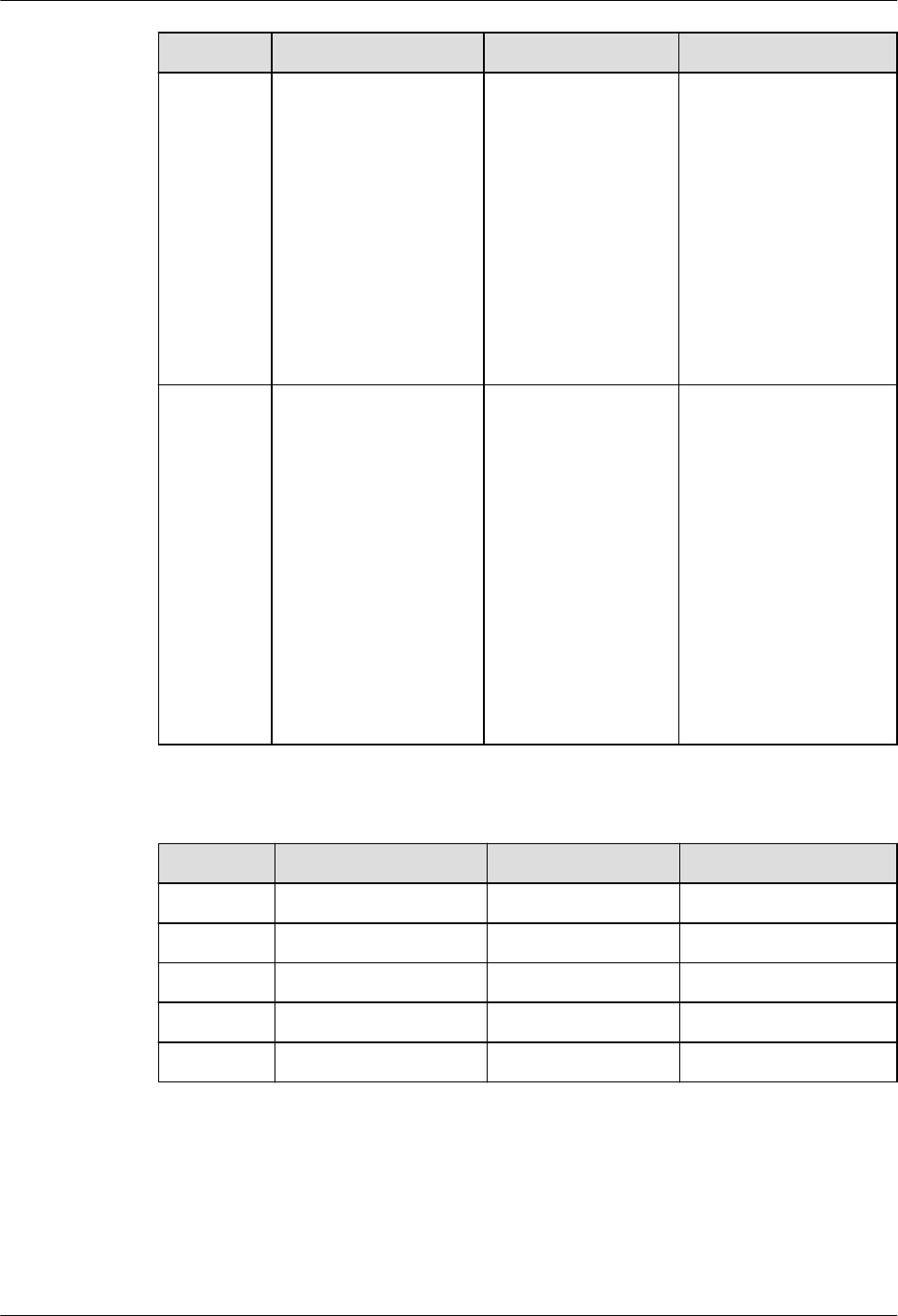
No. Oracle GaussDB Dierence
3 ORA_HASH Supported, with
dierences.
GaussDB has the
following behaviors:
● The input
parameter of the
time type is
converted into the
character string
type and then
hashed.
● The maxbucket
parameter is not
supported.
4 VSIZE Supported, with
dierences.
The returned results
of the numeric and
time types in
GaussDB are
inconsistent with
those in Oracle due to
dierent storage
formats. For example:
● In GaussDB,
SELECT vsize(999);
returns 4.
● In Oracle, SELECT
vsize(999) FROM
dual; returns 3.
Table 7-206 Null-related functions
No.
Oracle GaussDB Dierence
1 COALESCE Supported. -
2 LNNVL Supported. -
3 NULLIF Supported. -
4 NVL Supported. -
5 NVL2 Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 288
Table 7-207 Environment and identier functions
No. Oracle GaussDB Dierence
1 SYS_CONTEXT Supported, with
dierences.
GaussDB returns
NULL for
unsupported
parameters.
The following
parameters are not
supported:
'action'
'is_application_root'
'is_application_pdb'
'audited_cursorid'
'authenticated_identit
y'
'authentication_data'
'authentication_meth
od'
'cdb_domain'
'cdb_name'
'client_identier'
'con_id'
'con_name'
'current_sql_length'
'db_domain'
'db_supplemental_log
_level'
'dblink_info'
'drain_status'
'entryid'
'enterprise_identity'
'fg_job_id'
'global_uid'
'identication_type'
'instance'
'is_dg_rolling_upgrade
'
'ldap_server_type'
'module'
'network_protocol'
'nls_calendar'
'nls_sort'
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 289
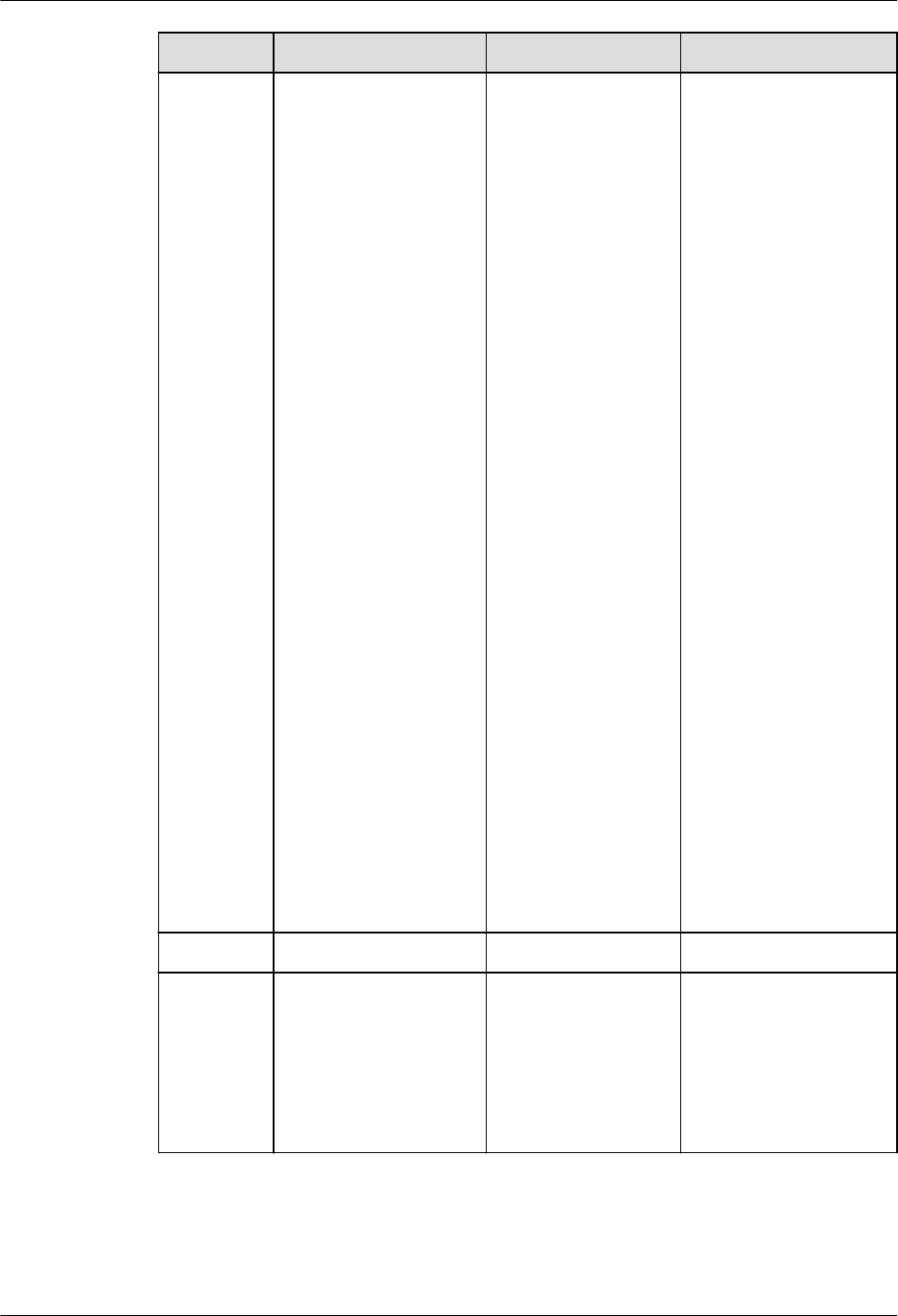
No. Oracle GaussDB Dierence
'nls_territory'
'oracle_home'
'os_user'
'platform_slash'
'policy_invoker'
'proxy_enterprise_ide
ntity'
'proxy_user'
'proxy_userid'
'scheduler_job'
'session_edition_id'
'session_edition_nam
e'
'sessionid'
'statementid'
'terminal'
'unied_audit_session
id'
'session_default_colla
tion'
'client_info'
'bg_job_id'
'client_program_name
'
'current_bind'
'global_context_mem
ory'
'host'
'current_sqln'
2
SYS_GUID Supported. -
3 USER Supported, with
dierences.
The return value
types are
inconsistent. The
return value type of
GaussDB is name,
and that of Oracle is
varchar2.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 290
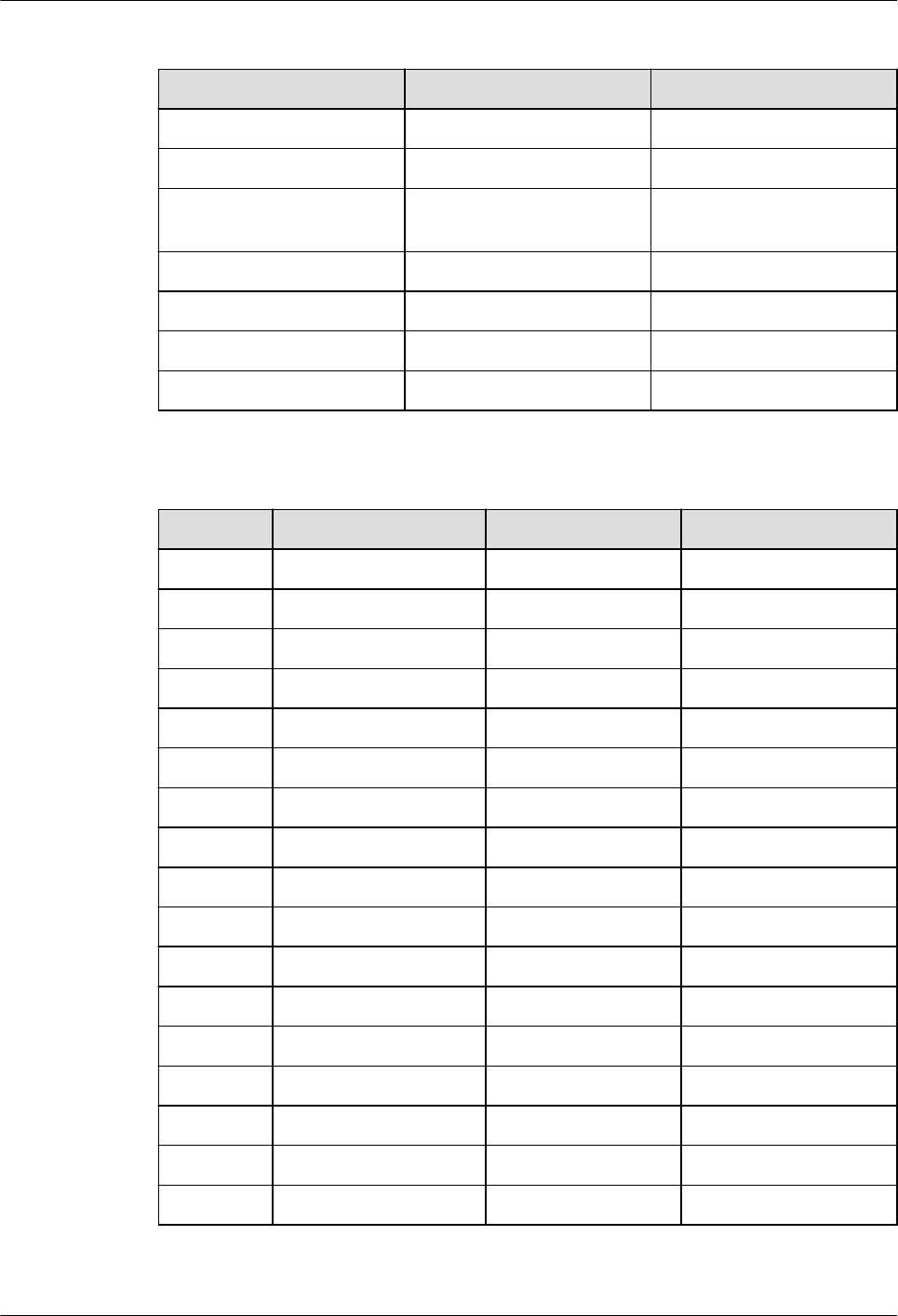
7.2.10.2 Other Functions
No. Oracle GaussDB
1 Aggregate functions Supported.
2 Analytic functions Supported.
3 Object reference
functions
Not supported.
4 Models functions Not supported.
5 OLAP functions Not supported.
6 Data cartridge functions Not supported.
7 User-dened functions Supported.
Table 7-208 Aggregate functions
No. Oracle GaussDB Dierence
1 AVG Supported. -
2 CORR Supported. -
3 COUNT Supported. -
4 COVAR_POP Supported. -
5 COVAR_SAMP Supported. -
6 CUME_DIST Supported. -
7 DENSE_RANK Supported. -
8 FIRST Supported. -
9 GROUPING Supported. -
10 LAST Supported. -
11 LISTAGG Supported. -
12 MAX Supported. -
13 MEDIAN Supported. -
14 MIN Supported. -
15 PERCENT_RANK Supported. -
16 PERCENTILE_CONT Supported. -
17 RANK Supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 291

No. Oracle GaussDB Dierence
18 REGR_ (Linear
Regression)
Supported. -
19 STDDEV Supported. -
20 STDDEV_POP Supported. -
21 STDDEV_SAMP Supported. -
22 SUM Supported. -
23 VAR_POP Supported. -
24 VAR_SAMP Supported. -
25 VARIANCE Supported. -
26 WM_CONCAT Supported, with
dierences.
The LISTAGG and
STRING_AGG
functions used in
GaussDB are
compatible with
Oracle.
Table 7-209 Analytic functions
No.
Oracle GaussDB
1 FIRST_VALUE Supported.
2 LAG Supported.
3 LAST_VALUE Supported.
4 LEAD Supported.
5 NTH_VALUE Supported.
6 NTILE Supported.
7 ROW_NUMBER Supported.
8 RATIO_TO_REPORT Supported.
7.2.11 System Views
GaussDB is compatible with some Oracle system views, as shown in the following
table.
For details about columns in system views, see "System Views" in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 292

Table 7-210 Supported views
No. Oracle GaussDB
1 ALL_ALL_TABLES DB_ALL_TABLES
2 ALL_COL_PRIVS DB_COL_PRIVS
3 ALL_COLL_TYPES DB_COLL_TYPES
4 ALL_ERRORS DB_ERRORS
5 ALL_IND_COLUMNS DB_IND_COLUMNS
6 ALL_COL_COMMENTS DB_COL_COMMENTS
7 ALL_CONS_COLUMNS DB_CONS_COLUMNS
8 ALL_CONSTRAINTS DB_CONSTRAINTS
9 ALL_DEPENDENCIES DB_DEPENDENCIES
10 ALL_DIRECTORIES DB_DIRECTORIES
11 ALL_IND_EXPRESSIONS DB_IND_EXPRESSIONS
12 ALL_IND_PARTITIONS DB_IND_PARTITIONS
13 ALL_INDEXES DB_INDEXES
14 ALL_IND_SUBPARTITIONS DB_IND_SUBPARTITIONS
15 ALL_OBJECTS DB_OBJECTS
16 ALL_PART_COL_STATISTICS DB_PART_COL_STATISTICS
17 ALL_PART_KEY_COLUMNS DB_PART_KEY_COLUMNS
18 ALL_PART_TABLES DB_PART_TABLES
19 ALL_SCHEDULER_JOB_ARGS DB_SCHEDULER_JOB_ARGS
20 ALL_SCHEDULER_PROGRAM_ARG
S
DB_SCHEDULER_PROGRAM_
ARGS
21 ALL_SEQUENCES DB_SEQUENCES
22 ALL_SUBPART_COL_STATISTICS DB_SUBPART_COL_STATISTI
CS
23 ALL_SUBPART_KEY_COLUMNS DB_SUBPART_KEY_COLUMN
S
24 ALL_SYNONYMS DB_SYNONYMS
25 ALL_TAB_COL_STATISTICS DB_TAB_COL_STATISTICS
26 ALL_TAB_COMMENTS DB_TAB_COMMENTS
27 ALL_TAB_HISTOGRAMS DB_TAB_HISTOGRAMS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 293

No. Oracle GaussDB
28 ALL_TAB_STATS_HISTORY DB_TAB_STATS_HISTORY
29 ALL_TYPES DB_TYPES
30 ALL_PART_INDEXES DB_PART_INDEXES
31 ALL_PROCEDURES DB_PROCEDURES
32 ALL_SOURCE DB_SOURCE
33 ALL_TAB_COLUMNS DB_TAB_COLUMNS
34 ALL_TAB_PARTITIONS DB_TAB_PARTITIONS
35 ALL_TAB_SUBPARTITIONS DB_TAB_SUBPARTITIONS
36 ALL_TABLES DB_TABLES
37 ALL_TRIGGERS DB_TRIGGERS
38 ALL_USERS DB_USERS
39 ALL_VIEWS DB_VIEWS
40 DBA_AUDIT_OBJECT ADM_AUDIT_OBJECT
41 DBA_AUDIT_SESSION ADM_AUDIT_SESSION
42 DBA_AUDIT_STATEMENT ADM_AUDIT_STATEMENT
43 DBA_AUDIT_TRAIL ADM_AUDIT_TRAIL
44 DBA_COL_COMMENTS ADM_COL_COMMENTS
45 DBA_COL_PRIVS ADM_COL_PRIVS
46 DBA_COLL_TYPES ADM_COLL_TYPES
47 DBA_ARGUMENTS ADM_ARGUMENTS
48 DBA_CONSTRAINTS ADM_CONSTRAINTS
49 DBA_DATA_FILES ADM_DATA_FILES
50 DBA_CONS_COLUMNS ADM_CONS_COLUMNS
51 DBA_DEPENDENCIES ADM_DEPENDENCIES
52 DBA_DIRECTORIES ADM_DIRECTORIES
53 DBA_PART_COL_STATISTICS ADM_PART_COL_STATISTICS
54 DBA_PART_TABLES ADM_PART_TABLES
55 DBA_RECYCLEBIN ADM_RECYCLEBIN
56 DBA_ROLE_PRIVS ADM_ROLE_PRIVS
57 DBA_ROLES ADM_ROLES
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 294

No. Oracle GaussDB
58 DBA_SCHEDULER_JOB_ARGS ADM_SCHEDULER_JOB_ARG
S
59 DBA_SCHEDULER_PROGRAMS ADM_SCHEDULER_PROGRA
MS
60 DBA_SCHEDULER_PROGRAM_AR
GS
ADM_SCHEDULER_PROGRA
M_ARGS
61 DBA_HIST_SNAPSHOT ADM_HIST_SNAPSHOT
62 DBA_HIST_SQL_PLAN ADM_HIST_SQL_PLAN
63 DBA_HIST_SQLSTAT ADM_HIST_SQLSTAT
64 DBA_HIST_SQLTEXT ADM_HIST_SQLTEXT
65 DBA_ILMDATAMOVEMENTPOLI-
CIES
GS_ADM_ILMDATAMOVEME
NTPOLICIES
66 DBA_ILMEVALUATIONDETAILS GS_ADM_ILMEVALUATIOND
ETAILS
67 DBA_ILMOBJECTS GS_ADM_ILMOBJECTS
68 DBA_ILMPARAMETERS GS_ADM_ILMPARAMETERS
69 DBA_ILMPOLICIES GS_ADM_ILMPOLICIES
70 DBA_ILMRESULTS GS_ADM_ILMRESULTS
71 DBA_ILMTASKS GS_ADM_ILMTASKS
72 DBA_IND_COLUMNS ADM_IND_COLUMNS
73 DBA_IND_EXPRESSIONS ADM_IND_EXPRESSIONS
74 DBA_IND_PARTITIONS ADM_IND_PARTITIONS
75 DBA_INDEXES ADM_INDEXES
76 DBA_OBJECTS ADM_OBJECTS
77 DBA_PART_INDEXES ADM_PART_INDEXES
78 DBA_PROCEDURES ADM_PROCEDURES
79 DBA_SCHEDULER_JOBS ADM_SCHEDULER_JOBS
80 DBA_SCHEDULER_RUNNING_JOB
S
ADM_SCHEDULER_RUNNIN
G_JOBS
81 DBA_SEGMENTS ADM_SEGMENTS
82 DBA_SEQUENCES ADM_SEQUENCES
83 DBA_SOURCE ADM_SOURCE
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 295

No. Oracle GaussDB
84 DBA_IND_SUBPARTITIONS ADM_IND_SUBPARTITIONS
85 DBA_SUBPART_COL_STATISTICS ADM_SUBPART_COL_STATIS
TICS
86 DBA_SUBPART_KEY_COLUMNS ADM_SUBPART_KEY_COLUM
NS
87 DBA_SYS_PRIVS ADM_SYS_PRIVS
88 DBA_TAB_COL_STATISTICS ADM_TAB_COL_STATISTICS
89 DBA_TAB_HISTOGRAMS ADM_TAB_HISTOGRAMS
90 DBA_TAB_STATISTICS ADM_TAB_STATISTICS
91 DBA_TAB_STATS_HISTORY ADM_TAB_STATS_HISTORY
92 DBA_TABLESPACES ADM_TABLESPACES
93 DBA_TYPES ADM_TYPES
94 DBA_USERS ADM_USERS
95 DBA_SYNONYMS ADM_SYNONYMS
96 DBA_TAB_COLS ADM_TAB_COLS
97 DBA_TAB_COLUMNS ADM_TAB_COLUMNS
98 DBA_TAB_COMMENTS ADM_TAB_COMMENTS
99 DBA_TABLES ADM_TABLES
100 DBA_TAB_PARTITIONS ADM_TAB_PARTITIONS
101 DBA_TAB_SUBPARTITIONS ADM_TAB_SUBPARTITIONS
102 DBA_TRIGGERS ADM_TRIGGERS
103 DBA_TYPE_ATTRS ADM_TYPE_ATTRS
104 DBA_VIEWS ADM_VIEWS
105 ROLE_ROLE_PRIVS ROLE_ROLE_PRIVS
106 ROLE_SYS_PRIVS ROLE_SYS_PRIVS
107 ROLE_TAB_PRIVS ROLE_TAB_PRIVS
108 USER_COL_COMMENTS MY_COL_COMMENTS
109 USER_COL_PRIVS MY_COL_PRIVS
110 USER_COLL_TYPES MY_COLL_TYPES
111 USER_CONSTRAINTS MY_CONSTRAINTS
112 USER_DEPENDENCIES MY_DEPENDENCIES
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 296

No. Oracle GaussDB
113 DICT DICT
114 DICTIONARY DICTIONARY
115 DUAL DUAL
116 NLS_DATABASE_PARAMETERS NLS_DATABASE_PARAMETER
S
117 NLS_INSTANCE_PARAMETERS NLS_INSTANCE_PARAMETER
S
118 PLAN_TABLE PLAN_TABLE
119 USER_ERRORS MY_ERRORS
120 USER_ILMDATAMOVEMENTPOLI-
CIES
GS_MY_ILMDATAMOVEMEN
TPOLICIES
121 USER_ILMEVALUATIONDETAILS GS_MY_ILMEVALUATIONDE-
TAILS
122 USER_ILMOBJECTS GS_MY_ILMOBJECTS
123 USER_ILMPOLICIES GS_MY_ILMPOLICIES
124 USER_ILMRESULTS GS_MY_ILMRESULTS
125 USER_ILMTASKS GS_MY_ILMTASKS
126 USER_IND_COLUMNS MY_IND_COLUMNS
127 USER_IND_EXPRESSIONS MY_IND_EXPRESSIONS
128 USER_IND_PARTITIONS MY_IND_PARTITIONS
129 USER_IND_SUBPARTITIONS MY_IND_SUBPARTITIONS
130 USER_INDEXES MY_INDEXES
131 USER_JOBS MY_JOBS
132 USER_OBJECTS MY_OBJECTS
133 USER_PART_COL_STATISTICS MY_PART_COL_STATISTICS
134 USER_PART_INDEXES MY_PART_INDEXES
135 USER_PART_TABLES MY_PART_TABLES
136 USER_PROCEDURES MY_PROCEDURES
137 USER_RECYCLEBIN MY_RECYCLEBIN
138 USER_SCHEDULER_JOB_ARGS MY_SCHEDULER_JOB_ARGS
139 USER_SCHEDULER_PROGRAM_AR
GS
MY_SCHEDULER_PROGRAM
_ARGS
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 297

No. Oracle GaussDB
140 USER_SEQUENCES MY_SEQUENCES
141 USER_SOURCE MY_SOURCE
142 USER_SUBPART_KEY_COLUMNS MY_SUBPART_KEY_COLUMN
S
143 USER_SYNONYMS MY_SYNONYMS
144 USER_SYS_PRIVS MY_SYS_PRIVS
145 USER_TAB_COL_STATISTICS MY_TAB_COL_STATISTICS
146 USER_TAB_COLUMNS MY_TAB_COLUMNS
147 USER_TAB_COMMENTS MY_TAB_COMMENTS
148 USER_TAB_HISTOGRAMS MY_TAB_HISTOGRAMS
149 USER_TAB_PARTITIONS MY_TAB_PARTITIONS
150 USER_TAB_STATISTICS MY_TAB_STATISTICS
151 USER_TAB_STATS_HISTORY MY_TAB_STATS_HISTORY
152 USER_TAB_SUBPARTITIONS MY_TAB_SUBPARTITIONS
153 USER_TABLES MY_TABLES
154 USER_TABLESPACES MY_TABLESPACES
155 USER_TRIGGERS MY_TRIGGERS
156 USER_TYPE_ATTRS MY_TYPE_ATTRS
157 USER_TYPES MY_TYPES
158 USER_VIEWS MY_VIEWS
159 V$GLOBAL_TRANSACTION V$GLOBAL_TRANSACTION
160 V$NLS_PARAMETERS V$NLS_PARAMETERS
161 V$SESSION_WAIT V$SESSION_WAIT
162 V$SYSSTAT V$SYSSTAT
163 V$SYSTEM_EVENT V$SYSTEM_EVENT
164 V$VERSION V$VERSION
165 V$INSTANCE V_INSTANCE
166 GV$INSTANCE GV_INSTANCE
167 V$MYSTAT V_MYSTAT
168 V$SESSION V_SESSION
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 298

No. Oracle GaussDB
169 GV$SESSION GV_SESSION
170 V$SESSION_LONGOPS DV_SESSION_LONGOPS
171 V$SESSION DV_SESSIONS
172 ALL_ARGUMENTS DB_ARGUMENTS
173 USER_CONS_COLUMNS MY_CONS_COLUMNS
174 USER_PART_KEY_COLUMNS MY_PART_KEY_COLUMNS
175 USER_SUBPART_COL_STATISTICS MY_SUBPART_COL_STATISTI
CS
176 USER_ROLE_PRIVS MY_ROLE_PRIVS
177 DBA_TAB_PRIVS ADM_TAB_PRIVS
178 USER_SCHEDULER_JOBS MY_SCHEDULER_JOBS
179 V$LOCK V$LOCK
180 V$DBLINK V$DBLINK
181 V$OPEN_CURSOR V$OPEN_CURSOR
182 ALL_TAB_PRIVS DB_TAB_PRIVS
183 ALL_TAB_MODIFICATIONS DB_TAB_MODIFICATIONS
184 USER_TAB_MODIFICATIONS MY_TAB_MODIFICATIONS
185 USER_AUDIT_TRAIL MY_AUDIT_TRAIL
7.2.12 Advanced Packages
Table 1 lists the advanced packages compatible with GaussDB.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 299
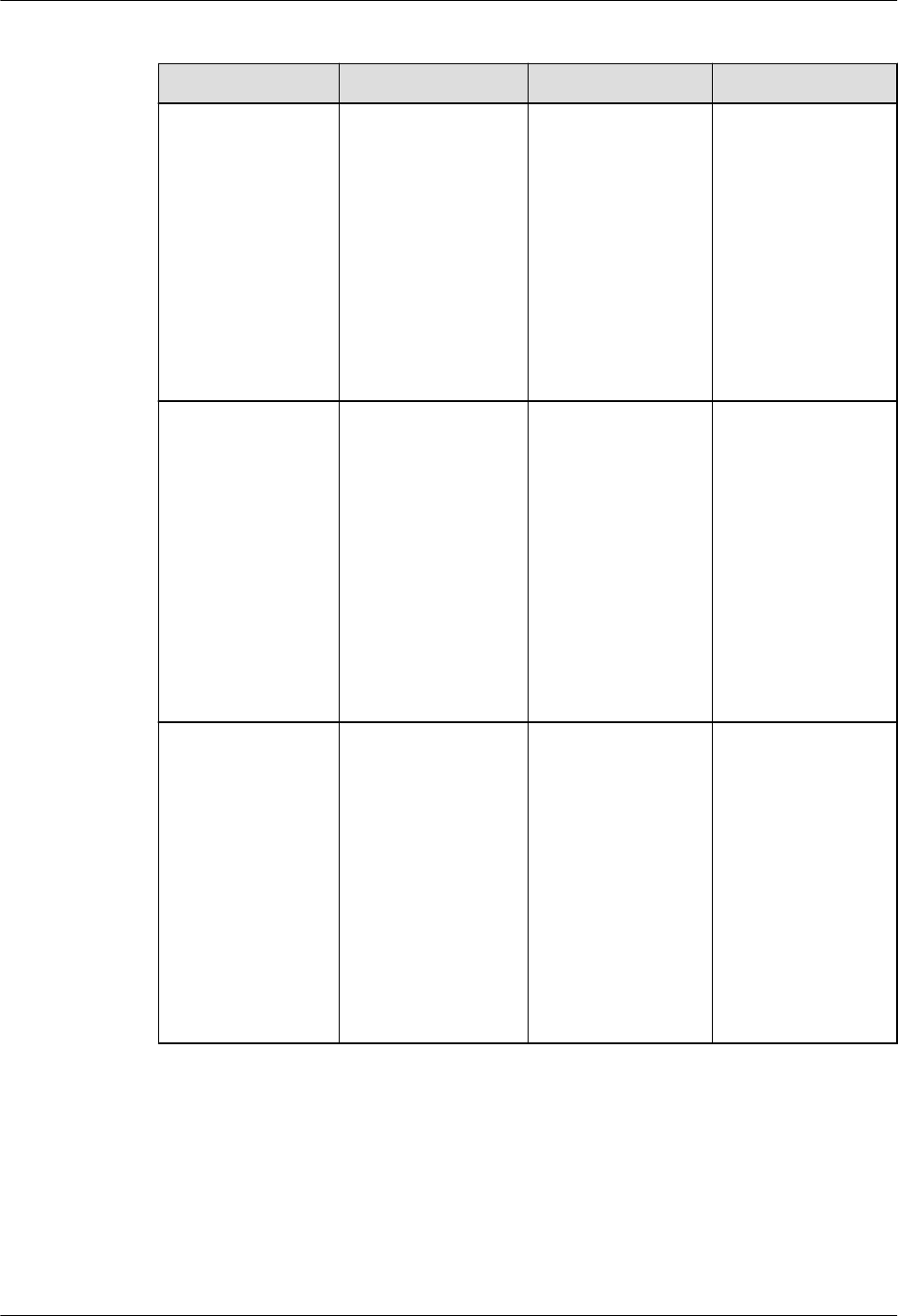
Table 7-211 Supported advanced packages
No. Oracle GaussDB Dierence
1 DBMS_LOB DBE_LOB For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_LOB" in
Developer Guide
.
2 DBMS_RANDOM DBE_RANDOM For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_RANDOM"
in
Developer
Guide
.
3 DBMS_OUTPUT DBE_OUTPUT For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_OUTPUT"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 300

No. Oracle GaussDB Dierence
4 UTL_RAW DBE_RAW For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_RAW" in
Developer Guide
.
5 DBMS_SCHEDULE
R
DBE_SCHEDULER For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_SCHEDULER"
in
Developer
Guide
.
6 DBMS_UTILITY DBE_UTILITY For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_UTILITY" in
Developer Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 301

No. Oracle GaussDB Dierence
7 DBMS_SQL DBE_SQL For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_SQL" in
Developer Guide
.
8 UTL_FILE DBE_FILE For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_FILE" in
Developer Guide
.
9 DBMS_SESSION DBE_SESSION For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_SESSION"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 302

No. Oracle GaussDB Dierence
10 UTL_MATCH DBE_MATCH For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_MATCH" in
Developer Guide
.
11 DBMS_APPLICATI
ON_INFO
DBE_APPLICATIO
N_INFO
For details about
how to use it in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_APPLICATIO
N_INFO" in
Developer Guide
.
12 DBMS_XMLDOM DBE_XMLDOM For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_XMLDOM"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 303

No. Oracle GaussDB Dierence
13 DBMS_XMLPARSE
R
DBE_XMLPARSER For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_XMLPARSER"
in
Developer
Guide
.
14 DBMS_ILM DBE_ILM For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_ILM" in
Developer Guide
.
15 DBMS_ILM_ADMI
N
DBE_ILM_ADMIN For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_ILM_ADMIN"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 304

No. Oracle GaussDB Dierence
16 DBMS_COMPRES
SION
DBE_COMPRESSI
ON
For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_COMPRESSI
ON" in
Developer
Guide
.
17 DBMS_HEAT_MA
P
DBE_HEAT_MAP For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_HEAT_MAP"
in
Developer
Guide
.
18 DBMS_DESCRIBE DBE_DESCRIBE For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_DESCRIBE"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 305

No. Oracle GaussDB Dierence
19 DBMS_XMLGEN DBE_XMLGEN For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_XMLGEN"
in
Developer
Guide
.
20 DBMS_STATS DBE_STATS For details about
information in
GaussDB, see
"Stored Procedure
> Advanced
Packages >
Secondary
Encapsulation
Interfaces
(Recommended)
> DBE_STATS" in
Developer Guide
.
Table 7-212 DBMS_LOB compatibility
No.
Oracle GaussDB Dierence
1 APPEND
Procedures
APPEND
Procedures
-
2 CLOB2FILE
Procedure
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 306

No. Oracle GaussDB Dierence
3 CLOSE Procedure BFILECLOSE
Procedure
GaussDB: The
parameter type is
BFILE, and no
function
overloading exists.
Oracle: There are
three overloaded
procedures. The
procedures have
three parameters
lob_loc, lob_loc,
and le_loc,
which are of the
BLOB, CLOB
CHARACTER SET
ANY_CS, and
BFILE types,
respectively.
4 COMPARE
Functions
COMPARE
Functions
GaussDB: There
are three
overloaded
functions. The
third parameter
(len) is of the
BIGINT type.
Oracle: There are
three overloaded
functions. The
third parameter
(amount) is of
the INTEGER type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 307

No. Oracle GaussDB Dierence
5 CONVERTTOBLOB
Procedure
LOB_CONVERTTO
BLOB Procedure
GaussDB: This
procedure has ve
parameters, and
the third, fourth,
and fth
parameters are of
the BIGINT type.
Oracle: This
procedure has
eight parameters.
In addition to all
GaussDB
parameters, the
blob_csid,
lang_context,
and warning
parameters are
added, which are
of the NUMBER,
INTEGER, and
INTEGER types,
respectively. The
third, fourth, and
fth parameters
are of the
INTEGER type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 308

No. Oracle GaussDB Dierence
6 CONVERTTOCLOB
Procedure
LOB_CONVERTTO
CLOB Procedure
GaussDB: This
procedure has ve
parameters. The
third, fourth, and
fth parameters
are of the BIGINT
type.
Oracle: This
procedure has
eight parameters.
The third, fourth,
and fth
parameters are of
the INTEGER type.
In addition to all
GaussDB
parameters, this
procedure in
Oracle adds three
parameters:
blob_csid,
lang_context,
and warning,
which are of
NUMBER,
INTEGER, and
INTEGER types,
respectively.
7
COPY Procedures LOB_COPY
Functions
-
8 COPY_DBFS_LINK
Procedures
Not supported. -
9 COPY_FROM_DBF
S_LINK
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 309
No. Oracle GaussDB Dierence
10 CREATETEMPORA
RY Procedures
CREATE_TEMPOR
ARY Procedures
GaussDB: There
are two
overloaded
procedures. The
rst parameter
(lob_loc) of the
rst overloaded
procedure is of
the BLOB type,
and the rst
parameter
(lob_loc) of the
second
overloaded
procedure is of
the CLOB type.
The third
parameter (dur)
of the two
overloaded
procedures is of
the INTEGER type,
and the default
value is 10.
Oracle: There are
two overloaded
procedures. The
rst parameter
(lob_loc) of the
rst overloaded
procedure is of
the BLOB type.
The rst
parameter
(lob_loc) of the
second
overloaded
procedure is of
the CLOB type.
The third
parameter (dur)
of the two
overloaded
procedures is of
the PLS_INTEGER
type. The default
value of dur of
the rst
overloaded
procedure is
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 310

No. Oracle GaussDB Dierence
DBMS_LOB.SESSI
ON, and the
default value of
dur of the second
overloaded
procedure is 10.
11 DBFS_LINK_GENE
RATE_PATH
Functions
Not supported. -
12 ERASE Procedures LOB_ERASE
Procedures
-
13 FILECLOSE
Procedure
Not supported. -
14 FILECLOSEALL
Procedure
Not supported. -
15 FILEEXISTS
Function
Not supported. -
16 FILEGETNAME
Procedure
Not supported. -
17 FILEISOPEN
Function
Not supported. -
18 FILEOPEN
Procedure
Not supported. -
19 FRAGMENT_DELE
TE Procedure
Not supported. -
20 FRAGMENT_INSE
RT Procedures
Not supported. -
21 FRAGMENT_MOV
E Procedure
Not supported. -
22 FRAGMENT_REPL
ACE Procedures
Not supported. -
23 FREETEMPORARY
Procedures
Not supported. -
24 GET_DBFS_LINK
Functions
Not supported. -
25 GET_DBFS_LINK_S
TATE Procedures
Not supported. -
26 GETCHUNKSIZE
Functions
GETCHUNKSIZE
Functions
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 311

No. Oracle GaussDB Dierence
27 GETCONTENTTYP
E Functions
Not supported. -
28 GETLENGTH
Functions
Not supported. -
29 GETOPTIONS
Functions
Not supported. -
30 GET_STORAGE_LI
MIT Function
Not supported. -
31 INSTR Functions MATCH Functions GaussDB: There
are three
overloaded
functions. The
third and fourth
parameters of the
three overloaded
functions are of
the BIGINT type.
Oracle: There are
three overloaded
functions. The
third and fourth
parameters of the
three overloaded
functions are of
the INTEGER type.
32 ISOPEN Functions Not supported. -
33 ISREMOTE
Function
Not supported. -
34 ISSECUREFILE
Function
Not supported. -
35 ISTEMPORARY
Functions
Not supported. -
36 LOADBLOBFROM
FILE Procedure
LOADBLOBFROM
BFILE Procedure
-
37 LOADCLOBFROM
FILE Procedure
LOADCLOBFROM
BFILE Procedure
-
38 LOADFROMFILE
Procedure
LOADFROMBFILE
Procedure
-
39 MOVE_TO_DBFS_
LINK Procedures
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 312

No. Oracle GaussDB Dierence
40 OPEN Procedures BFILEOPEN
Procedure
GaussDB: There is
no overloaded
procedure. The
rst parameter
(ble) is of the
DBE_LOB.BFILE
type, and the
second parameter
(open_mode) is
of the TEXT type.
Only the read
mode is
supported.
Oracle: There are
three overloaded
procedures. In the
rst overloaded
procedure, the
rst parameter
(lob_loc) is of the
NOCOPY BLOB
type, and the
second parameter
(openmode) is of
the
BINARY_INTEGER
type. In the
second
overloaded
procedure, the
rst parameter
(lob_loc) is of the
NOCOPY CLOB
CHARACTER SET
ANY_CS type, and
the second
parameter
(openmode) is of
the
BINARY_INTEGER
type. In the third
overloaded
procedure, the
rst parameter
(le_loc) is of the
NOCOPY BFILE
type, and the
second parameter
(openmode) is of
the
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 313

No. Oracle GaussDB Dierence
BINARY_INTEGER
type, and the
value can only be
le_readonly.
41 READ Procedures READ Procedures GaussDB: There
are two
overloaded
procedures.
Oracle: There are
three overloaded
procedures. The
rst two
overloaded
procedures are
the same as those
in GaussDB. The
third overloaded
procedure
includes four
parameters:
le_loc, amount,
oset, and
buer, which are
of the BFILE,
NOCOPY
INTEGER,
INTEGER, and
RAW types,
respectively.
42
SET_DBFS_LINK
Procedures
Not supported. -
43 SETCONTENTTYP
E Procedure
Not supported. -
44 SETOPTIONS
Procedures
Not supported. -
45 SUBSTR Functions LOB_SUBSTR
Functions
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 314

No. Oracle GaussDB Dierence
46 TRIM Procedures STRIP Functions GaussDB: There
are two
overloaded
procedures. The
second parameter
(newlen) of the
two overloaded
procedures is of
the BIGINT type.
Oracle: There are
two overloaded
procedures. The
second parameter
(newlen) of the
two overloaded
procedures is of
the INTEGER type.
47 WRITE Procedures WRITE Functions -
48 WRITEAPPEND
Procedures
WRITEAPPEND
Functions
-
Table 7-213 DBMS_RANDOM compatibility
No.
Oracle GaussDB Dierence
1 INITIALIZE
Procedure
Not supported. -
2 NORMAL
Function
Not supported. -
3 RANDOM
Function
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 315

No. Oracle GaussDB Dierence
4 SEED Procedures DBE_RANDOM.SE
T_SEED Function
GaussDB: There is
no overloaded
function. The
parameter is of
the INTEGER type.
Oracle: There are
two overloaded
procedures. The
parameter types
of the two
overloaded
procedures are
VARCHAR2 and
BINARY_INTEGER,
respectively.
5 STRING Function Not supported. -
6 TERMINATE
Procedure
Not supported. -
7 VALUE Functions DBE_RANDOM.GE
T_VALUE Function
GaussDB: There is
no overloaded
function.
Oracle: The
VALUE function
without
parameters is
overloaded, and
the return type is
NUMBER.
Table 7-214 DBMS_OUTPUT compatibility
No.
Oracle GaussDB Dierence
1 DISABLE
Procedure
DISABLE Function -
2 ENABLE
Procedure
ENABLE Function -
3 GET_LINE
Procedure
GET_LINE
Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 316

No. Oracle GaussDB Dierence
4 GET_LINES
Procedure
GET_LINES
Function
GaussDB: There is
no overloaded
function. The rst
parameter (lines)
is of the
VARCHAR[] type.
Oracle: There are
two overloaded
procedures. The
rst parameters
(lines) of the two
overloaded
procedures are of
the CHARARR and
DBMSOUTPUT_LI
NESARRAY types,
respectively.
5 NEW_LINE
Procedure
NEW_LINE
Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 317

No. Oracle GaussDB Dierence
6 PUT Procedure PUT Function GaussDB: If the
character set of
the database
server
(server_encoding
) is not encoded
in UTF-8 and the
character
encoding of the
input parameter is
valid UTF-8, this
function converts
character
encoding based
on the
relationship
"UTF8 >
server_encoding"
and then outputs
the result
regardless of the
data type of the
input parameter.
Oracle: If the
character set of
the database
server
(server_encoding
) is not encoded
in UTF-8, the
character
encoding of the
input parameter is
valid UTF-8, and
the input
parameter type is
NVARCHAR2, this
procedure coverts
the character
encoding based
on the
relationship
"UTF8 >
server_encoding"
and then outputs
the result. If the
input parameter is
of other character
types, the
character
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 318

No. Oracle GaussDB Dierence
encoding is
regarded as an
invalid character
and output as a
placeholder.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 319

No. Oracle GaussDB Dierence
7 PUT_LINE
Procedure
PUT_LINE
Function
GaussDB: If the
character set of
the database
server
(server_encoding
) is not encoded
in UTF-8 and the
character
encoding of the
input parameter is
valid UTF-8, this
function converts
character
encoding based
on the
relationship
"UTF8 >
server_encoding"
and then outputs
the result
regardless of the
data type of the
input parameter.
Oracle: If the
character set of
the database
server
(server_encoding
) is not encoded
in UTF-8, the
character
encoding of the
input parameter is
valid UTF-8, and
the input
parameter type is
NVARCHAR2, this
procedure coverts
the character
encoding based
on the
relationship
"UTF8 >
server_encoding"
and then outputs
the result. If the
input parameter is
of other character
types, the
character
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 320

No. Oracle GaussDB Dierence
encoding is
regarded as an
invalid character
and output as a
placeholder.
Table 7-215 UTL_RAW compatibility
No. Oracle GaussDB Dierence
1 BIT_AND Function BIT_AND Function -
2 BIT_COMPLEMEN
T Function
BIT_COMPLEMEN
T Function
-
3 BIT_OR Function BIT_OR Function GaussDB: The two
parameters are
dened as the
TEXT type and
returned as the
TEXT type.
Oracle: The two
parameters are of
the RAW type and
returned as the
RAW type.
4 BIT_XOR Function BIT_XOR Function -
5 CAST_FROM_BIN
ARY_DOUBLE
Function
CAST_FROM_BIN
ARY_DOUBLE_TO_
RAW Function
-
6 CAST_FROM_BIN
ARY_FLOAT
Function
CAST_FROM_BIN
ARY_FLOAT_TO_R
AW Function
GaussDB: The n
parameter is of
the FLOAT4 type.
Oracle: The n
parameter is of
the FLOAT type.
7 CAST_FROM_BIN
ARY_INTEGER
Function
CAST_FROM_BIN
ARY_INTEGER_TO
_RAW Function
GaussDB: The
value parameter
is of the BIGINT
type.
Oracle: The value
parameter is of
the INTEGER type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 321

No. Oracle GaussDB Dierence
8 CAST_FROM_NU
MBER Function
CAST_FROM_NU
MBER_TO_RAW
Function
GaussDB: The n
parameter is of
the NUMERIC
type.
Oracle: The n
parameter is of
the NUMBER
type.
9 CAST_TO_BINARY
_DOUBLE
Function
CAST_FROM_RAW
_TO_BINARY_DOU
BLE Function
-
10 CAST_TO_BINARY
_FLOAT Function
CAST_FROM_RAW
_TO_BINARY_FLO
AT Function
GaussDB: The
function returns
the FLOAT4 type.
Oracle: The
function returns
the FLOAT type.
11 CAST_TO_BINARY
_INTEGER
Function
CAST_FROM_RAW
_TO_BINARY_INTE
GER Function
GaussDB: The
endianess
parameter is of
the INTEGER type,
and the function
returns the
INTEGER type.
Oracle: The
endianess
parameter is of
the PLS_INTEGER
type, and the
function returns
the
BINARY_INTEGER
type.
12 CAST_TO_NUMBE
R Function
CAST_FROM_RAW
_TO_NUMBER
Function
GaussDB: The
function returns
the NUMERIC
type.
Oracle: The
function returns
the NUMBER
type.
13 CAST_TO_NVARC
HAR2 Function
CAST_FROM_RAW
_TO_NVARCHAR2
Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 322

No. Oracle GaussDB Dierence
14 CAST_TO_RAW
Function
CAST_FROM_VAR
CHAR2_TO_RAW
Function
-
15 CAST_TO_VARCH
AR2 Function
CAST_TO_VARCH
AR2 Function
-
16 COMPARE
Function
COMPARE
Function
GaussDB: The
function returns
the INTEGER type.
Oracle: The
function returns
the NUMBER
type.
17 CONCAT Function CONCAT Function -
18 CONVERT
Function
CONVERT
Function
-
19 COPIES Function COPIES Function GaussDB: The n
parameter is of
the NUMERIC
type.
Oracle: The n
parameter is of
the NUMBER
type.
20 LENGTH Function GET_LENGTH
Function
GaussDB: The
function returns
the INTEGER type.
Oracle: The
function returns
the NUMBER
type.
21 OVERLAY
Function
OVERLAY
Function
-
22 REVERSE Function REVERSE Function -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 323

No. Oracle GaussDB Dierence
23 SUBSTR Function SUBSTR Function GaussDB: The
lob_loc parameter
is of the BLOB
type. The o_set
parameter is of
the INTEGER type
and its default
value is 1. The
amount
parameter is of
the INTEGER type
and its default
value is 32767.
Oracle: The r
parameter is of
the RAW type.
The pos
parameter is of
the
BINARY_INTEGER
type and has no
default value. The
len parameter is
of the
BINARY_INTEGER
type and its
default value is
NULL.
24
TRANSLATE
Function
TRANSLATE
Function
-
25 TRANSLITERATE
Function
TRANSLITERATE
Function
-
26 XRANGE Function XRANGE Function GaussDB: The
start_byte and
end_byte
parameters do
not have default
values.
Oracle: The
default values of
the start_byte
and end_byte
parameters are
NULL.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 324

Table 7-216 DBMS_SCHEDULER compatibility
No. Oracle GaussDB
1 ADD_EVENT_QUEUE_SU
BSCRIBER Procedure
Not supported.
2 ADD_GROUP_MEMBER
Procedure
Not supported.
3 ADD_JOB_EMAIL_NOTIFI
CATION Procedure
Not supported.
4 ADD_TO_INCOMPATIBILI
TY Procedure
Not supported.
5 ALTER_CHAIN Procedure Not supported.
6 ALTER_RUNNING_CHAIN
Procedure
Not supported.
7 CLOSE_WINDOW
Procedure
Not supported.
8 COPY_JOB Procedure Not supported.
9 CREATE_CHAIN
Procedure
Not supported.
10 CREATE_CREDENTIAL
Procedure
CREATE_CREDENTIAL
Procedure
11 CREATE_DATABASE_DES
TINATION Procedure
Not supported.
12 CREATE_EVENT_SCHEDU
LE Procedure
Not supported.
13 CREATE_FILE_WATCHER
Procedure
Not supported.
14 CREATE_GROUP
Procedure
Not supported.
15 CREATE_INCOMPATIBILI
TY Procedure
Not supported.
16 CREATE_JOB Procedure CREATE_JOB Procedure
17 CREATE_JOB_CLASS
Procedure
CREATE_JOB_CLASS
Procedure
18 CREATE_JOBS Procedure Not supported.
19 CREATE_PROGRAM
Procedure
CREATE_PROGRAM
Procedure
20 CREATE_RESOURCE
Procedure
Not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 325

No. Oracle GaussDB
21 CREATE_SCHEDULE
Procedure
CREATE_SCHEDULE
Procedure
22 CREATE_WINDOW
Procedure
Not supported.
23 DEFINE_ANYDATA_ARGU
MENT Procedure
Not supported.
24 DEFINE_CHAIN_EVENT_S
TEP Procedure
Not supported.
25 DEFINE_CHAIN_RULE
Procedure
Not supported.
26 DEFINE_CHAIN_STEP
Procedure
Not supported.
27 DEFINE_METADATA_ARG
UMENT Procedure
Not supported.
28 DEFINE_PROGRAM_ARG
UMENT Procedure
DEFINE_PROGRAM_ARG
UMENT Procedure
29 DISABLE Procedure DISABLE Procedure
30 DROP_AGENT_DESTINAT
ION Procedure
Not supported.
31 DROP_CHAIN Procedure Not supported.
32 DROP_CHAIN_RULE
Procedure
Not supported.
33 DROP_CHAIN_STEP
Procedure
Not supported.
34 DROP_CREDENTIAL
Procedure
DROP_CREDENTIAL
Procedure
35 DROP_DATABASE_DESTI
NATION Procedure
Not supported.
36 DROP_FILE_WATCHER
Procedure
Not supported.
37 DROP_GROUP Procedure Not supported.
38 DROP_INCOMPATIBILITY
Procedure
Not supported.
39 DROP_JOB Procedure DROP_JOB Procedure
40 DROP_JOB_CLASS
Procedure
DROP_JOB_CLASS
Procedure
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 326

No. Oracle GaussDB
41 DROP_PROGRAM
Procedure
DROP_PROGRAM
Procedure
42 DROP_PROGRAM_ARGU
MENT Procedure
Not supported.
43 DROP_SCHEDULE
Procedure
DROP_SCHEDULE
Procedure
44 DROP_WINDOW
Procedure
Not supported.
45 ENABLE Procedure ENABLE Procedure
46 END_DETACHED_JOB_RU
N Procedure
Not supported.
47 EVALUATE_CALENDAR_S
TRING Procedure
EVALUATE_CALENDAR_S
TRING Procedure
48 EVALUATE_RUNNING_C
HAIN Procedure
Not supported.
49 GENERATE_JOB_NAME
Function
GENERATE_JOB_NAME
Function
50 GET_AGENT_INFO
Function
Not supported.
51 GET_AGENT_VERSION
Function
Not supported.
52 GET_ATTRIBUTE
Procedure
Not supported.
53 GET_FILE Procedure Not supported.
54 GET_SCHEDULER_ATTRI
BUTE Procedure
Not supported.
55 OPEN_WINDOW
Procedure
Not supported.
56 PURGE_LOG Procedure Not supported.
57 PUT_FILE Procedure Not supported.
58 REMOVE_EVENT_QUEUE
_SUBSCRIBER Procedure
Not supported.
59 REMOVE_FROM_INCOM
PATIBILITY Procedure
Not supported.
60 REMOVE_GROUP_MEMB
ER Procedure
Not supported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 327

No. Oracle GaussDB
61 REMOVE_JOB_EMAIL_N
OTIFICATION Procedure
Not supported.
62 RESET_JOB_ARGUMENT_
VALUE Procedure
Not supported.
63 RUN_CHAIN Procedure Not supported.
64 RUN_JOB Procedure RUN_JOB Procedure
65 SET_AGENT_REGISTRATI
ON_PASS Procedure
Not supported.
66 SET_ATTRIBUTE
Procedure
SET_ATTRIBUTE
Procedure
67 SET_ATTRIBUTE_NULL
Procedure
Not supported.
68 SET_JOB_ANYDATA_VAL
UE Procedure
Not supported.
69 SET_JOB_ARGUMENT_VA
LUE Procedure
SET_JOB_ARGUMENT_VA
LUE Procedure
70 SET_JOB_ATTRIBUTES
Procedure
Not supported.
71 SET_RESOURCE_CONSTR
AINT Procedure
Not supported.
72 SET_SCHEDULER_ATTRIB
UTE Procedure
Not supported.
73 STOP_JOB Procedure STOP_JOB Procedure
Table 7-217 DBMS_UTILITY compatibility
No.
Oracle GaussDB Dierence
1 ACTIVE_INSTANCE
S Procedure
Not supported. -
2 ANALYZE_DATABA
SE Procedure
Not supported. -
3 ANALYZE_PART_O
BJECT Procedure
Not supported. -
4 ANALYZE_SCHEM
A Procedure
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 328

No. Oracle GaussDB Dierence
5 CANONICALIZE
Procedure
CANONICALIZE
Procedure
GaussDB: The
default size of the
canon_len
parameter is 1024
bytes.
Oracle: The
canon_len
parameter has no
default value.
6 COMMA_TO_TABL
E Procedures
COMMA_TO_TABL
E Procedure
GaussDB: The tab
parameter is a
VARCHAR2 array.
Oracle: There are
two overloaded
procedures. The
tab parameter
can be of the
uncl_array or
lname_array type.
7 COMPILE_SCHEM
A Procedure
Not supported. -
8 CREATE_ALTER_TY
PE_ERROR_TABLE
Procedure
Not supported. -
9 CURRENT_INSTAN
CE Function
Not supported. -
10 DATA_BLOCK_AD
DRESS_BLOCK
Function
Not supported. -
11 DATA_BLOCK_AD
DRESS_FILE
Function
Not supported. -
12 DB_VERSION
Procedure
DB_VERSION
Procedure
GaussDB: There is
only the version
parameter, which
is of the
VARCHAR2 type.
Oracle: There are
the version and
compatibility
parameters, which
are of the
VARCHAR2 type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 329
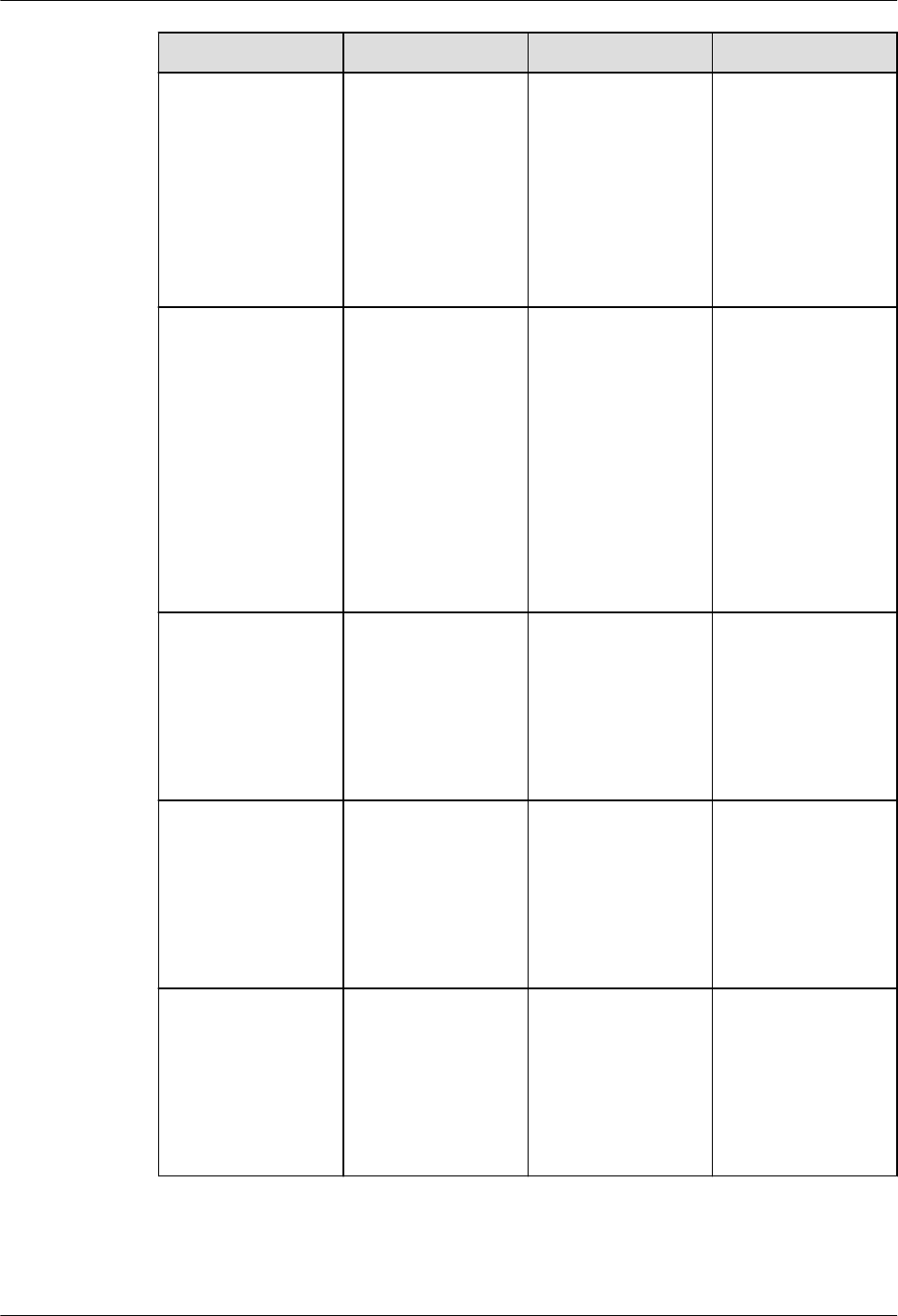
No. Oracle GaussDB Dierence
13 EXEC_DDL_STATE
MENT Procedure
EXEC_DDL_STATE
MENT Function
GaussDB: The
parse_string
parameter is of
the TEXT type.
Oracle: The
parse_string
parameter is of
the VARCHAR2
type.
14 EXPAND_SQL_TEX
T Procedure
EXPAND_SQL_TEX
T Function
GaussDB: The
output_sql_text
parameter is of
the CLOB type.
Oracle: The
output_sql_text
parameter is of
the NOCOPY
CLOB type. The
OUT parameter is
transferred by
reference.
15 FORMAT_CALL_ST
ACK Function
FORMAT_CALL_ST
ACK Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
16 FORMAT_ERROR_
BACKTRACE
Function
FORMAT_ERROR_
BACKTRACE
Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
17 FORMAT_ERROR_
STACK Function
FORMAT_ERROR_
STACK Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 330

No. Oracle GaussDB Dierence
18 GET_CPU_TIME
Function
GET_CPU_TIME
Function
GaussDB: The
function returns
the BIGINT type.
Oracle: The
function returns
the NUMBER
type.
19 GET_DEPENDENC
Y Procedure
Not supported. -
20 GET_ENDIANNESS
Function
GET_ENDIANNESS
Function
GaussDB: The
function returns
the INTEGER type.
Oracle: The
function returns
the NUMBER
type.
21 GET_HASH_VALU
E Function
GET_HASH_VALU
E Function
GaussDB: The
base and
hash_size
parameters and
the return types
are all INTEGER.
Oracle: The base
and hash_size
parameters and
the return types
are all NUMBER.
22 GET_PARAMETER_
VALUE Function
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 331

No. Oracle GaussDB Dierence
23 GET_SQL_HASH
Function
GET_SQL_HASH
Function
GaussDB: The
last4bytes
parameter of the
BIGINT type
species the last
four bytes of an
MD5 hash value
and is displayed
as an unsigned
integer. The
function returns
the BIGINT type.
Oracle: The
pre10ihash
parameter of the
NUMBER type is
used to store the
4-byte hash value
among the 16
bytes calculated
by MD5.
24
GET_TIME
Function
GET_TIME
Function
GaussDB: The
function returns
the BIGINT type.
Oracle: The
function returns
the NUMBER
type.
25 GET_TZ_TRANSITI
ONS Procedure
Not supported. -
26 INVALIDATE
Procedure
Not supported. -
27 IS_BIT_SET
Function
IS_BIT_SET
Function
GaussDB: The n
parameter and
return value type
are both INTEGER.
Oracle: The n
parameter and
return value type
are both
NUMBER.
28 IS_CLUSTER_DATA
BASE Function
IS_CLUSTER_DATA
BASE Function
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 332

No. Oracle GaussDB Dierence
29 MAKE_DATA_BLO
CK_ADDRESS
Function
Not supported. -
30 NAME_RESOLVE
Procedure
NAME_RESOLVE
Procedure
GaussDB: The
context and
part1_type
parameters are of
the INTEGER type,
and the
object_number
parameter is of
the OID type.
GaussDB does not
support implicit
conversion from
NUMBER to OID.
Oracle: The
context,
part1_type, and
object_number
parameters are of
the NUMBER
type.
31 NAME_TOKENIZE
Procedure
NAME_TOKENIZE
Procedure
GaussDB: The
nextpos
parameter is of
the INTEGER type.
Oracle: The
nextpos
parameter is of
the
BINARY_INTEGER
type.
32 OLD_CURRENT_S
CHEMA Function
OLD_CURRENT_S
CHEMA Function
GaussDB: The
function returns
the VARCHAR
type.
Oracle: The
function returns
the VARCHAR2
type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 333

No. Oracle GaussDB Dierence
33 OLD_CURRENT_U
SER Function
OLD_CURRENT_U
SER Function
GaussDB: The
function returns
the TEXT type.
Oracle: The
function returns
the VARCHAR2
type.
34 PORT_STRING
Function
Not supported. -
35 SQLID_TO_SQLHA
SH Function
Not supported. -
36 TABLE_TO_COMM
A Procedures
TABLE_TO_COMM
A Procedure
GaussDB: The tab
parameter is a
VARCHAR2 array.
Oracle: There are
two overloaded
stored procedures.
The tab
parameter can be
of the uncl_array
or lname_array
type.
37 VALIDATE
Procedure
Not supported. -
38 WAIT_ON_PENDI
NG_DML Function
Not supported. -
Table 7-218 DBMS_SQL compatibility
No.
Oracle GaussDB Dierence
1 BIND_ARRAY
Procedures
SQL_BIND_ARRAY
Function
-
2 BIND_VARIABLE
Procedures
SQL_BIND_VARIA
BLEFunction
-
3 BIND_VARIABLE_P
KG Procedure
Not supported. -
4 CLOSE_CURSOR
Procedure
SQL_UNREGISTER
_CONTEXT
Function
-
5 COLUMN_VALUE
Procedure
GET_RESULT
Procedure
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 334

No. Oracle GaussDB Dierence
6 COLUMN_VALUE_
LONG Procedure
Not supported. -
7 DEFINE_ARRAY
Procedure
SET_RESULTS_TYP
E Procedure
-
8 DEFINE_COLUMN
Procedures
SET_RESULT_TYPE
Procedure
-
9 DEFINE_COLUMN
_CHAR Procedure
Not supported. -
10 DEFINE_COLUMN
_LONG Procedure
Not supported. -
11 DEFINE_COLUMN
_RAW Procedure
Not supported. -
12 DEFINE_COLUMN
_ROWID
Procedure
Not supported. -
13 DESCRIBE_COLU
MNS Procedure
DESCRIBE_COLU
MNS Procedure
-
14 DESCRIBE_COLU
MNS2 Procedure
Not supported. -
15 DESCRIBE_COLU
MNS3 Procedure
Not supported. -
16 EXECUTE Function SQL_RUN
Function
-
17 EXECUTE_AND_FE
TCH Function
RUN_AND_NEXT
Function
-
18 FETCH_ROWS
Function
NEXT_ROW
Function
-
19 GET_NEXT_RESUL
T Procedures
Not supported. -
20 IS_OPEN Function IS_ACTIVE
Function
-
21 LAST_ERROR_POS
ITION Function
Not supported. -
22 LAST_ROW_COU
NT Function
LAST_ROW_COU
NT Function
-
23 LAST_ROW_ID
Function
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 335

No. Oracle GaussDB Dierence
24 LAST_SQL_FUNCT
ION_CODE
Function
Not supported. -
25 OPEN_CURSOR
Functions
REGISTER_CONTE
XT Function
-
26 PARSE Procedures Supported, with
dierences.
In GaussDB, the
SQL_SET_SQL
function does not
support
overloading.
27 RETURN_RESULT
Procedures
Not supported. -
28 TO_CURSOR_NU
MBER Function
Not supported. -
29 TO_REFCURSOR
Function
Not supported. -
30 VARIABLE_VALUE
Procedures
GET_VARIABLE_RE
SULT Procedures
-
31 VARIABLE_VALUE_
PKG Procedure
Not supported. -
Table 7-219 DBMS_SQL data type compatibility
No.
Oracle GaussDB
1 DBMS_SQL DESC_REC DBE_SQL.DESC_REC
2 DBMS_SQL DATE_TABLE DBE_SQL.DATE_TABLE
3 DBMS_SQL
NUMBER_TABLE
DBE_SQL.NUMBER_TABL
E
4 DBMS_SQL
VARCHAR2_TABLE
DBE_SQL.VARCHAR2_TA
BLE
5 DBMS_SQL BLOB_TABLE DBE_SQL.BLOB_TABLE
Table 7-220 UTL_FILE compatibility
No.
Oracle GaussDB Dierence
1 FCLOSE Procedure CLOSE Procedure -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 336
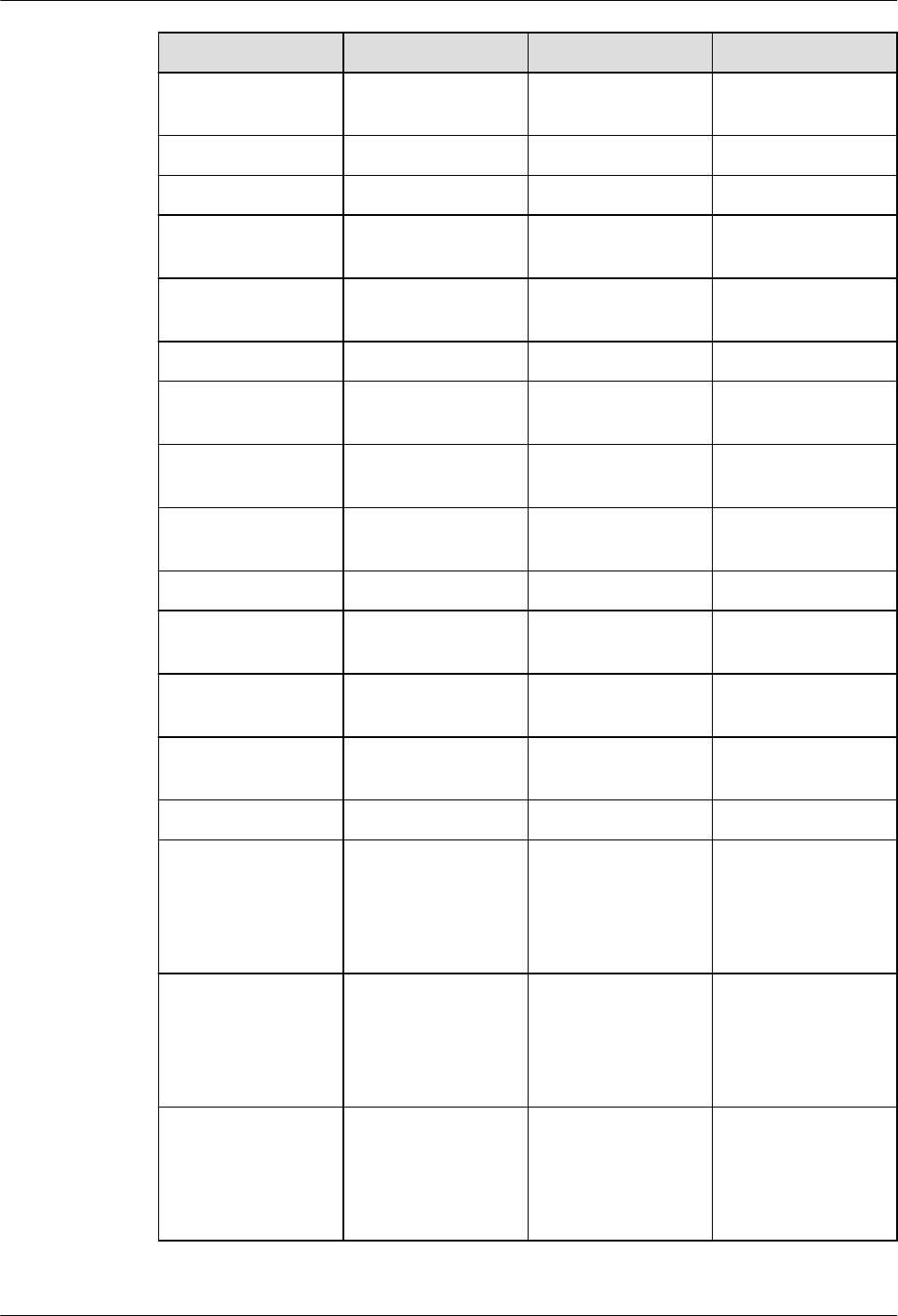
No. Oracle GaussDB Dierence
2 FCLOSE_ALL
Procedure
CLOSE_ALL
Procedure
-
3 FCOPY Procedure COPY Procedure -
4 FFLUSH Procedure FLUSH Procedure -
5 FGETATTR
Procedure
GET_ATTR
Procedure
-
6 FGETPOS
Function
GET_POS Function -
7 FOPEN Function FOPEN Function -
8 FOPEN_NCHAR
Function
FOPEN_NCHAR
Function
-
9 FREMOVE
Procedure
REMOVE
Procedure
-
10 FRENAME
Procedure
RENAME
Procedure
-
11 FSEEK Procedure SEEK Procedure -
12 GET_LINE
Procedure
READ_LINE
Procedure
-
13 GET_LINE_NCHAR
Procedure
READ_LINE_NCHA
R Procedure
-
14 GET_RAW
Procedure
GET_RAW
Procedure
-
15 IS_OPEN Function IS_OPEN Function -
16 NEW_LINE
Procedure
Supported, with
dierences in the
NEW_LINE
function
GaussDB denes
the interface as
function due to
performance
reasons.
17 PUT Procedure Supported, with
dierences in the
WRITE function
GaussDB denes
the interface as
function due to
performance
reasons.
18 PUT_LINE
Procedure
Supported, with
dierences in the
WRITE_LINE
function
GaussDB denes
the interface as
function due to
performance
reasons.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 337

No. Oracle GaussDB Dierence
19 PUT_LINE_NCHAR
Procedure
Supported, with
dierences in the
WRITE_LINE_NCH
AR function
GaussDB denes
the interface as
function due to
performance
reasons.
20 PUT_NCHAR
Procedure
Supported, with
dierences in the
WRITE_NCHAR
function
GaussDB denes
the interface as
function due to
performance
reasons.
21 PUTF Procedure Supported, with
dierences in the
FORMAT_WRITE
function
GaussDB denes
the interface as
function due to
performance
reasons.
22 PUTF_NCHAR
Procedure
Supported, with
dierences in the
FORMAT_WRITE_
NCHAR function
GaussDB denes
the interface as
function due to
performance
reasons.
23 PUT_RAW
Procedure
Supported, with
dierences in the
PUT_RAW
function
GaussDB denes
the interface as
function due to
performance
reasons.
Table 7-221 DBMS_SESSION compatibility
No.
Oracle GaussDB Dierence
1 CLEAR_ALL_CONT
EXT Procedure
Not supported. -
2 CLEAR_CONTEXT
Procedure
CLEAR_CONTEXT
Function
-
3 CLEAR_IDENTIFIER
Procedure
Not supported. -
4 CLOSE_DATABASE
_LINK Procedure
Not supported. -
5 CURRENT_IS_ROL
E_ENABLED
Function
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 338

No. Oracle GaussDB Dierence
6 FREE_UNUSED_US
ER_MEMORY
Procedure
Not supported. -
7 GET_PACKAGE_ME
MORY_UTILIZATI
ON Procedure
Not supported. -
8 IS_ROLE_ENABLED
Function
Not supported. -
9 IS_SESSION_ALIVE
Function
Not supported. -
10 LIST_CONTEXT
Procedures
Not supported. -
11 MODIFY_PACKAG
E_STATE
Procedure
MODIFY_PACKAG
E_STATE
Procedure
GaussDB: The
scenario where
ags is set to 1 is
supported.
Oracle: The
scenario where
ags is set to 1 or
2 is supported.
12 RESET_PACKAGE
Procedure
Not supported. -
13 SESSION_IS_ROLE
_ENABLED
Function
Not supported. -
14 SESSION_TRACE_
DISABLE
Procedure
Not supported. -
15 SESSION_TRACE_E
NABLE Procedure
Not supported. -
16 SET_CONTEXT
Procedure
SET_CONTEXT
Function
GaussDB: There
are the
namspace,
attribute, and
value parameters
of the TEXT type.
Oracle: There are
the namspace,
attribute, value,
username, and
client_id
parameters of the
VARCHAR2 type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 339

No. Oracle GaussDB Dierence
17 SET_EDITION_DEF
ERRED Procedure
Not supported. -
18 SET_IDENTIFIER
Procedure
Not supported. -
19 SET_NLS
Procedure
Not supported. -
20 SET_ROLE
Procedure
Not supported. -
21 SET_SQL_TRACE
Procedure
Not supported. -
22 SLEEP Procedure Not supported. -
23 SWITCH_CURREN
T_CONSUMER_GR
OUP Procedure
Not supported. --
24 UNIQUE_SESSION
_ID Function
Not supported. -
Table 7-222 UTL_MATCH compatibility
No.
Oracle GaussDB Dierence
1 EDIT_DISTANCE
Function
Not supported. -
2 EDIT_DISTANCE_S
IMILARITY
Function
EDIT_DISTANCE_S
IMILARITY
Function
GaussDB: The str1
and str2
parameters are of
the TEXT type,
and the function
returns the
INTEGER type.
Oracle: The s1
and s2
parameters are of
the VARCHAR2
type, and the
function returns
the PLS_INTEGER
type.
3 JARO_WINKLER
Function
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 340

No. Oracle GaussDB Dierence
4 JARO_WINKLER_SI
MILARITY
Function
Not supported. -
Table 7-223 DBMS_APPLICATION_INFO compatibility
No. Oracle GaussDB Dierence
1 READ_CLIENT_INF
O Procedure
READ_CLIENT_INF
O Function
GaussDB: The
client_info
parameter is of
the TEXT type.
Oracle: The
client_info
parameter is of
the VARCHAR2
type.
2 READ_MODULE
Procedure
READ_MODULE
Procedure
GaussDB: The
module_name
and action_name
parameters are of
the TEXT type.
Oracle: The
module_name
and action_name
parameters are of
the VARCHAR2
type.
3 SET_ACTION
Procedure
SET_ACTION
Procedure
GaussDB: The
action_name
parameter is of
the TEXT type.
Oracle: The
action_name
parameter is of
the VARCHAR2
type.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 341

No. Oracle GaussDB Dierence
4 SET_CLIENT_INFO
Procedure
SET_CLIENT_INFO
Function
GaussDB: The str
parameter is of
the TEXT type,
and the return
type is VOID.
Oracle: The
client_info
parameter is of
the VARCHAR2
type and no value
is returned. Both
of them are
written to the
client. The
maximum length
is 64 bytes. If the
length exceeds 64
bytes, it will be
truncated.
5 SET_MODULE
Procedure
SET_MODULE
Procedure
GaussDB: The
module_name
and action_name
parameters are of
the TEXT type.
Oracle: The
module_name
and action_name
parameters are of
the VARCHAR2
type.
6 SET_SESSION_LO
NGOPS Procedure
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 342
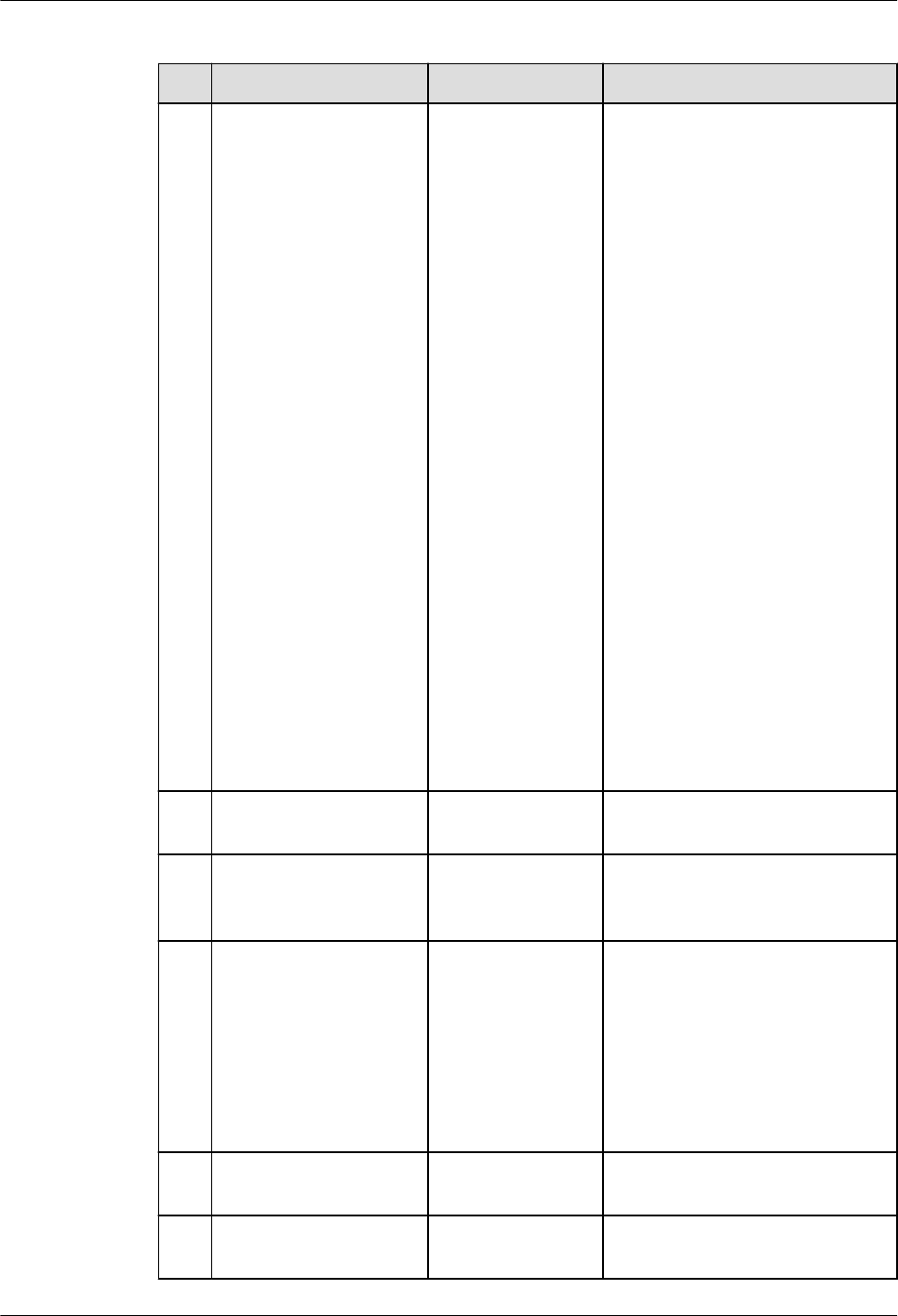
Table 7-224 DBMS_XMLDOM compatibility
No. Oracle GaussDB Dierence
1 DBMS_XMLDOM.APP
ENDCHILD
DBE_XMLDOM.A
PPENDCHILD
● GaussDB: The error
message "operation not
support" is displayed for
the APPEND ATTR node
under the DOCUMENT
node.
Oracle: No error is reported
in this scenario, but the
mounting fails.
● GaussDB: The error
message "operation not
support" is displayed for
the APPEND ATTR node
under the ATTR node.
Oracle: No error is reported
in this scenario, but the
mounting fails.
● GaussDB: When multiple
child nodes of the ATTR
type are added to a parent
node, the child nodes with
the same key value cannot
exist under the same
parent node.
Oracle: Subnodes with the
same key value can exist
under the same parent
node.
2
DBMS_XMLDOM.CRE
ATEELEMENT
DBE_XMLDOM.C
REATEELEMENT
-
3 DBMS_XMLDOM.CRE
ATETEXTNODE
DBE_XMLDOM.C
REATETEXTNOD
E
-
4 DBMS_XMLDOM.FRE
EDOCUMENT
DBE_XMLDOM.F
REEDOCUMENT
GaussDB: Objects are not
released immediately. They
are released after a certain
number of objects are
accumulated. All nodes in the
document are invalid.
Oracle: The object is released
immediately.
5 DBMS_XMLDOM.FRE
EELEMENT
DBE_XMLDOM.F
REEELEMENT
-
6 DBMS_XMLDOM.FRE
ENODE
DBE_XMLDOM.F
REENODE
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 343

No. Oracle GaussDB Dierence
7 DBMS_XMLDOM.FRE
ENODELIST
DBE_XMLDOM.F
REENODELIST
GaussDB: The nodelist will be
released.
Oracle: After the nodelist is
released, it can still be queried
in the original document.
8 DBMS_XMLDOM.GET
ATTRIBUTE
DBE_XMLDOM.G
ETATTRIBUTE
-
9 DBMS_XMLDOM.GET
ATTRIBUTES
DBE_XMLDOM.G
ETATTRIBUTES
-
10 DBMS_XMLDOM.GET
CHILDNODES
DBE_XMLDOM.G
ETCHILDNODES
GaussDB: When the document
node is used, DTD is included.
Oracle: DTD is not included.
11 DBMS_XMLDOM.GET
CHILDRENBYTAGNA
ME
DBE_XMLDOM.G
ETCHILDRENBYT
AGNAME
GaussDB: The ns parameter of
the
DBE_XMLDOM.GETCHILDREN
BYTAGNAME interface does
not support the asterisk (*)
parameter. To obtain all
attributes of a node, use the
DBE_XMLDOM.GETCHILDNOD
ES interface.
Oracle: The input parameter *
is supported.
12 DBMS_XMLDOM.GET
DOCUMENTELEMEN
T
DBE.XMLDOM.G
ETDOCUMENTEL
EMENT
-
13 DBMS_XMLDOM.GET
FIRSTCHILD
DBE_XMLDOM.G
ETFIRSTCHILD
-
14 DBMS_XMLDOM.GET
LASTCHILD
DBE_XMLDOM.G
ETLASTCHILD
-
15 DBMS_XMLDOM.GET
LENGTH
DBE_XMLDOM.G
ETLENGTH
-
16 DBMS_XMLDOM.GET
LOCALNAME
DBE_XMLDOM.G
ETLOCALNAME
-
17 DBMS_XMLDOM.GET
NAMEDITEM
DBE_XMLDOM.G
ETNAMEDITEM
-
18 DBMS_XMLDOM.GET
NEXTSIBLING
DBE_XMLDOM.G
ETNEXTSIBLING
-
19 DBMS_XMLDOM.GET
NODENAME
DBE_XMLDOM.G
ETNODENAME
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 344

No. Oracle GaussDB Dierence
20 DBMS_XMLDOM.GET
NODETYPE
DBE_XMLDOM.G
ETNODETYPE
-
21 DBMS_XMLDOM.GET
TAGNAME
DBE_XMLDOM.G
ETTAGNAME
-
22 DBMS_XMLDOM.IMP
ORTNODE
DBE_XMLDOM.I
MPORTNODE
-
23 DBMS_XMLDOM.ISN
ULL
DBE_XMLDOM.IS
NULL
GaussDB: When the input
parameter is of the
DOMNODELIST type, an error
is reported if the object does
not exist in the hash table.
Oracle: No error is reported.
24 DBMS_XMLDOM.ITE
M
DBE_XMLDOM.IT
EM
-
25 DBMS_XMLDOM.MA
KENODE
DBE_XMLDOM.
MAKENODE
GaussDB: This function cannot
be directly returned as the
function return value.
Oracle: It is directly returned
as the function return value.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 345

No. Oracle GaussDB Dierence
26 DBMS_XMLDOM.NE
WDOMDOCUMENT
DBE_XMLDOM.N
EWDOMDOCUM
ENT
● The input parameter size of
the centralized GaussDB
must be less than 2 GB.
Oracle: The size is the same
as that of the CLOB type.
● Currently, external DTD
parsing is not supported in
GaussDB.
Oracle: External DTD can
be parsed.
● GaussDB: The default
character set of doc created
by newdomdocument is
UTF-8.
Oracle: It is generated
based on the character set
of the server.
● GaussDB: Each doc parsed
from the same xmltype
instance is independent,
and the modication of the
doc does not aect the
xmltype.
Oracle: Each doc parsed
from the same xmltype
instance is not independent
but associated.
● GaussDB: The version
column supports only 1.0.
If 1.0 to 1.9 are parsed, a
warning is reported but the
execution is normal. For
versions later than 1.9, an
error is reported.
Oracle: No error is
reported.
● DTD verication dierence
between GaussDB and
Oracle: !ATTLIST to type
(CHECK|check|Check)
"Ch..." reports an error
because the default value
"Ch..." is not an
enumerated value in the
brackets. However, Oracle
does not report this error.
<!ENTITY baidu
"www.baidu.com">......
&Baidu;&writer reports an
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 346

No. Oracle GaussDB Dierence
error. Baidu cannot
correspond to baidu
because the letters are
case-sensitive.
Oracle: No error is
reported.
● Namespace verication
dierence between
GaussDB and Oracle:
Undeclared namespace
tags are parsed in
GaussDB.
Oracle: An error is reported.
27 DBMS_XMLDOM.SET
ATTRIBUTE
DBE_XMLDOM.S
ETATTRIBUTE
GaussDB: The attribute key
cannot be null or an empty
string.
Oracle: The attribute key can
be null or an empty string.
28 DBMS_XMLDOM.SET
CHARSET
DBE_XMLDOM.S
ETCHARSET
Currently, the following
character sets are supported
in GaussDB: UTF-8, UTF-16,
UCS-4, UCS-2, ISO-8859-1,
ISO-8859-2, ISO-8859-3,
ISO-8859-4, ISO-8859-5,
ISO-8859-6, ISO-8859-7,
ISO-8859-8, ISO-8859-9,
ISO-2022-JP, Shift_JIS, EUC-JP,
and ASCII. If you enter other
character sets, an error is
reported or garbled characters
may be displayed.
29 DBMS_XMLDOM.SET
DOCTYPE
DBE_XMLDOM.S
ETDOCTYPE
GaussDB: The total length of
name, sysid, and pubid cannot
exceed 32,500 bytes.
Oracle: The maximum size is
32,767 bytes.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 347

No. Oracle GaussDB Dierence
30 DBMS_XMLDOM.WRI
TETOBUFFER
DBE_XMLDOM.
WRITETOBUFFER
● GaussDB: The writetobuer
output buer is limited to
less than 1 GB.
Oracle: The maximum size
is 32,767 bytes.
● GaussDB: The output doc
will contain the XML
declaration version and
encoding.
Oracle: It is not contained
unless being specied by
users.
● GaussDB: If the input
parameter is of the
domnode type and the
node is converted from a
doc, the output node
contains the XML
declaration version and
encoding.
Oracle: It is not contained
unless being specied by
users.
● GaussDB: By default, XML
les are output in the
UTF-8 character set.
Oracle: It is generated
based on the database
character set.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 348

No. Oracle GaussDB Dierence
31 DBMS_XMLDOM.WRI
TETOCLOB
DBE_XMLDOM.
WRITETOCLOB
● GaussDB: The writetoclob
size cannot exceed 1 GB.
Oracle: The supported size
depends on the CLOB size.
● GaussDB: The output doc
will contain the XML
declaration version and
encoding.
Oracle: It is not contained
unless being specied by
users.
● GaussDB: If the input
parameter is of the
domnode type and the
node is converted from a
doc, the output node
contains the XML
declaration version and
encoding.
Oracle: It is not contained
unless being specied by
users.
● GaussDB: By default, XML
les are output in the
UTF-8 character set.
Oracle: It is generated
based on the database
character set.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 349

No. Oracle GaussDB Dierence
32 DBMS_XMLDOM.WRI
TETOFILE
DBE_XMLDOM.
WRITETOFILE
● GaussDB document input
parameter. The length of
lename cannot exceed
255 bytes. For details about
charset, see the
dbe_xmldom.setcharset
API.
Oracle: The length of
lename is aected by the
OS and is greater than 255
bytes.
● GaussDB DOMNode input
parameter. The length of
lename cannot exceed
255 bytes. For details about
charset, see the
dbe_xmldom.setcharset
API.
Oracle: The length of
lename is aected by the
OS and is greater than 255
bytes.
● GaussDB: This function
adds content such as
indentation to format the
output. The output doc will
contain the XML
declaration version and
encoding. If the input
parameter is of the
domnode type and the
node is converted from a
doc, the output node
contains the XML
declaration version and
encoding.
Oracle: It is not contained
unless being specied by
users.
● GaussDB: If
newdomdocument() is
used to create a doc
without parameters, no
error is reported when
charset is not specied.
The UTF-8 character set is
used by default.
Oracle: An error is reported.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 350

No. Oracle GaussDB Dierence
● GaussDB: The lename
must be in the path
created in pg_directory. The
backslash (\) in the
lename will be converted
to a slash (/). Only one
slash (/) is allowed. The le
name must be in the
pg_directory_name/
le_name format.
Oracle: User input is not
escaped.
33 DBMS_XMLDOM.GET
NODEVALUE
DBE_XMLDOM.G
ETNODEVALUE
-
34 DBMS_XMLDOM.GET
PARENTNODE
DBE_XMLDOM.G
ETPARENTNODE
-
35 DBMS_XMLDOM.HAS
CHILDNODES
DBE_XMLDOM.H
ASCHILDNODES
-
36 DBMS_XMLDOM.MA
KEELEMENT
DBE_XMLDOM.
MAKEELEMENT
-
37 DBMS_XMLDOM.SET
NODEVALUE
DBE_XMLDOM.S
ETNODEVALUE
● GaussDB: Input parameter
of nodeValue. You can
enter an empty string or
NULL, but the node value
will not be changed.
Oracle: If you enter an
empty string or NULL, the
node value is set to an
empty string.
● GaussDB: Input parameter
of nodeValue. The escape
character '&' is not
supported. If the character
string contains the escape
character, the node value
will be cleared.
Oracle: Escape characters
are supported.
38 DBMS_XMLDOM.GET
ELEMENTSBYTAGNA
ME
DBE_XMLDOM.G
ETELEMENTSBYT
AGNAME
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 351

Table 7-225 DBMS_XMLPARSER compatibility
No. Oracle GaussDB Dierence
1 DBMS_XMLPARSE
R.FREEPARSER
DBE_XMLPARSER.
FREEPARSER
-
2 DBMS_XMLPARSE
R.GETDOCUMENT
DBE_XMLPARSER.
GETDOCUMENT
-
3 DBMS_XMLPARSE
R.GETVALIDATIO
NMODE
DBE_XMLPARSER.
GETVALIDATION
MODE
-
4 DBMS_XMLPARSE
R.NEWPARSER
Supported, with
dierences in
DBE_XMLPARSER.
NEWPARSER
The maximum
number of parser
objects in
GaussDB is
16,777,215, and
that in Oracle is
about 100
million.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 352

No. Oracle GaussDB Dierence
5 DBMS_XMLPARSE
R.PARSEBUFFER
Supported, with
dierences in
DBE_XMLPARSER.
PARSEBUFFER
1. Dierence in
parsing columns:
Only UTF-8 is
supported in
terms of
character
encoding, and
version can only
be set to 1.0. If
versions 1.0 to 1.9
are parsed, a
warning appears
but the execution
is normal. For
versions later
than 1.9, an error
is reported.
2. Namespace
validation
dierence:
Undeclared
namespace tags
are parsed.
However, Oracle
reports this error.
3. Dierence in
parsing XML
predened
entities: '
and " are
parsed and
translated into '
and ". However,
predened
entities in Oracle
are not translated
into characters.
4. DTD validation
dierences:
● !ATTLIST to
type (CHECK|
check|Check)
"Ch..." reports
an error
because the
default value
"Ch..." is not
an
enumerated
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 353
No. Oracle GaussDB Dierence
value in the
brackets.
However,
Oracle does
not report this
error.
● <!ENTITY
baidu
"www.baidu.c
om">......
&Baidu;&writ
er reports an
error because
the letters are
case sensitive.
Baidu cannot
correspond to
baidu.
However,
Oracle does
not report this
error.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 354

No. Oracle GaussDB Dierence
6 DBMS_XMLPARSE
R.PARSECLOB
Supported, with
dierences in
DBE_XMLPARSER.
PARSECLOB
1. PARSECLOB
cannot parse
CLOBs greater
than or equal to
2 GB.
2. Dierence in
parsing columns:
Only UTF-8 is
supported in
terms of
character
encoding, and
version can only
be set to 1.0. If
versions 1.0 to 1.9
are parsed, a
warning appears
but the execution
is normal. For
versions later
than 1.9, an error
is reported.
3. Namespace
validation
dierence:
Undeclared
namespace tags
are parsed.
However, Oracle
reports this error.
4. Dierence in
parsing XML
predened
entities: '
and " are
parsed and
translated into '
and ". However,
predened
entities in Oracle
are not translated
into characters.
5. DTD validation
dierences:
● !ATTLIST to
type (CHECK|
check|Check)
"Ch..." reports
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 355
No. Oracle GaussDB Dierence
an error
because the
default value
"Ch..." is not
an
enumerated
value in the
brackets.
However,
Oracle does
not report this
error.
● <!ENTITY
baidu
"www.baidu.c
om">......
&Baidu;&writ
er reports an
error because
the letters are
case sensitive.
Baidu cannot
correspond to
baidu.
However,
Oracle does
not report this
error.
7
DBMS_XMLPARSE
R.SETVALIDATION
MODE
DBE_XMLPARSER.
SETVALIDATIONM
ODE
-
Table 7-226 DBMS_ILM compatibility
No.
Oracle GaussDB Dierence
1 DBMS_ILM.ADD_T
O_ILM
Not supported. -
2 DBMS_ILM.ARCHI
VESTATENAME
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 356

No. Oracle GaussDB Dierence
3 DBMS_ILM.EXECU
TE_ILM
Supported, with
dierences in
DBE_ILM.EXECUTE
_ILM
● The input
parameter
schema in
GaussDB
corresponds to
owner in
Oracle.
● GaussDB does
not support
the operation
of specifying
ilm_scope
(specifying
multiple
objects at a
time).
4 DBMS_ILM.EXECU
TE_ILM_TASK
Not supported. -
5 DBMS_ILM.PREVI
EW_ILM
Not supported. -
6 DBMS_ILM.REMO
VE_FROM_ILM
Not supported. -
7 DBMS_ILM.STOP_
ILM
DBE_ILM.STOP_IL
M
-
Table 7-227 DBMS_ILM_ADMIN compatibility
No.
Oracle GaussDB Dierence
1 DBMS_ILM_ADMI
N.CLEAR_HEAT_M
AP_ALL
Not supported. -
2 DBMS_ILM_ADMI
N.CLEAR_HEAT_M
AP_TABLE
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 357

No. Oracle GaussDB Dierence
3 DBMS_ILM_ADMI
N.CUSTOMIZE_IL
M
Supported, with
dierences in
DBE_ILM_ADMIN.
CUSTOMIZE_ILM
The feature
parameters
corresponding to
the values of
input parameters
are dierent. The
value of param in
GaussDB can be
1, 2, 7, 11, 12, 13,
14, or 15. When
the value of
param in
GaussDB is 14,
the corresponding
feature
parameter is
WIND_DURATIO
N which is used
to control the
execution window
duration in
automatic
scheduling. When
the value of
param in Oracle
is 14, the
corresponding
feature
parameter is
AUTO_OPTIMIZE
_INACTIVITY_TH
RESHOLD which
indicates the
inactive duration
of the ADO.
4
DBMS_ILM_ADMI
N.DISABLE_ILM
DBE_ILM_ADMIN.
DISABLE_ILM
-
5 DBMS_ILM_ADMI
N.ENABLE_AUTO_
OPTIMIZE
Not supported. -
6 DBMS_ILM_ADMI
N.ENABLE_ILM
DBE_ILM_ADMIN.E
NABLE_ILM
-
7 DBMS_ILM_ADMI
N.
IGNORE_AUTO_O
PTIMIZE_
CRITERIA
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 358

No. Oracle GaussDB Dierence
8 DBMS_ILM_ADMI
N.SET_HEAT_MAP
_ALL
Not supported. -
9 DBMS_ILM_ADMI
N.SET_HEAT_MAP
_START
Not supported. -
10 DBMS_ILM_ADMI
N.SET_HEAT_MAP
_TABLE
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 359

Table 7-228 DBMS_COMPRESSION compatibility
No. Oracle GaussDB Dierence
1 DBMS_COMPRESS
ION.GET_COMPRE
SSION_RATIO
Supported, with
dierences in
DBE_COMPRESSIO
N.GET_COMPRESS
ION_RATIO
● GaussDB
cannot obtain
compression
rates of LOBs.
● For obtaining
a compression
rate of a single
object:
– The value
of the input
parameter
comptype
in GaussDB
can only be
1
(uncompres
sed) or 2
(advanced
compressio
n) while
Oracle also
supports
values such
as 1024
and 2048.
– The value
of the input
parameter
objtype in
GaussDB
can only be
1 (table
object)
while
Oracle also
supports
the value 2
(index
object).
– Oracle uses
the
subset_nu
mrows
parameter
to directly
determine
the number
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 360

No. Oracle GaussDB Dierence
of rows to
be sampled
(that is, the
value of the
parameter).
GaussDB
uses
sample_rat
io
(sampling
rate) to
indirectly
determine
the number
of rows to
be sampled.
2 DBMS_COMPRESS
ION.GET_COMPRE
SSION_TYPE
Supported, with
dierences in
DBE_COMPRESSIO
N.GET_COMPRESS
ION_TYPE
● Oracle uses a
row ID to
specify the row
whose
compression
type is to be
obtained,
while GaussDB
uses a CTID to
specify the
row.
● The value of
comptype is
returned. The
value
dierence is
the same as
that of
GET_COMPRES
SION_RATIO.
Table 7-229 DBMS_HEAT_MAP compatibility
No.
Oracle GaussDB Dierence
1 DBMS_HEAT_MAP
.BLOCK_HEAT_MA
P
Not supported. -
2 DBMS_HEAT_MAP
.EXTENT_HEAT_M
AP
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 361

No. Oracle GaussDB Dierence
3 DBMS_HEAT_MAP
.OBJECT_HEAT_M
AP
Not supported. -
4 DBMS_HEAT_MAP
.SEGMENT_HEAT_
MAP
Not supported. -
5 DBMS_HEAT_MAP
.TABLESPACE_HEA
T_MAP
Not supported. -
6 Not supported. DBE_HEAT_MAP.R
OW_HEAT_MAP
For details, see
"Stored Procedure
> Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommended)
>
DBE_HEAT_MAP"
in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 362

Table 7-230 DBMS_DESCRIBE compatibility
No. Oracle GaussDB Dierence
1 DBMS_DESCRIBE.
DESCRIBE_PROCE
DURE
Supported, with
dierences in
DBE_DESCRIBE.DE
SCRIBE_PROCEDU
RE
● The datatype
parameter is
dierent from
the O
database.
GaussDB
returns the
OID of the
data type, and
the O
database
returns the ID
of the data
type in the O
database.
● The
datalength,
dataprecision,
and scale
parameters are
set to 0
because type
constraints
(such as
number (7,2)
and
varchar2(20))
cannot be
retained when
GaussDB
creates stored
procedures or
functions.
Oracle can use
the %type
method to
obtain
constrained
data types.
● For details
about the
behavior
dierences,
see "Stored
Procedure >
Advanced
Package >
Secondary
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 363

No. Oracle GaussDB Dierence
Encapsulation
Interfaces
(Recommende
d) >
DBE_DESCRIBE
" in
Developer
Guide
.
Table 7-231 DBMS_STATS compatibility
No. Oracle GaussDB Dierence
1 DBMS_STATS.ALTE
R_STATS_HISTORY
_RETENTION
Not supported. -
2 DBMS_STATS.CAN
CEL_ADVISOR_TA
SK
Not supported. -
3 DBMS_STATS.CON
FIGURE_ADVISOR
_FILTER
Not supported. -
4 DBMS_STATS.CON
FIGURE_ADVISOR
_OBJ_FILTER
Not supported. -
5 DBMS_STATS.CON
FIGURE_ADVISOR
_OPR_FILTER
Not supported. -
6 DBMS_STATS.CON
FIGURE_ADVISOR
_RULE_FILTER
Not supported. -
7 DBMS_STATS.CRE
ATE_ADVISOR_TA
SK
Not supported. -
8 DBMS_STATS.CON
VERT_RAW_VALU
E
Not supported. -
9 DBMS_STATS.CON
VERT_RAW_VALU
E_NVARCHAR
Not supported. -
10 DBMS_STATS.CON
VERT_RAW_VALU
E_ROWID
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 364

No. Oracle GaussDB Dierence
11 DBMS_STATS.COP
Y_TABLE_STATS
Not supported. -
12 DBMS_STATS.CRE
ATE_EXTENDED_S
TATS
Not supported. -
13 DBMS_STATS.CRE
ATE_STAT_TABLE
DBE_STATS.CREAT
E_STAT_TABLE
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 365

No. Oracle GaussDB Dierence
14 DBMS_STATS.DEL
ETE_COLUMN_ST
ATS
DBE_STATS.DELET
E_COLUMN_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In GaussDB,
this API can be
used to set
expression
statistics, but
tabname must
be set to an
index name
corresponding
to the
expression.
15
DBMS_STATS.DEL
ETE_DATABASE_P
REFS
Not supported. -
16 DBMS_STATS.DEL
ETE_DATABASE_S
TATS
Not supported. -
17 DEDBMS_STATS.D
ELETE_DICTIONAR
Y_STATS
Not supported. -
18 DBMS_STATS.DEL
ETE_FIXED_OBJEC
TS_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 366

No. Oracle GaussDB Dierence
19 DBMS_STATS.DEL
ETE_INDEX_STATS
DBE_STATS.DELET
E_INDEX_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
20
DBMS_STATS.DEL
ETE_PENDING_ST
ATS
Not supported. -
21 DBMS_STATS.DEL
ETE_PROCESSING
_RATE
Not supported. -
22 DBMS_STATS.DEL
ETE_SCHEMA_PRE
FS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 367

No. Oracle GaussDB Dierence
23 DBMS_STATS.DEL
ETE_SCHEMA_STA
TS
DBE_STATS.DELET
E_SCHEMA_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
24
DBMS_STATS.DEL
ETE_SYSTEM_STA
TS
Not supported. -
25 DBMS_STATS.DEL
ETE_TABLE_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 368

No. Oracle GaussDB Dierence
26 DBMS_STATS.DEL
ETE_TABLE_STATS
DBE_STATS.DELET
E_TABLE_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
27
DBMS_STATS.DIFF
_TABLE_STATS_IN
_HISTORY
Not supported. -
28 DBMS_STATS.DIFF
_TABLE_STATS_IN
_PENDING
Not supported. -
29 DBMS_STATS.DIFF
_TABLE_STATS_IN
_STATTAB
Not supported. -
30 DBMS_STATS.DRO
P_ADVISOR_TASK
Not supported. -
31 DBMS_STATS.DRO
P_EXTENDED_STA
TS
Not supported. -
32 DBMS_STATS.DRO
P_STAT_TABLE
DBE_STATS.DROP_
STAT_TABLE
-
33 DBMS_STATS.EXE
CUTE_ADVISOR_T
ASK
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 369
No. Oracle GaussDB Dierence
34 DBMS_STATS.EXP
ORT_COLUMN_ST
ATS
DBE_STATS.EXPOR
T_COLUMN_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● The exported
column-level
statistics are
consistent with
those in the
pg_statistic
catalog.
Multiple
columns are
consistent with
those in the
pg_statistic_ext
catalog.
● Index
expression
statistics can
be exported.
tabname must
be set to an
index name,
and colname
must be set to
an index
expression
name.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 370

No. Oracle GaussDB Dierence
● Permission:
You must have
the analyze
permission to
query tables
and the siud
permission on
the stattab
table.
35 DBMS_STATS.EXP
ORT_DATABASE_P
REFS
Not supported. -
36 DBMS_STATS.EXP
ORT_DATABASE_S
TATS
Not supported. -
37 DBMS_STATS.EXP
ORT_DICTIONARY
_STATS
Not supported. -
38 DBMS_STATS.EXP
ORT_FIXED_OBJEC
TS_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 371

No. Oracle GaussDB Dierence
39 DBMS_STATS.EXP
ORT_INDEX_STAT
S
DBE_STATS.EXPOR
T_INDEX_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In the stattab
table, the
exported
table-level and
partition-level
statistics are
numrows,
numblocks,
and
relallvisible,
which
correspond to
reltuples,
relpages, and
relallvisible in
the pg_class
and
pg_partition
system
catalogs,
respectively.
● Permission:
You must have
the analyze
permission to
query tables
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 372

No. Oracle GaussDB Dierence
and the siud
permission on
the stattab
table.
40 DBMS_STATS.EXP
ORT_PENDING_ST
ATS
Not supported. -
41 DBMS_STATS.EXP
ORT_SCHEMA_PR
EFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 373

No. Oracle GaussDB Dierence
42 DBMS_STATS.EXP
ORT_SCHEMA_ST
ATS
DBE_STATS.EXPOR
T_SCHEMA_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In the stattab
table, the
exported
table-level and
partition-level
statistics are
numrows,
numblocks,
and
relallvisible,
which
correspond to
reltuples,
relpages, and
relallvisible in
the pg_class
and
pg_partition
system
catalogs,
respectively.
The column-
level statistics
of the
exported table
are consistent
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 374

No. Oracle GaussDB Dierence
with those of
the pg_statistic
and
pg_statistic_ext
catalogs.
● Permission:
You must have
the siud
permission on
the stattab
table.
43 DBMS_STATS.EXP
ORT_SYSTEM_STA
TS
Not supported. -
44 DBMS_STATS.EXP
ORT_TABLE_PREF
S
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 375

No. Oracle GaussDB Dierence
45 DBMS_STATS.EXP
ORT_TABLE_STATS
DBE_STATS.EXPOR
T_TABLE_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In the stattab
table, the
exported
table-level and
partition-level
statistics are
numrows,
numblocks,
and
relallvisible,
which
correspond to
reltuples,
relpages, and
relallvisible in
the pg_class
and
pg_partition
system
catalogs,
respectively.
The column-
level statistics
exported in
cascading
mode are
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 376

No. Oracle GaussDB Dierence
consistent with
those in the
pg_statistic
and
pg_statistic_ext
catalogs.
● Permission:
You must have
the analyze
permission to
query tables
and the siud
permission on
the stattab
table.
46 DBMS_STATS.FLU
SH_DATABASE_M
ONITORING_INFO
Not supported. -
47 DBMS_STATS.GAT
HER_DATABASE_S
TATS
Not supported. -
48 DBMS_STATS.GAT
HER_DICTIONARY
_STATS
Not supported. -
49 DBMS_STATS.GAT
HER_FIXED_OBJEC
TS_STATS
Not supported. -
50 DBMS_STATS.GAT
HER_INDEX_STAT
S
Not supported. -
51 DBMS_STATS.GAT
HER_PROCESSING
_RATE
Not supported. -
52 DBMS_STATS.GAT
HER_SCHEMA_ST
ATS
Not supported. -
53 DBMS_STATS.GAT
HER_SYSTEM_STA
TS
Not supported. -
54 DBMS_STATS.GAT
HER_TABLE_STATS
Not supported. -
55 DBMS_STATS.GEN
ERATE_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 377

No. Oracle GaussDB Dierence
56 DBMS_STATS.GET
_ADVISOR_OPR_FI
LTER
Not supported. -
57 DBMS_STATS.GET
_ADVISOR_RECS
Not supported. -
58 DBMS_STATS.GET
_COLUMN_STATS
Not supported. -
59 DBMS_STATS.GET
_INDEX_STATS
Not supported. -
60 DBMS_STATS.GET
_PARAM
Not supported. -
61 DBMS_STATS.GET
_PREFS
Not supported. -
62 DBMS_STATS.GET
_STATS_HISTORY_
AVAILABILITY
DBE_STATS.GET_S
TATS_HISTORY_AV
AILABILITY
GaussDB queries
the collection
time of the
earliest historical
statistics in the
entire database.
63 DBMS_STATS.GET
_STATS_HISTORY_
RETENTION
DBE_STATS.GET_S
TATS_HISTORY_RE
TENTION
-
64 DBMS_STATS.GET
_SYSTEM_STATS
Not supported. -
65 DBMS_STATS.GET
_TABLE_STATS
Not supported. -
66 DBMS_STATS.IMP
LEMENT_ADVISO
R_TASK
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 378

No. Oracle GaussDB Dierence
67 DBMS_STATS.IMP
ORT_COLUMN_ST
ATS
DBE_STATS.IMPOR
T_COLUMN_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● The exported
single-column
col statistics
are the same
as those in the
pg_statistic
catalog. The
exported
multi-column
ext-col
statistics are
consistent with
those in the
pg_statistic_ext
catalog.
● Index
expression
statistics can
be imported.
tabname must
be set to an
index name,
and colname
must be set to
an index
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 379

No. Oracle GaussDB Dierence
expression
name.
● Permission:
You must have
the analyze
permission to
query tables
and the siud
permission on
the stattab
table.
68 DBMS_STATS.IMP
ORT_DATABASE_P
REFS
Not supported. -
69 DBMS_STATS.IMP
ORT_DATABASE_S
TATS
Not supported. -
70 DBMS_STATS.IMP
ORT_DICTIONARY
_STATS
Not supported. -
71 DBMS_STATS.IMP
ORT_FIXED_OBJEC
TS_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 380

No. Oracle GaussDB Dierence
72 DBMS_STATS.IMP
ORT_INDEX_STAT
S
DBE_STATS.IMPOR
T_INDEX_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In the stattab
table, the
imported
table-level and
partition-level
statistics are
numrows,
numblocks,
and
relallvisible,
which
correspond to
reltuples,
relpages, and
relallvisible in
the pg_class
and
pg_partition
system
catalogs,
respectively.
● Permission:
You must have
the analyze
permission to
query tables
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 381

No. Oracle GaussDB Dierence
and the siud
permission on
the stattab
table.
73 DBMS_STATS.IMP
ORT_SCHEMA_PR
EFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 382

No. Oracle GaussDB Dierence
74 DBMS_STATS.IMP
ORT_SCHEMA_ST
ATS
DBE_STATS.IMPOR
T_SCHEMA_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In the stattab
table, the
imported
table-level and
partition-level
statistics are
numrows,
numblocks,
and
relallvisible,
which
correspond to
reltuples,
relpages, and
relallvisible in
the pg_class
and
pg_partition
system
catalogs,
respectively.
The column-
level statistics
of the
imported table
are consistent
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 383

No. Oracle GaussDB Dierence
with those of
the pg_statistic
and
pg_statistic_ext
catalogs.
● Permission:
You must have
the siud
permission on
the stattab
table.
75 DBMS_STATS.IMP
ORT_SYSTEM_STA
TS
Not supported. -
76 DBMS_STATS.IMP
ORT_TABLE_PREF
S
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 384
No. Oracle GaussDB Dierence
77 DBMS_STATS.IMP
ORT_TABLE_STATS
DBE_STATS.IMPOR
T_TABLE_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● In the stattab
table, the
imported
table-level and
partition-level
statistics are
numrows,
numblocks,
and
relallvisible,
which
correspond to
reltuples,
relpages, and
relallvisible in
the pg_class
and
pg_partition
system
catalogs,
respectively.
The column-
level statistics
imported in
cascading
mode are
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 385

No. Oracle GaussDB Dierence
consistent with
those in the
pg_statistic
and
pg_statistic_ext
catalogs.
● Permission:
You must have
the analyze
permission to
query tables
and the siud
permission on
the stattab
table.
78 DBMS_STATS.INTE
RRUPT_ADVISOR_
TASK
Not supported. -
79 DBMS_STATS.LOC
K_PARTITION_STA
TS
DBE_STATS.LOCK_
PARTITION_STATS
In GaussDB,
ownname must
be set to a
schema name.
80 DBMS_STATS.LOC
K_SCHEMA_STATS
DBE_STATS.LOCK_
SCHEMA_STATS
In GaussDB,
ownname must
be set to a
schema name.
81 DBMS_STATS.LOC
K_TABLE_STATS
DBE_STATS.LOCK_
TABLE_STATS
In GaussDB,
ownname must
be set to a
schema name.
82 DBMS_STATS.MER
GE_COL_USAGE
Not supported. -
83 DBMS_STATS.PRE
PARE_COLUMN_V
ALUES
Not supported. -
84 DBMS_STATS.PRE
PARE_COLUMN_V
ALUES_ROWID
Not supported. -
85 DBMS_STATS.PUB
LISH_PENDING_S
TATS
Not supported. -
86 DBMS_STATS.PUR
GE_STATS
DBE_STATS.PURGE
_STATS
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 386

No. Oracle GaussDB Dierence
87 DBMS_STATS.REM
AP_STAT_TABLE
Not supported. -
88 DBMS_STATS.REP
ORT_ADVISOR_TA
SK
Not supported. -
89 DBMS_STATS.REP
ORT_COL_USAGE
Not supported. -
90 DBMS_STATS.REP
ORT_GATHER_AU
TO_STATS
Not supported. -
91 DBMS_STATS.REP
ORT_GATHER_DA
TABASE_STATS
Not supported. -
92 DBMS_STATS.REP
ORT_GATHER_DIC
TIONARY_STATS
Not supported. -
93 DBMS_STATS.REP
ORT_GATHER_FIX
ED_OBJ_STATS
Not supported. -
94 DBMS_STATS.REP
ORT_GATHER_SC
HEMA_STATS
Not supported. -
95 DBMS_STATS.REP
ORT_STATS_OPER
ATIONS
Not supported. -
96 DBMS_STATS.RES
ET_ADVISOR_TAS
K
Not supported. -
97 DBMS_STATS.RES
ET_COL_USAGE
Not supported. -
98 DBMS_STATS.RES
ET_GLOBAL_PREF
_DEFAULTS
Not supported. -
99 DBMS_STATS.RES
ET_PARAM_DEFA
ULTS
Not supported. -
100 DBMS_STATS.RES
TORE_DICTIONAR
Y_STATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 387

No. Oracle GaussDB Dierence
101 DBMS_STATS.RES
TORE_FIXED_OBJE
CTS_STATS
Not supported. -
102 DBMS_STATS.RES
TORE_SCHEMA_S
TATS
DBE_STATS.RESTO
RE_SCHEMA_STAT
S
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
103
DBMS_STATS.RES
TORE_SYSTEM_ST
ATS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 388

No. Oracle GaussDB Dierence
104 DBMS_STATS.RES
TORE_TABLE_STAT
S
DBE_STATS.RESTO
RE_TABLE_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
105
DBMS_STATS.RES
UME_ADVISOR_T
ASK
Not supported. -
106 DBMS_STATS.SCRI
PT_ADVISOR_TAS
K
Not supported. -
107 DBMS_STATS.SEE
D_COL_USAGE
Not supported. -
108 DBMS_STATS.SET_
ADVISOR_TASK_P
ARAMETER
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 389

No. Oracle GaussDB Dierence
109 DBMS_STATS.SET_
COLUMN_STATS
DBE_STATS.SET_C
OLUMN_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
110
DBMS_STATS.SET_
DATABASE_PREFS
Not supported. -
111 DBMS_STATS.SET_
GLOBAL_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 390
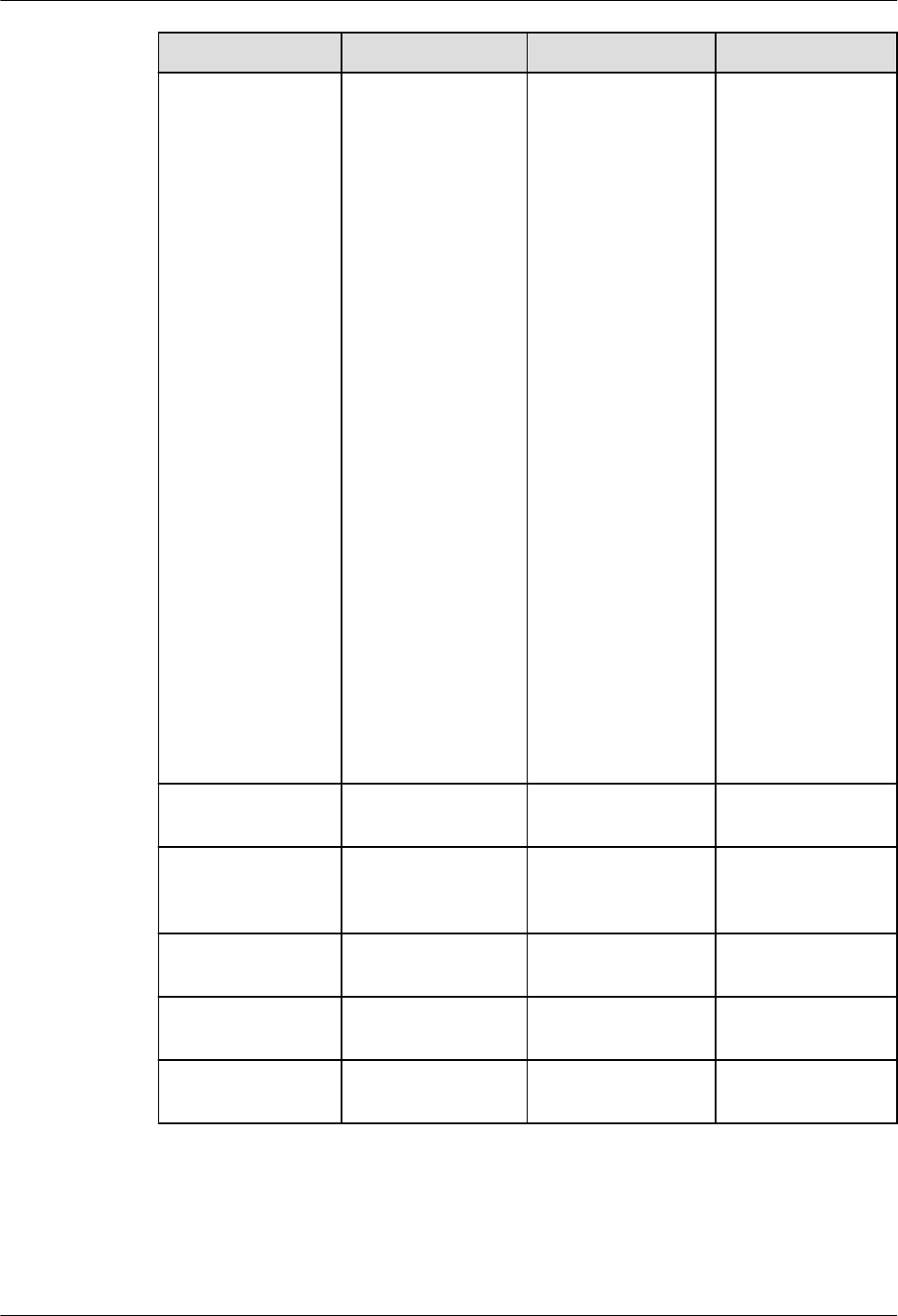
No. Oracle GaussDB Dierence
112 DBMS_STATS.SET_
INDEX_STATS
DBE_STATS.SET_IN
DEX_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● The
relallvisible
input
parameter is
added to
GaussDB.
113
DBMS_STATS.SET_
PARAM
Not supported. -
114 DBMS_STATS.SET_
PROCESSING_RAT
E
Not supported. -
115 DBMS_STATS.SET_
SCHEMA_PREFS
Not supported. -
116 DBMS_STATS.SET_
SYSTEM_STATS
Not supported. -
117 DBMS_STATS.SET_
TABLE_PREFS
Not supported. -
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 391

No. Oracle GaussDB Dierence
118 DBMS_STATS.SET_
TABLE_STATS
DBE_STATS.SET_TA
BLE_STATS
● In GaussDB,
ownname
must be set to
a schema
name.
● GaussDB
supports only
some input
parameter
functions. For
details, see
"Stored
Procedure >
Advanced
Package >
Secondary
Encapsulation
Interfaces
(Recommende
d) >
DBE_STATS" in
Developer
Guide
.
● The
relallvisible
input
parameter is
added to
GaussDB.
119
DBMS_STATS.SHO
W_EXTENDED_ST
ATS_NAME
Not supported. -
120 DBMS_STATS.TRA
NSFER_STATS
Not supported. -
121 DBMS_STATS.UNL
OCK_PARTITION_
STATS
DBE_STATS.UNLO
CK_PARTITION_ST
ATS
In GaussDB,
ownname must
be set to a
schema name.
122 DBMS_STATS.UNL
OCK_SCHEMA_ST
ATS
DBE_STATS.UNLO
CK_SCHEMA_STAT
S
In GaussDB,
ownname must
be set to a
schema name.
123 DBMS_STATS.UNL
OCK_TABLE_STAT
S
DBE_STATS.UNLO
CK_TABLE_STATS
In GaussDB,
ownname must
be set to a
schema name.
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 392

No. Oracle GaussDB Dierence
124 DBMS_STATS.UPG
RADE_STAT_TABL
E
Not supported. -
Table 7-232 DBMS_XMLGEN compatibility
No. Oracle GaussDB Dierence
1 DBMS_XMLGEN.C
ONVERT
DBE_XMLGEN.CO
NVERT
-
2 DBMS_XMLGEN.N
EWCONTEXT
DBE_XMLGEN.NE
WCONTEXT
-
3 DBMS_XMLGEN.N
EWCONTEXTFRO
MHIERARCHY
DBE_XMLGEN.NE
WCONTEXTFROM
HIERARCHY
● The maximum
depth of
recursive XML
les generated
by GaussDB
cannot exceed
50 million
layers.
● XML les
generated by
the CONNECT
BY statement
in Oracle's
newcontextfro
mhierarchy
method
contain XML
headers.
However, the
directly
constructed
data does not
contain the
XML header. In
GaussDB, the
les contain
XML headers.
4
DBMS_XMLGEN.S
ETCONVERTSPECI
ALCHARS
DBE_XMLGEN.SET
CONVERTSPECIAL
CHARS
-
5 DBMS_XMLGEN.S
ETNULLHANDLIN
G
DBE_XMLGEN.SET
NULLHANDLING
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 393

No. Oracle GaussDB Dierence
6 DBMS_XMLGEN.S
ETROWSETTAG
DBE_XMLGEN.SET
ROWSETTAG
-
7 DBMS_XMLGEN.S
ETROWTAG
DBE_XMLGEN.SET
ROWTAG
-
8 DBMS_XMLGEN.U
SENULLATTRIBUT
EINDICATOR
DBE_XMLGEN.USE
NULLATTRIBUTEI
NDICATOR
-
9 DBMS_XMLGEN.U
SEITEMTAGSFORC
OLL
DBE_XMLGEN.USEI
TEMTAGSFORCOL
L
-
10 DBMS_XMLGEN.G
ETNUMROWSPRO
CESSED
DBE_XMLGEN.GET
NUMROWSPROCE
SSED
-
11 DBMS_XMLGEN.S
ETMAXROWS
DBE_XMLGEN.SET
MAXROWS
-
12 DBMS_XMLGEN.S
ETSKIPROWS
DBE_XMLGEN.SET
SKIPROWS
-
13 DBMS_XMLGEN.R
ESTARTQUERY
DBE_XMLGEN.RES
TARTQUERY
● GaussDB: The
updated data
is invisible
after the
RESTARTQUER
Y method is
called.
● Oracle: The
updated data
is visible after
the
RESTARTQUER
Y method is
called.
14 DBMS_XMLGEN.G
ETXMLTYPE
DBE_XMLGEN.GET
XMLTYPE
-
15 DBMS_XMLGEN.G
ETXML
DBE_XMLGEN.GET
XML
-
16 DBMS_XMLGEN.C
LOSECONTEXT
DBE_XMLGEN.CLO
SECONTEXT
-
GaussDB
Service Overview 7 Compatibility with Oracle
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 394

8 Compatibility with MySQL Databases
8.1 Distributed Instances
8.1.1 MySQL Compatibility in MySQL-Compatible Mode
8.1.1.1 MySQL Compatibility Overview
This document compares the MySQL 5.7 compatibility mode in GaussDB (that is,
when sql_compatibility is set to 'B', b_format_version is set to '5.7', and
b_format_dev_version is set to 's1') with MySQL 5.7. Only compatibility features
added later than GaussDB Kernel 503.0.0 are described. You are advised to view
the specications and restrictions of the features in
Developer Guide
.
GaussDB is compatible with MySQL in terms of data types, SQL functions, and
database objects.
The underlying framework implementation of the GaussDB is dierent from that
of MySQL. Therefore, there are still some dierences between GaussDB and
MySQL.
8.1.1.2 Data Types
The data types of GaussDB are the same as those of MySQL in most function
scenarios, but there are some dierences.
● Unless otherwise specied, the precision, scale, and number of bits of some
data types cannot be dened as oating-point values. You are advised to use
valid integer values.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 395

8.1.1.2.1 Numeric Data Types
Table 8-1 Integer types
No. MySQL GaussDB Dierence
1 BOOL Not fully
compatible
MySQL: The BOOL/BOOLEAN type is
actually mapped to the TINYINT type.
GaussDB: BOOL is supported.
● Valid literal values for the "true" state
include: TRUE, 't', 'true', 'y', 'yes', '1',
'TRUE', true, 'on', and all non-zero
values.
● Valid literal values for the "false" state
include: FALSE, 'f', 'false', 'n', 'no', '0', 0,
'FALSE', false, and 'o'.
TRUE and FALSE are standard expressions,
compatible with SQL statements.
2 BOOLEAN Not fully
compatible
3 TINYINT[(M
)]
[UNSIGNED
]
Supported. For details, see the following note.
4 SMALLINT[(
M)]
[UNSIGNED
]
Supported. For details, see the following note.
5 MEDIUMIN
T[(M)]
[UNSIGNED
]
Supported. MySQL requires 3 bytes to store
MEDIUMINT data.
● The signed range is –8388608 to
+8388607.
● The unsigned range is 0 to +16777215.
GaussDB maps data to the INT type and
requires 4 bytes for storage.
● The signed range is –2147483648 to
+2147483647.
● The unsigned range is 0 to
+4294967295.
For other dierences, see the following
note.
6 INT[(M)]
[UNSIGNED
]
Supported. For details, see the following note.
7 INTEGER[(M
)]
[UNSIGNED
]
Supported. For details, see the following note.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 396

No. MySQL GaussDB Dierence
8 BIGINT[(M)
]
[UNSIGNED
]
Supported. For details, see the following note.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 397

NO TE
● Input formats
● MySQL
For characters such as "asbd", "12dd", and "12 12", the system truncates them or
returns 0 and reports a WARNING message. Data fails to be inserted into a table in
strict mode.
● GaussDB
● For integer types (TINYINT, SMALLINT, MEDIUMINT, INT, INTEGER, and
BIGINT), if the invalid part of a character string is truncated, for example,
"12@3", no message is displayed. Data is successfully inserted into a table.
● If the whole integer is truncated (for example, "@123") or the character
string is empty, 0 is returned and data is successfully inserted into a table.
● Operators
● +, -, and *
GaussDB: When INT, INTEGER, SMALLINT, or BIGINT is used for calculation, a value
of the original type is returned and is not changed to a larger type. If the return
value exceeds the range, an error is reported.
MySQL: The value can be changed to BIGINT for calculation.
● |, &, ^, and ~
GaussDB: The value is calculated in the bits occupied by the type. In GaussDB, ^
indicates the exponentiation operation. If the XOR operator is required, replace it
with #.
MYSQL: The value is changed to a larger type for calculation.
● Type conversion of negative numbers:
GaussDB: The result is 0 in loose mode and an error is reported in strict mode.
MySQL: The most signicant bit is replaced with a numeric bit based on the
corresponding binary value, for example, (-1)::uint4 = 4294967295.
● Other dierences:
The precision of INT[(M)] controls formatted output in MySQL. GaussDB supports only
the syntax but does not support the function.
● Aggregate function:
● variance: indicates the sample variance in GaussDB and the population variance in
MySQL.
● stddev: indicates the sample standard deviation in GaussDB and the overall
standard deviation in MySQL.
● Display width:
● If ZEROFILL is not specied when the width information is specied for an integer
column, the width information is not displayed in the table structure description.
● When the INSERT statement is used to insert a column of the character type,
GaussDB pads 0s before inserting the column.
● The JOIN USING statement involves type derivation. In MySQL, the rst table
column is used by default. In GaussDB, if the result is of the signed type, the width
information is invalid. Otherwise, the width of the rst table column is used.
● For GREATEST/LEAST, IFNULL/IF, and CASE WHEN/DECODE, MySQL does not pad
0s. In GaussDB, 0s are padded when the type and width information is consistent.
● MySQL supports this function when it is used as the input or output parameter or
return value of a function or stored procedure. GaussDB neither reports syntax
errors nor supports this function.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 398

Table 8-2 Arbitrary precision types
No. MySQL GaussDB Dierence
1 DECIMAL[(
M[,D])]
Supported. ● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Input format: No error is reported when
all input parameters of a character string
(for example, '@123') are truncated. An
error is reported only when it is partially
truncated, for example, '12@3'.
2 NUMERIC[(
M[,D])]
Supported.
3 DEC[(M[,D])
]
Supported.
4 FIXED[(M[,D
])]
Not
supported
-
Table 8-3 Floating-point types
No.
MySQL GaussDB Dierence
1 FLOAT[(M,D
)]
Supported. ● Partitioned table: The FLOAT data type
does not support partitioned tables with
the key partitioning policy.
● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 399

No. MySQL GaussDB Dierence
2 FLOAT(p) Supported. ● Partitioned table: The FLOAT data type
does not support partitioned tables with
the key partitioning policy.
● Operator: The ^ operator is used for the
numeric types, which is dierent from
that in MySQL. In GaussDB, the ^
operator is used for exponential
calculation.
● Value range: When the precision p is
dened, only valid integer data types are
supported.
● Output format: The precision M and
scale D support only integers and do not
support oating-point values.
● An ERROR message is reported for
invalid input parameters. No WARNING
message is reported in loose mode (that
is, sql_mode is set to '').
3 DOUBLE[(M
,D)]
Supported. ● Partitioned table: The DOUBLE data type
does not support partitioned tables with
the key partitioning policy.
● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
4 DOUBLE
PRECISION[(
M,D)]
Supported. ● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 400

No. MySQL GaussDB Dierence
5 REAL[(M,D)
]
Supported. ● Partitioned table: The REAL data type
does not support partitioned tables with
the key partitioning policy.
● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 401

Table 8-4 Sequential integers
No. MySQL GaussDB Dierence
1 SERIAL Not fully
compatible
For details about SERIAL, see section
"Numeric Data Types" in
GaussDB
Developer Guide
.
The dierences in specications are as
follows:
CREATE TABLE test(f1 serial, f2 CHAR(20));
● The SERIAL of MySQL is mapped to
BIGINT(20) UNSIGNED NOT NULL
AUTO_INCREMENT UNIQUE, and the
SERIAL of GaussDB is mapped to
INTEGER NOT NULL DEFAULT
nextval('test_f1_seq'::regclass). For
example:
-- Denition of MySQL SERIAL:
mysql> SHOW CREATE TABLE test\G
*************************** 1. row ***************************
Table: test
Create Table: CREATE TABLE `test` (
`f1` bigint(20) unsigned NOT NULL
AUTO_INCREMENT,
`f2` char(20) DEFAULT NULL,
UNIQUE KEY `f1` (`f1`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8
1 row in set (0.00 sec)
-- Denition of GaussDB SERIAL
gaussdb=# \d+ test
Table "public.test"
Column | Type |
Modiers | Storage | Stats target |
Description
--------+---------------
+---------------------------------------------------
+----------+--------------+-------------
f1 | integer | not null default
nextval('test_f1_seq'::regclass) | plain | |
f2 | character(20)
| | extended
| |
Has OIDs: no
Options: orientation=row, compression=no,
storage_type=USTORE
● The default values of the SERIAL type in
the INSERT scenario are dierent. For
example:
-- The inserted default value of the SERIAL type in
MySQL
mysql> INSERT INTO test VALUES(DEFAULT, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> INSERT INTO test VALUES(10, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> INSERT INTO test VALUES(DEFAULT, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+----+------+
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 402

No. MySQL GaussDB Dierence
| f1 | f2 |
+----+------+
| 1 | aaaa |
| 10 | aaaa |
| 11 | aaaa |
+----+------+
3 rows in set (0.00 sec)
-- The inserted default value of the SERIAL type in
GaussDB
gaussdb=# INSERT INTO test VALUES(DEFAULT,
'aaaa');
INSERT 0 1
gaussdb=# INSERT INTO test VALUES(10, 'aaaa');
INSERT 0 1
gaussdb=# INSERT INTO test VALUES(DEFAULT,
'aaaa');
INSERT 0 1
gaussdb=# SELECT * FROM test;
f1 | f2
----+----------------------
1 | aaaa
2 | aaaa
10 | aaaa
(3 rows)
● The reference columns of the SERIAL
type in the REPLACE scenario are
dierent. For details about the GaussDB
reference columns, see section
"REPLACE" in
GaussDB Developer Guide
.
For example:
-- The inserted reference column value of the SERIAL
type in MySQL
mysql> REPLACE INTO test VALUES(f1, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> REPLACE INTO test VALUES(f1, 'bbbb');
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+----+------+
| f1 | f2 |
+----+------+
| 1 | aaaa |
| 2 | bbbb |
+----+------+
2 rows in set (0.00 sec)
-- The inserted reference column value of the SERIAL
type in GaussDB
gaussdb=# REPLACE INTO test VALUES(f1, 'aaaa');
REPLACE 0 1
gaussdb=# REPLACE INTO test VALUES(f1, 'bbbb');
REPLACE 0 1
gaussdb=# SELECT * FROM test;
f1 | f2
----+----------------------
0 | aaaa
0 | bbbb
(2 rows)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 403

8.1.1.2.2 Date and Time Data Types
Table 8-5 Date and time data types
No. MySQL GaussDB Dierence
1 DATE Supported. GaussDB supports the date data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats
– GaussDB supports only the character
type and does not support the
numeric type. For example, the
format can be '2020-01-01' or
'20200101', but cannot be 20200101.
MySQL supports conversion from
numeric input to the date type.
– Separator: GaussDB does not support
the plus sign (+) or colon (:) as the
separator between the year, month,
and day. Other symbols are
supported. MySQL supports all
symbols as separators. Sometimes,
the mixed use of separators is not
supported, which is dierent from
MySQL, such as '2020-01>01' and
'2020/01+01'. You are advised to use
hyphens (-) or slashes (/) as
separators.
– No separator: You are advised to use
the complete format, for example,
'YYYYMMDD' or 'YYMMDD'. The
parsing rules of incomplete formats
(including the ultra-long format) are
dierent from those of MySQL. An
error may be reported or the parsing
result may be inconsistent with that
of MySQL. Therefore, the incomplete
format is not recommended.
● Output formats
If the sql_mode parameter of GaussDB
does not contain 'strict_trans_tables'
(the strict mode is used unless otherwise
dened as the loose mode), the year,
month, and day can be set to 0.
However, the value is converted to a
valid value in the sequence of year,
month, and day. For example, date
'0000-00-10' is converted to 0002-12-10
BC. If the input is invalid or exceeds the
range, a warning message is reported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 404

No. MySQL GaussDB Dierence
and the value 0000-00-00 is returned.
MySQL outputs the date value as it is,
even if the year, month, and day are set
to 0.
● Value ranges
The value range of GaussDB is
4713-01-01 BC to 5874897-12-31 AD.
BC dates are supported. In loose mode,
if the value exceeds the range,
0000-00-00 is returned. In strict mode,
an error is reported. The value range of
MySQL is 0000-00-00 to 9999-12-31. In
loose mode, if the value exceeds the
range, the performance varies in
dierent scenarios. An error may be
reported (for example, in the SELECT
statement) or the value 0000-00-00
may be returned (for example, in the
INSERT statement). As a result, when
the date type is used as the input
parameter of the function, the results
returned by the function are dierent.
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between date types and
returns true or false. For the addition
operation between the date and
interval types, the return result is of
the date type. For the subtraction
operation between the date and
interval types, the return result is of
the date type. For the subtraction
operation between date types, the
return result is of the interval type.
– When the MySQL date type and
other numeric types are calculated,
the date type is converted to the
numeric type, and then the
calculation is performed based on the
numeric type. The result is also of the
numeric type. It is dierent from
GaussDB. For example:
-- MySQL: date+numeric. Convert the date type to
20200101 and add it to 1. The result is 20200102.
mysql> select date'2020-01-01' + 1;
+----------------------+
| date'2020-01-01' + 1 |
+----------------------+
| 20200102 |
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 405
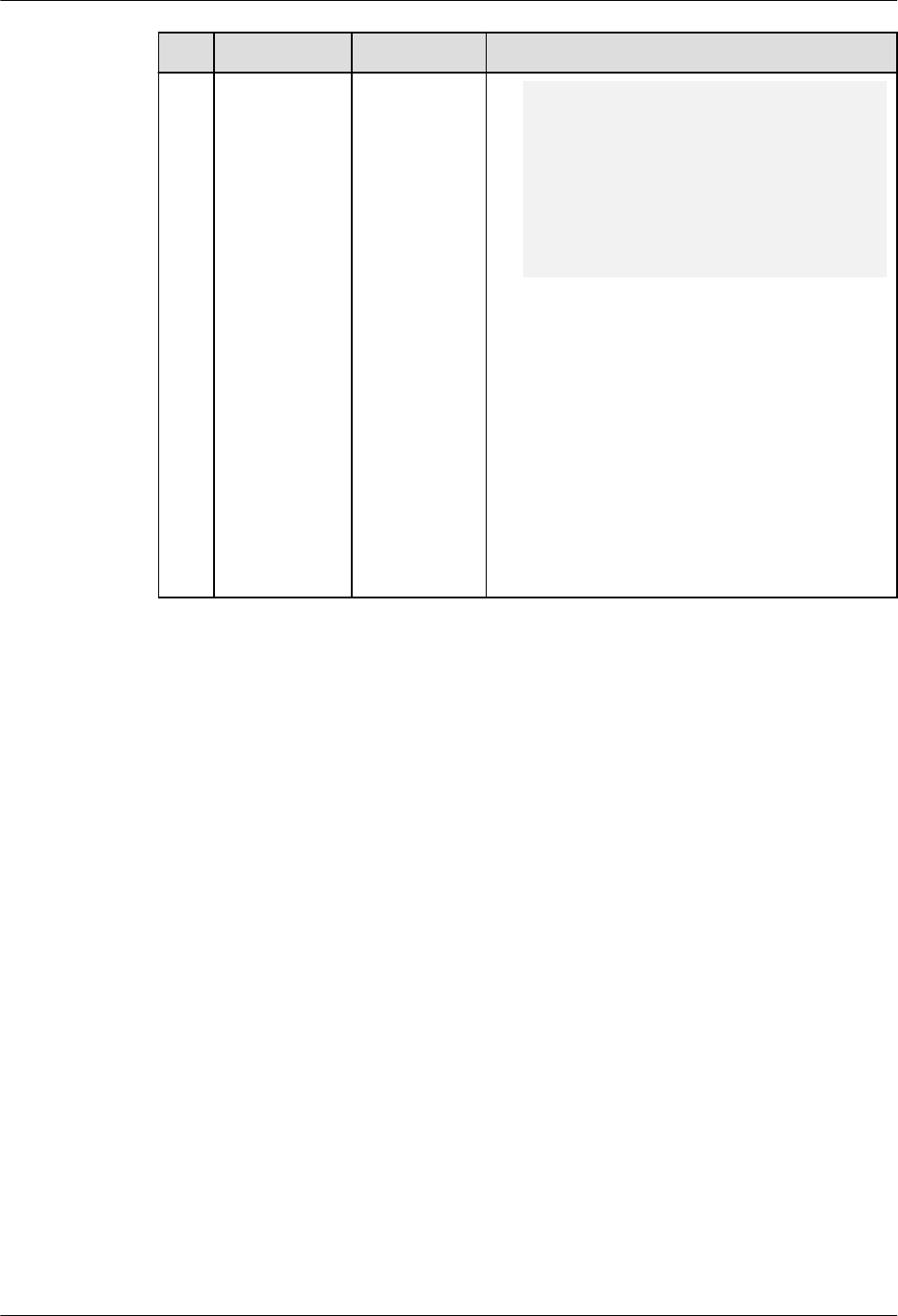
No. MySQL GaussDB Dierence
+----------------------+
1 row in set (0.00 sec)
-- GaussDB: date+numeric. Convert the numeric type
to the interval type (1 day), and then add them up
to obtain a new date.
gaussdb=# select date'2020-01-01' + 1;
?column?
------------
2020-01-02
(1 row)
● Type conversion
Compared with MySQL, GaussDB
supports conversion between the date
type and char(n), nchar(n), datetime, or
timestamp type, but does not support
conversion between the date type and
binary, decimal, JSON, integer, unsigned
integer, or time type. The principles for
determining common types in scenarios
such as collections and complex
expressions are dierent from those in
MySQL. For details, see Data Type
Conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 406

No. MySQL GaussDB Dierence
2 DATETIME[(f
sp)]
Supported. GaussDB supports the datetime data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats
– GaussDB supports only the character
type and does not support the
numeric type. For example,
'2020-01-01 10:20:30.123456' or
'20200101102030.123456' is
supported, but
20200101102030.123456 is not
supported. MySQL supports
conversion from numeric input to the
datetime type.
– Separator: GaussDB does not support
the plus sign (+) or colon (:) as the
separator between the year, month,
and day. Other symbols are
supported. Only colons (:) can be
used as separators between hours,
minutes, and seconds. Sometimes,
the mixed use of separators is not
supported, which is dierent from
MySQL. Therefore, it is not
recommended. MySQL supports all
symbols as separators.
– No separator: The complete format
'YYYYMMDDhhmiss.' is
recommended. The parsing rules of
incomplete formats (including the
ultra-long format) may be dierent
from those of MySQL. An error may
be reported or the parsing result may
be inconsistent with that of MySQL.
Therefore, the incomplete format is
not recommended.
● Output formats
– The format is 'YYYY-MM-DD
hh:mi:ss.', which is the same as
that of MySQL and is not aected by
the DateStyle parameter. However,
for the precision part, if the last
several digits are 0, they are not
displayed in GaussDB but displayed in
MySQL.
– If the sql_mode parameter of
GaussDB does not contain
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 407

No. MySQL GaussDB Dierence
'strict_trans_tables' (the strict mode
is used unless otherwise dened as
the loose mode), the year, month,
and day can be set to 0. However, the
value is converted to a valid value in
the sequence of year, month, and
day. For example, datetime
'0000-00-10 00:00:00' is converted to
0002-12-10 00:00:00 BC. If the input
is invalid or exceeds the range, a
warning message is reported and the
value 0000-00-00 00:00:00 is
returned. MySQL outputs the
datetime value as it is, even if the
year, month, and day are set to 0.
● Value ranges
4713-11-24 00:00:00.000000 BC to
294277-01-09 04:00:54.775806 AD. If
the value is 294277-01-09
04:00:54.775807 AD, innity is
returned. If the value exceeds the range,
GaussDB reports an error in strict mode.
Whether MySQL reports an error
depends on the application scenario.
Generally, no error is reported in the
query scenario. However, an error is
reported when the DML or SQL
statement is executed to change the
value of a table attribute. In loose mode,
GaussDB returns 0000-00-00 00:00:00.
MySQL may report an error, return
0000-00-00 00:00:00, or return null
based on the application scenario. As a
result, the execution result of the
function that uses the datetime type as
the input parameter is dierent from
that of MySQL.
● Precision
The value ranges from 0 to 6. For a
table column, the default value is 0,
which is the same as that in MySQL. In
the datetime[(p)]'str' expression,
GaussDB parses (p) as the precision.
The default value is 6, indicating that
'str' is formatted to the datetime type
based on the precision specied by p.
MySQL does not support the
datetime[(p)]'str' expression.
● Operators
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 408

No. MySQL GaussDB Dierence
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between datetime types and
returns true or false. For the addition
operation between the datetime and
interval types, the return result is of
the datetime type. For the
subtraction operation between the
datetime and interval types, the
return result is of the datetime type.
For the subtraction operation
between datetime types, the return
result is of the interval type.
– When the MySQL datetime type and
other numeric types are calculated,
the datetime type is converted to the
numeric type, and then the
calculation is performed based on the
numeric type. The result is also of the
numeric type. It is dierent from
GaussDB. For example:
-- MySQL: datetime+numeric. Convert the datetime
type to 20201010123456 and add it to 1. The result
is 20201010123457.
mysql> select cast('2020-10-10 12:34:56.123456' as
datetime) + 1;
+----------------------------------------------------+
| cast('2020-10-10 12:34:56.123456' as datetime) + 1
|
+----------------------------------------------------+
| 20201010123457 |
+----------------------------------------------------+
1 row in set (0.00 sec)
-- GaussDB: datetime+numeric. Convert the numeric
type to the interval type (1 day), and then add them
up to obtain the new datetime.
gaussdb=# select cast('2020-10-10 12:34:56.123456'
as datetime) + 1;
?column?
---------------------
2020-10-11 12:34:56
(1 row)
If the calculation result of the datetime
type and numeric type is used as the
input parameter of a function, the result
of the function may be dierent from
that of MySQL.
● Type conversion
Compared with MySQL, GaussDB
supports only conversion between the
datetime type and char(n), varchar(n),
and timestamp types, and conversion
from datetime to date and time types
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 409
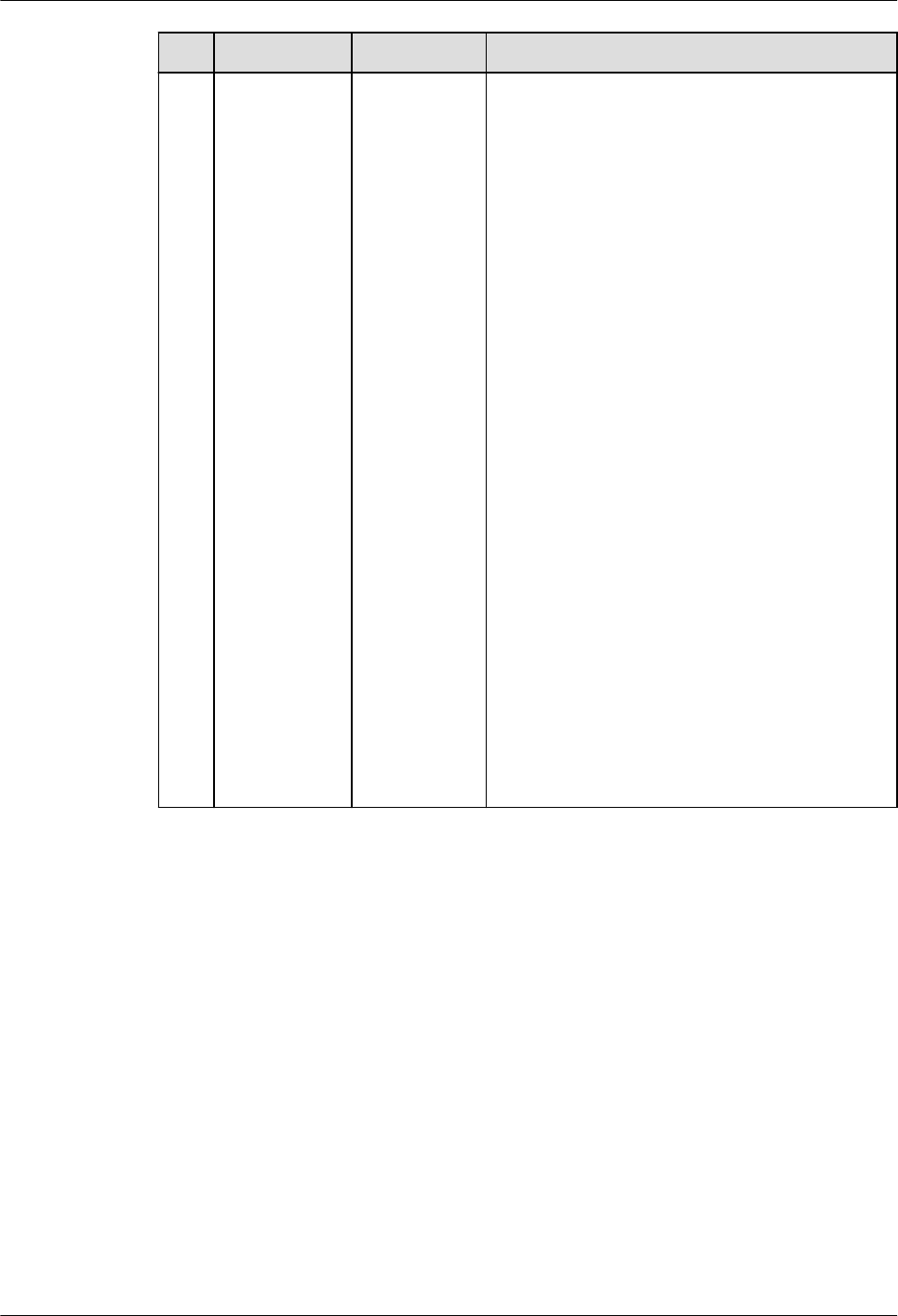
No. MySQL GaussDB Dierence
(only value assignment and explicit
conversion). The conversion between the
datetime type and the binary, decimal,
json, integer, or unsigned integer type is
not supported. The principles for
determining common types in scenarios
such as collections and complex
expressions are dierent from those in
MySQL. For details, see Data Type
Conversion.
● Time zones
In GaussDB, the datetime value can
carry the time zone information (time
zone oset or time zone name), for
example, '2020-01-01 12:34:56.123456
+01:00' or '2020-01-01 2:34:56.123456
CST'. GaussDB converts the time to the
time of the current server time zone.
MySQL 5.7 does not support this
function. MySQL 8.0 and later versions
support this function.
● The table columns of the datetime data
type in GaussDB are actually converted
to the timestamp(p) without time zone.
When you query the table information
or use a tool to export the table
structure, the data type of columns is
timestamp(p) without time zone instead
of datetime. For MySQL, datetime(p) is
displayed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 410

No. MySQL GaussDB Dierence
3 TIMESTAMP[
(fsp)]
Supported. GaussDB supports the timestamp data
type. Compared with MySQL, GaussDB has
the following dierences in specications:
● Input formats
– It supports only the character type
and does not support the numeric
type. For example, '2020-01-01
10:20:30.123456' or
'20200101102030.123456' is
supported, but
20200101102030.123456 is not
supported. MySQL supports
conversion from numeric input to the
timestamp type.
– Separator: It does not support the
plus sign (+) or colon (:) as the
separator between the year, month,
and day. Other symbols are
supported. Only colons (:) can be
used as separators between hours,
minutes, and seconds. Sometimes,
the mixed use of separators is not
supported, which is dierent from
MySQL. Therefore, it is not
recommended. MySQL supports all
symbols as separators.
– No separator: The complete format
'YYYYMMDDhhmiss.' is
recommended. The parsing rules of
incomplete formats (including the
ultra-long format) may be dierent
from those of MySQL. An error may
be reported or the parsing result may
be inconsistent with that of MySQL.
Therefore, the incomplete format is
not recommended.
● Output formats
– The format is 'YYYY-MM-DD
hh:mi:ss.', which is the same as
that of MySQL and is not aected by
the DateStyle parameter. However,
for the precision part, if the last
several digits are 0, they are not
displayed in GaussDB but displayed in
MySQL.
– If the sql_mode parameter of
GaussDB does not contain
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 411

No. MySQL GaussDB Dierence
'strict_trans_tables' (the strict mode
is used unless otherwise dened as
the loose mode), the year, month,
and day can be set to 0. However, the
value is converted to a valid value in
the sequence of year, month, and
day. For example, timestamp
'0000-00-10 00:00:00' is converted to
0002-12-10 00:00:00 BC. If the input
is invalid or exceeds the range, a
warning message is reported and the
value 0000-00-00 00:00:00 is
returned. MySQL outputs the
timestamp value as it is, even if the
year, month, and day are set to 0.
● Value ranges
4713-11-24 00:00:00.000000 BC to
294277-01-09 04:00:54.775806 AD. If
the value is 294277-01-09
04:00:54.775807 AD, innity is
returned. If the value exceeds the range,
GaussDB reports an error in strict mode.
Whether MySQL reports an error
depends on the application scenario.
Generally, no error is reported in the
query scenario. However, an error is
reported when the DML or SQL
statement is executed to change the
value of a table attribute. In loose mode,
GaussDB returns 0000-00-00 00:00:00.
MySQL may report an error, return
0000-00-00 00:00:00, or return null
based on the application scenario. As a
result, the execution result of the
function that uses the timestamp type
as the input parameter is dierent from
that of MySQL.
● Precision
The value ranges from 0 to 6. For a
table column, the default value is 0,
which is the same as that in MySQL. In
the timestamp[(p)] 'str' expression:
– GaussDB parses (p) as the precision.
The default value is 6, indicating that
'str' is formatted to the timestamp
type based on the precision specied
by p.
– The meaning of timestamp 'str' in
MySQL is the same as that in
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 412
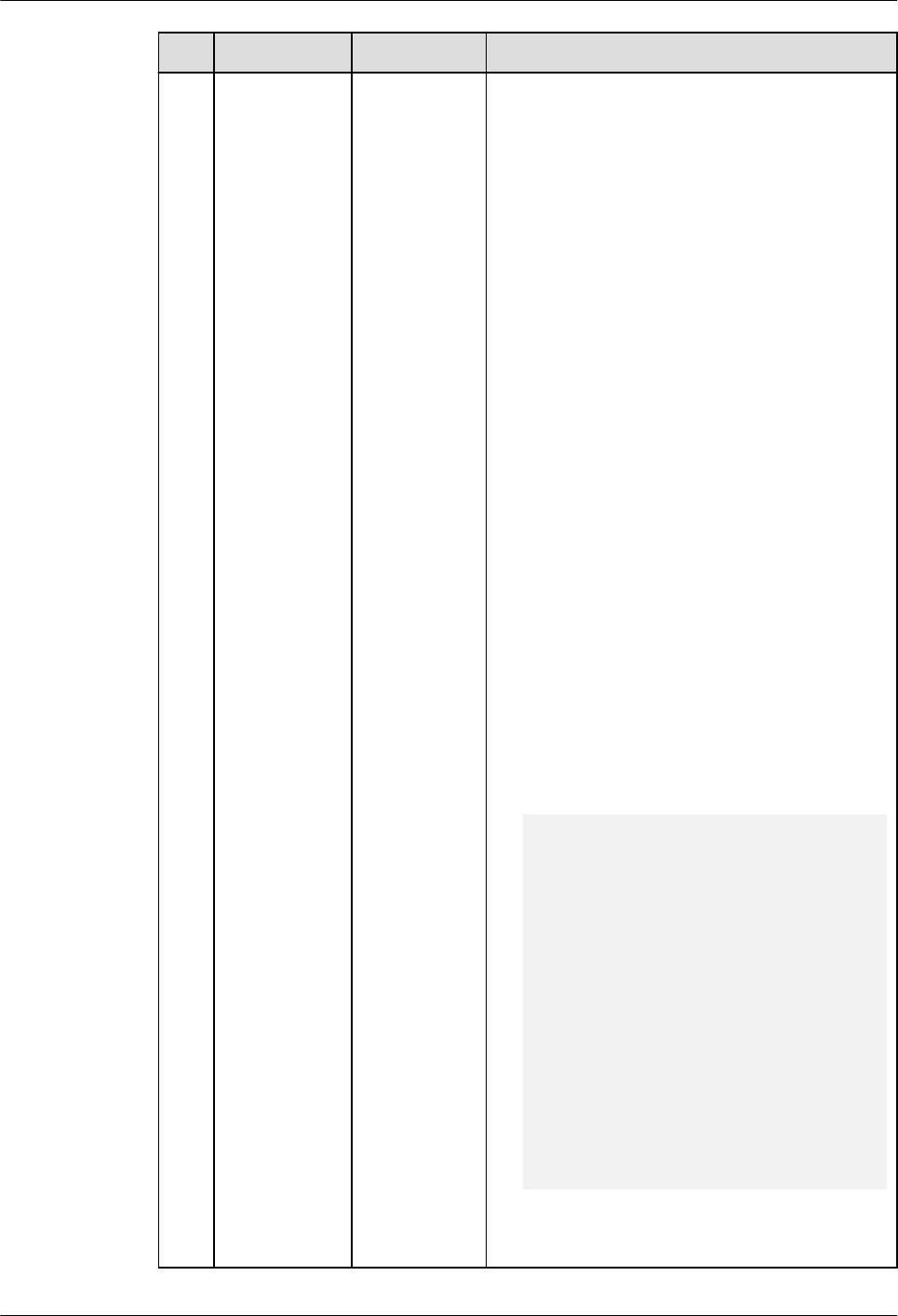
No. MySQL GaussDB Dierence
GaussDB. The default precision is 6.
However, timestamp(p) 'str' is parsed
as a function call. p is used as the
input parameter of the timestamp
function. The result returns a value of
the timestamp type, and 'str' is used
as the alias of the projection column.
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between timestamp types
and returns true or false. For the
addition operation between the
timestamp and interval types, the
return result is of the timestamp
type. For the subtraction operation
between the timestamp and interval
types, the return result is of the
timestamp type. For the subtraction
operation between timestamp types,
the return result is of the interval
type.
– When the MySQL timestamp type
and other numeric types are
calculated, the timestamp type is
converted to the numeric type, and
then the calculation is performed
based on the numeric type. The result
is also of the numeric type. It is
dierent from GaussDB. For example:
-- MySQL: timestamp+numeric. Convert the
timestamp type to 20201010123456.123456 and
add it to 1. The result is 20201010123457.123456.
mysql> select timestamp '2020-10-10
12:34:56.123456' + 1;
+--------------------------------------------+
| timestamp '2020-10-10 12:34:56.123456' + 1 |
+--------------------------------------------+
| 20201010123457.123456 |
+--------------------------------------------+
1 row in set (0.00 sec)
-- GaussDB: timestamp+numeric. Convert the
numeric type to the interval type (1 day), and then
add them up to obtain a new timestamp.
gaussdb=# select timestamp '2020-10-10
12:34:56.123456' + 1;
?column?
----------------------------
2020-10-11 12:34:56.123456
(1 row)
If the calculation result of the
timestamp type and numeric type is
used as the input parameter of a
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 413

No. MySQL GaussDB Dierence
function, the result of the function may
be dierent from that of MySQL.
● Type conversion
Compared with MySQL, GaussDB
supports only conversion between
timestamp and char(n), varchar(n), and
datetime, and conversion from
timestamp to date and time (only value
assignment and explicit conversion). The
conversion between the timestamp type
and the binary, decimal, json, integer, or
unsigned integer type is not supported.
The principles for determining common
types in scenarios such as collections
and complex expressions are dierent
from those in MySQL. For details, see
Data Type Conversion.
● Time zones
In GaussDB, the timestamp value can
carry the time zone information (time
zone oset or time zone name), for
example, '2020-01-01 12:34:56.123456
+01:00' or '2020-01-01 2:34:56.123456
CST'. GaussDB converts the time to the
time of the current server time zone. If
the time zone of the server is changed,
the timestamp value is converted to the
timestamp of the new time zone.
MySQL 5.7 does not support this
function. MySQL 8.0 and later versions
support this function.
● The table columns of the timestamp
data type in GaussDB are actually
converted to the timestamp(p) with
time zone. When you query the table
information or use a tool to export the
table structure, the data type of
columns is timestamp(p) with time zone
instead of timestamp. For MySQL,
timestamp(p) is displayed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 414

No. MySQL GaussDB Dierence
4 TIME[(fsp)] Supported. GaussDB supports the time data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats
– It supports only the character type
and does not support the numeric
type. For example, '1 10:20:30' or
'102030' is supported, but 102030 is
not supported. MySQL supports
conversion from numeric input to the
time type.
– Separator: GaussDB supports only
colons (:) as separators between
hours, minutes, and seconds. MySQL
supports all symbols as separators.
– No separator: The complete format
'hhmiss.' is recommended. The
parsing rules of incomplete formats
(including the ultra-long format) may
be dierent from those of MySQL. An
error may be reported or the parsing
result may be inconsistent with that
of MySQL. Therefore, the incomplete
format is not recommended.
– When a negative value is entered for
minute, second, or precision,
GaussDB may ignore the rst part of
the negative value, which is parsed as
0. For example, '00:00:-10' is parsed
as '00:00:00'. An error may also be
reported. For example, if
'00:00:-10000' is parsed, an error will
be reported. The result depends on
the range of the input value.
However, MySQL reports an error in
both cases.
● Output formats
The format is hh:mi:ss., which is the
same as that of MySQL. However, for
the precision part, if the last several
digits are 0, they are not displayed in
GaussDB but displayed in MySQL.
● Value ranges
–838:59:59.000000 to 838:59:59.000000,
which is the same as that of MySQL. In
GaussDB loose mode, if a value exceeds
the range, the nearest boundary value –
838:59:59 or 838:59:59 is returned,
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 415
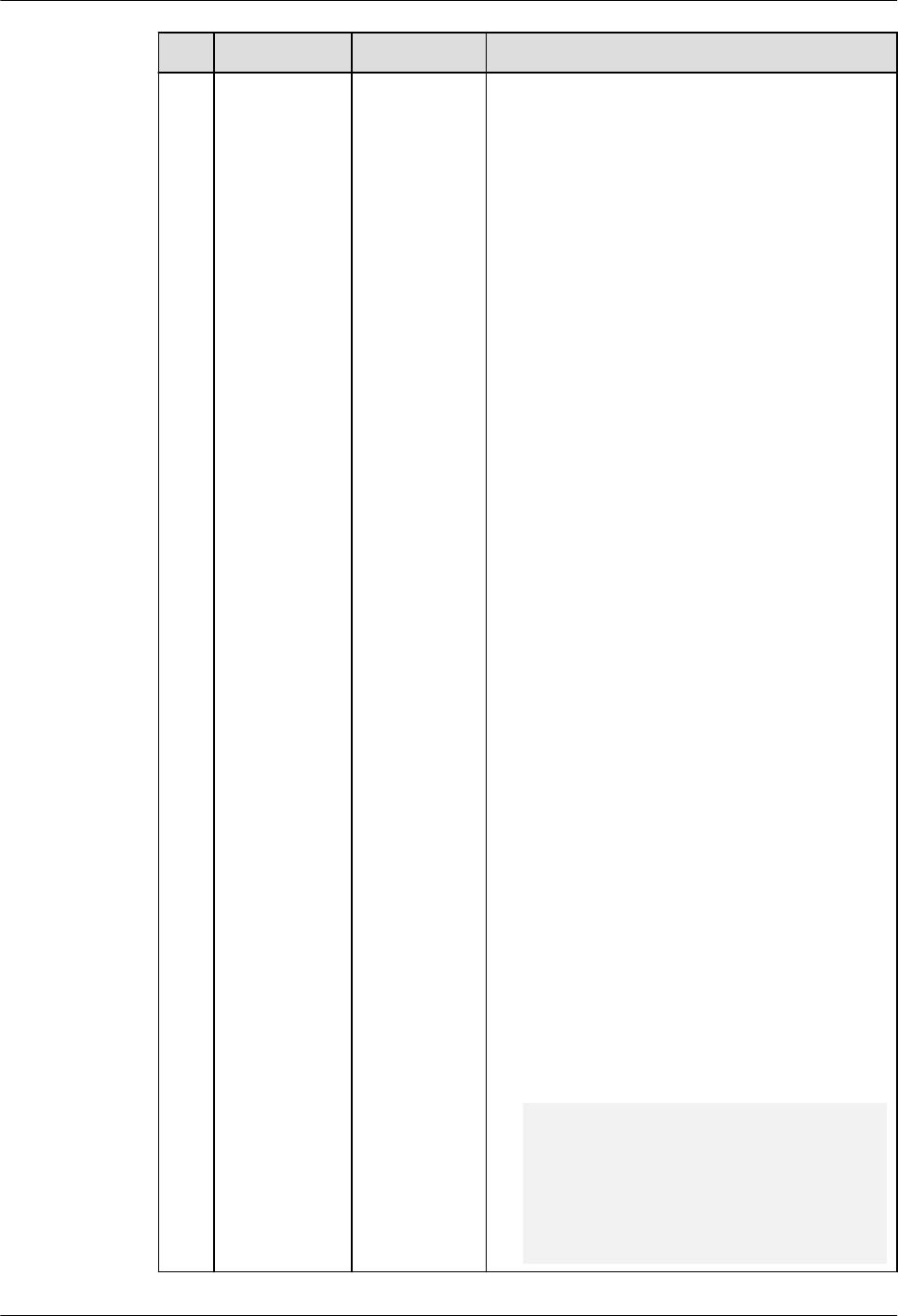
No. MySQL GaussDB Dierence
regardless of the query or DML
operations such as insert and update. In
MySQL, an error is reported during
query, or the nearest boundary value is
returned after a DML operation. As a
result, when the time type is used as the
input parameter of the function, the
results returned by the function are
dierent.
● Precision
The value ranges from 0 to 6. For a
table column, the default value is 0,
which is the same as that in MySQL. In
the time(p) 'str' expression, GaussDB
parses (p) as the precision. The default
value is 6, indicating that 'str' is
formatted to the time type based on the
precision specied by p. MySQL parses it
as a time function, p is an input
parameter, and 'str' is the alias of the
projection column.
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between time types and
returns true or false. For the addition
operation between the time and
interval types, the return result is of
the time type. For the subtraction
operation between the time and
interval types, the return result is of
the time type. For the subtraction
operation between time types, the
return result is of the interval type.
– When the MySQL time type and
other numeric types are calculated,
the time type is converted to the
numeric type, and then the
calculation is performed based on the
numeric type. The result is also of the
numeric type. It is dierent from
GaussDB. For example:
-- MySQL: time+numeric. Convert the time type to
123456 and add it to 1. The result is 123457.
mysql> select time '12:34:56' + 1;
+---------------------+
| time '12:34:56' + 1 |
+---------------------+
| 123457 |
+---------------------+
1 row in set (0.00 sec)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 416

No. MySQL GaussDB Dierence
-- GaussDB: time+numeric. Convert the numeric type
to the interval type (1 day), and then add them up
to obtain the new time. Because 24 hours are added,
the obtained time is still 12:34:56.
gaussdb=# select time '12:34:56' + 1;
?column?
----------
12:34:56
(1 row)
If the calculation result of the time type
and numeric type is used as the input
parameter of a function, the result of
the function may be dierent from that
of MySQL.
● Type conversion
Compared with MySQL, GaussDB
supports only conversion between the
time type and char(n) or nchar(n) type,
and conversion between the datetime or
timestamp type and time type. The
conversion between the time type and
binary, decimal, date, JSON, integer, or
unsigned integer type is not supported.
The principles for determining common
types in scenarios such as collections
and complex expressions are dierent
from those in MySQL. For details, see
Data Type Conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 417

No. MySQL GaussDB Dierence
5 YEAR[(4)] Supported. GaussDB supports the year data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between year types and
returns true or false.
– GaussDB supports only the arithmetic
operators + and - between the year
and int4 types and returns integer
values. MySQL returns unsigned
integer values.
● Type conversion
Compared with MySQL, GaussDB
supports only the conversion between
the year type and int4 type, and
supports only the conversion from the
int4, varchar, numeric, date, time,
timestamp, or timestamptz type to the
year type. The principles for determining
common types in scenarios such as
collections and complex expressions are
dierent from those in MySQL. For
details, see Data Type Conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 418

No. MySQL GaussDB Dierence
6 INTERVAL Supported. GaussDB supports the INTERVAL data type,
but INTERVAL is an expression in MySQL.
The dierences are as follows:
● The date input of the character string
type cannot be used as an operation, for
example, select '2023-01-01' + interval 1
day.
● In the INTERVAL expr unit syntax, expr
cannot be a negative integer or oating-
point number, for example, select
date'2023-01-01' + interval -1 day.
● In the INTERVAL expr unit syntax, expr
cannot be the input of an operation
expression, for example, select
date'2023-01-01' + interval 4/2 day.
● When the INTERVAL expression is used
for calculation, the return value is of the
datetime type. For MySQL, the return
value is of the datetime or date type.
The calculation logic is the same as that
of GaussDB but dierent from that of
MySQL.
● In the INTERVAL expr unit syntax, the
value range of expr varies with the unit.
The maximum value range is [–
2147483648, 2147483647]. If the value
exceeds the range, an error is reported
in strict mode, and a warning is reported
in loose mode and 0 is returned.
● In the INTERVAL expr unit syntax, if the
number of columns specied by expr is
greater than the expected number of
columns in unit, an error is reported in
strict mode, and a warning is reported in
loose mode and 0 is returned. For
example, if the value of unit is
DAY_HOUR, the expected number of
columns is 2. If the value of expr is
'1-2-3', the expected number of columns
is 3.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 419

8.1.1.2.3 String Data Types
Table 8-6 String data types
No. MySQL GaussDB Dierence
1 CHAR[(M)] Supported ● Input format
– The length of parameters and return
values of GaussDB user-dened
functions cannot be veried. The
length of stored procedure
parameters cannot be veried. In
addition, correct spaces cannot be
supplemented when
PAD_CHAR_TO_FULL_LENGTH is
enabled. However, MySQL supports
these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Syntax
The CAST(expr as char) syntax of
GaussDB cannot convert the input
string to the corresponding type based
on the string length. It can only be
converted to the varchar type. CAST(''
as char) and CAST('' as char(0)) cannot
convert an empty string to the char(0)
type. MySQL supports conversion to the
corresponding type by length.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 420
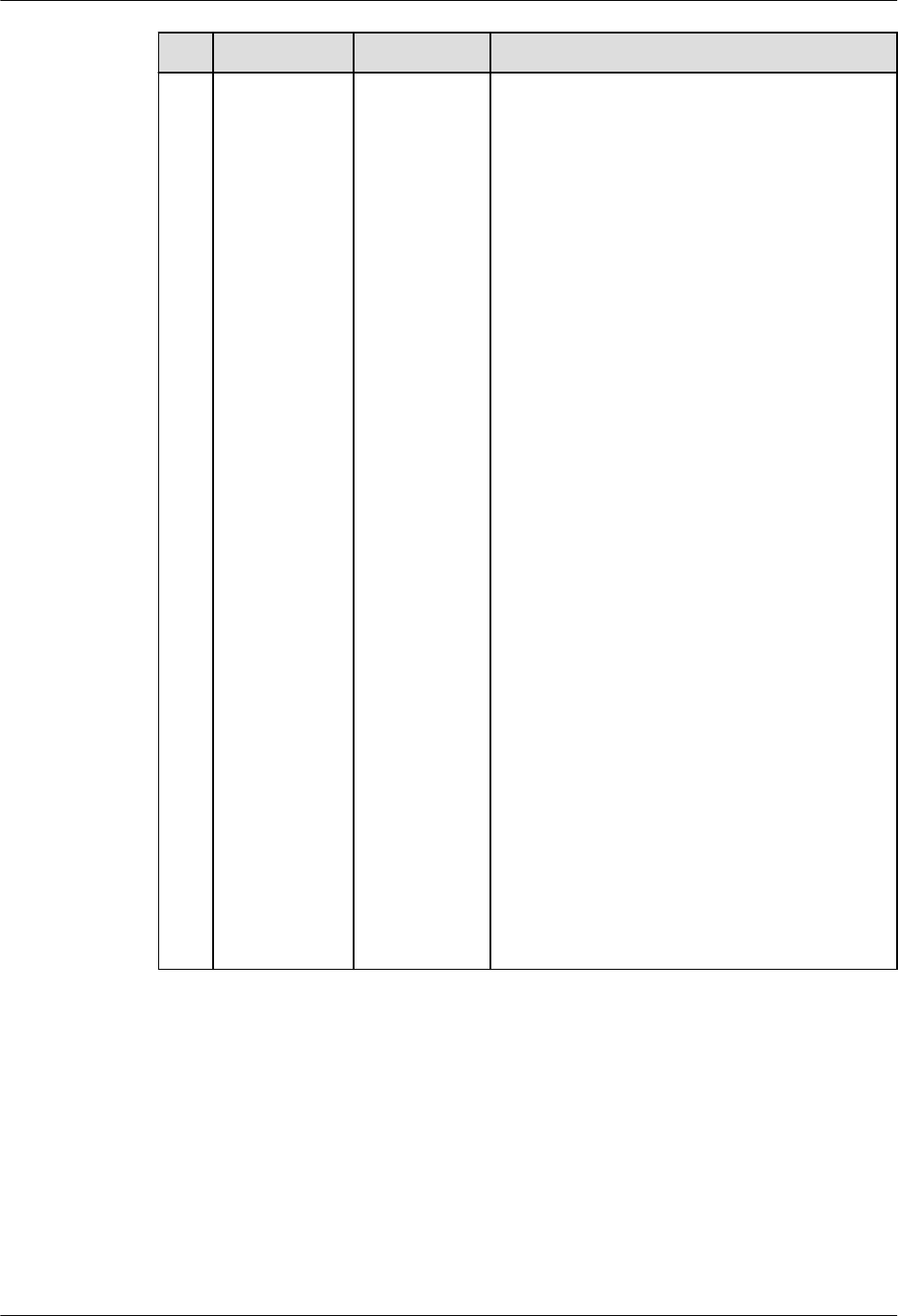
No. MySQL GaussDB Dierence
2 VARCHAR(M
)
Supported ● Input format
– The length of parameters and return
values of GaussDB user-dened
functions cannot be veried. The
length of stored procedure
parameters cannot be veried.
However, MySQL supports these
functions.
– The length of temporary variables in
GaussDB user-dened functions and
stored procedures can be veried,
and an error or truncation alarm is
reported in strict or loose mode.
However, MySQL does not support
these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 421
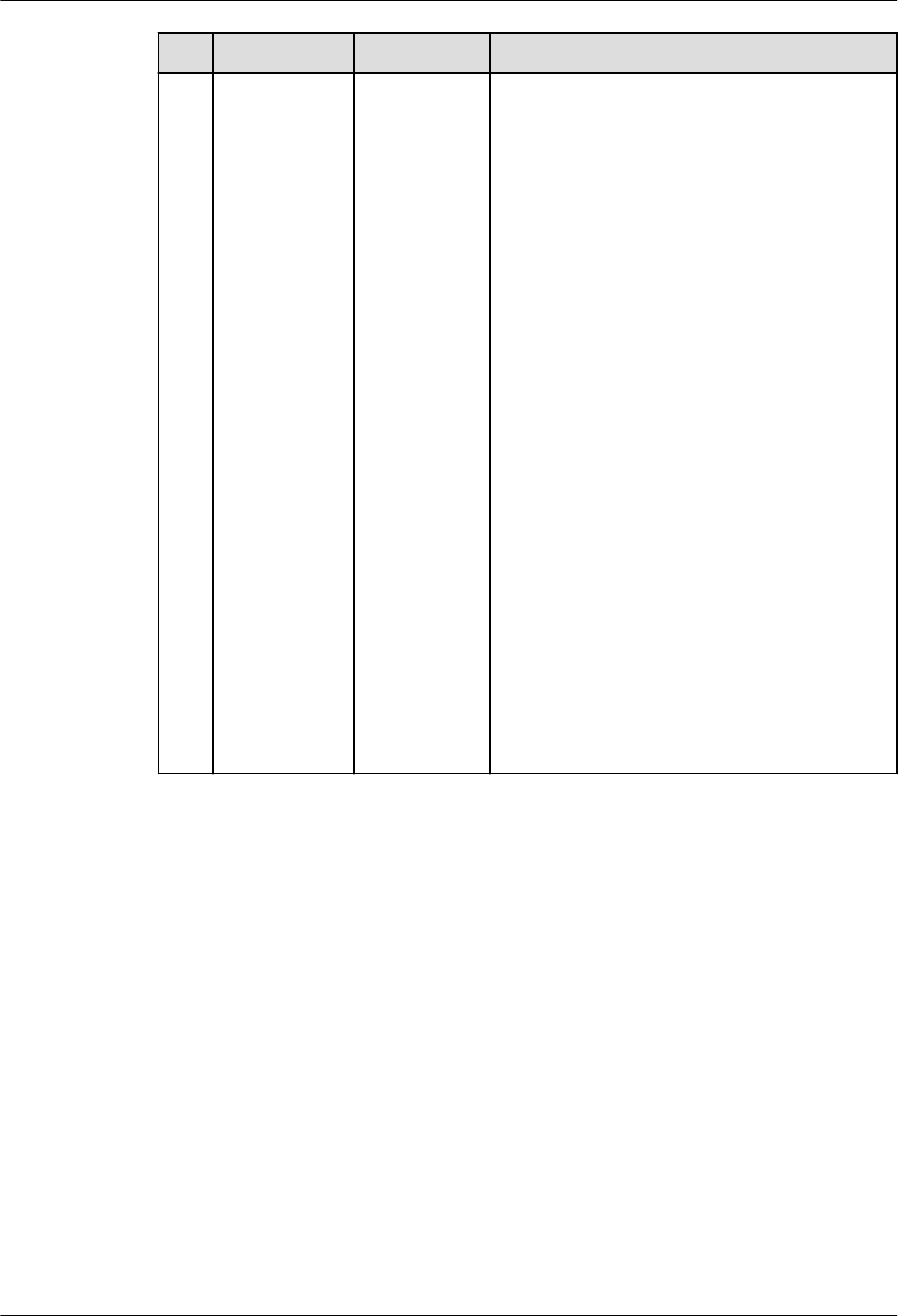
No. MySQL GaussDB Dierence
3 TINYTEXT Supported ● Input format
– The length limit in GaussDB is 1 GB,
not 255 bytes. If the length exceeds
the limit, no error or truncation
alarm is reported in strict or loose
mode. However, MySQL supports
these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 422
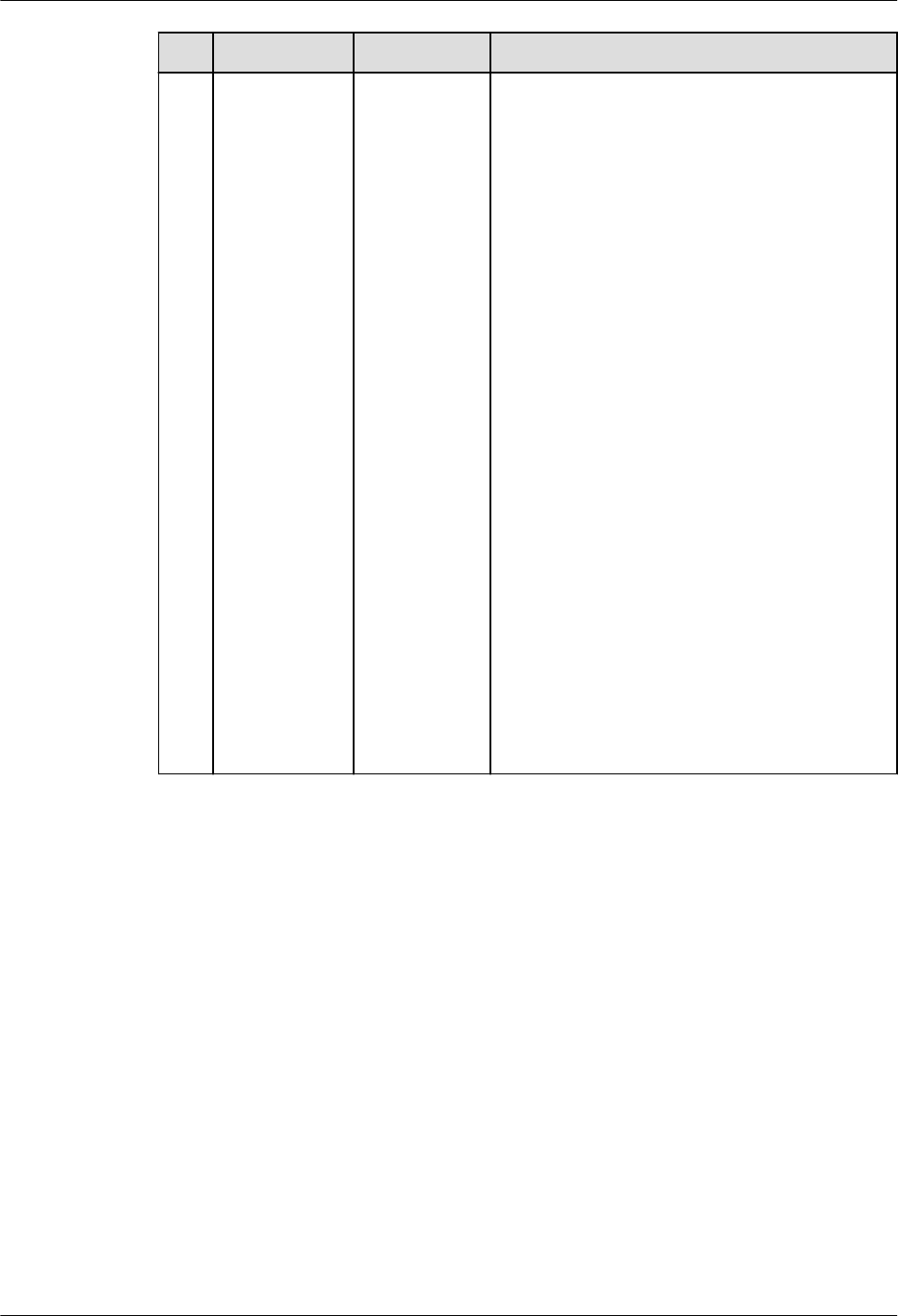
No. MySQL GaussDB Dierence
4 TEXT Supported ● Input format
– The length limit in GaussDB is 1 GB,
not 65535 bytes. If the length
exceeds the limit, no error or
truncation alarm is reported in strict
or loose mode. However, MySQL
supports these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 423

No. MySQL GaussDB Dierence
5 MEDIUMTEX
T
Supported ● Input format
– The length limit in GaussDB is 1 GB,
not 16777215 bytes. If the length
exceeds the limit, no error or
truncation alarm is reported in strict
or loose mode. However, MySQL
supports these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 424

No. MySQL GaussDB Dierence
6 LONGTEXT Supported ● Input format
– GaussDB supports a maximum of 1
GB, and MySQL supports a
maximum of 4 GB minus 1 byte.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
7
ENUM('value
1','value2',...)
Not
supported
-
8 SET('value1','
value2',...)
Not
supported
-
8.1.1.2.4 Binary Data Types
Table 8-7 Binary data types
No.
MySQL GaussDB Dierence
1 BINARY[(M)] Not
supported
-
2 VARBINARY(
M)
Not
supported
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 425

No. MySQL GaussDB Dierence
3 TINYBLOB Supported ● Value range: The length limit is 1 GB,
not 255 bytes. If the length exceeds the
limit, no error or truncation alarm is
reported in strict or loose mode.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
4 BLOB Supported ● Value range: The length limit is 1 GB,
not 65535 bytes. If the length exceeds
the limit, no error or truncation alarm is
reported in strict or loose mode.
However, MySQL supports these
functions.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
5 MEDIUMBLO
B
Supported ● Value range: The length limit is 1 GB,
not 16777215 bytes. If the length
exceeds the limit, no error or truncation
alarm is reported in strict or loose
mode. However, MySQL supports these
functions.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 426

No. MySQL GaussDB Dierence
6 LONGBLOB Supported ● Value range: The upper limit is 1 GB.
For details about the range, see the
centralized and distributed
specications of the bytea data type.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
7 BIT[(M)] Not
supported
-
8.1.1.2.5 JSON Data Type
Table 8-8 JSON data type
No.
MySQL GaussDB
1 JSON Not fully compatible
8.1.1.2.6 Attributes Supported by Data Types
Table 8-9 Attributes supported by data types
No.
MySQL GaussDB
1 NULL Supported
2 NOT NULL Supported
3 DEFAULT Supported
4 ON UPDATE Supported
5 PRIMARY KEY Supported
6 CHARACTER SET name Supported
7 COLLATE name Supported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 427

8.1.1.2.7 Data Type Conversion
Conversion between dierent data types is supported. Data type conversion is
involved in the following scenarios:
● The data types of operands of operators (such as comparison and arithmetic
operators) are inconsistent. It is commonly used for comparison operations in
query conditions or join conditions.
● The data types of arguments and parameters are inconsistent when a
function is called.
● The data types of target columns to be updated by DML statements
(including INSERT, UPDATE, MERGE, and REPLACE) and the dened column
types are inconsistent.
● Explicit type conversion: cast(expr as datatype), which converts an expression
to a data type.
● After the target data type of the nal projection column is determined by set
operations (UNION, MINUS, EXCEPT, and INTERSECT), the type of the
projection column in each SELECT statement is inconsistent with the target
data type.
● In other expression calculation scenarios, the target data type used for
comparison or nal result is determined based on the data type of dierent
expressions.
– DECODE
– CASE WHEN
– lexpr [ NOT ] IN (expr_list)
– BETWEEN AND
– JOIN USING(a,b)
– GREATEST and LEAST
– NVL and COALESCE
GaussDB and MySQL have dierent rules for data type conversion and target data
types. The following examples show the dierences between the two processing
modes:
-- MySQL: The execution result of IN is 0, indicating false. According to the rule, '1970-01-01' is compared
with the expressions in the list in sequence. The results are all 0s. Therefore, the nal result is 0.
mysql> select '1970-01-01' in ('1970-01-02', 1, '1970-01-02');
+-------------------------------------------------+
| '1970-01-01' in ('1970-01-02', 1, '1970-01-02') |
+-------------------------------------------------+
| 0 |
+-------------------------------------------------+
-- GaussDB: The execution result of IN is true, which is opposite to the MySQL result. The common type
selected based on the rule is int. Therefore, the left expression '1970-01-01' is converted to the int type and
compared with the value after the expression in the list is converted to the int type.
-- When '1970-01-01' and '1970-01-02' are converted to the int type, the values are 1970. (In MySQL-
compatible mode, invalid characters and the following content are ignored during conversion, and the
previous part is converted to the int type.) The comparison result is equal. Therefore, the returned result is
true.
gaussdb=# select '1970-01-01' in ('1970-01-02', 1::int, '1970-01-02') as result;
result
--------
t
(1 row)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 428

1. Dierences in data type conversion rules:
● The GaussDB clearly denes the conversion rules between dierent data
types.
– Whether to support conversion: Conversion is supported only when the
conversion path of two types is dened in the pg_cast system catalog.
– Conversion scenarios: conversion in any scenario, conversion only in CAST
expressions, and conversion only during value assignment. In scenarios
that are not supported, data type conversion cannot be performed even if
the conversion path is dened.
● MySQL supports conversion between any two data types.
Due to the preceding dierences, when MySQL-based applications are migrated to
GaussDB, an error may be reported because the SQL statement does not support
the conversion between dierent data types. In the scenario where conversion is
supported, dierent conversion rules result in dierent execution results of SQL
statements.
You are advised to use the same data type in SQL statements for comparison or
value assignment to avoid unexpected results or performance loss caused by data
type conversion.
2. Dierences in target data type selection rules:
In some scenarios, the data type to be compared or returned can be determined
only after the types of multiple expressions are considered. For example, in the
UNION operation, projection columns at the same position in dierent SELECT
statements are of dierent data types. The nal data type of the query result
needs to be determined based on the data type of the projection columns in each
SELECT statement.
GaussDB and MySQL have dierent rules for determining the target data types.
● GaussDB rules:
– If the operand types of operators are inconsistent, the operand types are
not converted to the target type before calculation. Instead, operators of
two data types are directly registered, and two types of processing rules
are dened during operator processing. In this mode, implicit type
conversion does not exist, but the customized processing rule implies the
conversion operation.
– Rules for determining the target data type in the set operation and
expression scenarios:
▪ If all types are the same, it is the target type.
▪ If the two data types are dierent, check whether the data types are
of the same type, such as the numeric type, character type, and date
and time type. If they do not belong to the same type, the target
type cannot be determined. In this case, an error is reported during
SQL statement execution.
▪ For data types with the same category attribute (dened in the
pg_type system catalog), the data type with the preferred attribute
(dened in the pg_type system catalog) is selected as the target
type. If operand 1 can be converted to operand 2 (no conversion
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 429

path), but operand 2 cannot be converted to operand 1 or the
priority of the numeric type is lower than that of operand 2, then
operand 2 is selected as the target type.
▪ If three or more data types are involved, the rule for determining the
target type is as follows: common_type(type1,type2,type3) =
common_type(common_type(type1,type2),type3). Perform iterative
processing in sequence to obtain the nal result.
▪ For IN and NOT IN expressions, if the target type cannot be
determined based on the preceding rules, each expression in lexpr
and expr_list is compared one by one based on the equivalent
operator (=).
▪ Precision determination: The precision of the nally selected
expression is used as the nal result.
● MySQL rules:
– If the operand types of operators are inconsistent, determine the target
type based on the following rules. Then, convert the inconsistent operand
types to the target type and then process the operands.
▪
If both parameters are of the string type, they are compared based
on the string type.
▪
If both parameters are of the integer type, they are compared based
on the integer type.
▪
If a hexadecimal value is not compared with a numeric value, they
are compared based on the binary string.
▪
If one parameter is of the datetime/timestamp type, and the other
parameter is a constant, the constant is converted to the timestamp
type for comparison.
▪
If one parameter is of the decimal type, the data type used for
comparison depends on the other parameter. If the other type is
decimal or integer, the decimal type is used. If the other type is not
decimal, the real type is used.
▪
In other scenarios, the data type is converted to the real type for
comparison.
– Rules for determining the target data type in the set operation and
expression scenarios:
▪ Establish a target type matrix between any two types. Given two
types, the target type can be determined by using the matrix.
▪ If three or more data types are involved, the rule for determining the
target type is as follows: common_type(type1,type2,type3) =
common_type(common_type(type1,type2),type3). Perform iterative
processing in sequence to obtain the nal result.
▪ If the target type is integer and each expression type contains signed
and unsigned integers, the type is promoted to an integer type with
higher precision. The result is unsigned only when all expressions are
unsigned. Otherwise, the result is signed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 430

▪ The highest precision in the expression is used as the nal result.
According to the preceding rules, GaussDB and MySQL dier greatly in data type
conversion rules and types cannot be directly compared. In the preceding scenario,
the execution result of SQL statements may be dierent from that in MySQL. In
the current version, you are advised to use the same type for all expressions or use
CAST to convert the type to the required type in advance to avoid dierences.
8.1.1.3 System Functions
GaussDB is compatible with most MySQL system functions, but there are some
dierences. If not listed, the function behavior is the native GaussDB behavior by
default.
8.1.1.3.1 Flow Control Functions
Table 8-10 Flow control functions
N
o.
MySQL GaussD
B
Dierence
1 IF() Support
ed
● The expr1 input parameter supports only the
Boolean type. If an input parameter of the non-
Boolean type cannot be converted to the Boolean
type, an error is reported.
● If the types of expr2 and expr3 are dierent and
no implicit conversion function exists between the
two types, an error is reported.
● If the two input parameters are of the same type,
the input parameter type is returned.
● If the expr2 and expr3 input parameters are of the
NUMERIC, STRING, or TIME type respectively, the
output is of the TEXT type. In MySQL, the output is
of the VARCHAR type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 431

N
o.
MySQL GaussD
B
Dierence
2 IFNUL
L()
Support
ed
● If the types of expr1 and expr2 are dierent and
no implicit conversion function exists between the
two types, an error is reported.
● If the two input parameters are of the same type,
the input parameter type is returned.
● If the expr1 and expr2 input parameters are of the
NUMERIC, STRING, or TIME type respectively, the
output is of the TEXT type. In MySQL, the output is
of the VARCHAR type.
● If one input parameter is of the FLOAT4 type and
the other is of any type in the numeric category,
the return type is DOUBLE. In MySQL, if one input
parameter is of FLOAT4 type and the other input
parameter is of the TINYINT, UNSIGNED TINYINT,
SMALLINT, UNSIGNED SMALLINT, MEDIUMINT,
UNSIGNED MEDIUMINT, or BOOL type, the FLOAT4
type is returned. If the rst input parameter is of
FLOAT4 type and the second input parameter is of
BIGINT or UNSIGNED BIGINT type, the FLOAT type
is returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 432

N
o.
MySQL GaussD
B
Dierence
3 NULLI
F()
Support
ed
● The NULLIF() type derivation in GaussDB complies
with the following logic:
1. If the data types of two parameters are dierent
and the two input parameter types have an
equality comparison operator, the left value type
corresponding to the equality comparison
operator is returned. Otherwise, the two input
parameter types are forcibly compatible.
2. If an equality comparison operator exists after
forcible type compatibility, the left value type of
the equality comparison operator after forcible
type compatibility is returned.
3. If the corresponding equality operator cannot be
found after forcible type compatibility, an error is
reported.
-- The two input parameter types have an equality comparison
operator.
gaussdb=# select pg_typeof(nullif(1::int2, 2::int8));
pg_typeof
-----------
smallint
(1 row)
-- The two input parameter types do not have the equality
comparison operator, but the equality comparison operator can
be found after forcible type compatibility.
gaussdb=# select pg_typeof(nullif(1::int1, 2::int2));
pg_typeof
-----------
bigint
(1 row)
-- The two input parameter types do not have the equality
comparison operator, and the equality comparison operator
does not exist after forcible type compatibility.
gaussdb=# SELECT nullif(1::bit, '1'::MONEY);
ERROR: operator does not exist: bit = money
LINE 1: SELECT nullif(1::bit, '1'::MONEY);
^
HINT: No operator matches the given name and argument
type(s). You might need to add explicit type casts.
CONTEXT: referenced column: nullif
● The MySQL output type is related only to the type
of the rst input parameter.
1. If the type of the rst input parameter is
TINYINT, SMALLINT, MEDIUMINT, INT, or BOOL,
the output is of the INT type.
2. If the type of the rst input parameter is BIGINT,
the output is of the BIGINT type.
3. When the type of the rst input parameter is
UNSIGNED TINYINT, UNSIGNED SMALLINT,
UNSIGNED MEDIUMINT, UNSIGNED INT, or BIT,
the output is of the UNSIGNED INT type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 433

N
o.
MySQL GaussD
B
Dierence
4. If the type of the rst input parameter is
UNSIGNED BIGINT, the output is of the
UNSIGNED BIGINT type.
5. If the type of the rst input parameter is FLOAT,
DOUBLE, or REAL, the output is of the DOUBLE
type.
6. If the type of the rst input parameter DECIMAL
or NUMERIC, the output is of the DECIMAL type.
7. If the type of the rst input parameter is DATE,
TIME, DATE, DATETIME, TIMESTAMP, CHAR,
VARCHAR, TINYTEXT, ENUM, or SET, the output
is of the VARCHAR type.
8. If the type of the rst input parameter is TEXT,
MEDIUMTEXT, or LONGTEXT, the output is of the
LONGTEXT type.
9. If the type of the rst input parameter is
TINYBLOB, the output is of the VARBINARY type.
10.If the type of the rst input parameter is
MEDIUMBLOB or LONGBLOB, the output is of
the LONGBLOB type.
11.If the type of the rst input parameter is BLOB,
the output is of the BLOB type.
4
ISNUL
L()
Support
ed
In GaussDB, the return value is t or f of the BOOLEAN
type. In MySQL, the return value is 1 or 0 of the INT
type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 434

8.1.1.3.2 Date and Time Functions
NO TE
The following describes the date and time function compatibility between GaussDB and
MySQL:
● In the
Developer Guide
, if an input parameter of a function is a time expression:
Time expressions include text, datetime, date, and time. All types that can be implicitly
converted to time expressions can be used as input parameters. For example, a number can
be implicitly converted to text and then used as a time expression.
However, the eective mode varies according to the function. For example, datedi is used
to calculate only the date dierence. Therefore, the time expression is parsed as date.
timestampdi is used to calculate the time dierence based on the unit. Therefore, the time
expression is parsed as date, time, or datetime based on the unit.
● If an input parameter of a function is an invalid date:
Generally, the supported date and datetime ranges are the same as those of MySQL. The
value of date ranges from '0000-01-01' to '9999-12-31', and the value of datetime ranges
from '0000-01-01 00:00:00' to '9999-12-31 23:59:59'. Although the date and datetime
ranges supported by GaussDB are greater than those supported by MySQL, out-of-bounds
dates are still invalid.
Most time functions generate alarms and return NULL. Only dates that can be normally
converted by CAST are normal and reasonable dates.
Most function scenarios of GaussDB date and time functions are the same as
those of MySQL, but there are still dierences. Some dierences are as follows:
● If an input parameter of a function is NULL, the function returns NULL, and
no warning or error is reported. These functions include:
from_days, date_format, str_to_date, datedi, timestampdi, date_add,
subtime, month, time_to_sec, to_days, to_seconds, dayname, monthname,
convert_tz, sec_to_time, addtime, adddate, date_sub, timedi, last_day,
weekday, from_unixtime, unix_timestamp, subdate, day, year, weekofyear,
dayofmonth, dayofyear, week, yearweek, dayofweek, time_format, hour,
minute, second, microsecond, quarter, get_format, extract, makedate,
period_add, timestampadd, period_di, utc_time, utc_timestamp, maketime,
and curtime.
Example:
gaussdb=# select day(null);
day
-----
(1 row)
● Some functions with pure numeric input parameters are dierent from those
of MySQL. Numeric input parameters without quotation marks are converted
into text input parameters for processing.
Example:
gaussdb=# select day(19231221.123141);
WARNING: Incorrect datetime value: "19231221.123141"
CONTEXT: referenced column: day
day
-----
(1 row)
● Time and date calculation functions are adddate, subdate, date_add, and
date_sub. If the date result after calculation is within the range
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 435
[0000-01-01,0001-01-01], the result is returned normally. MySQL returns
'0000-00-00'.
Example:
gaussdb=# select subdate('0001-01-01', interval 1 day);
subdate
-------------
0000-12-31
(1 row)
● If the input parameter of the date or datetime type of the date and time
function contains month 0 or day 0, the value is invalid. In strict mode, an
error is reported. In loose mode, if the input is a character string or number, a
warning is reported. If the input is of the date or datetime type, the system
processes the input as December of the previous year or the last day of the
previous month.
If the type of the CAST function is converted to date or datetime, an error is
reported in strict mode. In loose mode, no warning is reported. Instead, the
system processes the input as December of the previous year or the last day
of the previous month. Pay attention to this dierence. MySQL outputs the
value as it is, even if the year, month, and day are set to 0.
Example:
gaussdb=# select adddate('2023-01-00', 1);-- Strict mode
ERROR: Incorrect datetime value: "2023-01-00"
CONTEXT: referenced column: adddate
gaussdb=# select adddate('2023-01-00', 1);-- Loose mode
WARNING: Incorrect datetime value: "2023-01-00"
CONTEXT: referenced column: adddate
adddate
---------
(1 row)
gaussdb=# select adddate(date'2023-00-00', 1);-- Loose mode
adddate
------------
2022-12-01
(1 row)
gaussdb=# select cast('2023/00/00' as date);-- Loose mode
date
------------
2022-11-30
(1 row)
gaussdb=# select cast('0000-00-00' as datetime);-- Loose mode
timestamp
---------------------
0000-00-00 00:00:00
(1 row)
● If the input parameter of the function is of the numeric data type, no error is
reported in the case of invalid input, and the input parameter is processed as
0.
Example:
gaussdb=# select from_unixtime('aa');
from_unixtime
---------------------
1970-01-01 08:00:00
(1 row)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 436

● A maximum of six decimal places are allowed. Decimal places with all 0s are
not allowed.
Example:
gaussdb=# select from_unixtime('1234567899.00000');
from_unixtime
---------------------
2009-02-14 07:31:39
(1 row)
● If the time function parameter is a character string, the result is correct only
when the year, month, and day are separated by a hyphen (-) and the hour,
minute, and second are separated by a colon (:).
Example:
gaussdb=# select adddate('20-12-12',interval 1 day);
adddate
------------
2020-12-13
(1 row)
● If the return value of a function is of the varchar type in MySQL, the return
value of the function is of the text type in GaussDB.
-- Return value of a function in GaussDB.
gaussdb=# SELECT pg_typeof(adddate('2023-01-01', 1));
pg_typeof
-----------
text
(1 row)
-- Return value of a function in MySQL.
mysql> CREATE VIEW v1 AS SELECT adddate('2023-01-01', 1);
Query OK, 0 rows aected (0.00 sec)
mysql> DESC v1;
+--------------------------+-------------+------+-----+---------+-------+
| Field | Type | Null | Key | Default | Extra |
+--------------------------+-------------+------+-----+---------+-------+
| adddate('2023-01-01', 1) | varchar(29) | YES | | NULL | |
+--------------------------+-------------+------+-----+---------+-------+
1 row in set (0.00 sec)
Table 8-11 Date and time functions
N
o.
MySQL GaussDB Dierence
1 ADDDATE() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 437

N
o.
MySQL GaussDB Dierence
2 ADDTIME() Supported. ● MySQL returns NULL if the
second input parameter is a
string in the DATETIME format.
GaussDB can calculate the
value.
● The value range of an input
parameter is ['0001-01-01
00:00:00', 9999-12-31
23:59:59.999999].
● If the rst parameter of the
ADDTIME function in MySQL is
a dynamic parameter (for
example, in a prepared
statement), the return type is
TIME. Otherwise, the parse type
of the function is derived from
the parse type of the rst
parameter. The return value
rules of the ADDTIME function
in GaussDB are as follows:
– The rst input parameter is
of the date type, the second
input parameter is of the
date type, and the return
value is of the time type.
– The rst input parameter is
of the date type, the second
input parameter is of the
text type, and the return
value is of the text type.
– The rst input parameter is
of the date type, the second
input parameter is of the
datetime type, and the
return value is of the time
type.
– The rst input parameter is
of the date type, the second
input parameter is of the
time type, and the return
value is of the time type.
– The rst input parameter is
of the text type, the second
input parameter is of the
date type, and the return
value is of the text type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 438

N
o.
MySQL GaussDB Dierence
– The rst input parameter is
of the text type, the second
input parameter is of the
text type, and the return
value is of the text type.
– The rst input parameter is
of the text type, the second
input parameter is of the
datetime type, and the
return value is of the text
type.
– The rst input parameter is
of the text type, the second
input parameter is of the
time type, and the return
value is of the text type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the date type, and the return
value is of the datetime type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the text type, and the return
value is of the text type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the datetime type, and the
return value is of the
datetime type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the time type, and the return
value is of the datetime type.
– The rst input parameter is
of the time type, the second
input parameter is of the
date type, and the return
value is of the time type.
– The rst input parameter is
of the time type, the second
input parameter is of the
text type, and the return
value is of the text type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 439

N
o.
MySQL GaussDB Dierence
– The rst input parameter is
of the time type, the second
input parameter is of the
datetime type, and the
return value is of the time
type.
– The rst input parameter is
of the time type, the second
input parameter is of the
time type, and the return
value is of the time type.
3 CONVERT_TZ() Supported. -
4 CURDATE() Supported. -
5 CURRENT_DATE(),
CURRENT_DATE
Supported. -
6 CURRENT_TIME(),
CURRENT_TIME
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only integer values within
the range of [0,6] as the precision
of the returned time. For other
values, an error is reported. The
valid precision value in MySQL is
within [0,6], but the input integer
value is modulated by 256. For
example, if the input integer value
is 257, the time value with
precision 1 is returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 440
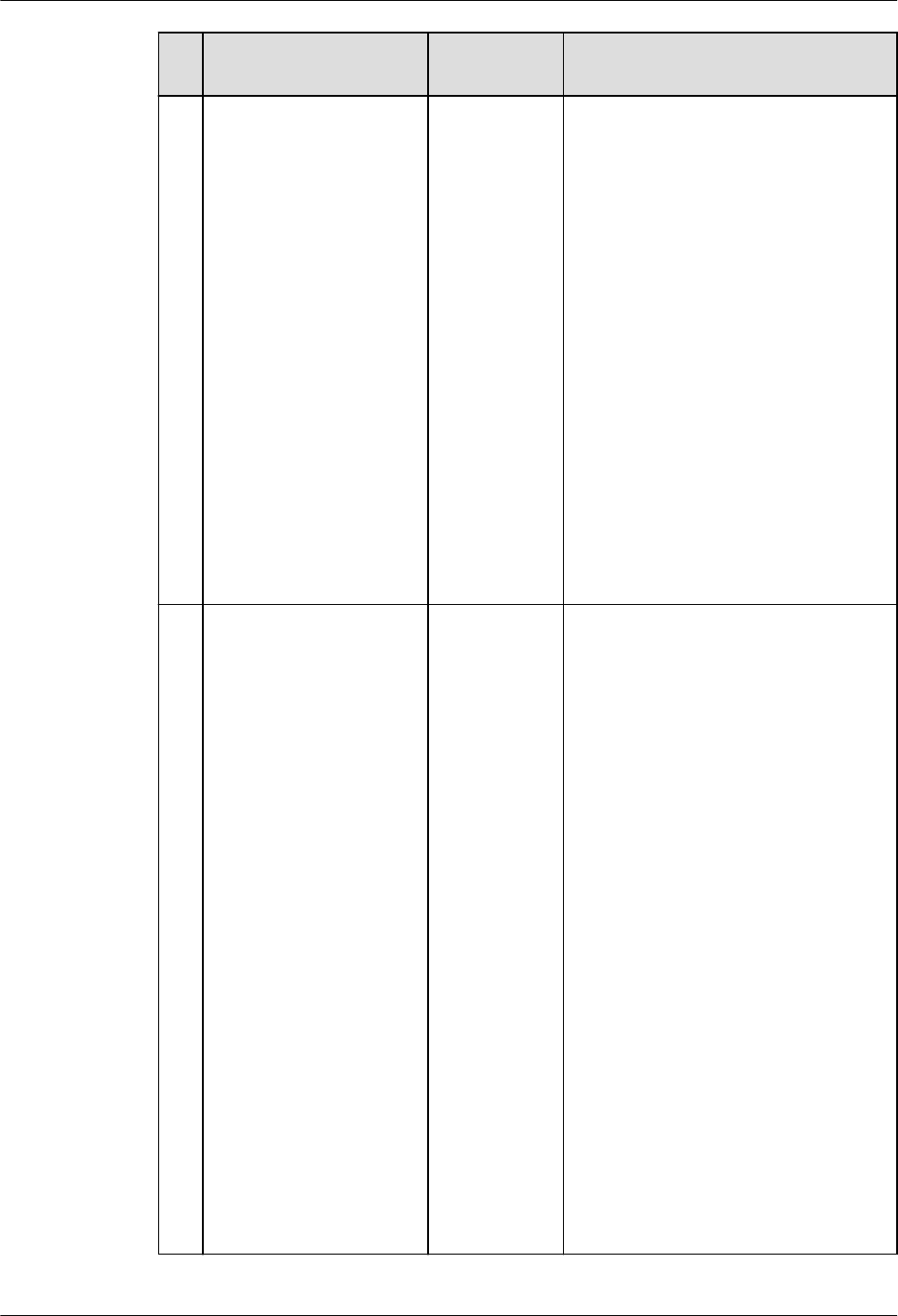
N
o.
MySQL GaussDB Dierence
7 CURRENT_TIMESTAM
P(),
CURRENT_TIMESTAMP
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only the input integer
value within the range of [0,6] as
the precision of the returned time.
If the input integer value is greater
than 6, an alarm is generated and
the time value is output based on
the precision 6. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
8 CURTIME() Supported. In GaussDB, if a character string or
a non-integer value is entered, the
value is implicitly converted into
an integer and then the precision
is veried. If the value is beyond
the [0,6] range, an error is
reported. If the value is within the
range, the time value is output
normally. In MySQL, an error is
reported. The time value (after the
decimal point) output by precision
is rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only integer values within
the range of [0,6] as the precision
of the returned time. For other
values, an error is reported. The
valid precision value in MySQL is
within [0,6], but the input integer
value is modulated by 256. For
example, if the input integer value
is 257, the time value with
precision 1 is returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 441

N
o.
MySQL GaussDB Dierence
9 YEARWEEK() Supported. -
10 DATE_ADD() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
11 DATE_FORMAT() Supported. -
12 DATE_SUB() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
13 DATEDIFF() Supported. -
14 DAY() Supported. -
15 DAYNAME() Supported. -
16 DAYOFMONTH() Supported. -
17 DAYOFWEEK() Supported. -
18 DAYOFYEAR() Supported. -
19 EXTRACT() Supported. -
20 FROM_DAYS() Supported. -
21 FROM_UNIXTIME() Supported. -
22 GET_FORMAT() Supported. -
23 HOUR() Supported. -
24 LAST_DAY Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 442
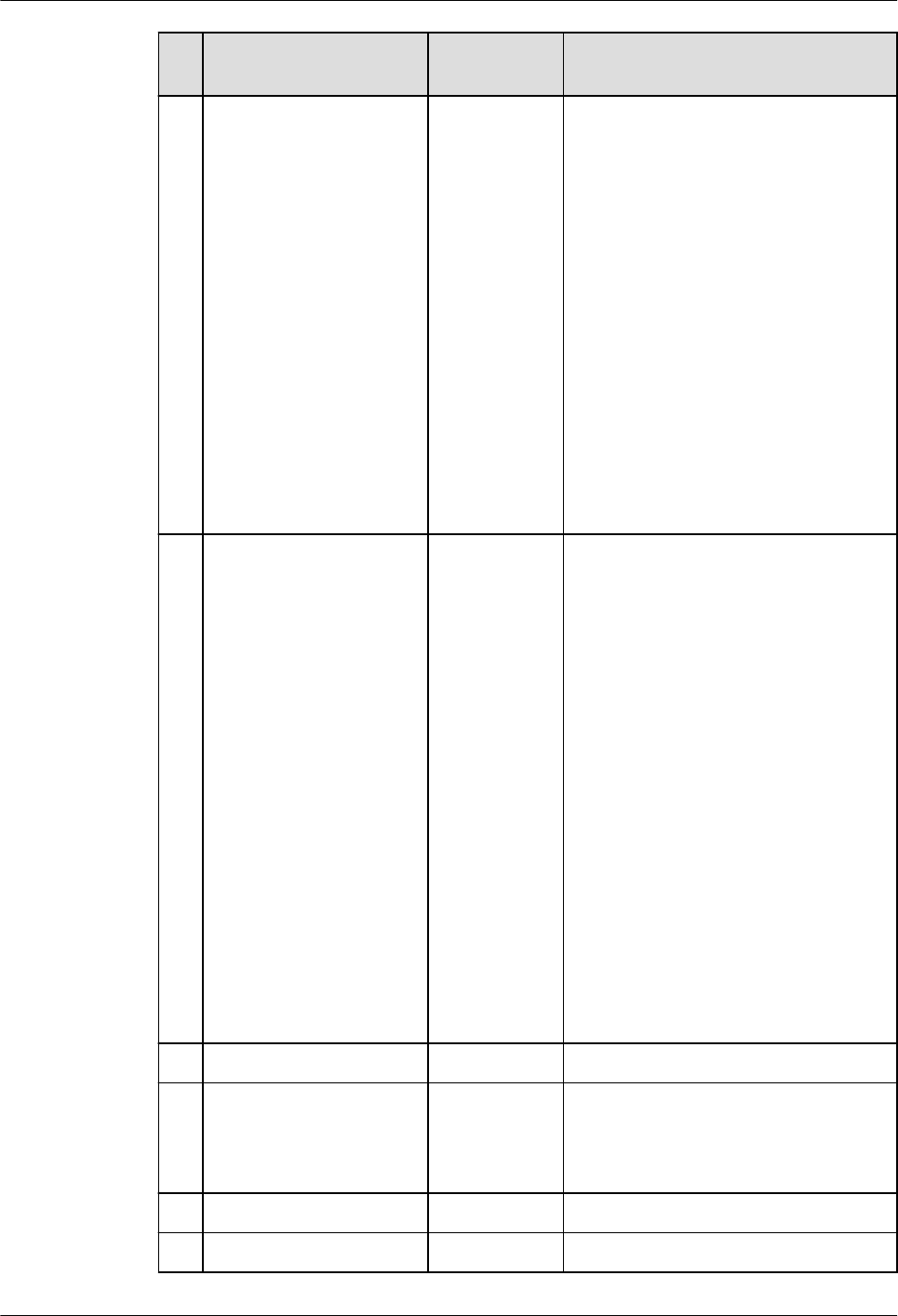
N
o.
MySQL GaussDB Dierence
25 LOCALTIME(),
LOCALTIME
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only integer values within
the range of [0,6] as the precision
of the returned time. For other
integer values, an error is reported.
The valid precision value in MySQL
is within [0,6], but the input
integer value is modulated by 256.
For example, if the input integer
value is 257, the time value with
precision 1 is returned.
26 LOCALTIMESTAMP,
LOCALTIMESTAMP()
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only the input integer
value within the range of [0,6] as
the precision of the returned time.
If the input integer value is greater
than 6, an alarm is generated and
the time value is output based on
the precision 6. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
27 MAKEDATE() Supported. -
28 MAKETIME() Supported. When the input parameter is
NULL, GaussDB does not support
self-nesting of the maketime
function, but MySQL supports.
29 MICROSECOND() Supported. -
30 MINUTE() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 443
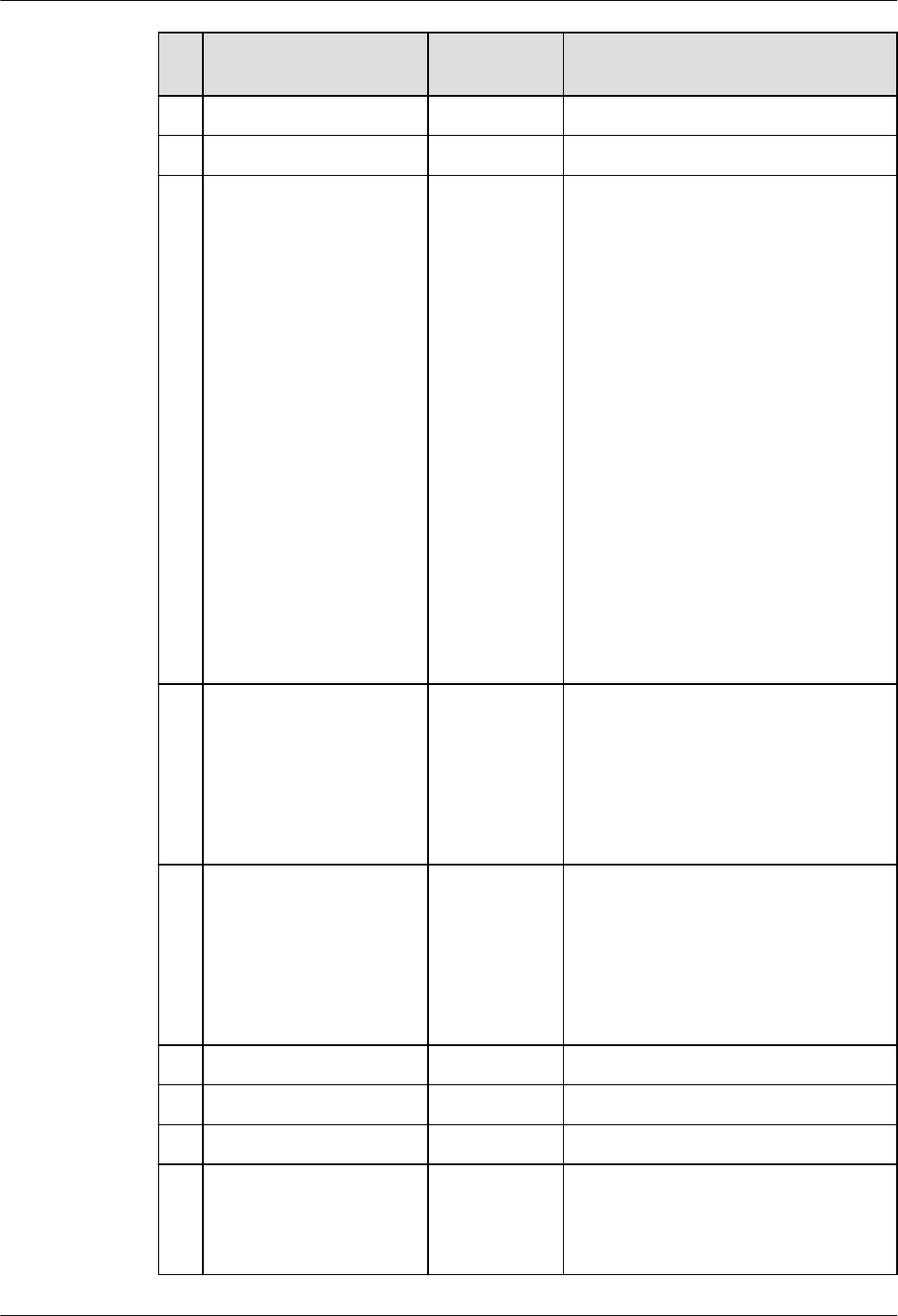
N
o.
MySQL GaussDB Dierence
31 MONTH() Supported. -
32 MONTHNAME() Supported. -
33 NOW() Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only the input integer
value within the range of [0,6] as
the precision of the returned time.
If the input integer value is greater
than 6, an alarm is generated and
the time value is output based on
the precision 6. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
34 PERIOD_ADD() Supported. If the input parameter period or
result is less than 0, GaussDB
reports an error by referring to the
performance in MySQL 8.0.x.
Integer wrapping occurs in MySQL
5.7. As a result, the calculation
result is abnormal.
35 PERIOD_DIFF() Supported. If the input parameter or result is
less than 0, GaussDB reports an
error by referring to the
performance in MySQL 8.0.x.
Integer wrapping occurs in MySQL
5.7. As a result, the calculation
result is abnormal.
36 QUARTER() Supported. -
37 SEC_TO_TIME() Supported. -
38 SECOND() Supported. -
39 STR_TO_DATE() Supported. Return value dierence: In
GaussDB, text is returned. In
MySQL, datetime and date are
returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 444

N
o.
MySQL GaussDB Dierence
40 SUBDATE() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 445

N
o.
MySQL GaussDB Dierence
41 SUBTIME() Supported. ● MySQL returns NULL if the
second input parameter is a
string in the DATETIME format.
GaussDB can calculate the
value.
● The value range of an input
parameter is ['0001-01-01
00:00:00', 9999-12-31
23:59:59.999999].
● If the rst parameter of the
SUBTIME function in MySQL is
a dynamic parameter (for
example, in a prepared
statement), the return type is
TIME. Otherwise, the parse type
of the function is derived from
the parse type of the rst
parameter. The return value
rules of the SUBTIME function
in GaussDB are as follows:
– The rst input parameter is
of the date type, the second
input parameter is of the
date type, and the return
value is of the time type.
– The rst input parameter is
of the date type, the second
input parameter is of the
text type, and the return
value is of the text type.
– The rst input parameter is
of the date type, the second
input parameter is of the
datetime type, and the
return value is of the time
type.
– The rst input parameter is
of the date type, the second
input parameter is of the
time type, and the return
value is of the time type.
– The rst input parameter is
of the text type, the second
input parameter is of the
date type, and the return
value is of the text type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 446

N
o.
MySQL GaussDB Dierence
– The rst input parameter is
of the text type, the second
input parameter is of the
text type, and the return
value is of the text type.
– The rst input parameter is
of the text type, the second
input parameter is of the
datetime type, and the
return value is of the text
type.
– The rst input parameter is
of the text type, the second
input parameter is of the
time type, and the return
value is of the text type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the date type, and the return
value is of the datetime type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the text type, and the return
value is of the text type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the datetime type, and the
return value is of the
datetime type.
– The rst input parameter is
of the datetime type, the
second input parameter is of
the time type, and the return
value is of the datetime type.
– The rst input parameter is
of the time type, the second
input parameter is of the
date type, and the return
value is of the time type.
– The rst input parameter is
of the time type, the second
input parameter is of the
text type, and the return
value is of the text type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 447

N
o.
MySQL GaussDB Dierence
– The rst input parameter is
of the time type, the second
input parameter is of the
datetime type, and the
return value is of the time
type.
– The rst input parameter is
of the time type, the second
input parameter is of the
time type, and the return
value is of the time type.
42 SYSDATE() Supported. The integer value of the MySQL
input parameter is wrapped when
reaching the maximum value 255
in one byte. The integer in
GaussDB is not wrapped.
43 YEAR() Supported. -
44 TIME_FORMAT() Supported. -
45 TIME_TO_SEC() Supported. -
46 TIMEDIFF() Supported. -
47 WEEKOFYEAR() Supported. -
48 TIMESTAMPADD() Supported. -
49 TIMESTAMPDIFF() Supported. -
50 TO_DAYS() Supported. -
51 TO_SECONDS() Supported. -
52 UNIX_TIMESTAMP() Supported. Return value dierence: In
GaussDB, numeric is returned. In
MySQL, int is returned.
53 UTC_DATE() Supported. MySQL supports calling without
parentheses, but GaussDB does
not. The integer value of the
MySQL input parameter is
wrapped when reaching the
maximum value 255 in one byte.
MySQL input parameters support
only integers ranging from 0 to 6.
GaussDB supports input
parameters that can be implicitly
converted to integers ranging from
0 to 6.
54 UTC_TIME() Supported.
55 UTC_TIMESTAMP() Supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 448

N
o.
MySQL GaussDB Dierence
56 WEEK() Supported. -
57 WEEKDAY() Supported. -
8.1.1.3.3 String Functions
Table 8-12 String functions
No. MySQL GaussDB Dierence
1 BIN() Supported. In GaussDB, the types supported by
function input parameter 1 are as
follows:
● Integer types: tinyint, smallint,
mediumint, int, and bigint.
● Unsigned integer types: tinyint
unsigned, smallint unsigned, int
unsigned, and bigint unsigned.
● Character and text types: char, varchar,
tinytext, text, mediumtext, and
longtext. Only numeric integer strings
are supported, and the integer range
is within the bigint range.
● Floating-point types: oat, real, and
double.
● Fixed-point types: numeric, decimal,
and dec.
● Boolean type: bool.
2 CONCAT() Supported. The data type of the return value of
CONCAT is always text regardless of the
data type of the parameter. However, in
MySQL, if CONCAT contains binary
parameters, the return value is binary.
3 CONCAT_WS() Supported. The data type of the return value of
CONCAT_WS is always text regardless of
the data type of the parameter. However,
in MySQL, if CONCAT_WS contains
binary parameters, the return value is
binary. In other cases, the return value is
a string.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 449

No. MySQL GaussDB Dierence
4 ELT() Supported. ● In GaussDB, the types supported by
function input parameter 1 are as
follows:
Integer types: tinyint, smallint,
mediumint, int, and bigint.
Unsigned integer types: tinyint
unsigned, smallint unsigned, and int
unsigned.
Character and text types: char, varchar,
tinytext, text, mediumtext, and
longtext. Only numeric integer strings
are supported, and the integer range
is within the bigint range.
Floating-point types: oat, real, and
double.
Fixed-point types: numeric, decimal,
and dec.
Boolean type: bool.
● In GaussDB, the types supported by
function input parameter 2 are as
follows:
Integer types: tinyint, smallint,
mediumint, int, and bigint.
Unsigned integer types: tinyint
unsigned, smallint unsigned, int
unsigned, and bigint unsigned.
Character and text types: char, varchar,
tinytext, text, mediumtext, and
longtext.
Floating-point types: oat, real, and
double.
Fixed-point types: numeric, decimal,
and dec.
Boolean type: bool.
Large object types: tinyblob, blob,
mediumblob, and longblob.
Date types: datetime, timestamp, date,
and time.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 450
No. MySQL GaussDB Dierence
5 FIELD Supported. When function input parameters range
from the maximum bigint value to the
maximum bigint unsigned value,
incompatibility occurs.
When function input parameters are of
oat(m, d), double(m, d), or real(m, d)
type, the precision is higher and
incompatibility occurs.
6 FIND_IN_SET() Supported. When the database encoding is set to
'SQL_ASCII', the default case sensitivity
rule is not supported. That is, if no
character set rule is specied, uppercase
and lowercase letters are treated as
distinct.
7 INSERT() Supported. ● The range of input parameters of the
Int64 type is from –
9223372036854775808 to
+9223372036854775807. If a value is
out of range, an error is reported.
MySQL does not limit the range of
input parameters of the numeric type.
If an exception occurs, an alarm is
generated, indicating that the value is
set to the upper or lower limit.
● The maximum length of the input
parameter of the text type is 2^30 – 5
bytes, and the maximum length of the
input parameter of the bytea type is
2^30 – 512 bytes.
● If any of the s1 and s2 parameters is
of the bytea type and the result
contains invalid characters, the
displayed result may be dierent from
that of MySQL, but the character
encoding is the same as that of
MySQL.
8
LOCATE() Supported. When input parameter 1 is of the bytea
type and input parameter 2 is of the text
type, the behavior of GaussDB is dierent
from that of MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 451

No. MySQL GaussDB Dierence
9 MAKE_SET() Supported. ● When the bits parameter is an integer,
the maximum range is int128, which is
smaller than the MySQL range.
● When the bits parameter is of the
date type (datetime, timestamp, date,
or time), it is not supported because
the conversion from the date type to
the integer type is dierent from that
in MySQL.
● GaussDB and MySQL are inherently
dierent in the bit and Boolean types,
causing dierent returned results.
When the bits input parameter is of
the Boolean type, and the str input
parameter is of the bit or Boolean
type, they are not supported.
● When the bits input parameter is of
the character string or text type, only
the pure integer format is supported.
In addition, the value range of pure
integers is limited to bigint.
● The integer value of the str input
parameter exceeds the range from 81
negative nines to 81 positive nines.
The return value is dierent from that
of MySQL.
● When the str input parameter is
expressed in scientic notation,
trailing zeros are displayed in GaussDB
but not displayed in MySQL. This is an
inherent dierence.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 452
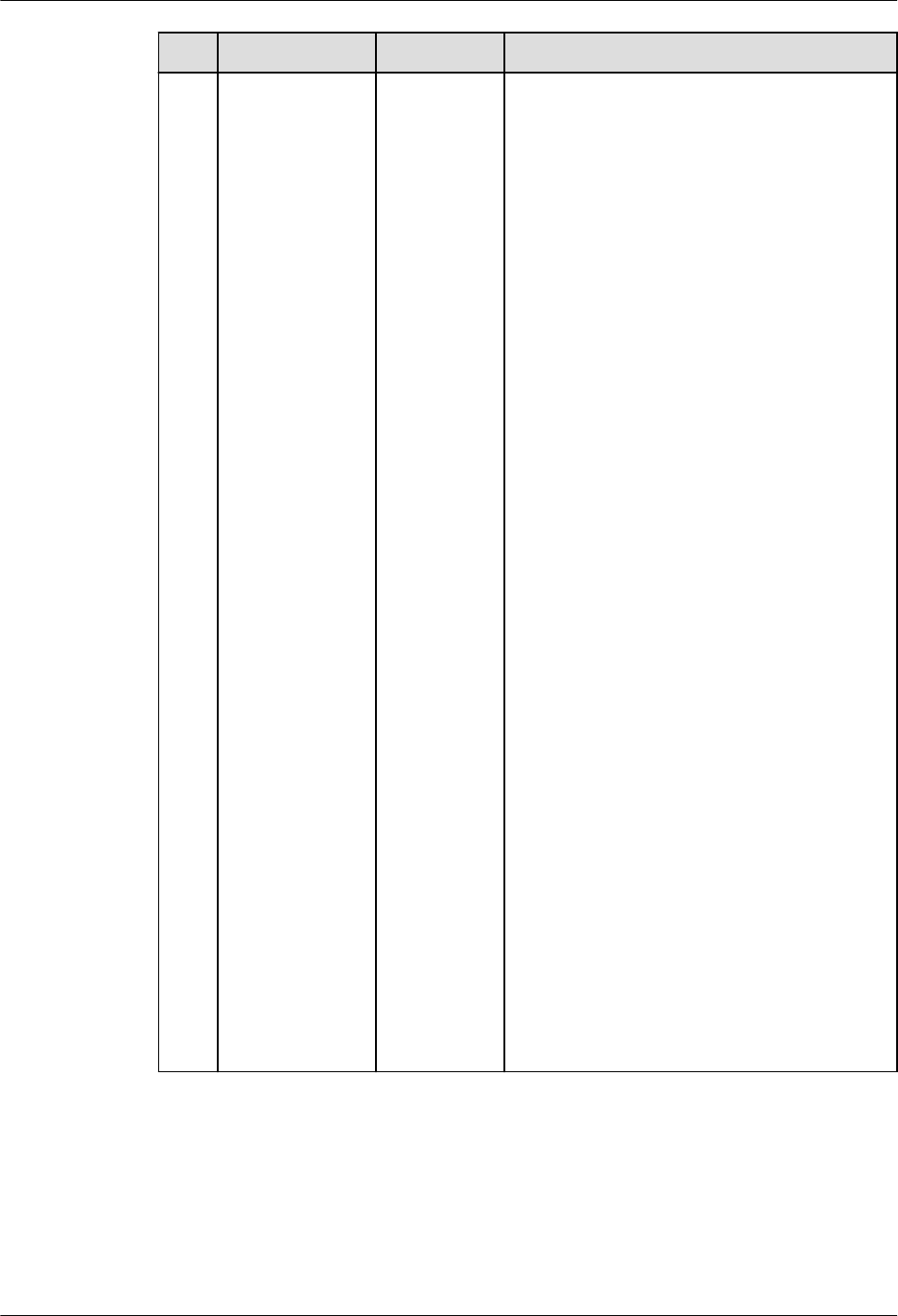
No. MySQL GaussDB Dierence
10 QUOTE() Supported. ● If the str character string contains
"\Z", "\r", "\%", or "\_", GaussDB does
not escape it, which is dierent from
MySQL. The slash followed by digits
may also cause dierences, for
example, "\563". This function
dierence is the escape character
dierence between GaussDB and
MySQL.
● The output format of "\b" in the str
character string is dierent from that
in MySQL. This is an inherent
dierence between GaussDB and
MySQL.
● If the str character string contains
"\0", GaussDB cannot identify the
character because the UTF-8 character
set cannot identify the character. As a
result, the input fails. This is an
inherent dierence between GaussDB
and MySQL.
● If str is of the bit or Boolean type, this
type is not supported because it is
dierent in GaussDB and MySQL.
● GaussDB supports a maximum of 1
GB data transfer. The maximum
length of the str input parameter is
536870908, and the maximum size of
the result string returned by the
function is 1 GB.
● The integer value of the str input
parameter exceeds the range from 81
negative nines to 81 positive nines.
The return value is dierent from that
of MySQL.
● When the str input parameter is
expressed in scientic notation,
trailing zeros are displayed in GaussDB
but not displayed in MySQL. This is an
inherent dierence.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 453

No. MySQL GaussDB Dierence
11 SPACE() Supported. 1. The maximum value of GaussDB input
parameter 1 is 1073741818. If the
value exceeds 1073741818, an empty
string is returned. By default, the
maximum value of MySQL input
parameter 1 is 4194304. If the value
exceeds 4194304, an alarm is
generated.
2. In GaussDB, the types supported by
function input parameter 1 are as
follows:
● Integer types: tinyint, smallint,
mediumint, int, and bigint.
● Unsigned integer types: tinyint
unsigned, smallint unsigned, and
int unsigned.
● Character and text types: char,
varchar, tinytext, text, mediumtext,
and longtext. Only numeric integer
strings are supported, and the
integer range is within the bigint
range.
● Floating-point types: oat, real, and
double.
● Fixed-point types: numeric, decimal,
and dec.
● Boolean type: bool.
12
SUBSTR() Supported. -
13 SUBSTRING() Supported. -
14 SUBSTRING_IN
DEX()
Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 454

No. MySQL GaussDB Dierence
15 STRCMP() Supported. 1. Dierent from MySQL, GaussDB
supports the following input
parameter types:
● Character types: CHAR, VARCHAR,
NVARCHAR2, and TEXT.
● Binary type: BYTEA.
● Numeral types: TINYING
[UNSIGNED], SMALLINT
[UNSIGNED], INTEGER
[UNSIGNED], BIGINT [UNSIGNED],
FLOAT4, FLOAT8, and NUMERIC.
● Date and time types: DATE, TIME
WITHOUT TIME ZONE, DATETIME,
and TIMESTAMPTZ.
2. For the oating-point type in the
numeric type, the precision may be
dierent from that in MySQL due to
dierent connection parameter
settings. Therefore, this scenario is not
recommended, or the NUMERIC type
is used instead.
16
SHA()/SHA1() Supported. -
17 SHA2() Supported. -
8.1.1.3.4 Forced Conversion Functions
Table 8-13 Forced conversion functions
No.
MySQL GaussDB Dierence
1 CAST() Supported The data type
conversion rules
and supported
conversion
types are
subject to the
conversion
scope and rules
supported by
GaussDB.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 455

No. MySQL GaussDB Dierence
2 CONVERT() Supported The data type
conversion rules
and supported
conversion
types are
subject to the
conversion
scope and rules
supported by
GaussDB.
8.1.1.3.5 Encryption Functions
Table 8-14 Encryption functions
No. MySQL GaussDB Diere
nce
1 AES_DECRYPT() Supported. -
2 AES_ENCRYPT() Supported. -
8.1.1.3.6 JSON Functions
NO TE
JSON function dierences:
1. For JSON functions and other character input parameter functions, if the input contains
escape characters, you need to set the GUC parameter set
standard_conforming_strings to o, which is dierent from MySQL by default. In this
case, escape characters are compatible with MySQL. However, a warning alarm is
generated for non-standard character input. Escape characters \t and \u, and escape
digits are dierent from those in MySQL. If the GUC parameter is not set, the
JSON_UNQUOTE() function is still compatible with MySQL and no alarm is reported.
2. When processing an ultra-long number (the number contains more than 64 characters),
the JSON function of GaussDB parses the number as a DOUBLE and uses scientic
notation for counting. The input parameters of the non-JSON type are the same as
those of MySQL. However, when input parameters of the JSON type are used, the JSON
type is not completely compatible with MySQL. As a result, dierences occur in this
scenario. MySQL displays complete numbers. (When the number length exceeds 82,
MySQL displays an incorrect result.) GaussDB still parses an ultra-long number into a
double-precision value. Long numbers are stored using oating-point numbers. During
calculation, precision loss occurs in both GaussDB and MySQL. Therefore, you are
advised to use character strings to store long numbers.
gaussdb=# select json_insert('[1, 4,
99999999999999999999999999999999999999999999999999999999999999999999999999]','$[6]',j
son_insert('[1,4]','$[5]',99999999999999999999999999999999999999999999999999999999999999
999999999999));
json_insert
------------------------------
[1, 4, 1e+74, [1, 4, 1e+74]]
(1 row)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 456

Table 8-15 JSON functions
N
o.
MySQL GaussDB Dierence
1 JSON_APPEND() Supported. -
2 JSON_ARRAY() Supported. -
3 JSON_ARRAY_APPEND() Supported. -
4 JSON_ARRAY_INSERT() Supported. -
5 JSON_CONTAINS() Supported. -
6 JSON_CONTAINS_PATH() Supported. -
7 JSON_DEPTH() Supported. Return value
dierence: In
GaussDB, int
is returned. In
MySQL, bigint
is returned.
8 JSON_EXTRACT() Supported. -
9 JSON_INSERT() Supported. -
10 JSON_KEYS() Supported. -
11 JSON_LENGTH() Supported. Return value
dierence: In
GaussDB, int
is returned. In
MySQL, bigint
is returned.
12 JSON_MERGE() Supported. -
13 JSON_OBJECT() Supported. -
14 JSON_QUOTE() Supported. Return value
dierence: In
GaussDB,
JSON is
returned. In
MySQL,
varchar or
text is
returned.
15 JSON_REMOVE() Supported. -
16 JSON_REPLACE() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 457

N
o.
MySQL GaussDB Dierence
17 JSON_SEARCH() Supported. Return value
dierence: In
GaussDB, text
is returned. In
MySQL, JSON
is returned.
18 JSON_SET() Supported. -
19 JSON_TYPE() Supported. JSON values
of the
numeric type
are identied
as number,
which is
dierent from
MySQL.
20 JSON_UNQUOTE() Supported. -
21 JSON_VALID() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 458

8.1.1.3.7 Aggregate Functions
Table 8-16 Aggregate functions
No. MySQL GaussDB Dierence
1 GROUP_CONCAT() Supported. 1. If the group_concat
parameter contains both the
DISTINCT and ORDER BY
syntaxes, all expressions
following ORDER BY must be
in the DISTINCT expression.
2. group_concat(... order by
Number
) does not indicate
the sequence of the
parameter. The number is
only a constant expression,
which is equivalent to no
sorting.
3. The data type of the return
value of group_concat is
always text regardless of the
data type of the parameter.
For MySQL, if group_concat
contains binary parameters,
the return value is binary. In
other cases, the return value
is a character string. If the
return value length is greater
than 512 bytes, the data type
is a character large object or
binary large object.
4. The value of
group_concat_max_len
ranges from 0 to 1073741823.
The maximum value is
smaller than that of MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 459

No. MySQL GaussDB Dierence
2 DEFAULT() Supported. 1. The default value of a column
is an array. GaussDB returns
an array. MySQL does not
support the array type.
2. GaussDB columns are hidden
columns (such as xmin and
cmin). The function returns a
null value.
3. GaussDB supports default
values of partitioned tables,
temporary tables, and multi-
table join query.
4. GaussDB supports the query
of nodes whose column
names contain character
string values (indicating
names) and A_Star nodes
(indicating that asterisks [*]
appear), for example,
default(tt.t4.id) and
default(tt.t4.*). For invalid
query column names and
A_Star nodes, the error
information reported by
GaussDB is dierent from
that reported by MySQL.
5. When the default value of a
column is created in GaussDB,
the range of the column type
is not veried. As a result, an
error may be reported when
the default function is used.
6. If the default value of a
column is a function
expression, the default
function in GaussDB returns
the calculated value of the
default expression of the
column during table creation.
The default function in
MySQL returns NULL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 460
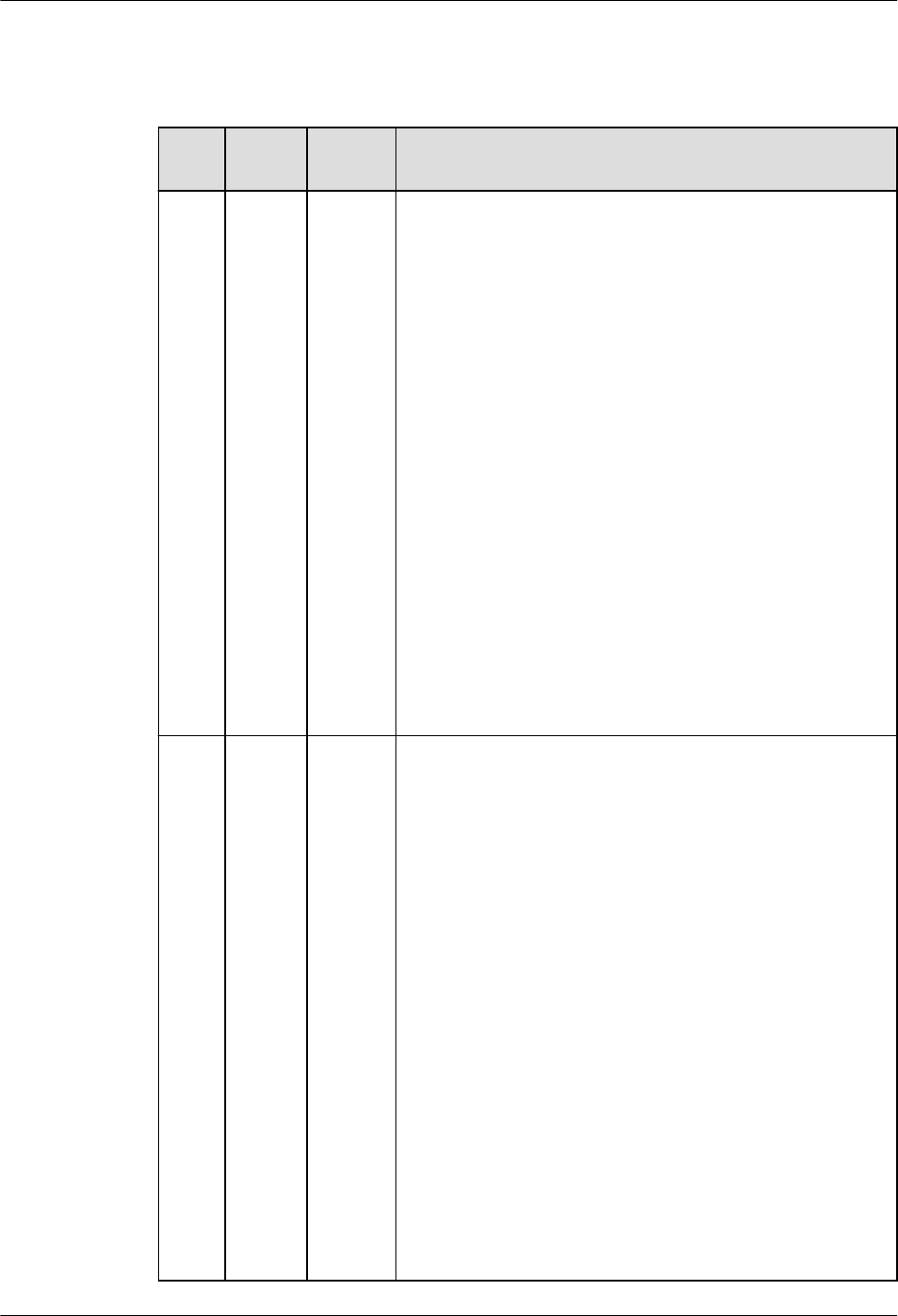
8.1.1.3.8 Arithmetic Functions
Table 8-17 Arithmetic functions
No. MySQ
L
Gauss
DB
Dierence
1 log2() Suppor
ted.
1. The display of decimal places is dierent from that
in MySQL. Due to the restriction of the GaussDB
oating-point data type, the extra_oat_digits
parameter is used to control the number of
decimal places to be displayed.
2. Due to the internal processing dierence of the
input precision, the calculation results of GaussDB
and MySQL are dierent.
3. The following data types are supported:
● Integer types: bigint, int16, int, smallint, and
tinyint.
● Unsigned integer types: bigint unsigned, integer
unsigned, smallint unsigned, and tinyint
unsigned.
● Floating-point types: numeric and real.
● String types: character, character varying, clob,
text, and numeric. However, only numeric
integer strings are supported.
● SET type.
● NULL type.
2
log10(
)
Suppor
ted.
1. The display of decimal places is dierent from that
in MySQL. Due to the restriction of the GaussDB
oating-point data type, the extra_oat_digits
parameter is used to control the number of
decimal places to be displayed.
2. Due to the internal processing dierence of the
input precision, the calculation results of GaussDB
and MySQL are dierent.
3. The following data types are supported:
● Integer types: bigint, int16, int, smallint, and
tinyint.
● Unsigned integer types: bigint unsigned, integer
unsigned, smallint unsigned, and tinyint
unsigned.
● Floating-point types: numeric and real.
● String types: character, character varying, clob,
text, and numeric. However, only numeric
integer strings are supported.
● SET type.
● NULL type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 461

8.1.1.3.9 Other Functions
Table 8-18 Other functions
No. MySQL GaussDB Dierence
1 UUID() Supported -
2 UUID_SHORT() Supported -
8.1.1.4 Operators
GaussDB is compatible with most MySQL operators, but there are some
dierences. If not listed, the operator behavior is the native GaussDB behavior by
default.
No. MySQL GaussDB Dierence
1 NULL-safe equal
(<=>)
Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 462

No. MySQL GaussDB Dierence
2 [NOT] REGEXP Supported. ● When b_format_dev_version
is set to 's2', the pattern
string contains escape
characters such as '\\a', '\\d',
'\\e', '\\n', '\\Z', and '\\u', and
the source strings '\a', '\d',
'\e', '\n', '\Z', and '\u' are
matched, the behavior of
GaussDB is dierent from
that of MySQL 5.7. MySQL
5.7 has a bug, which has
been xed in later MySQL
versions and is now
consistent with GaussDB.
● When b_format_dev_version
is set to 's2', GaussDB's '\b'
can match '\\b', but MySQL
cannot.
● GaussDB reports an error
when the input parameter of
the pattern string pat is
invalid and only the right
single parenthesis ')' exists.
MySQL has a bug, which has
been xed in later versions.
● When de|abc matches de or
abc, if there is a null value
on the left or right of |,
MySQL reports an error. This
bug has been xed in later
versions.
● The regular expression of the
blank character [\t] can
match the character class
[:blank:] in GaussDB, but
MySQL's [\t] cannot match
[:blank:]. MySQL has a bug,
which has been xed in later
versions.
● GaussDB supports non-
greedy pattern matching.
That is, the number of
matching characters is as
small as possible. A question
mark (?) is added after some
special characters, for
example, ??, *?, +?, {n}?,
{n,}?, and {n,m}?. MySQL 5.7
does not support non-greedy
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 463
No. MySQL GaussDB Dierence
pattern matching, and the
error message "Got error
'repetition-operator operand
invalid' from regexp" is
displayed. MySQL 8.0 already
supports this function.
● In the binary character set,
the text and BLOB types are
converted to the bytea type.
The REGEXP operator does
not support the bytea type.
Therefore, the two types
cannot be matched.
3 [NOT] RLIKE Supported. Same as [NOT] REGEXP.
8.1.1.5 Character Sets
GaussDB allows you to specify the following character sets for databases,
schemas, tables, or columns.
Table 8-19 Character sets
No.
MySQL GaussDB
1 utf8mb4 Supported
2 gbk Supported
3 gb18030 Supported
8.1.1.6 Collation Rules
GaussDB allows you to specify the following collation rules for schemas, tables, or
columns.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 464

NO TE
Dierences in collation rules:
● Currently, only the character string type and some binary types support the specied
collation rules. You can check whether the typcollation attribute of a type in the
pg_type system catalog is not 0 to determine whether the type supports the collation.
The collation can be specied for all types in MySQL. However, collation rules are
meaningless except those for character strings and binary types.
● The current collation rules can be specied only when the corresponding character set is
the same as the database-level character set.
● The default collation of the utf8mb4 character set is utf8mb4_general_ci, which is the
same as that in MySQL 5.7. utf8mb4_0900_ai_ci is not the default collation of utf8mb4.
● In GaussDB, utf8 and utf8mb4 are the same character set.
Table 8-20 Collation rules
No. MySQL GaussDB
1 utf8mb4_general_ci Supported.
2 utf8mb4_unicode_ci Supported.
3 utf8mb4_bin Supported.
4 gbk_chinese_ci Supported.
5 gbk_bin Supported.
6 gb18030_chinese_ci Supported.
7 gb18030_bin Supported.
8 binary Supported.
9 utf8mb4_0900_ai_ci Supported.
10 utf8_general_ci Supported.
11 utf8_bin Supported.
8.1.1.7 SQL
GaussDB is compatible with most MySQL syntax, but there are some dierences.
This chapter describes the MySQL syntax supported by GaussDB.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 465

8.1.1.7.1 DDL
N
o.
Introduction Syntax
Description
Dierence
1 Create primary keys
and UNIQUE
indexes during table
creation and
modication.
ALTER TABLE,
CREATE TABLE
● GaussDB does not support
the UNIQUE INDEX|KEY
index_name syntax. An error
will be reported when the
UNIQUE INDEX|KEY
index_name syntax is used.
However, MySQL supports
these functions.
● When a constraint is created
as a global secondary index
and USING BTREE is specied
in the SQL statement, the
underlying index is created as
UB-tree.
● When the table joined with
the constraint is Ustore and
USING BTREE is specied in
the SQL statement, the
underlying index is created as
UB-tree.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 466

N
o.
Introduction Syntax
Description
Dierence
2 Support prex
indexes.
CREATE INDEX ● The prex length cannot
exceed 2676. The actual
length of the key value is
restricted by the internal
page. If a column contains
multi-byte characters or an
index has multiple keys, an
error may be reported when
the index line length exceeds
the threshold.
● In the CREATE INDEX syntax,
the following keywords
cannot be used as prex keys
for column names:
COALESCE, EXTRACT,
GREATEST, LEAST, LNNVL,
NULLIF, NVL, NVL2,
OVERLAY, POSITION,
REGEXP_LIKE, SUBSTRING,
TIMESTAMPDIFF, TREAT,
TRIM, XMLCONCAT,
XMLELEMENT, XMLEXISTS,
XMLFOREST, XMLPARSE,
XMLPI, XMLROOT, and
XMLSERIALIZE.
● Prex keys are not supported
in primary key and unique
key indexes.
3
Specify character
sets and collation
rules.
ALTER SCHEMA,
ALTER TABLE,
CREATE SCHEMA,
CREATE TABLE
-
4 Compatible with
the syntax for
creating partitioned
tables.
CREATE TABLE
PARTITION,
CREATE TABLE
SUBPARTITION
-
5 Specify table-level
and column-level
comments during
table creation and
modication.
CREATE TABLE,
ALTER TABLE
-
6 Specify index-level
comments during
index creation.
CREATE INDEX -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 467
N
o.
Introduction Syntax
Description
Dierence
7 Exchange the
partition data of an
ordinary table and
a partitioned table.
ALTER TABLE
PARTITION
Dierences in ALTER TABLE
EXCHANGE PARTITION:
● If MySQL tables or partitions
use tablespaces, data in
partitions and ordinary tables
cannot be exchanged. If
GaussDB tables or partitions
use dierent tablespaces,
data in partitions and
ordinary tables can still be
exchanged.
● MySQL does not verify the
default values of columns.
Therefore, data in partitions
and ordinary tables can be
exchanged even if the default
values are dierent. GaussDB
veries the default values. If
the default values are
dierent, data in partitions
and ordinary tables cannot
be exchanged.
● After the DROP COLUMN
operation is performed on a
partitioned table or an
ordinary table in MySQL, if
the table structure is still
consistent, data can be
exchanged between
partitions and ordinary
tables. In GaussDB, data can
be exchanged between
partitions and ordinary tables
only when the deleted
columns of ordinary tables
and partitioned tables are
strictly aligned.
● MySQL and GaussDB use
dierent hash algorithms.
Therefore, data stored in the
same hash partition may be
inconsistent. As a result, the
exchanged data may also be
inconsistent.
● MySQL partitioned tables do
not support foreign keys. If
an ordinary table contains
foreign keys or other tables
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 468
N
o.
Introduction Syntax
Description
Dierence
reference foreign keys of an
ordinary table, data in
partitions and ordinary tables
cannot be exchanged.
GaussDB partitioned tables
support foreign keys. If the
foreign key constraints of two
tables are the same, data in
partitions and ordinary tables
can be exchanged. If a
GaussDB partitioned table
does not contain foreign
keys, an ordinary table is
referenced by other tables,
and the partitioned table is
the same as the ordinary
table, data in the partitioned
table can be exchanged with
that in the ordinary table.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 469

N
o.
Introduction Syntax
Description
Dierence
8 Support auto-
increment columns.
ALTER TABLE,
CREATE TABLE
● Currently, only local auto-
increment columns of each
DN are supported.
● It is recommended that the
auto-increment column be
the rst column of a non-
global secondary index.
Otherwise, an alarm is
generated when a table is
created, and errors may occur
when some operations are
performed on a table that
contains auto-increment
columns, for example, ALTER
TABLE EXCHANGE
PARTITION. The auto-
increment column in MySQL
must be the rst column of
the index.
● In the syntax
AUTO_INCREMENT = value,
value must be a positive
number less than 2^127.
MySQL does not verify the
value.
● An error occurs if the auto-
increment continues after an
auto-increment value reaches
the maximum value of a
column data type. In MySQL,
errors or warnings may be
generated during auto-
increment, and sometimes
auto-increment continues
until the maximum value is
reached.
● GaussDB does not support
the
innodb_autoinc_lock_mode
system variable, but when its
GUC parameter
auto_increment_cache is set
to 0, the behavior of
inserting auto-increment
columns in batches is similar
to that when the MySQL
system variable
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 470

N
o.
Introduction Syntax
Description
Dierence
innodb_autoinc_lock_mode
is
set to 1.
● When 0s, NULLs, and denite
values are imported or batch
inserted into auto-increment
columns, the auto-increment
values inserted after an error
occurs in GaussDB may not
be the same as those in
MySQL.
– The
auto_increment_cache
parameter is provided to
control the number of
reserved auto-increment
values.
● In dierent execution plans,
the auto-increment sequence
and reserved auto-increment
values may be dierent from
those in MySQL. For
example, "INSERT INTO table
VALUES(...),(...),..." is
distributed to dierent DNs.
Therefore, in some execution
plans, DNs cannot obtain the
number of rows to be
inserted.
– The
auto_increment_cache
parameter is provided to
control the number of
reserved auto-increment
values.
● When auto-increment is
triggered by parallel import
or insertion of auto-
increment columns, the
cache value reserved for each
parallel thread is used only in
the thread. If the cache value
is not used up, the values of
auto-increment columns in
the table are discontinuous.
The auto-increment value
generated by parallel
insertion cannot be
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 471

N
o.
Introduction Syntax
Description
Dierence
guaranteed to be the same
as that generated in MySQL.
● The SERIAL data type of
GaussDB is an original auto-
increment column, which is
dierent from the
AUTO_INCREMENT column.
The SERIAL data type of
MySQL is the
AUTO_INCREMENT column.
● The value of
auto_increment_oset
cannot be greater than that
of
auto_increment_increment.
Otherwise, an error occurs.
MySQL allows it and states
that auto_increment_oset
will be ignored.
● If a table has a primary key
or index, the sequence in
which the ALTER TABLE
command rewrites table data
may be dierent from that in
MySQL. GaussDB rewrites
table data based on the table
data storage sequence, while
MySQL rewrites table data
based on the primary key or
index sequence. As a result,
the auto-increment sequence
may be dierent.
● When the ALTER TABLE
command is used to add or
modify auto-increment
columns, the number of
auto-increment values
reserved for the rst time is
the number of rows in the
table statistics. The number
of rows in the statistics may
not be the same as that in
MySQL.
● When auto-increment is
performed in a trigger or
user-dened function, the
return value of last_insert_id
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 472

N
o.
Introduction Syntax
Description
Dierence
is updated. MySQL does not
update it.
● If the values of the GUC
parameters
auto_increment_oset and
auto_increment_increment
are out of range, an error
occurs. MySQL automatically
changes the value to a
boundary value.
● The last_insert_id function is
not supported.
● Currently, local temporary
tables do not support auto-
increment columns.
9 Delete the primary
key constraints of a
table.
ALTER TABLE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 473

N
o.
Introduction Syntax
Description
Dierence
1
0
Compatible with
the CREATE TABLE...
LIKE syntax.
CREATE TABLE ...
LIKE
● In versions earlier than
MySQL 8.0.16, CHECK
constraints are parsed but
their functions are ignored. In
this case, CHECK constraints
are not replicated. GaussDB
supports replication of
CHECK constraints.
● For the set data type, MySQL
supports replication while
GaussDB does not during
table creation.
● When a table is created, all
primary key constraint names
in MySQL are xed to
PRIMARY KEY. GaussDB does
not support replication of
primary key constraint
names.
● When a table is created,
MySQL supports replication
of unique key constraint
names, but GaussDB does
not.
● When a table is created,
MySQL versions earlier than
8.0.16 do not have CHECK
constraint information, but
GaussDB supports replication
of CHECK constraint names.
● When a table is created,
MySQL supports replication
of index names, but GaussDB
does not.
● When a table is created
across sql_mode, MySQL is
controlled by the loose mode
and strict mode. The strict
mode may become invalid in
GaussDB.
For example, if the source
table has the default value
"0000-00-00", GaussDB can
create a table that contains
the default value
"0000-00-00" in
"no_zero_date" strict mode,
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 474
N
o.
Introduction Syntax
Description
Dierence
which means that the strict
mode is invalid. MySQL fails
to create the table because it
is controlled by the strict
mode.
● MySQL supports cross-
database table creation, but
GaussDB does not.
● If the source table is a
temporary table, you can
create a non-temporary table
in MySQL but not in
GaussDB.
1
1
Compatible with
syntax for changing
table names.
ALTER TABLE[ IF
EXISTS ] tbl_name
RENAME [TO | AS
| =]
new_tbl_name;
RENAME {TABLE |
TABLES} tbl_name
TO new_tbl_name
[, tbl_name2 TO
new_tbl_name2, ...
];
● The ALTER RENAME syntax in
GaussDB supports only the
function of changing the
table name and cannot be
coupled with other function
operations.
● In GaussDB, only the old
table name column supports
the usage of
schema.table_name, and the
new and old table names
belong to the same schema.
● GaussDB does not support
renaming of old and new
tables across schemas.
However, if you have the
permission, you can modify
the names of tables in other
schemas in the current
schema.
● The syntax for renaming
multiple groups of tables in
GaussDB supports renaming
of all local temporary tables,
but does not support the
combination of local
temporary tables and non-
local temporary tables.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 475

N
o.
Introduction Syntax
Description
Dierence
1
2
Compatible with
the subpartition
addition syntax.
ALTER TABLE [ IF
EXISTS ]
{ table_name [*] |
ONLY table_name
| ONLY
( table_name )}
action [, ... ];
action:
move_clause |
exchange_clause |
row_clause |
merge_clause |
modify_clause |
split_clause |
add_clause |
drop_clause |
ilm_clause
add_clause:
ADD
{{partition_less_th
an_item |
partition_start_en
d_item |
partition_list_item
} |
PARTITION({partit
ion_less_than_ite
m |
partition_start_en
d_item |
partition_list_item
})}
● The ALTER TABLE table_name
ADD PARTITION
(partition_denition1,
partition_denition1,…);
syntax cannot be used to add
multiple partitions.
● Only the original syntax for
adding multiple partitions is
supported: ALTER TABLE
table_name ADD PARTITION
(partition_denition1), ADD
PARTITION
(partition_denition2[y1] ),
…;.
8.1.1.7.2 DML
No.
Introduction Syntax
Descriptio
n
Dierence
1 DELETE supports
ORDER BY and LIMIT.
DELETE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 476

No. Introduction Syntax
Descriptio
n
Dierence
2 UPDATE supports
ORDER BY and LIMIT.
UPDATE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 477
No. Introduction Syntax
Descriptio
n
Dierence
3 The syntax is
compatible with
REPLACE INTO.
REPLACE ● Dierence between the initial
values of the time type. For
example:
– MySQL is not aected by
the strict or loose mode.
You can insert time 0 into
a table.
mysql> CREATE TABLE test(f1
TIMESTAMP NOT NULL, f2
DATETIME NOT NULL, f3 DATE
NOT NULL);
Query OK, 1 row aected (0.00 sec)
mysql> REPLACE INTO test
VALUES(f1, f2, f3);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+---------------------
+---------------------+------------+
| f1 | f2 |
f3 |
+---------------------
+---------------------+------------+
| 0000-00-00 00:00:00 | 0000-00-00
00:00:00 | 0000-00-00 |
+---------------------
+---------------------+------------+
1 row in set (0.00 sec)
– The time 0 can be
successfully inserted only
when GaussDB is in loose
mode.
gaussdb=# SET b_format_version =
'5.7';
SET
gaussdb=# SET
b_format_dev_version = 's1';
SET
gaussdb=# SET sql_mode = '';
SET
gaussdb=# CREATE TABLE test(f1
TIMESTAMP NOT NULL, f2
DATETIME NOT NULL, f3 DATE
NOT NULL) DISTRIBUTE BY
HASH(f1);
CREATE TABLE
gaussdb=# REPLACE INTO test
VALUES(f1, f2, f3);
REPLACE 0 1
gaussdb=# SELECT * FROM test;
f1 | f2 | f3
---------------------
+---------------------+------------
0000-00-00 00:00:00 | 0000-00-00
00:00:00 | 0000-00-00
(1 row)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 478

No. Introduction Syntax
Descriptio
n
Dierence
In strict mode, the error is
reported: date/time eld
value out of range:
"0000-00-00 00:00:00".
● Dierence between the initial
values of the BIT type when
NOT NULL exists. For
example:
– The initial value of the BIT
type is an empty string '' in
MySQL, that is:
mysql> CREATE TABLE test(f1
BIT(3) NOT NULL);
Query OK, 0 rows aected (0.01
sec)
mysql> REPLACE INTO test
VALUES(f1);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT f1, f1 IS NULL
FROM test;
+----+------------+
| f1 | f1 is null |
+----+------------+
| | 0 |
| | 0 |
+----+------------+
2 rows in set (0.00 sec)
– If the initial value of the
BIT type is NULL in
GaussDB, an error is
reported.
gaussdb=# CREATE TABLE test(f1
int, f2 BIT(3) NOT NULL)
DISTRIBUTE BY HASH(f1);
CREATE TABLE
gaussdb=# REPLACE INTO test
VALUES(1, f2);
ERROR: null value in column "f2"
violates not-null constraint
DETAIL: Failing row contains (1,
null).
4
SELECT supports multi-
partition query.
SELECT -
5 UPDATE supports
multi-partition update.
UPDATE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 479

No. Introduction Syntax
Descriptio
n
Dierence
6 Import data by using
LOAD DATA.
LOAD
DATA
● The execution result of the
LOAD DATA syntax is the
same as that in MySQL strict
mode. The loose mode is not
adapted currently.
● The IGNORE and LOCAL
parameters are used only to
ignore the conicting rows
when the imported data
conicts with the data in the
table and to automatically ll
default values for other
columns when the number of
columns in the le is less than
the number of columns in the
table. Other functions are not
supported currently.
● If the keyword LOCAL is
specied and the le path is a
relative path, the le is
searched from the binary
directory. If the keyword
LOCAL is not specied and
the le path is a relative path,
the le is searched from the
data directory.
● If single quotation marks are
specied as separators, escape
characters, and line breaks in
the syntax, lexical parsing
errors occur.
● The [(col_name_or_user_var
[, col_name_or_user_var]...)]
parameter cannot be used to
specify a column repeatedly.
● The line break specied by
[FIELDS TERMINATED BY
'string'] cannot be the same
as the separator specied by
[LINES TERMINATED
BY'string'].
● If the data written to a table
by running LOAD DATA
cannot be converted to the
data type of the table, an
error is reported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 480

No. Introduction Syntax
Descriptio
n
Dierence
● Columns can only be specied
by column name instead of
user variables.
● The LOAD DATA SET
expression does not support
the calculation of a specied
column name.
● If no implicit conversion
function exists between the
return value type of the SET
expression and the
corresponding column type,
an error is reported.
● LOAD DATA does not support
the INSERT or DELETE trigger.
● LOAD DATA applies only to
tables but not views.
● The default newline character
of the le in Windows is
dierent from that in Linux.
LOAD DATA cannot identify
this scenario and reports an
error. You are advised to check
the newline character at the
end of lines of the le to be
imported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 481
No. Introduction Syntax
Descriptio
n
Dierence
7 Compatible with
INSERT IGNORE.
INSERT
IGNORE
● GaussDB displays the error
information after the
downgrade. MySQL records
the error information after
the downgrade to the error
stack and runs the show
warnings; command to view
the error information.
● Time type dierence. For
example:
– The default values of date,
datetime, and timestamp
in GaussDB are 0.
gaussdb=# CREATE TABLE test(f1
DATE NOT NULL, f2 DATETIME
NOT NULL, f3 TIMESTAMP NOT
NULL);
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test VALUES(NULL, NULL, NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null,
null, null, null).
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (null,
null, null, null).
WARNING: null value in column
"f3" violates not-null constraint
DETAIL: Failing row contains (null,
null, null, null).
INSERT 0 1
gaussdb=#
SELECT * FROM test;
f1 | f2 |
f3
------------+---------------------
+---------------------
1970-01-01 | 1970-01-01 00:00:00
| 1970-01-01 00:00:00
(1 row)
– The default values of date,
datetime, and timestamp
in MySQL are 0.
mysql> CREATE TABLE test(f1
DATE NOT NULL, f2 DATETIME
NOT NULL, f3 TIMESTAMP NOT
NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
VALUES(NULL, NULL, NULL);
Query OK, 1 row aected, 3
warnings (0.00 sec)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 482
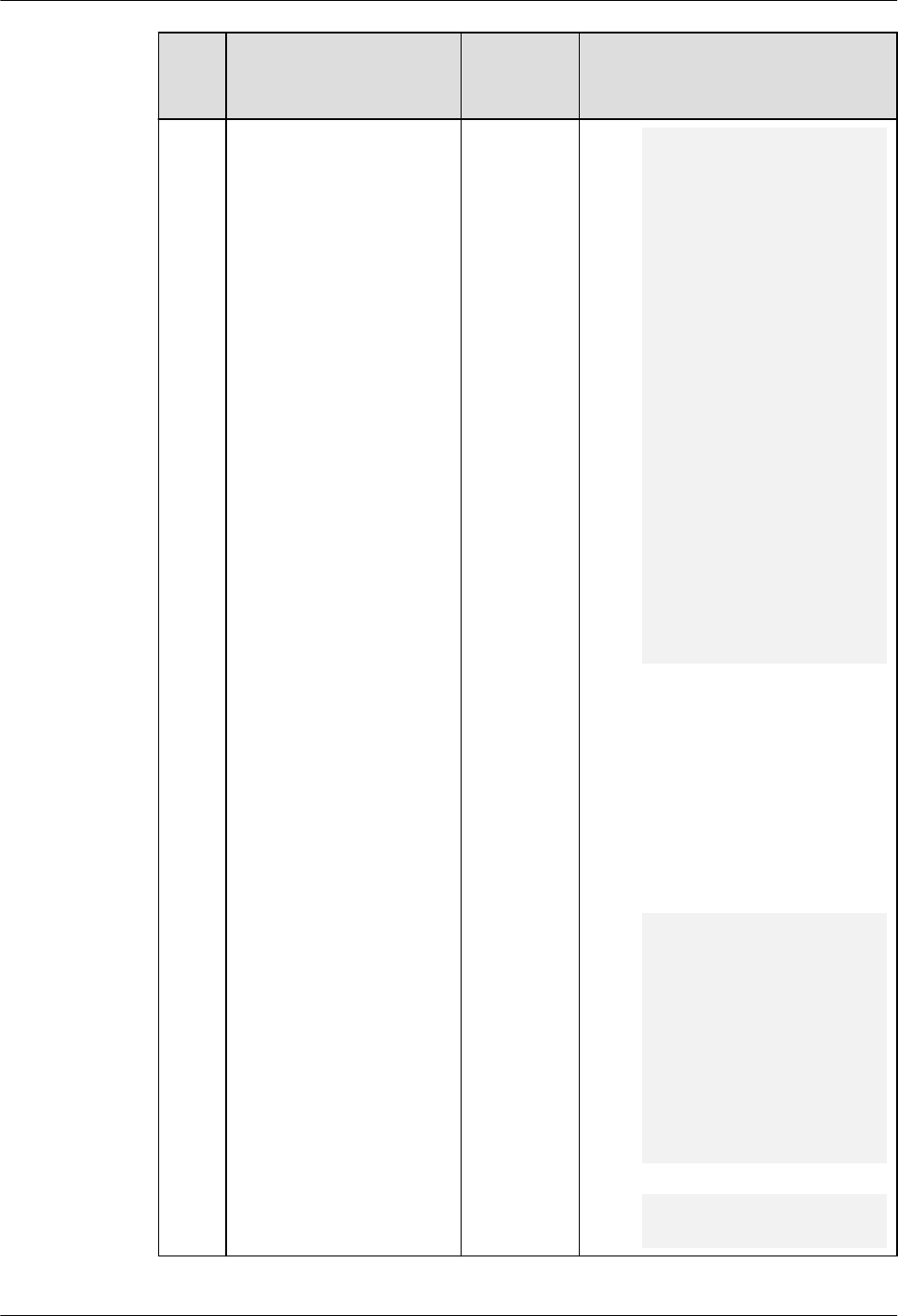
No. Introduction Syntax
Descriptio
n
Dierence
mysql> show warnings;
+---------+------
+----------------------------+
| Level | Code |
Message |
+---------+------
+----------------------------+
| Warning | 1048 | Column 'f1'
cannot be null |
| Warning | 1048 | Column 'f2'
cannot be null |
| Warning | 1048 | Column 'f3'
cannot be null |
+---------+------
+----------------------------+
3 rows in set (0.00 sec)
mysql> SELECT * FROM test;
+------------+---------------------
+---------------------+
| f1 | f2 |
f3 |
+------------+---------------------
+---------------------+
| 0000-00-00 | 0000-00-00 00:00:00
| 0000-00-00 00:00:00 |
+------------+---------------------
+---------------------+
1 row in set (0.00 sec)
● GaussDB does not support the
MySQL bit type. Therefore,
the INSERT IGNORE error
downgrade is not supported
when the NOT NULL
constraint of the bit type is
ignored and the length of the
inserted bit type is dierent
from that dened.
– Bit type in GaussDB
gaussdb=# CREATE TABLE test(f1
BIT(10) NOT NULL);
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test VALUES(NULL);
ERROR: Un-support feature
DETAIL: ignore null for insert
statement is not supported in
column f1.
gaussdb=# INSERT IGNORE INTO
test VALUES('1010');
ERROR: bit string length 4 does
not match type bit(10)
CONTEXT: referenced column: f1
– Bit type in MySQL
mysql> CREATE TABLE test(f1
BIT(10) NOT NULL);
Query OK, 0 rows aected (0.00
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 483

No. Introduction Syntax
Descriptio
n
Dierence
sec)
mysql> INSERT IGNORE INTO test
VALUES(NULL);
Query OK, 1 row aected, 1
warning (0.00 sec)
mysql> INSERT IGNORE INTO test
VALUES('1010');
Query OK, 1 row aected, 1
warning (0.01 sec)
● If the precision is specied for
the time type in MySQL, the
precision is displayed when
the zero value is inserted. It is
not displayed in GaussDB. For
example:
– Time precision specied in
GaussDB
gaussdb=# CREATE TABLE test(f1
TIME(3) NOT NULL, f2
DATETIME(3) NOT NULL, f3
TIMESTAMP(3) NOT NULL);
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test VALUES(NULL,NULL,NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null,
null, null).
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (null,
null, null).
WARNING: null value in column
"f3" violates not-null constraint
DETAIL: Failing row contains (null,
null, null).
INSERT 0 1
gaussdb=# SELECT * FROM test;
f1 | f2 | f3
----------+---------------------
+---------------------
00:00:00 | 1970-01-01 00:00:00 |
1970-01-01 00:00:00
(1 row)
– Time precision specied in
MySQL
mysql> CREATE TABLE test(f1
TIME(3) NOT NULL, f2
DATETIME(3) NOT NULL, f3
TIMESTAMP(3) NOT NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
VALUES(NULL,NULL,NULL);
Query OK, 1 row aected, 3
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 484
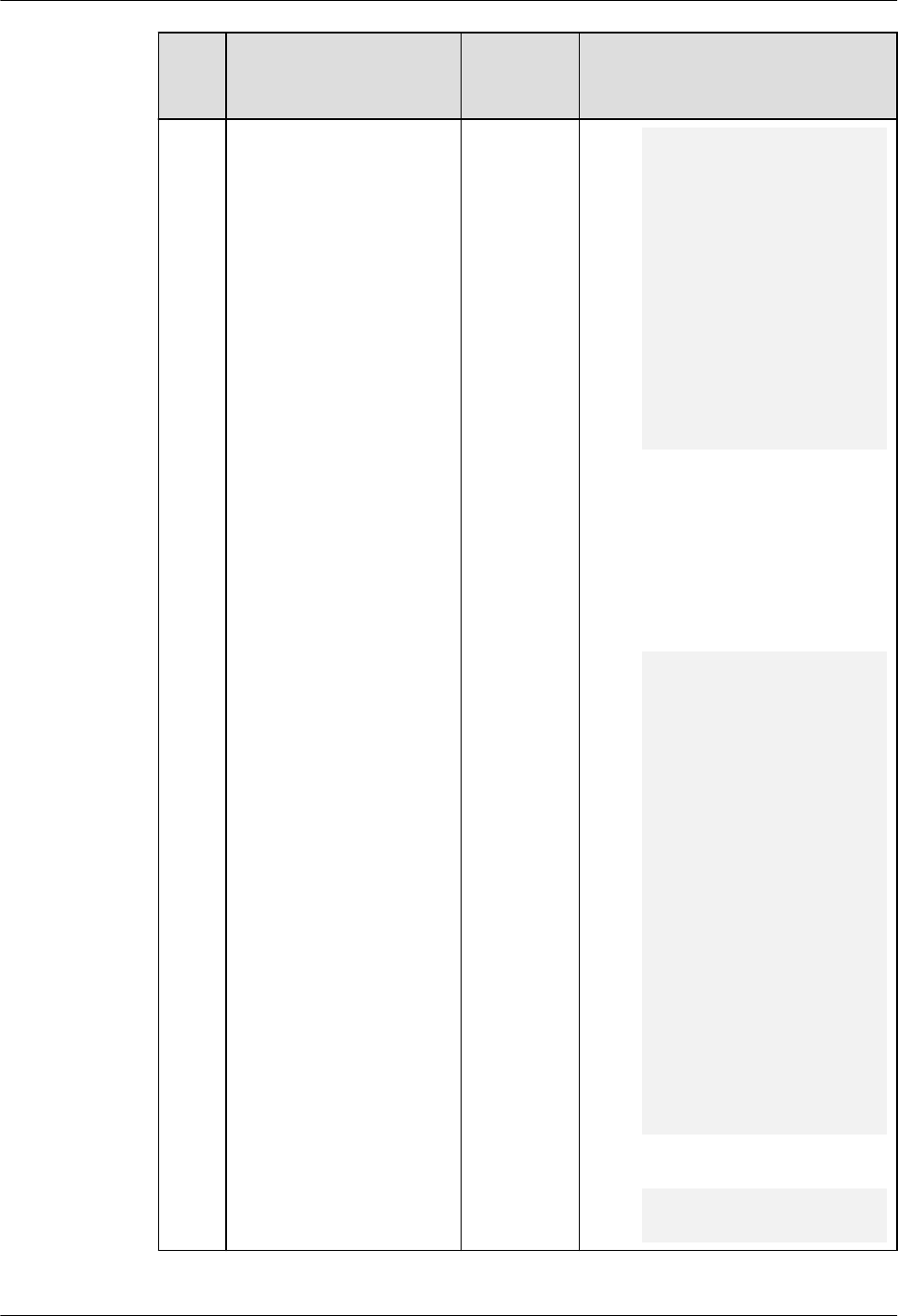
No. Introduction Syntax
Descriptio
n
Dierence
warnings (0.00 sec)
mysql> SELECT * FROM test;
+--------------
+-------------------------
+-------------------------+
| f1 | f2 |
f3 |
+--------------
+-------------------------
+-------------------------+
| 00:00:00.000 | 0000-00-00
00:00:00.000 | 0000-00-00
00:00:00.000 |
+--------------
+-------------------------
+-------------------------+
1 row in set (0.00 sec)
● The execution process in
MySQL is dierent from that
in GaussDB. Therefore, the
number of generated
warnings may be dierent.
For example:
– Number of warnings
generated in GaussDB
gaussdb=# CREATE TABLE test(f1
INT, f2 INT not null);
CREATE TABLE
gaussdb=# INSERT INTO test
VALUES(1,0),(3,0),(5,0);
INSERT 0 3
gaussdb=# INSERT IGNORE INTO
test SELECT f1+1, f1/f2 FROM test;
WARNING: division by zero
CONTEXT: referenced column: f2
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (2,
null).
WARNING: division by zero
CONTEXT: referenced column: f2
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (4,
null).
WARNING: division by zero
CONTEXT: referenced column: f2
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (6,
null).
INSERT 0 3
– Number of warnings
generated in MySQL
mysql> CREATE TABLE test(f1 INT,
f2 INT not null);
Query OK, 0 rows aected (0.01
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 485

No. Introduction Syntax
Descriptio
n
Dierence
sec)
mysql> INSERT INTO test
VALUES(1,0),(3,0),(5,0);
Query OK, 3 rows aected (0.00
sec)
Records: 3 Duplicates: 0
Warnings: 0
mysql> INSERT IGNORE INTO test
SELECT f1+1, f1/f2 FROM test;
Query OK, 3 rows aected, 4
warnings (0.00 sec)
Records: 3 Duplicates: 0
Warnings: 4
● The dierences between
MySQL's and GaussDB's
INSERT IGNORE in triggers
are as follows:
– INSERT IGNORE used in a
GaussDB trigger
gaussdb=# CREATE TABLE test1(f1
INT NOT NULL);
CREATE TABLE
gaussdb=# CREATE TABLE test2(f1
INT);
CREATE TABLE
gaussdb=# CREATE OR REPLACE
FUNCTION trig_test() RETURNS
TRIGGER AS $$
gaussdb$# BEGIN
gaussdb$# INSERT IGNORE INTO
test1 VALUES(NULL);
gaussdb$# RETURN NEW;
gaussdb$# END;
gaussdb$# $$ LANGUAGE plpgsql;
CREATE FUNCTION
gaussdb=# CREATE TRIGGER trig2
BEFORE INSERT ON test2 FOR
EACH ROW EXECUTE PROCEDURE
trig_test();
CREATE TRIGGER
gaussdb=# INSERT INTO test2
VALUES(NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null).
CONTEXT: SQL statement "INSERT
IGNORE INTO test1
VALUES(NULL)"
PL/pgSQL function trig_test() line
3 at SQL statement
INSERT 0 1
gaussdb=# SELECT * FROM test1;
f1
----
0
(1 rows)
gaussdb=# SELECT * FROM test2;
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 486

No. Introduction Syntax
Descriptio
n
Dierence
f1
----
(1 rows)
– INSERT IGNORE used in a
MySQL trigger
mysql> CREATE TABLE test1(f1 INT
NOT NULL);
Query OK, 0 rows aected (0.01
sec)
mysql> CREATE TABLE test2(f1
INT);
Query OK, 0 rows aected (0.00
sec)
mysql> DELIMITER ||
mysql> CREATE TRIGGER trig2
BEFORE INSERT ON test2 FOR
EACH ROW
-> BEGIN
-> INSERT IGNORE into test1
values(NULL);
-> END||
Query OK, 0 rows aected (0.01
sec)
mysql> DELIMITER ;
mysql> INSERT INTO test2
VALUES(NULL);
ERROR 1048 (23000): Column 'f1'
cannot be null
mysql> INSERT IGNORE INTO test2
VALUES(NULL);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test1;
+----+
| f1 |
+----+
| 0 |
+----+
1 row in set (0.00 sec)
mysql> SELECT * FROM test2;
+------+
| f1 |
+------+
| NULL |
+------+
1 row in set (0.00 sec)
● The implementation
mechanism of Boolean and
serial in GaussDB is dierent
from that in MySQL.
Therefore, the default zero
value in GaussDB is dierent
from that in MySQL. For
example:
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 487

No. Introduction Syntax
Descriptio
n
Dierence
– Behavior in GaussDB
gaussdb=# CREATE TABLE test(f1
SERIAL, f2 BOOL NOT NULL);
NOTICE: CREATE TABLE will create
implicit sequence "test_f1_seq" for
serial column "test.f1"
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test values(NULL,NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null,
null).
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (null,
null).
INSERT 0 1
gaussdb=# SELECT * FROM test;
f1 | f2
----+----
0 | f
(1 row)
– Behavior in MySQL
mysql> CREATE TABLE test(f1
SERIAL, f2 BOOL NOT NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
values(NULL,NULL);
Query OK, 1 row aected, 1
warning (0.00 sec)
mysql> SELECT * FROM test;
+----+----+
| f1 | f2 |
+----+----+
| 1 | 0 |
+----+----+
1 row in set (0.00 sec)
8.1.1.7.3 DCL
No.
Introduction Syntax Description Dierence
1 Set names with
COLLATE specied.
SET [ SESSION |
LOCAL ] NAMES
{'charset_name'
[COLLATE
'collation_name'] |
DEFAULT};
GaussDB does not allow
charset_name to be
dierent from the
database character set.
For details, see "SQL
Reference > SQL Syntax >
S > SET" in
Developer
Guide
.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 488
8.1.1.8 Drivers
8.1.1.8.1 JDBC
JDBC API Reference
Obtaining Data from a Result Set
ResultSet objects provide a variety of methods to obtain data from a result set.
Table 8-21 describes the common methods for obtaining data. If you want to
know more about other methods, see JDK ocial documents.
Table 8-21 Common methods for obtaining data from a result set
Method Description Dierence
int getInt(int
columnIndex)
Obtains int
data by
column
index.
-
int getInt(String
columnLabel)
Obtains int
data by
column
name.
-
String
getString(int
columnIndex)
Obtains
string data
by column
index.
If the column type is integer and the column
contains the ZEROFILL attribute, GaussDB
pads 0s to meet the width required by the
ZEROFILL attribute and outputs the result.
MySQL directly outputs the result.
String
getString(String
columnLabel)
Obtains
string data
by column
name.
If the column type is integer and the column
contains the ZEROFILL attribute, GaussDB
pads 0s to meet the width required by the
ZEROFILL attribute and outputs the result.
MySQL directly outputs the result.
Date getDate(int
columnIndex)
Obtains
date data
by column
index.
-
Date
getDate(String
columnLabel)
Obtains
date data
by column
name.
-
8.2 Primary/Standby Instances
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 489
8.2.1 Introduction
This document compares GaussDB (B-compatible mode and M-compatible mode)
with MySQL 5.7. MySQL Compatibility in B-Compatible Mode describes the
MySQL compatibility in B-compatible mode, and MySQL Compatibility in M-
Compatible Mode describes the MySQL compatibility in M-compatible mode.
8.2.2 MySQL Compatibility in B-Compatible Mode
8.2.2.1 MySQL Compatibility Overview
This chapter compares the MySQL 5.7 compatibility mode in GaussDB (that is,
when sql_compatibility is set to 'B', b_format_version is set to '5.7', and
b_format_dev_version is set to 's1') with MySQL 5.7. Only compatibility features
added later than GaussDB Kernel 503.0.0 are described. You are advised to view
the specications and restrictions of the features in
Developer Guide
.
GaussDB is compatible with MySQL in terms of data types, SQL functions, and
database objects.
The underlying framework implementation of the GaussDB is dierent from that
of MySQL. Therefore, there are still some dierences between GaussDB and
MySQL.
8.2.2.2 Data Types
The data types of GaussDB are the same as those of MySQL in most function
scenarios, but there are some dierences.
● Unless otherwise specied, the precision, scale, and number of bits of some
data types cannot be dened as oating-point values. You are advised to use
valid integer values.
8.2.2.2.1 Numeric Data Types
Table 8-22 Integer types
No.
MySQL GaussDB Dierence
1 BOOL Not fully
compatible.
MySQL: The BOOL/BOOLEAN type is
actually mapped to the TINYINT type.
GaussDB: BOOL is supported.
● Valid literal values for the "true" state
include: TRUE, 't', 'true', 'y', 'yes', '1',
'TRUE', true, 'on', and all non-zero
values.
● Valid literal values for the "false" state
include: FALSE, 'f', 'false', 'n', 'no', '0', 0,
'FALSE', false, and 'o'.
TRUE and FALSE are standard expressions,
compatible with SQL statements.
2 BOOLEAN Not fully
compatible.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 490

No. MySQL GaussDB Dierence
3 TINYINT[(M
)]
[UNSIGNED
]
Supported. For details, see the following note.
4 SMALLINT[(
M)]
[UNSIGNED
]
Supported. For details, see the following note.
5 MEDIUMIN
T[(M)]
[UNSIGNED
]
Supported. MySQL requires 3 bytes to store
MEDIUMINT data.
● The signed range is –8388608 to
+8388607.
● The unsigned range is 0 to +16777215.
GaussDB maps data to the INT type and
requires 4 bytes for storage.
● The signed range is –2147483648 to
+2147483647.
● The unsigned range is 0 to
+4294967295.
For other dierences, see the following
note.
6 INT[(M)]
[UNSIGNED
]
Supported. For details, see the following note.
7 INTEGER[(M
)]
[UNSIGNED
]
Supported. For details, see the following note.
8 BIGINT[(M)
]
[UNSIGNED
]
Supported. For details, see the following note.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 491

NO TE
● Input formats:
● MySQL
For characters such as "asbd", "12dd", and "12 12", the system truncates them or
returns 0 and reports a WARNING message. Data fails to be inserted into a table in
strict mode.
● GaussDB
● For integer types (TINYINT, SMALLINT, MEDIUMINT, INT, INTEGER, and
BIGINT), if the invalid part of a character string is truncated, for example,
"12@3", no message is displayed. Data is successfully inserted into a table.
● If the whole integer is truncated (for example, "@123") or the character
string is empty, 0 is returned and data is successfully inserted into a table.
● Operators:
● +, -, and *
GaussDB: When INT, INTEGER, SMALLINT, or BIGINT is used for calculation, a value
of the original type is returned and is not changed to a larger type. If the return
value exceeds the range, an error is reported.
MySQL: The value can be changed to BIGINT for calculation.
● |, &, ^, and ~
GaussDB: The value is calculated in the bits occupied by the type. In GaussDB, ^
indicates the exponentiation operation. If the XOR operator is required, replace it
with #.
MYSQL: The value is changed to a larger type for calculation.
● Type conversion of negative numbers:
GaussDB: The result is 0 in loose mode and an error is reported in strict mode.
MySQL: The most signicant bit is replaced with a numeric bit based on the
corresponding binary value, for example, (-1)::uint4 = 4294967295.
● Other dierences:
The precision of INT[(M)] controls formatted output in MySQL. GaussDB supports only
the syntax but does not support the function.
● Aggregate function:
● variance: indicates the sample variance in GaussDB and the population variance in
MySQL.
● stddev: indicates the sample standard deviation in GaussDB and the overall
standard deviation in MySQL.
● Display width:
● If ZEROFILL is not specied when the width information is specied for an integer
column, the width information is not displayed in the table structure description.
● When the INSERT statement is used to insert a column of the character type,
GaussDB pads 0s before inserting the column.
● The JOIN USING statement involves type derivation. In MySQL, the rst table
column is used by default. In GaussDB, if the result is of the signed type, the width
information is invalid. Otherwise, the width of the rst table column is used.
● For GREATEST/LEAST, IFNULL/IF, and CASE WHEN/DECODE, MySQL does not pad
0s. In GaussDB, 0s are padded when the type and width information is consistent.
● MySQL supports this function when it is used as the input or output parameter or
return value of a function or stored procedure. GaussDB neither reports syntax
errors nor supports this function.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 492

Table 8-23 Arbitrary precision types
No. MySQL GaussDB Dierence
1 DECIMAL[(
M[,D])]
Supported. ● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Input format: No error is reported when
all input parameters of a character string
(for example, '@123') are truncated. An
error is reported only when it is partially
truncated, for example, '12@3'.
2 NUMERIC[(
M[,D])]
Supported.
3 DEC[(M[,D])
]
Supported.
4 FIXED[(M[,D
])]
Not
supported
-
Table 8-24 Floating-point types
No.
MySQL GaussDB Dierence
1 FLOAT[(M,D
)]
Supported. ● Partitioned table: The FLOAT data type
does not support partitioned tables with
the key partitioning policy.
● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 493
No. MySQL GaussDB Dierence
2 FLOAT(p) Supported. ● Partitioned table: The FLOAT data type
does not support partitioned tables with
the key partitioning policy.
● Operator: The ^ operator is used for the
numeric types, which is dierent from
that in MySQL. In GaussDB, the ^
operator is used for exponential
calculation.
● Value range: When the precision p is
dened, only valid integer data types are
supported.
● Output format: The precision M and
scale D support only integers and do not
support oating-point values.
● An ERROR message is reported for
invalid input parameters. No WARNING
message is reported in loose mode (that
is, sql_mode is set to '').
3 DOUBLE[(M
,D)]
Supported. ● Partitioned table: The DOUBLE data type
does not support partitioned tables with
the key partitioning policy.
● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
4 DOUBLE
PRECISION[(
M,D)]
Supported. ● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 494

No. MySQL GaussDB Dierence
5 REAL[(M,D)
]
Supported. ● Partitioned table: The REAL data type
does not support partitioned tables with
the key partitioning policy.
● Operator: In GaussDB, "^" indicates the
exponentiation operation. If the XOR
operator is required, replace it with "#".
In MySQL, "^" indicates the XOR
operation.
● Value range: The precision M and scale
D support only integers and do not
support oating-point values.
● Output format: An ERROR message is
reported for invalid input parameters. No
WARNING message is reported in loose
mode (that is, sql_mode is set to '').
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 495
Table 8-25 Sequential integers
No. MySQL GaussDB Dierence
1 SERIAL Not fully
compatible.
For details about SERIAL, see section
"Numeric Data Types" in
GaussDB
Developer Guide
.
The dierences in specications are as
follows:
CREATE TABLE test(f1 serial, f2 CHAR(20));
● The SERIAL of MySQL is mapped to
BIGINT(20) UNSIGNED NOT NULL
AUTO_INCREMENT UNIQUE, and the
SERIAL of GaussDB is mapped to
INTEGER NOT NULL DEFAULT
nextval('test_f1_seq'::regclass). For
example:
-- Denition of MySQL SERIAL:
mysql> SHOW CREATE TABLE test\G
*************************** 1. row ***************************
Table: test
Create Table: CREATE TABLE `test` (
`f1` bigint(20) unsigned NOT NULL
AUTO_INCREMENT,
`f2` char(20) DEFAULT NULL,
UNIQUE KEY `f1` (`f1`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8
1 row in set (0.00 sec)
-- Denition of GaussDB SERIAL
gaussdb=# \d+ test
Table "public.test"
Column | Type |
Modiers | Storage | Stats target |
Description
--------+---------------
+---------------------------------------------------
+----------+--------------+-------------
f1 | integer | not null default
nextval('test_f1_seq'::regclass) | plain | |
f2 | character(20)
| | extended
| |
Has OIDs: no
Options: orientation=row, compression=no,
storage_type=USTORE
● The default values of the SERIAL type in
the INSERT scenario are dierent. For
example:
-- The inserted default value of the SERIAL type in
MySQL
mysql> INSERT INTO test VALUES(DEFAULT, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> INSERT INTO test VALUES(10, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> INSERT INTO test VALUES(DEFAULT, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+----+------+
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 496

No. MySQL GaussDB Dierence
| f1 | f2 |
+----+------+
| 1 | aaaa |
| 10 | aaaa |
| 11 | aaaa |
+----+------+
3 rows in set (0.00 sec)
-- The inserted default value of the SERIAL type in
GaussDB
gaussdb=# INSERT INTO test VALUES(DEFAULT,
'aaaa');
INSERT 0 1
gaussdb=# INSERT INTO test VALUES(10, 'aaaa');
INSERT 0 1
gaussdb=# INSERT INTO test VALUES(DEFAULT,
'aaaa');
INSERT 0 1
gaussdb=# SELECT * FROM test;
f1 | f2
----+----------------------
1 | aaaa
2 | aaaa
10 | aaaa
(3 rows)
● The reference columns of the SERIAL
type in the REPLACE scenario are
dierent. For details about the GaussDB
reference columns, see section
"REPLACE" in
GaussDB Developer Guide
.
For example:
-- The inserted reference column value of the SERIAL
type in MySQL
mysql> REPLACE INTO test VALUES(f1, 'aaaa');
Query OK, 1 row aected (0.00 sec)
mysql> REPLACE INTO test VALUES(f1, 'bbbb');
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+----+------+
| f1 | f2 |
+----+------+
| 1 | aaaa |
| 2 | bbbb |
+----+------+
2 rows in set (0.00 sec)
-- The inserted reference column value of the SERIAL
type in GaussDB
gaussdb=# REPLACE INTO test VALUES(f1, 'aaaa');
REPLACE 0 1
gaussdb=# REPLACE INTO test VALUES(f1, 'bbbb');
REPLACE 0 1
gaussdb=# SELECT * FROM test;
f1 | f2
----+----------------------
0 | aaaa
0 | bbbb
(2 rows)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 497

8.2.2.2.2 Date and Time Data Types
Table 8-26 Date and time data types
No. MySQL GaussDB Dierence
1 DATE Supported. GaussDB supports the date data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input format
– GaussDB supports only the character
type and does not support the
numeric type. For example, the
format can be '2020-01-01' or
'20200101', but cannot be 20200101.
MySQL supports conversion from
numeric input to the date type.
– Separator: GaussDB does not support
the plus sign (+) or colon (:) as the
separator between the year, month,
and day. Other symbols are
supported. MySQL supports all
symbols as separators. Sometimes,
the mixed use of separators is not
supported, which is dierent from
MySQL, such as '2020-01>01' and
'2020/01+01'. You are advised to use
hyphens (-) or slashes (/) as
separators.
– No separator: You are advised to use
the complete format, for example,
'YYYYMMDD' or 'YYMMDD'. The
parsing rules of incomplete formats
(including the ultra-long format) are
dierent from those of MySQL. An
error may be reported or the parsing
result may be inconsistent with that
of MySQL. Therefore, the incomplete
format is not recommended.
● Output format
If the sql_mode parameter of GaussDB
does not contain 'strict_trans_tables'
(the strict mode is used unless otherwise
dened as the loose mode), the year,
month, and day can be set to 0.
However, the value is converted to a
valid value in the sequence of year,
month, and day. For example, date
'0000-00-10' is converted to 0002-12-10
BC. If the input is invalid or exceeds the
range, a warning message is reported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 498

No. MySQL GaussDB Dierence
and the value 0000-00-00 is returned.
MySQL outputs the date value as it is,
even if the year, month, and day are set
to 0.
● Value range
The value range of GaussDB is
4713-01-01 BC to 5874897-12-31 AD.
BC dates are supported. In loose mode,
if the value exceeds the range,
0000-00-00 is returned. In strict mode,
an error is reported. The value range of
MySQL is 0000-00-00 to 9999-12-31. In
loose mode, if the value exceeds the
range, the performance varies in
dierent scenarios. An error may be
reported (for example, in the SELECT
statement) or the value 0000-00-00
may be returned (for example, in the
INSERT statement). As a result, when
the date type is used as the input
parameter of the function, the results
returned by the function are dierent.
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between date types and
returns true or false. For the addition
operation between the date and
interval types, the return result is of
the date type. For the subtraction
operation between the date and
interval types, the return result is of
the date type. For the subtraction
operation between date types, the
return result is of the interval type.
– When the MySQL date type and
other numeric types are calculated,
the date type is converted to the
numeric type, and then the
calculation is performed based on the
numeric type. The result is also of the
numeric type. It is dierent from
GaussDB. For example:
-- MySQL: date+numeric. Convert the date type to
20200101 and add it to 1. The result is 20200102.
mysql> select date'2020-01-01' + 1;
+----------------------+
| date'2020-01-01' + 1 |
+----------------------+
| 20200102 |
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 499

No. MySQL GaussDB Dierence
+----------------------+
1 row in set (0.00 sec)
-- GaussDB: date+numeric. Convert the numeric type
to the interval type (1 day), and then add them up
to obtain a new date.
gaussdb=# select date'2020-01-01' + 1;
?column?
------------
2020-01-02
(1 row)
● Type conversion
Compared with MySQL, GaussDB
supports conversion between the date
type and char(n), nchar(n), datetime, or
timestamp type, but does not support
conversion between the date type and
binary, decimal, JSON, integer, unsigned
integer, or time type. The principles for
determining common types in scenarios
such as collections and complex
expressions are dierent from those in
MySQL. For details, see Data Type
Conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 500

No. MySQL GaussDB Dierence
2 DATETIME[(f
sp)]
Supported. GaussDB supports the datetime data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats:
– GaussDB supports only the character
type and does not support the
numeric type. For example,
'2020-01-01 10:20:30.123456' or
'20200101102030.123456' is
supported, but
20200101102030.123456 is not
supported. MySQL supports
conversion from numeric input to the
datetime type.
– Separator: GaussDB does not support
the plus sign (+) or colon (:) as the
separator between the year, month,
and day. Other symbols are
supported. Only colons (:) can be
used as separators between hours,
minutes, and seconds. Sometimes,
the mixed use of separators is not
supported, which is dierent from
MySQL. Therefore, it is not
recommended. MySQL supports all
symbols as separators.
– No separator: The complete format
'YYYYMMDDhhmiss.' is
recommended. The parsing rules of
incomplete formats (including the
ultra-long format) may be dierent
from those of MySQL. An error may
be reported or the parsing result may
be inconsistent with that of MySQL.
Therefore, the incomplete format is
not recommended.
● Output formats:
– The format is 'YYYY-MM-DD
hh:mi:ss.', which is the same as
that of MySQL and is not aected by
the DateStyle parameter. However,
for the precision part, if the last
several digits are 0, they are not
displayed in GaussDB but displayed in
MySQL.
– If the sql_mode parameter of
GaussDB does not contain
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 501

No. MySQL GaussDB Dierence
'strict_trans_tables' (the strict mode
is used unless otherwise dened as
the loose mode), the year, month,
and day can be set to 0. However, the
value is converted to a valid value in
the sequence of year, month, and
day. For example, datetime
'0000-00-10 00:00:00' is converted to
0002-12-10 00:00:00 BC. If the input
is invalid or exceeds the range, a
warning message is reported and the
value 0000-00-00 00:00:00 is
returned. MySQL outputs the
datetime value as it is, even if the
year, month, and day are set to 0.
● Value range
4713-11-24 00:00:00.000000 BC to
294277-01-09 04:00:54.775806 AD. If
the value is 294277-01-09
04:00:54.775807 AD, innity is
returned. If the value exceeds the range,
GaussDB reports an error in strict mode.
Whether MySQL reports an error
depends on the application scenario.
Generally, no error is reported in the
query scenario. However, an error is
reported when the DML or SQL
statement is executed to change the
value of a table attribute. In loose mode,
GaussDB returns 0000-00-00 00:00:00.
MySQL may report an error, return
0000-00-00 00:00:00, or return null
based on the application scenario. As a
result, the execution result of the
function that uses the datetime type as
the input parameter is dierent from
that of MySQL.
● Precision
The value ranges from 0 to 6. For a
table column, the default value is 0,
which is the same as that in MySQL. In
the datetime[(p)]'str' expression,
GaussDB parses (p) as the precision.
The default value is 6, indicating that
'str' is formatted to the datetime type
based on the precision specied by p.
MySQL does not support the
datetime[(p)]'str' expression.
● Operators
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 502

No. MySQL GaussDB Dierence
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between datetime types and
returns true or false. For the addition
operation between the datetime and
interval types, the return result is of
the datetime type. For the
subtraction operation between the
datetime and interval types, the
return result is of the datetime type.
For the subtraction operation
between datetime types, the return
result is of the interval type.
– When the MySQL datetime type and
other numeric types are calculated,
the datetime type is converted to the
numeric type, and then the
calculation is performed based on the
numeric type. The result is also of the
numeric type. It is dierent from
GaussDB. For example:
-- MySQL: datetime+numeric. Convert the datetime
type to 20201010123456 and add it to 1. The result
is 20201010123457.
mysql> select cast('2020-10-10 12:34:56.123456' as
datetime) + 1;
+----------------------------------------------------+
| cast('2020-10-10 12:34:56.123456' as datetime) + 1
|
+----------------------------------------------------+
| 20201010123457 |
+----------------------------------------------------+
1 row in set (0.00 sec)
-- GaussDB: datetime+numeric. Convert the numeric
type to the interval type (1 day), and then add them
up to obtain the new datetime.
gaussdb=# select cast('2020-10-10 12:34:56.123456'
as datetime) + 1;
?column?
---------------------
2020-10-11 12:34:56
(1 row)
If the calculation result of the datetime
type and numeric type is used as the
input parameter of a function, the result
of the function may be dierent from
that of MySQL.
● Type conversion
Compared with MySQL, GaussDB
supports only conversion between the
datetime type and char(n), nchar(n),
and timestamp types, and conversion
from datetime to date and time types
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 503

No. MySQL GaussDB Dierence
(only value assignment and explicit
conversion). The conversion between the
datetime type and the binary, decimal,
json, integer, or unsigned integer type is
not supported. The principles for
determining common types in scenarios
such as collections and complex
expressions are dierent from those in
MySQL. For details, see Data Type
Conversion.
● Time zone
In GaussDB, the datetime value can
carry the time zone information (time
zone oset or time zone name), for
example, '2020-01-01 12:34:56.123456
+01:00' or '2020-01-01 2:34:56.123456
CST'. GaussDB converts the time to the
time of the current server time zone.
MySQL 5.7 does not support this
function. MySQL 8.0 and later versions
support this function.
● The table columns of the datetime data
type in GaussDB are actually converted
to the timestamp(p) without time zone.
When you query the table information
or use a tool to export the table
structure, the data type of columns is
timestamp(p) without time zone instead
of datetime. For MySQL, datetime(p) is
displayed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 504

No. MySQL GaussDB Dierence
3 TIMESTAMP[
(fsp)]
Supported. GaussDB supports the timestamp data
type. Compared with MySQL, GaussDB has
the following dierences in specications:
● Input format
– It supports only the character type
and does not support the numeric
type. For example, '2020-01-01
10:20:30.123456' or
'20200101102030.123456' is
supported, but
20200101102030.123456 is not
supported. MySQL supports
conversion from numeric input to the
timestamp type.
– Separator: It does not support the
plus sign (+) or colon (:) as the
separator between the year, month,
and day. Other symbols are
supported. Only colons (:) can be
used as separators between hours,
minutes, and seconds. Sometimes,
the mixed use of separators is not
supported, which is dierent from
MySQL. Therefore, it is not
recommended. MySQL supports all
symbols as separators.
– No separator: The complete format
'YYYYMMDDhhmiss.' is
recommended. The parsing rules of
incomplete formats (including the
ultra-long format) may be dierent
from those of MySQL. An error may
be reported or the parsing result may
be inconsistent with that of MySQL.
Therefore, the incomplete format is
not recommended.
● Output format
– The format is 'YYYY-MM-DD
hh:mi:ss.', which is the same as
that of MySQL and is not aected by
the DateStyle parameter. However,
for the precision part, if the last
several digits are 0, they are not
displayed in GaussDB but displayed in
MySQL.
– If the sql_mode parameter of
GaussDB does not contain
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 505

No. MySQL GaussDB Dierence
'strict_trans_tables' (the strict mode
is used unless otherwise dened as
the loose mode), the year, month,
and day can be set to 0. However, the
value is converted to a valid value in
the sequence of year, month, and
day. For example, timestamp
'0000-00-10 00:00:00' is converted to
0002-12-10 00:00:00 BC. If the input
is invalid or exceeds the range, a
warning message is reported and the
value 0000-00-00 00:00:00 is
returned. MySQL outputs the
timestamp value as it is, even if the
year, month, and day are set to 0.
● Value range
4713-11-24 00:00:00.000000 BC to
294277-01-09 04:00:54.775806 AD. If
the value is 294277-01-09
04:00:54.775807 AD, innity is
returned. If the value exceeds the range,
GaussDB reports an error in strict mode.
Whether MySQL reports an error
depends on the application scenario.
Generally, no error is reported in the
query scenario. However, an error is
reported when the DML or SQL
statement is executed to change the
value of a table attribute. In loose mode,
GaussDB returns 0000-00-00 00:00:00.
MySQL may report an error, return
0000-00-00 00:00:00, or return null
based on the application scenario. As a
result, the execution result of the
function that uses the timestamp type
as the input parameter is dierent from
that of MySQL.
● Precision
The value ranges from 0 to 6. For a
table column, the default value is 0,
which is the same as that in MySQL. In
the timestamp[(p)] 'str' expression:
– GaussDB parses (p) as the precision.
The default value is 6, indicating that
'str' is formatted to the timestamp
type based on the precision specied
by p.
– The meaning of timestamp 'str' in
MySQL is the same as that in
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 506

No. MySQL GaussDB Dierence
GaussDB. The default precision is 6.
However, timestamp(p) 'str' is parsed
as a function call. p is used as the
input parameter of the timestamp
function. The result returns a value of
the timestamp type, and 'str' is used
as the alias of the projection column.
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between timestamp types
and returns true or false. For the
addition operation between the
timestamp and interval types, the
return result is of the timestamp
type. For the subtraction operation
between the timestamp and interval
types, the return result is of the
timestamp type. For the subtraction
operation between timestamp types,
the return result is of the interval
type.
– When the MySQL timestamp type
and other numeric types are
calculated, the timestamp type is
converted to the numeric type, and
then the calculation is performed
based on the numeric type. The result
is also of the numeric type. It is
dierent from GaussDB. For example:
-- MySQL: timestamp+numeric. Convert the
timestamp type to 20201010123456.123456 and
add it to 1. The result is 20201010123457.123456.
mysql> select timestamp '2020-10-10
12:34:56.123456' + 1;
+--------------------------------------------+
| timestamp '2020-10-10 12:34:56.123456' + 1 |
+--------------------------------------------+
| 20201010123457.123456 |
+--------------------------------------------+
1 row in set (0.00 sec)
-- GaussDB: timestamp+numeric. Convert the
numeric type to the interval type (1 day), and then
add them up to obtain a new timestamp.
gaussdb=# select timestamp '2020-10-10
12:34:56.123456' + 1;
?column?
----------------------------
2020-10-11 12:34:56.123456
(1 row)
If the calculation result of the
timestamp type and numeric type is
used as the input parameter of a
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 507

No. MySQL GaussDB Dierence
function, the result of the function may
be dierent from that of MySQL.
● Type conversion
Compared with MySQL, GaussDB
supports only conversion between
timestamp and char(n), varchar(n), and
datetime, and conversion from
timestamp to date and time (only value
assignment and explicit conversion). The
conversion between the timestamp type
and the binary, decimal, json, integer, or
unsigned integer type is not supported.
The principles for determining common
types in scenarios such as collections
and complex expressions are dierent
from those in MySQL. For details, see
Data Type Conversion.
● Time zone
In GaussDB, the timestamp value can
carry the time zone information (time
zone oset or time zone name), for
example, '2020-01-01 12:34:56.123456
+01:00' or '2020-01-01 2:34:56.123456
CST'. GaussDB converts the time to the
time of the current server time zone. If
the time zone of the server is changed,
the timestamp value is converted to the
timestamp of the new time zone.
MySQL 5.7 does not support this
function. MySQL 8.0 and later versions
support this function.
● The table columns of the timestamp
data type in GaussDB are actually
converted to the timestamp(p) with
time zone. When you query the table
information or use a tool to export the
table structure, the data type of
columns is timestamp(p) with time zone
instead of timestamp. For MySQL,
timestamp(p) is displayed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 508

No. MySQL GaussDB Dierence
4 TIME[(fsp)] Supported. GaussDB supports the time data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input format
– It supports only the character type
and does not support the numeric
type. For example, '1 10:20:30' or
'102030' is supported, but 102030 is
not supported. MySQL supports
conversion from numeric input to the
time type.
– Separator: GaussDB supports only
colons (:) as separators between
hours, minutes, and seconds. MySQL
supports all symbols as separators.
– No separator: The complete format
'hhmiss.' is recommended. The
parsing rules of incomplete formats
(including the ultra-long format) may
be dierent from those of MySQL. An
error may be reported or the parsing
result may be inconsistent with that
of MySQL. Therefore, the incomplete
format is not recommended.
– When negative values are entered for
minute, second, and precision,
GaussDB may ignore the rst part of
a negative value, which is parsed as
0. For example, '00:00:-10' is parsed
as '00:00:00'. An error may also be
reported. For example, if
'00:00:-10000' is parsed, an error will
be reported. The result depends on
the range of the input value.
However, MySQL reports an error in
both cases.
● Output format
The format is hh:mi:ss., which is the
same as that of MySQL. However, for
the precision part, if the last several
digits are 0, they are not displayed in
GaussDB but displayed in MySQL.
● Value range
–838:59:59.000000 to 838:59:59.000000,
which is the same as that of MySQL. In
GaussDB loose mode, if a value exceeds
the range, the nearest boundary value –
838:59:59 or 838:59:59 is returned,
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 509
No. MySQL GaussDB Dierence
regardless of the query or DML
operations such as insert and update. In
MySQL, an error is reported during
query, or the nearest boundary value is
returned after a DML operation. As a
result, when the time type is used as the
input parameter of the function, the
results returned by the function are
dierent.
● Precision
The value ranges from 0 to 6. For a
table column, the default value is 0,
which is the same as that in MySQL. In
the time(p) 'str' expression, GaussDB
parses (p) as the precision. The default
value is 6, indicating that 'str' is
formatted to the time type based on the
precision specied by p. MySQL parses it
as a time function, p is an input
parameter, and 'str' is the alias of the
projection column.
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between time types and
returns true or false. For the addition
operation between the time and
interval types, the return result is of
the time type. For the subtraction
operation between the time and
interval types, the return result is of
the time type. For the subtraction
operation between time types, the
return result is of the interval type.
– When the MySQL time type and
other numeric types are calculated,
the time type is converted to the
numeric type, and then the
calculation is performed based on the
numeric type. The result is also of the
numeric type. It is dierent from
GaussDB. For example:
-- MySQL: time+numeric. Convert the time type to
123456 and add it to 1. The result is 123457.
mysql> select time '12:34:56' + 1;
+---------------------+
| time '12:34:56' + 1 |
+---------------------+
| 123457 |
+---------------------+
1 row in set (0.00 sec)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 510

No. MySQL GaussDB Dierence
-- GaussDB: time+numeric. Convert the numeric type
to the interval type (1 day), and then add them up
to obtain the new time. Because 24 hours are added,
the obtained time is still 12:34:56.
gaussdb=# select time '12:34:56' + 1;
?column?
----------
12:34:56
(1 row)
If the calculation result of the time type
and numeric type is used as the input
parameter of a function, the result of
the function may be dierent from that
of MySQL.
● Type conversion
Compared with MySQL, GaussDB
supports only conversion between the
time type and char(n) or nchar(n) type,
and conversion between the datetime or
timestamp type and time type. The
conversion between the time type and
binary, decimal, date, JSON, integer, or
unsigned integer type is not supported.
The principles for determining common
types in scenarios such as collections
and complex expressions are dierent
from those in MySQL. For details, see
Data Type Conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 511

No. MySQL GaussDB Dierence
5 YEAR[(4)] Supported. GaussDB supports the year data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Operators
– GaussDB supports only the
comparison operators =, !=, <, <=, >,
and >= between year types and
returns true or false.
– GaussDB supports only the arithmetic
operators + and - between the year
and int4 types and returns integer
values. MySQL returns unsigned
integer values.
● Type conversion
Compared with MySQL, GaussDB
supports only the conversion between
the year type and int4 type, and
supports only the conversion from the
int4, varchar, numeric, date, time,
timestamp, or timestamptz type to the
year type. The principles for determining
common types in scenarios such as
collections and complex expressions are
dierent from those in MySQL. For
details, see Data Type Conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 512
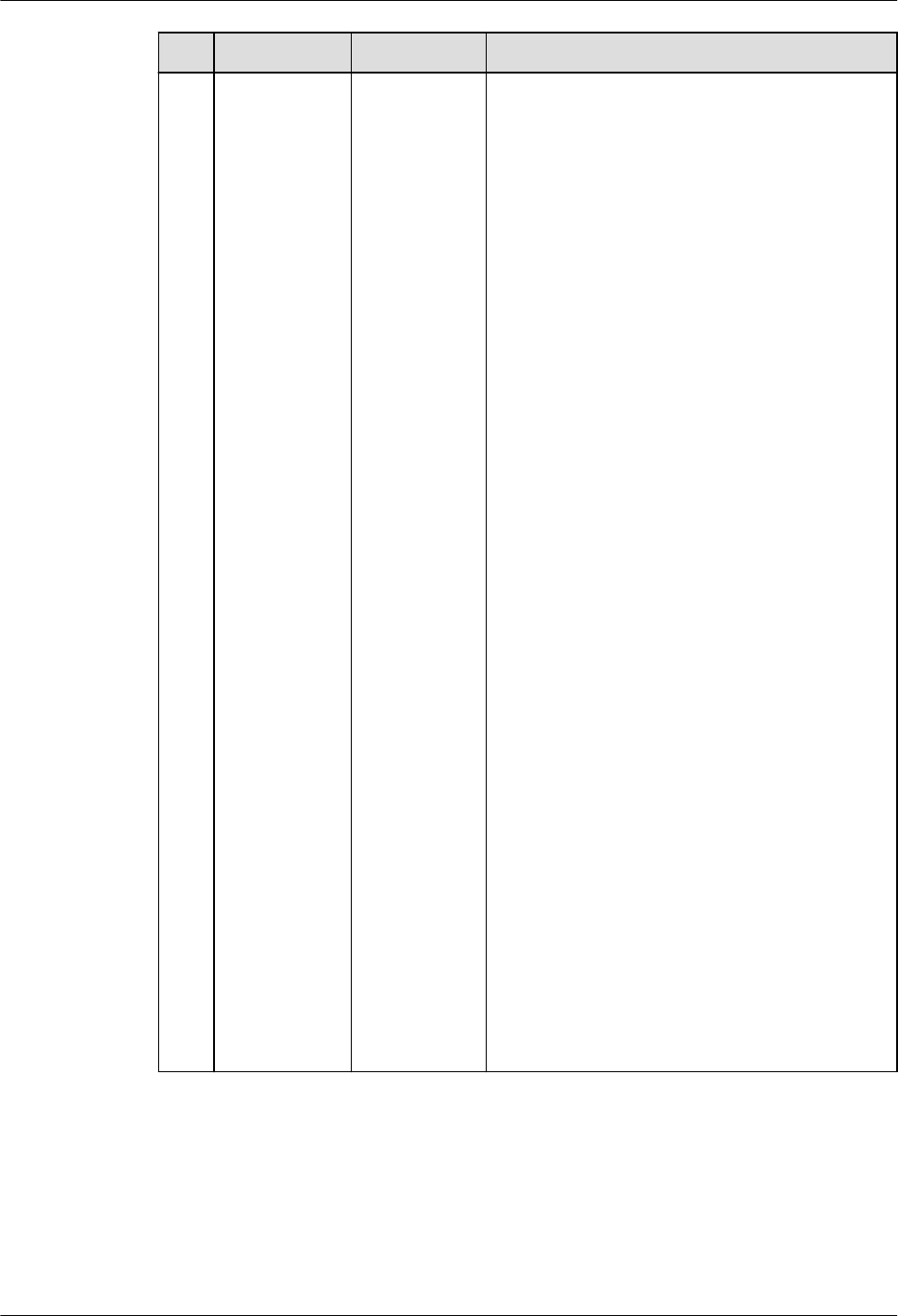
No. MySQL GaussDB Dierence
6 INTERVAL Supported. GaussDB supports the INTERVAL data type,
but INTERVAL is an expression in MySQL.
The dierences are as follows:
● The date input of the character string
type cannot be used as an operation, for
example, select '2023-01-01' + interval 1
day.
● In the INTERVAL expr unit syntax, expr
cannot be a negative integer or oating-
point number, for example, select
date'2023-01-01' + interval -1 day.
● In the INTERVAL expr unit syntax, expr
cannot be the input of an operation
expression, for example, select
date'2023-01-01' + interval 4/2 day.
● When the INTERVAL expression is used
for calculation, the return value is of the
datetime type. For MySQL, the return
value is of the datetime or date type.
The calculation logic is the same as that
of GaussDB but dierent from that of
MySQL.
● In the INTERVAL expr unit syntax, the
value range of expr varies with the unit.
The maximum value range is [–
2147483648, 2147483647]. If the value
exceeds the range, an error is reported
in strict mode, and a warning is reported
in loose mode and 0 is returned.
● In the INTERVAL expr unit syntax, if the
number of columns specied by expr is
greater than the expected number of
columns in unit, an error is reported in
strict mode, and a warning is reported in
loose mode and 0 is returned. For
example, if the value of unit is
DAY_HOUR, the expected number of
columns is 2. If the value of expr is
'1-2-3', the expected number of columns
is 3.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 513

8.2.2.2.3 String Data Types
Table 8-27 String data types
No. MySQL GaussDB Dierence
1 CHAR[(M)] Supported ● Input format
– The length of parameters and return
values of GaussDB user-dened
functions cannot be veried. The
length of stored procedure
parameters cannot be veried. In
addition, correct spaces cannot be
supplemented when
PAD_CHAR_TO_FULL_LENGTH is
enabled. However, MySQL supports
these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Syntax
The CAST(expr as char) syntax of
GaussDB cannot convert the input
string to the corresponding type based
on the string length. It can only be
converted to the varchar type. CAST(''
as char) and CAST('' as char(0)) cannot
convert an empty string to the char(0)
type. MySQL supports conversion to the
corresponding type by length.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 514

No. MySQL GaussDB Dierence
2 VARCHAR(M
)
Supported ● Input format:
– The length of parameters and return
values of GaussDB user-dened
functions cannot be veried. The
length of stored procedure
parameters cannot be veried.
However, MySQL supports these
functions.
– The length of temporary variables in
GaussDB user-dened functions and
stored procedures can be veried,
and an error or truncation alarm is
reported in strict or loose mode.
However, MySQL does not support
these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 515

No. MySQL GaussDB Dierence
3 TINYTEXT Supported ● Input format
– The length limit in GaussDB is 1 GB,
not 255 bytes. If the length exceeds
the limit, no error or truncation
alarm is reported in strict or loose
mode. However, MySQL supports
these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 516

No. MySQL GaussDB Dierence
4 TEXT Supported ● Input format
– The length limit in GaussDB is 1 GB,
not 65535 bytes. If the length
exceeds the limit, no error or
truncation alarm is reported in strict
or loose mode. However, MySQL
supports these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 517

No. MySQL GaussDB Dierence
5 MEDIUMTEX
T
Supported ● Input format
– The length limit in GaussDB is 1 GB,
not 16777215 bytes. If the length
exceeds the limit, no error or
truncation alarm is reported in strict
or loose mode. However, MySQL
supports these functions.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 518

No. MySQL GaussDB Dierence
6 LONGTEXT Supported ● Input format
– GaussDB supports a maximum of 1
GB, and MySQL supports a
maximum of 4 GB minus 1 byte.
– GaussDB does not support escape
characters or double quotation
marks (""). MySQL supports these
inputs.
● Operator
– GaussDB can convert a character
string to a oating-point value and
perform the modulo operation on
the character string and integer
value. The return value is an integer.
MySQL returns a oating-point
value.
– If a value is divided by 0, GaussDB
reports an error, and MySQL returns
null.
– "~": returns a negative number in
GaussDB and an 8-byte unsigned
integer in MySQL.
– "^": indicates a power in GaussDB
and a bitwise XOR in MySQL.
7
ENUM('value
1','value2',...)
Not
supported
-
8 SET('value1','
value2',...)
Supported -
8.2.2.2.4 Binary Data Types
Table 8-28 Binary data types
No.
MySQL GaussDB Dierence
1 BINARY[(M)] Not
supported
-
2 VARBINARY(
M)
Not
supported
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 519

No. MySQL GaussDB Dierence
3 TINYBLOB Supported ● Value range: The length limit is 1 GB,
not 255 bytes. If the length exceeds the
limit, no error or truncation alarm is
reported in strict or loose mode.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
4 BLOB Supported ● Value range: The length limit is 1 GB,
not 65535 bytes. If the length exceeds
the limit, no error or truncation alarm is
reported in strict or loose mode.
However, MySQL supports these
functions.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
5 MEDIUMBLO
B
Supported ● Value range: The length limit is 1 GB,
not 16777215 bytes. If the length
exceeds the limit, no error or truncation
alarm is reported in strict or loose
mode. However, MySQL supports these
functions.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 520

No. MySQL GaussDB Dierence
6 LONGBLOB Supported ● Value range: The upper limit is 1 GB.
For details about the range, see the
centralized and distributed
specications of the bytea data type.
● Input format: Escape characters and
double quotation marks ("") are not
supported.
● Operator: Arithmetic operators (+, -, *, /,
and %) are not supported. Common
logical operators OR, AND, NOT (||, &&,
and !) are not supported. Common
bitwise operators (~, &, |, and ^) are not
supported.
7 BIT[(M)] Not
supported
-
8.2.2.2.5 JSON Data Type
Table 8-29 JSON data type
No.
MySQL GaussDB
1 JSON Not fully compatible
8.2.2.2.6 Attributes Supported by Data Types
Table 8-30 Attributes supported by data types
No.
MySQL GaussDB
1 NULL Supported
2 NOT NULL Supported
3 DEFAULT Supported
4 ON UPDATE Supported
4 PRIMARY KEY Supported
5 AUTO_INCREMENT Supported
6 CHARACTER SET name Supported
7 COLLATE name Supported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 521

8.2.2.2.7 Data Type Conversion
Conversion between dierent data types is supported. Data type conversion is
involved in the following scenarios:
● The data types of operands of operators (such as comparison and arithmetic
operators) are inconsistent. It is commonly used for comparison operations in
query conditions or join conditions.
● The data types of arguments and parameters are inconsistent when a
function is called.
● The data types of target columns to be updated by DML statements
(including INSERT, UPDATE, MERGE, and REPLACE) and the dened column
types are inconsistent.
● Explicit type conversion: cast(expr as datatype), which converts an expression
to a data type.
● After the target data type of the nal projection column is determined by set
operations (UNION, MINUS, EXCEPT, and INTERSECT), the type of the
projection column in each SELECT statement is inconsistent with the target
data type.
● In other expression calculation scenarios, the target data type used for
comparison or nal result is determined based on the data type of dierent
expressions.
– DECODE
– CASE WHEN
– lexpr [ NOT ] IN (expr_list)
– BETWEEN AND
– JOIN USING(a,b)
– GREATEST and LEAST
– NVL and COALESCE
GaussDB and MySQL have dierent rules for data type conversion and target data
types. The following examples show the dierences between the two processing
modes:
-- MySQL: The execution result of IN is 0, indicating false. According to the rule, '1970-01-01' is compared
with the expressions in the list in sequence. The results are all 0s. Therefore, the nal result is 0.
mysql> select '1970-01-01' in ('1970-01-02', 1, '1970-01-02');
+-------------------------------------------------+
| '1970-01-01' in ('1970-01-02', 1, '1970-01-02') |
+-------------------------------------------------+
| 0 |
+-------------------------------------------------+
-- GaussDB: The execution result of IN is true, which is opposite to the MySQL result. The common type
selected based on the rule is int. Therefore, the left expression '1970-01-01' is converted to the int type and
compared with the value after the expression in the list is converted to the int type.
-- When '1970-01-01' and '1970-01-02' are converted to the int type, the values are 1970. (In MySQL-
compatible mode, invalid characters and the following content are ignored during conversion, and the
previous part is converted to the int type.) The comparison result is equal. Therefore, the returned result is
true.
gaussdb=# select '1970-01-01' in ('1970-01-02', 1::int, '1970-01-02') as result;
result
--------
t
(1 row)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 522

1. Dierences in data type conversion rules:
● The GaussDB clearly denes the conversion rules between dierent data
types.
– Whether to support conversion: Conversion is supported only when the
conversion path of two types is dened in the pg_cast system catalog.
– Conversion scenarios: conversion in any scenario, conversion only in CAST
expressions, and conversion only during value assignment. In scenarios
that are not supported, data type conversion cannot be performed even if
the conversion path is dened.
● MySQL supports conversion between any two data types.
Due to the preceding dierences, when MySQL-based applications are migrated to
GaussDB, an error may be reported because the SQL statement does not support
the conversion between dierent data types. In the scenario where conversion is
supported, dierent conversion rules result in dierent execution results of SQL
statements.
You are advised to use the same data type in SQL statements for comparison or
value assignment to avoid unexpected results or performance loss caused by data
type conversion.
2. Dierences in target data type selection rules:
In some scenarios, the data type to be compared or returned can be determined
only after the types of multiple expressions are considered. For example, in the
UNION operation, projection columns at the same position in dierent SELECT
statements are of dierent data types. The nal data type of the query result
needs to be determined based on the data type of the projection columns in each
SELECT statement.
GaussDB and MySQL have dierent rules for determining the target data types.
● GaussDB rules:
– If the operand types of operators are inconsistent, the operand types are
not converted to the target type before calculation. Instead, operators of
two data types are directly registered, and two types of processing rules
are dened during operator processing. In this mode, implicit type
conversion does not exist, but the customized processing rule implies the
conversion operation.
– Rules for determining the target data type in the set operation and
expression scenarios:
▪ If all types are the same, it is the target type.
▪ If the two data types are dierent, check whether the data types are
of the same type, such as the numeric type, character type, and date
and time type. If they do not belong to the same type, the target
type cannot be determined. In this case, an error is reported during
SQL statement execution.
▪ For data types with the same category attribute (dened in the
pg_type system catalog), the data type with the preferred attribute
(dened in the pg_type system catalog) is selected as the target
type. If operand 1 can be converted to operand 2 (no conversion
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 523

path), but operand 2 cannot be converted to operand 1 or the
priority of the numeric type is lower than that of operand 2, then
operand 2 is selected as the target type.
▪ If three or more data types are involved, the rule for determining the
target type is as follows: common_type(type1,type2,type3) =
common_type(common_type(type1,type2),type3). Perform iterative
processing in sequence to obtain the nal result.
▪ For IN and NOT IN expressions, if the target type cannot be
determined based on the preceding rules, each expression in lexpr
and expr_list is compared one by one based on the equivalent
operator (=).
▪ Precision determination: The precision of the nally selected
expression is used as the nal result.
● MySQL rules:
– If the operand types of operators are inconsistent, determine the target
type based on the following rules. Then, convert the inconsistent operand
types to the target type and then process the operands.
▪
If both parameters are of the string type, they are compared based
on the string type.
▪
If both parameters are of the integer type, they are compared based
on the integer type.
▪
If a hexadecimal value is not compared with a numeric value, they
are compared based on the binary string.
▪
If one parameter is of the datetime/timestamp type, and the other
parameter is a constant, the constant is converted to the timestamp
type for comparison.
▪
If one parameter is of the decimal type, the data type used for
comparison depends on the other parameter. If the other type is
decimal or integer, the decimal type is used. If the other type is not
decimal, the real type is used.
▪
In other scenarios, the data type is converted to the real type for
comparison.
– Rules for determining the target data type in the set operation and
expression scenarios:
▪ Establish a target type matrix between any two types. Given two
types, the target type can be determined by using the matrix.
▪ If three or more data types are involved, the rule for determining the
target type is as follows: common_type(type1,type2,type3) =
common_type(common_type(type1,type2),type3). Perform iterative
processing in sequence to obtain the nal result.
▪ If the target type is integer and each expression type contains signed
and unsigned integers, the type is promoted to an integer type with
higher precision. The result is unsigned only when all expressions are
unsigned. Otherwise, the result is signed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 524

▪ The highest precision in the expression is used as the nal result.
According to the preceding rules, GaussDB and MySQL dier greatly in data type
conversion rules and types cannot be directly compared. In the preceding scenario,
the execution result of SQL statements may be dierent from that in MySQL. In
the current version, you are advised to use the same type for all expressions or use
CAST to convert the type to the required type in advance to avoid dierences.
8.2.2.3 System Functions
GaussDB is compatible with most MySQL system functions, but there are some
dierences. If not listed, the function behavior is the native GaussDB behavior by
default.
NO TE
For most GaussDB system functions compatible with MySQL, the return value precision (the
number of trailing zeros in the result) is inconsistent with that of MySQL. This is because
the precision of some data types is lost in some scenarios and the precision cannot be
correctly obtained. As a result, some functions are not fully adapted.
8.2.2.3.1 Flow Control Functions
Table 8-31 Flow control functions
N
o.
MySQL GaussD
B
Dierence
1 IF() Support
ed
● The expr1 input parameter supports only the
Boolean type. If an input parameter of the non-
Boolean type cannot be converted to the Boolean
type, an error is reported.
● If the types of expr2 and expr3 are dierent and
no implicit conversion function exists between the
two types, an error is reported.
● If the two input parameters are of the same type,
the input parameter type is returned.
● If the expr2 and expr3 input parameters are of
the NUMERIC, STRING, or TIME type respectively,
the output is of the TEXT type. In MySQL, the
output is of the VARCHAR type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 525

N
o.
MySQL GaussD
B
Dierence
2 IFNULL() Support
ed
● If the types of expr1 and expr2 are dierent and
no implicit conversion function exists between the
two types, an error is reported.
● If the two input parameters are of the same type,
the input parameter type is returned.
● If the expr1 and expr2 input parameters are of
the NUMERIC, STRING, or TIME type respectively,
the output is of the TEXT type. In MySQL, the
output is of the VARCHAR type.
● If the rst input parameter is FLOAT4 and the
other input parameter is BIGINT or UNSIGNED
BIGINT, the DOUBLE type is returned. In MySQL,
the FLOAT type is returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 526

N
o.
MySQL GaussD
B
Dierence
3 NULLIF() Support
ed
● The NULLIF() type derivation in GaussDB complies
with the following logic:
1. If the data types of two parameters are
dierent and the two input parameter types
have an equality comparison operator, the left
value type corresponding to the equality
comparison operator is returned. Otherwise,
the two input parameter types are forcibly
compatible.
2. If an equality comparison operator exists after
forcible type compatibility, the left value type
of the equality comparison operator after
forcible type compatibility is returned.
3. If the corresponding equality operator cannot
be found after forcible type compatibility, an
error is reported.
-- The two input parameter types have an equality
comparison operator.
gaussdb=# select pg_typeof(nullif(1::int2, 2::int8));
pg_typeof
-----------
smallint
(1 row)
-- The two input parameter types do not have the equality
comparison operator, but the equality comparison operator
can be found after forcible type compatibility.
gaussdb=# select pg_typeof(nullif(1::int1, 2::int2));
pg_typeof
-----------
bigint
(1 row)
-- The two input parameter types do not have the equality
comparison operator, and the equality comparison operator
does not exist after forcible type compatibility.
gaussdb=# SELECT nullif(1::bit, '1'::MONEY);
ERROR: operator does not exist: bit = money
LINE 1: SELECT nullif(1::bit, '1'::MONEY);
^
HINT: No operator matches the given name and argument
type(s). You might need to add explicit type casts.
CONTEXT: referenced column: nullif
● The MySQL output type is related only to the type
of the rst input parameter.
1. If the type of the rst input parameter is
TINYINT, SMALLINT, MEDIUMINT, INT, or
BOOL, the output is of the INT type.
2. If the type of the rst input parameter is
BIGINT, the output is of the BIGINT type.
3. When the type of the rst input parameter is
UNSIGNED TINYINT, UNSIGNED SMALLINT,
UNSIGNED MEDIUMINT, UNSIGNED INT, or
BIT, the output is of the UNSIGNED INT type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 527

N
o.
MySQL GaussD
B
Dierence
4. If the type of the rst input parameter is
UNSIGNED BIGINT, the output is of the
UNSIGNED BIGINT type.
5. If the type of the rst input parameter is
FLOAT, DOUBLE, or REAL, the output is of the
DOUBLE type.
6. If the type of the rst input parameter
DECIMAL or NUMERIC, the output is of the
DECIMAL type.
7. If the type of the rst input parameter is DATE,
TIME, DATE, DATETIME, TIMESTAMP, CHAR,
VARCHAR, TINYTEXT, ENUM, or SET, the output
is of the VARCHAR type.
8. If the type of the rst input parameter is TEXT,
MEDIUMTEXT, or LONGTEXT, the output is of
the LONGTEXT type.
9. If the type of the rst input parameter is
TINYBLOB, the output is of the VARBINARY
type.
10.If the type of the rst input parameter is
MEDIUMBLOB or LONGBLOB, the output is of
the LONGBLOB type.
11.If the type of the rst input parameter is BLOB,
the output is of the BLOB type.
4
ISNULL() Support
ed
In GaussDB, the return value is t or f of the
BOOLEAN type. In MySQL, the return value is 1 or 0
of the INT type.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 528

8.2.2.3.2 Date and Time Functions
NO TE
The following describes the date and time function compatibility between GaussDB and
MySQL:
● In the
Developer Guide
, if an input parameter of a function is a time expression:
Time expressions (mainly including TEXT, DATETIME, DATE, and TIME) and types that
can be implicitly converted to time expressions can be used as input parameters. For
example, a number can be implicitly converted to text and then used as a time
expression.
However, the eective mode varies according to the function. For example, DATEDIFF is
used to calculate only the date dierence. Therefore, the time expression is parsed as
date. TIMESTAMPDIFF is used to calculate the time dierence based on UNIT. Therefore,
the time expression is parsed as DATE, TIME, or DATETIME based on UNIT.
● If an input parameter of a function is an invalid date:
Generally, the supported DATE and DATETIME ranges are the same as those in MySQL.
The value of DATE ranges from '0000-01-01' to '9999-12-31', and the value of
DATETIME ranges from '0000-01-01 00:00:00' to '9999-12-31 23:59:59'. Although the
DATE and DATETIME ranges supported by GaussDB are greater than those supported by
MySQL, out-of-bounds dates are still invalid.
Most time functions generate alarms and return NULL. Only dates that can be normally
converted by CAST are normal and reasonable dates.
Most function scenarios of GaussDB date and time functions are the same as
those of MySQL, but there are still dierences. Some dierences are as follows:
● If an input parameter of a function is NULL, the function returns NULL, and
no warning or error is reported. These functions include:
from_days, date_format, str_to_date, datedi, timestampdi, date_add,
subtime, month, time_to_sec, to_days, to_seconds, dayname, monthname,
convert_tz, sec_to_time, addtime, adddate, date_sub, timedi, last_day,
weekday, from_unixtime, unix_timestamp, subdate, day, year, weekofyear,
dayofmonth, dayofyear, week, yearweek, dayofweek, time_format, hour,
minute, second, microsecond, quarter, get_format, extract, makedate,
period_add, timestampadd, period_di, utc_time, utc_timestamp, maketime,
and curtime.
Example:
gaussdb=# select day(null);
day
-----
(1 row)
● Some functions with pure numeric input parameters are dierent from those
of MySQL. Numeric input parameters without quotation marks are converted
into text input parameters for processing.
Example:
gaussdb=# select day(19231221.123141);
WARNING: Incorrect datetime value: "19231221.123141"
CONTEXT: referenced column: day
day
-----
(1 row)
● Time and date calculation functions are adddate, subdate, date_add, and
date_sub. If the date result after calculation is within the range
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 529

[0000-01-01,0001-01-01], the result is returned normally. MySQL returns
'0000-00-00'.
Example:
gaussdb=# select subdate('0001-01-01', interval 1 day);
subdate
-------------
0000-12-31
(1 row)
● If the input parameter of the date or datetime type of the date and time
function contains month 0 or day 0, the value is invalid. In strict mode, an
error is reported. In loose mode, if the input is a character string or number, a
warning is reported. If the input is of the date or datetime type, the system
processes the input as December of the previous year or the last day of the
previous month.
If the type of the CAST function is converted to date or datetime, an error is
reported in strict mode. In loose mode, no warning is reported. Instead, the
system processes the input as December of the previous year or the last day
of the previous month. Pay attention to this dierence. MySQL outputs the
value as it is, even if the year, month, and day are set to 0.
Example:
gaussdb=# select adddate('2023-01-00', 1);-- Strict mode
ERROR: Incorrect datetime value: "2023-01-00"
CONTEXT: referenced column: adddate
gaussdb=# select adddate('2023-01-00', 1);-- Loose mode
WARNING: Incorrect datetime value: "2023-01-00"
CONTEXT: referenced column: adddate
adddate
---------
(1 row)
gaussdb=# select adddate(date'2023-00-00', 1);-- Loose mode
adddate
------------
2022-12-01
(1 row)
gaussdb=# select cast('2023/00/00' as date);-- Loose mode
date
------------
2022-11-30
(1 row)
gaussdb=# select cast('0000-00-00' as datetime);-- Loose mode
timestamp
---------------------
0000-00-00 00:00:00
(1 row)
● If the input parameter of the function is of the numeric data type, no error is
reported in the case of invalid input, and the input parameter is processed as
0.
Example:
gaussdb=# select from_unixtime('aa');
from_unixtime
---------------------
1970-01-01 08:00:00
(1 row)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 530

● A maximum of six decimal places are allowed. Decimal places with all 0s are
not allowed.
Example:
gaussdb=# select from_unixtime('1234567899.00000');
from_unixtime
---------------------
2009-02-14 07:31:39
(1 row)
● If the time function parameter is a character string, the result is correct only
when the year, month, and day are separated by a hyphen (-) and the hour,
minute, and second are separated by a colon (:).
Example:
gaussdb=# select adddate('20-12-12',interval 1 day);
adddate
------------
2020-12-13
(1 row)
● If the return value of a function is of the varchar type in MySQL, the return
value of the function is of the text type in GaussDB.
-- Return value of a function in GaussDB.
gaussdb=# SELECT pg_typeof(adddate('2023-01-01', 1));
pg_typeof
-----------
text
(1 row)
-- Return value of a function in MySQL.
mysql> CREATE VIEW v1 AS SELECT adddate('2023-01-01', 1);
Query OK, 0 rows aected (0.00 sec)
mysql> DESC v1;
+--------------------------+-------------+------+-----+---------+-------+
| Field | Type | Null | Key | Default | Extra |
+--------------------------+-------------+------+-----+---------+-------+
| adddate('2023-01-01', 1) | varchar(29) | YES | | NULL | |
+--------------------------+-------------+------+-----+---------+-------+
1 row in set (0.00 sec)
Table 8-32 Date and time functions
N
o.
MySQL GaussDB Dierence
1 ADDDATE() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 531

N
o.
MySQL GaussDB Dierence
2 ADDTIME() Supported. ● MySQL returns NULL if the
second input parameter is a
string in the DATETIME format.
GaussDB can calculate the value.
● The value range of an input
parameter is ['0001-01-01
00:00:00', 9999-12-31
23:59:59.999999].
● If the rst parameter of the
ADDTIME function in MySQL is a
dynamic parameter (for
example, in a prepared
statement), the return type is
TIME. Otherwise, the parse type
of the function is derived from
the parse type of the rst
parameter. The return value
rules of the ADDTIME function
in GaussDB are as follows:
– The rst input parameter is of
the date type, the second
input parameter is of the date
type, and the return value is
of the time type.
– The rst input parameter is of
the date type, the second
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the date type, the second
input parameter is of the
datetime type, and the return
value is of the time type.
– The rst input parameter is of
the date type, the second
input parameter is of the
time type, and the return
value is of the time type.
– The rst input parameter is of
the text type, the second
input parameter is of the date
type, and the return value is
of the text type.
– The rst input parameter is of
the text type, the second
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 532

N
o.
MySQL GaussDB Dierence
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the text type, the second
input parameter is of the
datetime type, and the return
value is of the text type.
– The rst input parameter is of
the text type, the second
input parameter is of the
time type, and the return
value is of the text type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the date
type, and the return value is
of the datetime type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the
datetime type, and the return
value is of the datetime type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the
time type, and the return
value is of the datetime type.
– The rst input parameter is of
the time type, the second
input parameter is of the date
type, and the return value is
of the time type.
– The rst input parameter is of
the time type, the second
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the time type, the second
input parameter is of the
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 533

N
o.
MySQL GaussDB Dierence
datetime type, and the return
value is of the time type.
– The rst input parameter is of
the time type, the second
input parameter is of the
time type, and the return
value is of the time type.
3 CONVERT_TZ() Supported. -
4 CURDATE() Supported. -
5 CURRENT_DATE(),
CURRENT_DATE
Supported. -
6 CURRENT_TIME(),
CURRENT_TIME
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only integer values within
the range of [0,6] as the precision
of the returned time. For other
values, an error is reported. The
valid precision value in MySQL is
within [0,6], but the input integer
value is modulated by 256. For
example, if the input integer value
is 257, the time value with
precision 1 is returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 534

N
o.
MySQL GaussDB Dierence
7 CURRENT_TIMESTAM
P(),
CURRENT_TIMESTAMP
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only the input integer
value within the range of [0,6] as
the precision of the returned time.
If the input integer value is greater
than 6, an alarm is generated and
the time value is output based on
the precision 6. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
8 CURTIME() Supported. In GaussDB, if a character string or
a non-integer value is entered, the
value is implicitly converted into an
integer and then the precision is
veried. If the value is beyond the
[0,6] range, an error is reported. If
the value is within the range, the
time value is output normally. In
MySQL, an error is reported. The
time value (after the decimal point)
output by precision is rounded o
in GaussDB and directly truncated
in MySQL. The last 0 of the time
value (after the decimal point)
output by precision is not displayed
in GaussDB but displayed in
MySQL. GaussDB supports only
integer values within the range of
[0,6] as the precision of the
returned time. For other values, an
error is reported. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 535
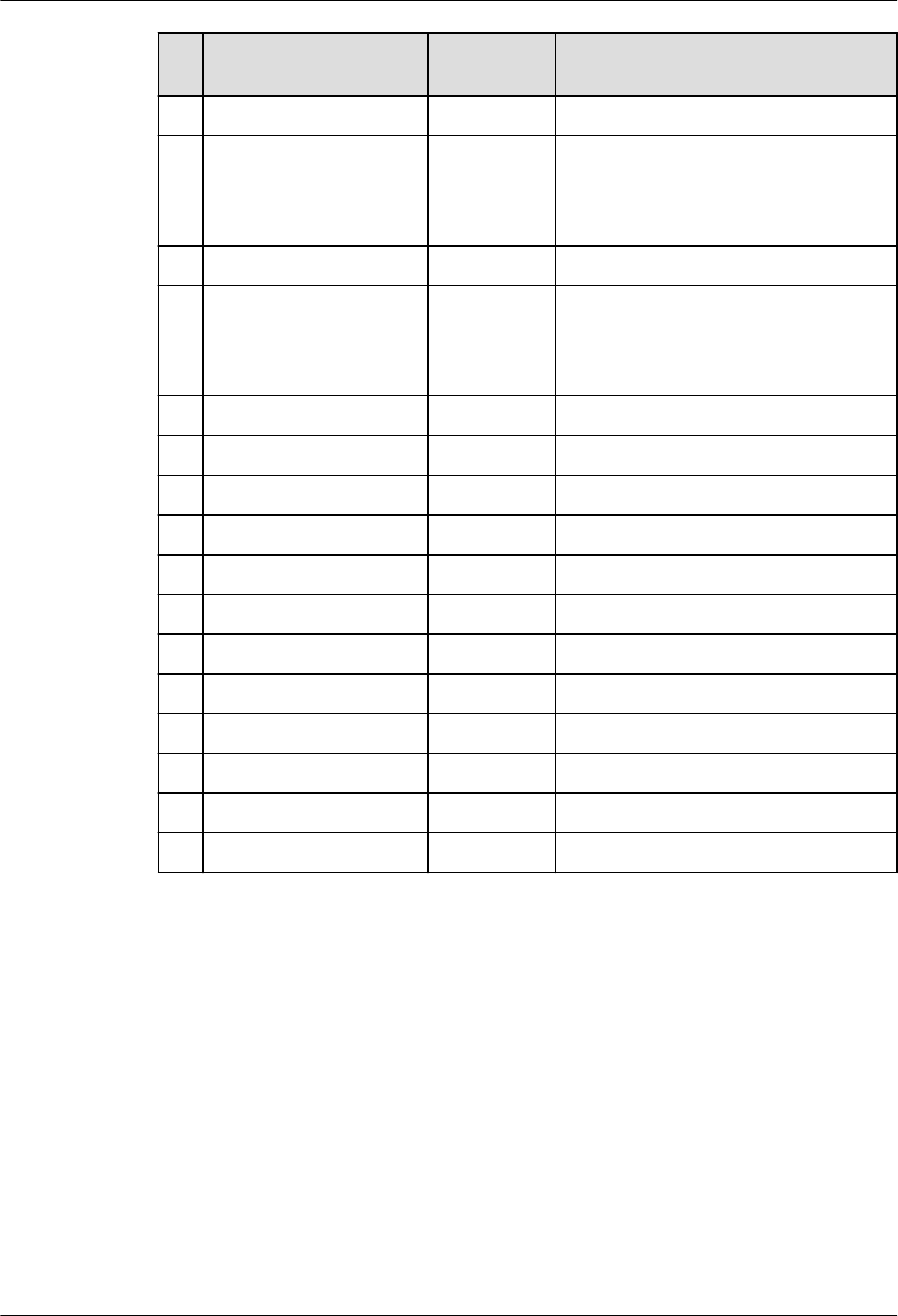
N
o.
MySQL GaussDB Dierence
9 YEARWEEK() Supported. -
10 DATE_ADD() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
11 DATE_FORMAT() Supported. -
12 DATE_SUB() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
13 DATEDIFF() Supported. -
14 DAY() Supported. -
15 DAYNAME() Supported. -
16 DAYOFMONTH() Supported. -
17 DAYOFWEEK() Supported. -
18 DAYOFYEAR() Supported. -
19 EXTRACT() Supported. -
20 FROM_DAYS() Supported. -
21 FROM_UNIXTIME() Supported. -
22 GET_FORMAT() Supported. -
23 HOUR() Supported. -
24 LAST_DAY Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 536

N
o.
MySQL GaussDB Dierence
25 LOCALTIME(),
LOCALTIME
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only integer values within
the range of [0,6] as the precision
of the returned time. For other
integer values, an error is reported.
The valid precision value in MySQL
is within [0,6], but the input integer
value is modulated by 256. For
example, if the input integer value
is 257, the time value with
precision 1 is returned.
26 LOCALTIMESTAMP,
LOCALTIMESTAMP()
Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only the input integer
value within the range of [0,6] as
the precision of the returned time.
If the input integer value is greater
than 6, an alarm is generated and
the time value is output based on
the precision 6. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
27 MAKEDATE() Supported. -
28 MAKETIME() Supported. When the input parameter is NULL,
GaussDB does not support self-
nesting of the maketime function,
but MySQL supports.
29 MICROSECOND() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 537

N
o.
MySQL GaussDB Dierence
30 MINUTE() Supported. -
31 MONTH() Supported. -
32 MONTHNAME() Supported. -
33 NOW() Supported. The time value (after the decimal
point) output by precision is
rounded o in GaussDB and
directly truncated in MySQL. The
last 0 of the time value (after the
decimal point) output by precision
is not displayed in GaussDB but
displayed in MySQL. GaussDB
supports only the input integer
value within the range of [0,6] as
the precision of the returned time.
If the input integer value is greater
than 6, an alarm is generated and
the time value is output based on
the precision 6. The valid precision
value in MySQL is within [0,6], but
the input integer value is
modulated by 256. For example, if
the input integer value is 257, the
time value with precision 1 is
returned.
34 PERIOD_ADD() Supported. If the input parameter period or
result is less than 0, GaussDB
reports an error by referring to the
performance in MySQL 8.0.x.
Integer wrapping occurs in MySQL
5.7. As a result, the calculation
result is abnormal.
35 PERIOD_DIFF() Supported. If the input parameter or result is
less than 0, GaussDB reports an
error by referring to the
performance in MySQL 8.0.x.
Integer wrapping occurs in MySQL
5.7. As a result, the calculation
result is abnormal.
36 QUARTER() Supported. -
37 SEC_TO_TIME() Supported. -
38 SECOND() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 538

N
o.
MySQL GaussDB Dierence
39 STR_TO_DATE() Supported. Return value dierence: In
GaussDB, text is returned. In
MySQL, datetime and date are
returned.
40 SUBDATE() Supported. The performance of this function is
dierent from that of MySQL due
to interval expression dierences.
For details, see INTERVAL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 539
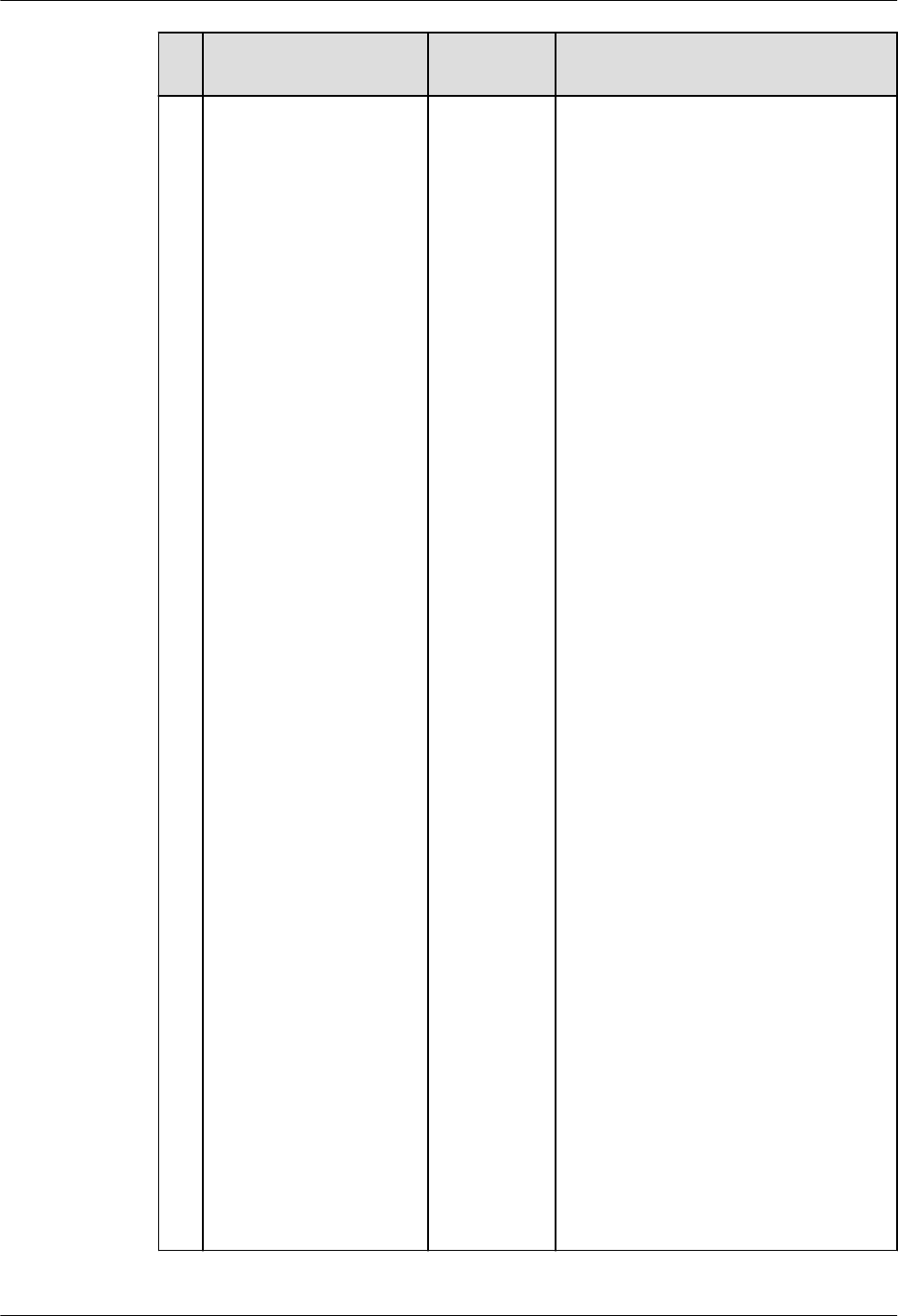
N
o.
MySQL GaussDB Dierence
41 SUBTIME() Supported. ● MySQL returns NULL if the
second input parameter is a
string in the DATETIME format.
GaussDB can calculate the value.
● The value range of an input
parameter is ['0001-01-01
00:00:00', 9999-12-31
23:59:59.999999].
● If the rst parameter of the
SUBTIME function in MySQL is a
dynamic parameter (for
example, in a prepared
statement), the return type is
TIME. Otherwise, the parse type
of the function is derived from
the parse type of the rst
parameter. The return value
rules of the SUBTIME function in
GaussDB are as follows:
– The rst input parameter is of
the date type, the second
input parameter is of the date
type, and the return value is
of the time type.
– The rst input parameter is of
the date type, the second
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the date type, the second
input parameter is of the
datetime type, and the return
value is of the time type.
– The rst input parameter is of
the date type, the second
input parameter is of the
time type, and the return
value is of the time type.
– The rst input parameter is of
the text type, the second
input parameter is of the date
type, and the return value is
of the text type.
– The rst input parameter is of
the text type, the second
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 540

N
o.
MySQL GaussDB Dierence
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the text type, the second
input parameter is of the
datetime type, and the return
value is of the text type.
– The rst input parameter is of
the text type, the second
input parameter is of the
time type, and the return
value is of the text type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the date
type, and the return value is
of the datetime type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the
datetime type, and the return
value is of the datetime type.
– The rst input parameter is of
the datetime type, the second
input parameter is of the
time type, and the return
value is of the datetime type.
– The rst input parameter is of
the time type, the second
input parameter is of the date
type, and the return value is
of the time type.
– The rst input parameter is of
the time type, the second
input parameter is of the text
type, and the return value is
of the text type.
– The rst input parameter is of
the time type, the second
input parameter is of the
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 541

N
o.
MySQL GaussDB Dierence
datetime type, and the return
value is of the time type.
– The rst input parameter is of
the time type, the second
input parameter is of the
time type, and the return
value is of the time type.
42 SYSDATE() Supported. The integer value of the MySQL
input parameter is wrapped when
reaching the maximum value 255
in one byte. The integer in GaussDB
is not wrapped.
43 YEAR() Supported. -
44 TIME_FORMAT() Supported. -
45 TIME_TO_SEC() Supported. -
46 TIMEDIFF() Supported. -
47 WEEKOFYEAR() Supported. -
48 TIMESTAMPADD() Supported. -
49 TIMESTAMPDIFF() Supported. -
50 TO_DAYS() Supported. -
51 TO_SECONDS() Supported. -
52 UNIX_TIMESTAMP() Supported. Return value dierence: In
GaussDB, numeric is returned. In
MySQL, int is returned.
53 UTC_DATE() Supported. MySQL supports calling without
parentheses, but GaussDB does not.
The integer value of the MySQL
input parameter is wrapped when
reaching the maximum value 255
in one byte.
MySQL input parameters support
only integers ranging from 0 to 6.
GaussDB supports input parameters
that can be implicitly converted to
integers ranging from 0 to 6.
54 UTC_TIME() Supported.
55 UTC_TIMESTAMP() Supported.
56 WEEK() Supported. -
57 WEEKDAY() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 542
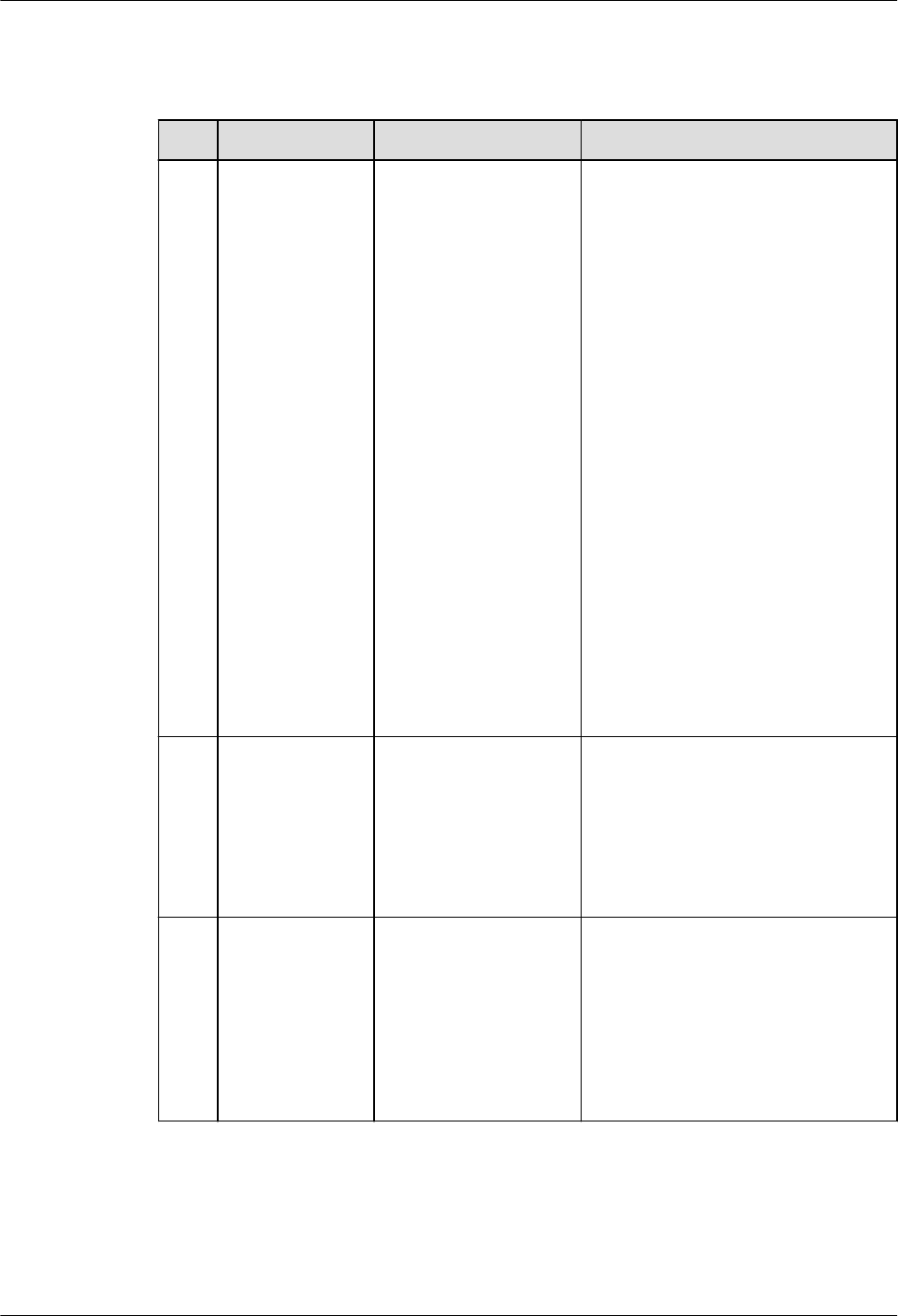
8.2.2.3.3 String Functions
Table 8-33 String functions
No. MySQL GaussDB Dierence
1 BIN() Supported. In GaussDB, the types supported
by function input parameter 1
are as follows:
● Integer types: tinyint,
smallint, mediumint, int, and
bigint.
● Unsigned integer types:
tinyint unsigned, smallint
unsigned, int unsigned, and
bigint unsigned.
● Character and text types:
char, varchar, tinytext, text,
mediumtext, and longtext.
Only numeric integer strings
are supported, and the
integer range is within the
bigint range.
● Floating-point types: oat,
real, and double.
● Fixed-point types: numeric,
decimal, and dec.
● Boolean type: bool.
2
CONCAT() Supported. The data type of the return
value of CONCAT is always text
regardless of the data type of
the parameter. However, in
MySQL, if CONCAT contains
binary parameters, the return
value is binary.
3 CONCAT_WS() Supported. The data type of the return
value of CONCAT_WS is always
text regardless of the data type
of the parameter. However, in
MySQL, if CONCAT_WS contains
binary parameters, the return
value is binary. In other cases,
the return value is a string.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 543

No. MySQL GaussDB Dierence
4 ELT() Supported. 1. In GaussDB, the types
supported by function input
parameter 1 are as follows:
● Integer types: tinyint,
smallint, mediumint, int,
and bigint.
● Unsigned integer types:
tinyint unsigned, smallint
unsigned, and int
unsigned.
● Character and text types:
char, varchar, tinytext, text,
mediumtext, and longtext.
Only numeric integer
strings are supported, and
the integer range is within
the bigint range.
● Floating-point types: oat,
real, and double.
● Fixed-point types: numeric,
decimal, and dec.
● Boolean type: bool.
2. In GaussDB, the types
supported by function input
parameter 2 are as follows:
● Integer types: tinyint,
smallint, mediumint, int,
and bigint.
● Unsigned integer types:
tinyint unsigned, smallint
unsigned, int unsigned,
and bigint unsigned.
● Character and text types:
char, varchar, tinytext, text,
mediumtext, and longtext.
● Floating-point types: oat,
real, and double.
● Fixed-point types: numeric,
decimal, and dec.
● Boolean type: bool.
● Large object types:
tinyblob, blob,
mediumblob, and
longblob.
● Date types: datetime,
timestamp, date, and time.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 544
No. MySQL GaussDB Dierence
5 FIELD() Supported. When function input parameters
range from the maximum bigint
value to the maximum bigint
unsigned value, incompatibility
occurs.
When function input parameters
are of oat(m, d), double(m, d),
or real(m, d) type, the precision
is higher and incompatibility
occurs.
6 FIND_IN_SET() Supported. When the database encoding is
set to 'SQL_ASCII', the default
case sensitivity rule is not
supported. That is, if no
character set rule is specied,
uppercase and lowercase letters
are treated as distinct.
7 INSERT() Supported. ● The range of input
parameters of the Int64 type
is from –
9223372036854775808 to
+9223372036854775807. If a
value is out of range, an error
is reported. MySQL does not
limit the range of input
parameters of the numeric
type. If an exception occurs,
an alarm is generated,
indicating that the value is set
to the upper or lower limit.
● The maximum length of the
input parameter of the text
type is 2^30 – 5 bytes, and
the maximum length of the
input parameter of the bytea
type is 2^30 – 512 bytes.
● If any of the s1 and s2
parameters is of the bytea
type and the result contains
invalid characters, the
displayed result may be
dierent from that of MySQL,
but the character encoding is
the same as that of MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 545

No. MySQL GaussDB Dierence
8 LOCATE() Supported. When input parameter 1 is of
the bytea type and input
parameter 2 is of the text type,
the behavior of GaussDB is
dierent from that of MySQL.
9 MAKE_SET() Supported. ● When the bits parameter is
an integer, the maximum
range is int128, which is
smaller than the MySQL
range.
● When the bits parameter is of
the date type (datetime,
timestamp, date, or time), it
is not supported because the
conversion from the date type
to the integer type is dierent
from that in MySQL.
● GaussDB and MySQL are
inherently dierent in the bit
and Boolean types, causing
dierent returned results.
When the bits input
parameter is of the Boolean
type, and the str input
parameter is of the bit or
Boolean type, they are not
supported.
● When the bits input
parameter is of the character
string or text type, only the
pure integer format is
supported. In addition, the
value range of pure integers
is limited to bigint.
● The integer value of the str
input parameter exceeds the
range from 81 negative nines
to 81 positive nines. The
return value is dierent from
that of MySQL.
● When the str input parameter
is expressed in scientic
notation, trailing zeros are
displayed in GaussDB but not
displayed in MySQL. This is an
inherent dierence.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 546

No. MySQL GaussDB Dierence
10 QUOTE() Supported. ● If the str character string
contains "\Z", "\r", "\%", or
"\_", GaussDB does not
escape it, which is dierent
from MySQL. The slash
followed by digits may also
cause dierences, for
example, "\563". This function
dierence is the escape
character dierence between
GaussDB and MySQL.
● The output format of "\b" in
the str character string is
dierent from that in MySQL.
This is an inherent dierence
between GaussDB and
MySQL.
● If the str character string
contains "\0", GaussDB
cannot identify the character
because the UTF-8 character
set cannot identify the
character. As a result, the
input fails. This is an inherent
dierence between GaussDB
and MySQL.
● If str is of the bit or Boolean
type, this type is not
supported because it is
dierent in GaussDB and
MySQL.
● GaussDB supports a
maximum of 1 GB data
transfer. The maximum length
of the str input parameter is
536870908, and the
maximum size of the result
string returned by the
function is 1 GB.
● The integer value of the str
input parameter exceeds the
range from 81 negative nines
to 81 positive nines. The
return value is dierent from
that of MySQL.
● When the str input parameter
is expressed in scientic
notation, trailing zeros are
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 547
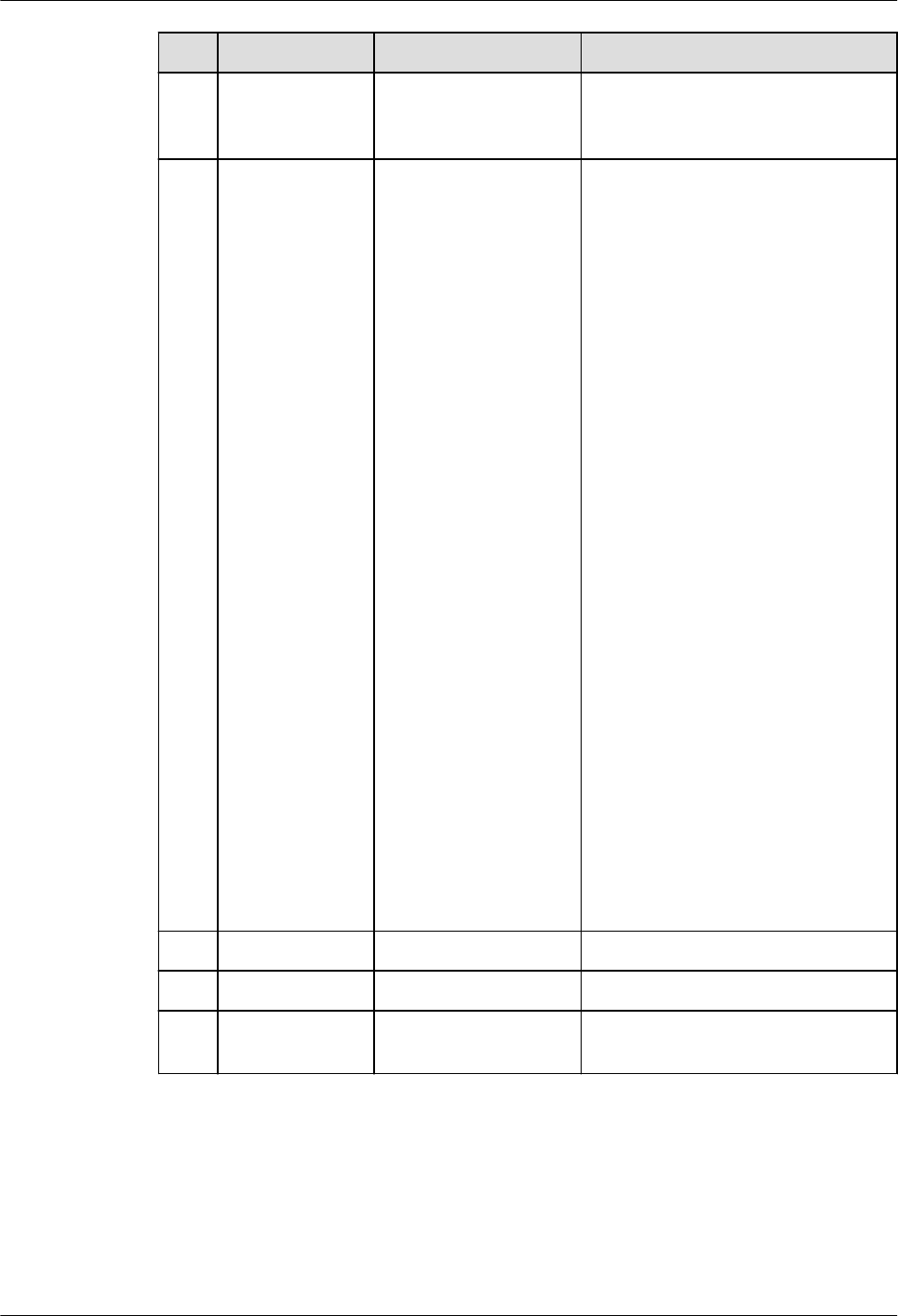
No. MySQL GaussDB Dierence
displayed in GaussDB but not
displayed in MySQL. This is an
inherent dierence.
11 SPACE() Supported. The maximum value of GaussDB
input parameter 1 is
1073741818. If the value
exceeds 1073741818, an empty
string is returned. By default, the
maximum value of MySQL input
parameter 1 is 4194304. If the
value exceeds 4194304, an alarm
is generated.
In GaussDB, the types supported
by function input parameter 1
are as follows:
● Integer types: tinyint,
smallint, mediumint, int, and
bigint.
● Unsigned integer types:
tinyint unsigned, smallint
unsigned, and int unsigned.
● Character and text types:
char, varchar, tinytext, text,
mediumtext, and longtext.
Only numeric integer strings
are supported, and the
integer range is within the
bigint range.
● Floating-point types: oat,
real, and double.
● Fixed-point types: numeric,
decimal, and dec.
● Boolean type: bool.
12
SUBSTR() Supported. -
13 SUBSTRING() Supported. -
14 SUBSTRING_IN
DEX()
Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 548

No. MySQL GaussDB Dierence
15 STRCMP() Supported. 1. Dierent from MySQL,
GaussDB supports the
following input parameter
types:
● Character types: CHAR,
VARCHAR, NVARCHAR2,
and TEXT.
● Binary type: BYTEA.
● Numeral types: TINYING
[UNSIGNED], SMALLINT
[UNSIGNED], INTEGER
[UNSIGNED], BIGINT
[UNSIGNED], FLOAT4,
FLOAT8, and NUMERIC.
● Date and time types:
DATE, TIME WITHOUT
TIME ZONE, DATETIME,
and TIMESTAMPTZ.
2. For the oating-point type in
the numeric type, the
precision may be dierent
from that in MySQL due to
dierent connection
parameter settings. Therefore,
this scenario is not
recommended, or the
NUMERIC type is used
instead.
16
SHA() /
SHA1()
Supported. -
17 SHA2() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 549

8.2.2.3.4 Forced Conversion Functions
Table 8-34 Forced conversion functions
No. MySQL GaussDB Dierence
1 CAST() Supported The data type
conversion rules
and supported
conversion
types are
subject to the
conversion
scope and rules
supported by
GaussDB.
2 CONVERT() Supported The data type
conversion rules
and supported
conversion
types are
subject to the
conversion
scope and rules
supported by
GaussDB.
8.2.2.3.5 Encryption Functions
Table 8-35 Encryption functions
No.
MySQL GaussDB Diere
nce
1 AES_DECRYPT() Supported. -
2 AES_ENCRYPT() Supported. -
8.2.2.3.6 Information Functions
Table 8-36 Information functions
No.
MySQL GaussDB Diere
nce
1 LAST_INSERT_ID() Supported -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 550
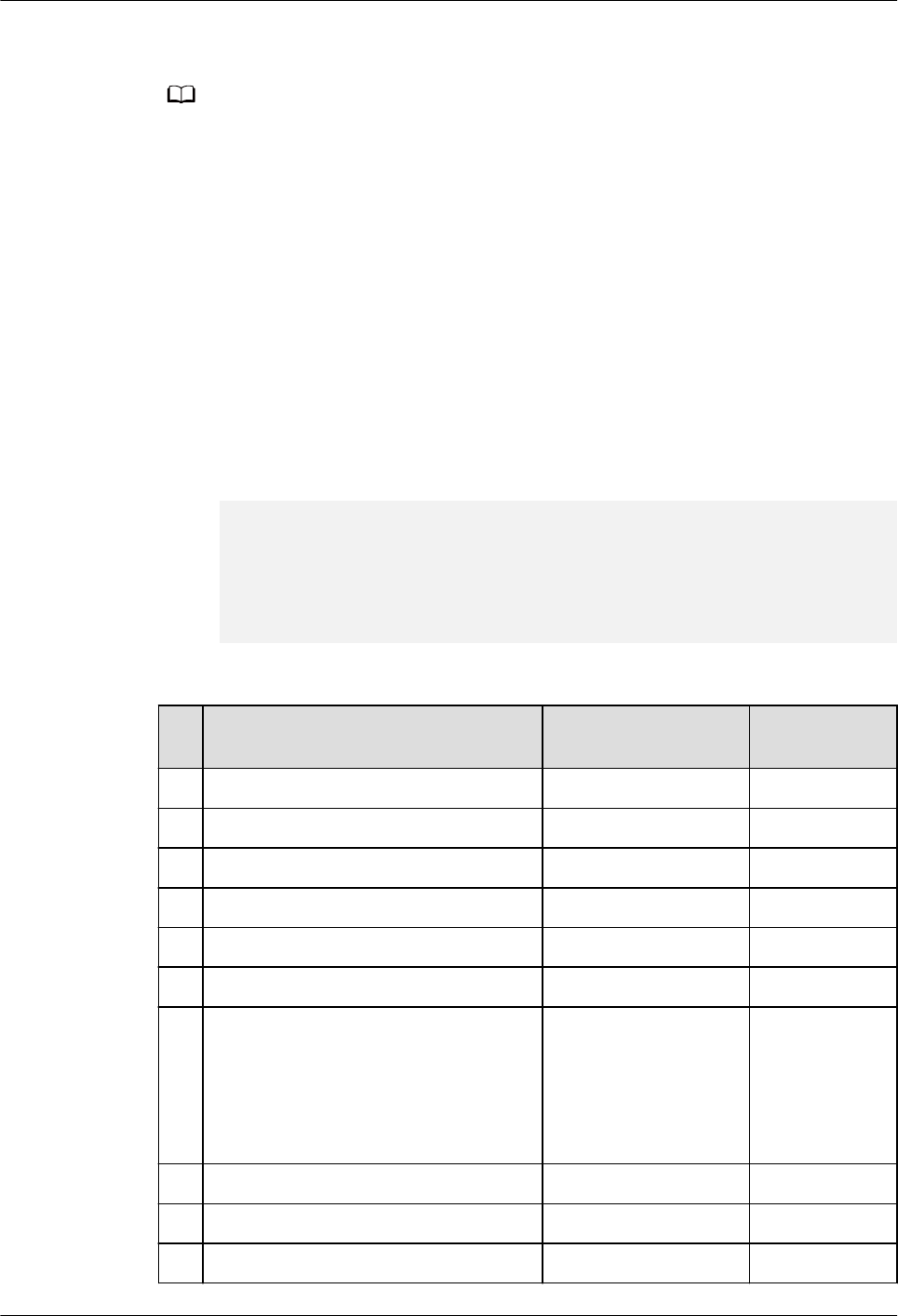
8.2.2.3.7 JSON Functions
NO TE
JSON function dierences:
1. For JSON functions and other character input parameter functions, if the input contains
escape characters, you need to set the GUC parameter set
standard_conforming_strings to o, which is dierent from MySQL by default. In this
case, escape characters are compatible with MySQL. However, a warning alarm is
generated for non-standard character input. Escape characters \t and \u, and escape
digits are dierent from those in MySQL. If the GUC parameter is not set, the
JSON_UNQUOTE() function is still compatible with MySQL and no alarm is reported.
2. When processing an ultra-long number (the number contains more than 64 characters),
the JSON function of GaussDB parses the number as a DOUBLE and uses scientic
notation for counting. The input parameters of the non-JSON type are the same as
those of MySQL. However, when input parameters of the JSON type are used, the JSON
type is not completely compatible with MySQL. As a result, dierences occur in this
scenario. MySQL displays complete numbers. (When the number length exceeds 82,
MySQL displays an incorrect result.) GaussDB still parses an ultra-long number into a
double-precision value. Long numbers are stored using oating-point numbers. During
calculation, precision loss occurs in both GaussDB and MySQL. Therefore, you are
advised to use character strings to store long numbers.
gaussdb=# select json_insert('[1, 4,
99999999999999999999999999999999999999999999999999999999999999999999999999]','$[6]',j
son_insert('[1,4]','$[5]',99999999999999999999999999999999999999999999999999999999999999
999999999999));
json_insert
------------------------------
[1, 4, 1e+74, [1, 4, 1e+74]]
(1 row)
Table 8-37 JSON functions
N
o.
MySQL GaussDB Dierence
1 JSON_APPEND() Supported. -
2 JSON_ARRAY() Supported. -
3 JSON_ARRAY_APPEND() Supported. -
4 JSON_ARRAY_INSERT() Supported. -
5 JSON_CONTAINS() Supported. -
6 JSON_CONTAINS_PATH() Supported. -
7 JSON_DEPTH() Supported. Return value
dierence: In
GaussDB, int
is returned. In
MySQL, bigint
is returned.
8 JSON_EXTRACT() Supported. -
9 JSON_INSERT() Supported. -
10 JSON_KEYS() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 551

N
o.
MySQL GaussDB Dierence
11 JSON_LENGTH() Supported. Return value
dierence: In
GaussDB, int
is returned. In
MySQL, bigint
is returned.
12 JSON_MERGE() Supported. -
13 JSON_OBJECT() Supported. -
14 JSON_QUOTE() Supported. Return value
dierence: In
GaussDB,
JSON is
returned. In
MySQL,
varchar or
text is
returned.
15 JSON_REMOVE() Supported. -
16 JSON_REPLACE() Supported. -
17 JSON_SEARCH() Supported. Return value
dierence: In
GaussDB, text
is returned. In
MySQL, JSON
is returned.
18 JSON_SET() Supported. -
19 JSON_TYPE() Supported. JSON values
of the
numeric type
are identied
as number,
which is
dierent from
MySQL.
20 JSON_UNQUOTE() Supported. -
21 JSON_VALID() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 552

8.2.2.3.8 Aggregate Functions
Table 8-38 Aggregate functions
No. MySQL GaussDB Dierence
1 GROUP_CONCAT() Supported. If the group_concat parameter
contains both the DISTINCT and
ORDER BY syntaxes, all
expressions following ORDER BY
must be in the DISTINCT
expression.
group_concat(... order by
Number
) does not indicate the
sequence of the parameter. The
number is only a constant
expression, which is equivalent
to no sorting.
The data type of the return
value of group_concat is always
text regardless of the data type
of the parameter. For MySQL, if
group_concat contains binary
parameters, the return value is
binary. In other cases, the return
value is a character string. If the
return value length is greater
than 512 bytes, the data type is
a character large object or
binary large object.
The value of
group_concat_max_len ranges
from 0 to 1073741823. The
maximum value is smaller than
that of MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 553
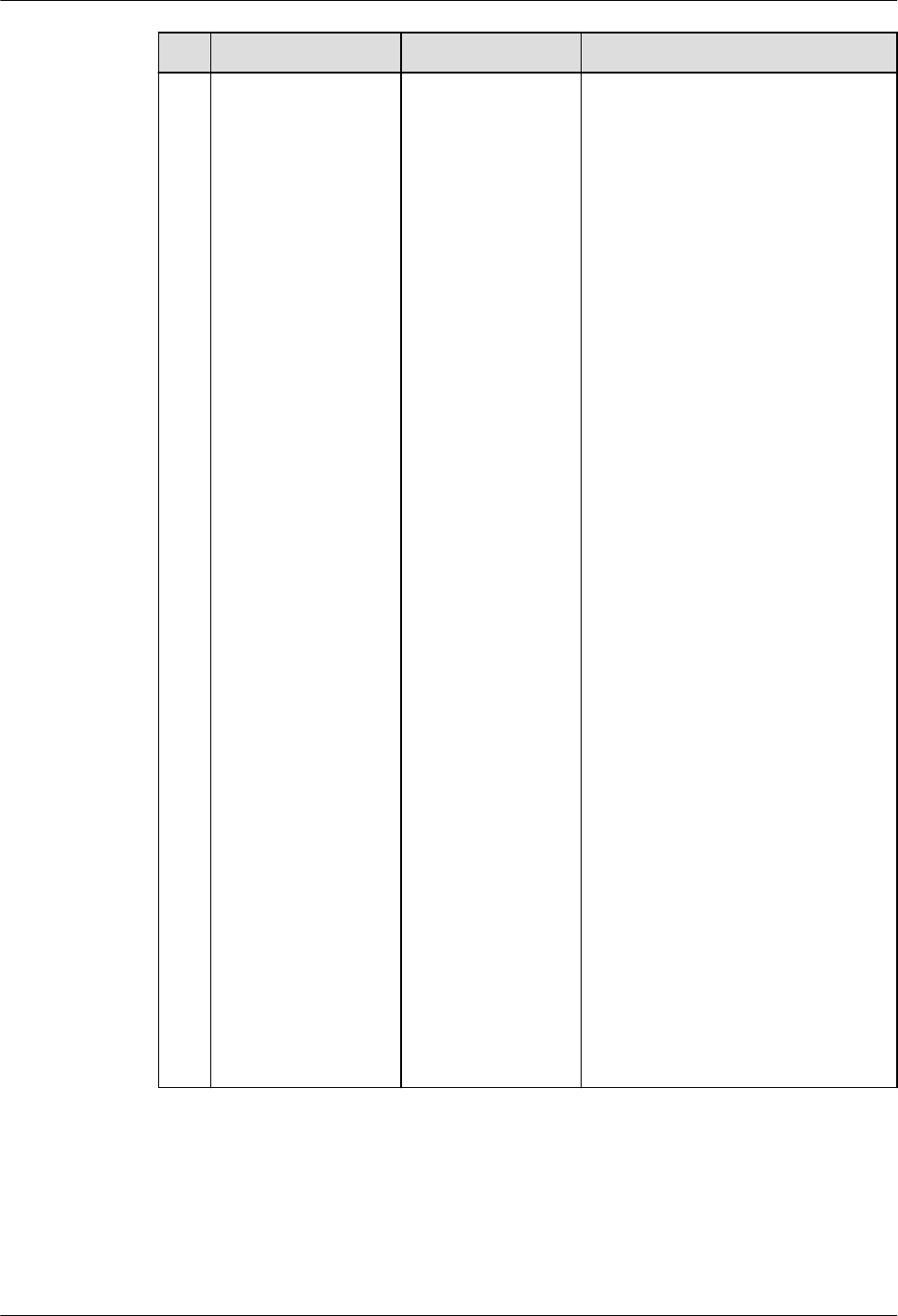
No. MySQL GaussDB Dierence
2 DEFAULT() Supported. ● The default value of a column
is an array. GaussDB returns
an array. MySQL does not
support the array type.
● GaussDB columns are hidden
columns (such as xmin and
cmin). The default function
returns a null value.
● GaussDB supports default
values of partitioned tables,
temporary tables, and multi-
table join query.
● GaussDB supports the query
of nodes whose column
names contain character
string values (indicating
names) and A_Star nodes
(indicating that asterisks [*]
appear), for example,
default(tt.t4.id) and
default(tt.t4.*). For invalid
query column names and
A_Star nodes, the error
information reported by
GaussDB is dierent from
that reported by MySQL.
● When the default value of a
column is created in GaussDB,
the range of the column type
is not veried. As a result, an
error may be reported when
the default function is used.
● If the default value of a
column is a function
expression, the default
function in GaussDB returns
the calculated value of the
default expression of the
column during table creation.
The default function in
MySQL returns NULL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 554

8.2.2.3.9 Arithmetic Functions
Table 8-39 Arithmetic functions
No. MySQ
L
Gauss
DB
Dierence
1 log2() Suppor
ted.
● The display of decimal places is dierent from that
in MySQL. Due to the restriction of the GaussDB
oating-point data type, the extra_oat_digits
parameter is used to control the number of
decimal places to be displayed.
● Due to the internal processing dierence of the
input precision, the calculation results of GaussDB
and MySQL are dierent.
● The following data types are supported: integer
types (bigint, int16, int, smallint, and tinyint);
unsigned integer types (bigint unsigned, integer
unsigned, smallint unsigned, and tinyint unsigned);
oating-point types (numeric and real); character
string types (character, character varying, clob,
text, and numeric, but only numeric integer strings
are supported); set type; NULL type.
2 log10(
)
Suppor
ted.
● The display of decimal places is dierent from that
in MySQL. Due to the restriction of the GaussDB
oating-point data type, the extra_oat_digits
parameter is used to control the number of
decimal places to be displayed.
● Due to the internal processing dierence of the
input precision, the calculation results of GaussDB
and MySQL are dierent.
● The following data types are supported: integer
types (bigint, int16, int, smallint, and tinyint);
unsigned integer types (bigint unsigned, integer
unsigned, smallint unsigned, and tinyint unsigned);
oating-point types (numeric and real); character
string types (character, character varying, clob,
text, and numeric, but only numeric integer strings
are supported); set type; NULL type.
8.2.2.3.10 Other Functions
Table 8-40 Other functions
No.
MySQL GaussDB Dierence
1 UUID() Supported -
2 UUID_SHORT() Supported -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 555

8.2.2.4 Operators
GaussDB is compatible with most MySQL operators, but there are some
dierences. If not listed, the operator behavior is the native GaussDB behavior by
default.
Table 8-41 Operators
No. MySQL GaussDB Dierence
1 NULL-safe equal
(<=>)
Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 556

No. MySQL GaussDB Dierence
2 [NOT] REGEXP Supported. ● When b_format_dev_version
is set to 's2', the pattern
string contains escape
characters such as '\\a', '\\d',
'\\e', '\\n', '\\Z', and '\\u', and
the source strings '\a', '\d',
'\e', '\n', '\Z', and '\u' are
matched, the behavior of
GaussDB is dierent from
that of MySQL 5.7. MySQL
5.7 has a bug, which has
been xed in later MySQL
versions and is now
consistent with GaussDB.
● When b_format_dev_version
is set to 's2', GaussDB's '\b'
can match '\\b', but MySQL
cannot.
● GaussDB reports an error
when the input parameter of
the pattern string pat is
invalid and only the right
single parenthesis ')' exists.
MySQL has a bug, which has
been xed in later versions.
● When de|abc matches de or
abc, if there is a null value
on the left or right of |,
MySQL reports an error. This
bug has been xed in later
versions.
● The regular expression of the
blank character [\t] can
match the character class
[:blank:] in GaussDB, but
MySQL's [\t] cannot match
[:blank:]. MySQL has a bug,
which has been xed in later
versions.
● GaussDB supports non-
greedy pattern matching.
That is, the number of
matching characters is as
small as possible. A question
mark (?) is added after some
special characters, for
example, ??, *?, +?, {n}?,
{n,}?, and {n,m}?. MySQL 5.7
does not support non-greedy
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 557

No. MySQL GaussDB Dierence
pattern matching, and the
error message "Got error
'repetition-operator operand
invalid' from regexp" is
displayed. MySQL 8.0 already
supports this function.
● In the binary character set,
the text and BLOB types are
converted to the bytea type.
The REGEXP operator does
not support the bytea type.
Therefore, the two types
cannot be matched.
3 [NOT] RLIKE Supported. Same as [NOT] REGEXP.
8.2.2.5 Character Sets
GaussDB allows you to specify the following character sets for databases,
schemas, tables, or columns.
Table 8-42 Character sets
No.
MySQL GaussDB
1 utf8mb4 Supported.
2 gbk Supported.
3 gb18030 Supported.
4 utf8 Supported.
5 binary Supported.
8.2.2.6 Collation Rules
GaussDB allows you to specify the following collation rules for databases,
schemas, tables, or columns.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 558

NO TE
Dierences in collation rules:
● Currently, only the character string type and some binary types support the specied
collation rules. You can check whether the typcollation attribute of a type in the
pg_type system catalog is not 0 to determine whether the type supports the collation.
The collation can be specied for all types in MySQL. However, collation rules are
meaningless except those for character strings and binary types.
● The current collation rules (except binary) can be specied only when the corresponding
character set is the same as the database-level character set. In GaussDB, the character
set must be the same as the database character set, and multiple character sets cannot
be used together in a table.
● The default collation of the utf8mb4 character set is utf8mb4_general_ci, which is the
same as that in MySQL 5.7.
● In GaussDB, utf8 and utf8mb4 are the same character set.
Table 8-43 Collation rules
No. MySQL GaussDB
1 utf8mb4_general_ci Supported.
2 utf8mb4_unicode_ci Supported.
3 utf8mb4_bin Supported.
4 gbk_chinese_ci Supported.
5 gbk_bin Supported.
6 gb18030_chinese_ci Supported.
7 gb18030_bin Supported.
8 binary Supported.
9 utf8mb4_0900_ai_ci Supported.
10 utf8_general_ci Supported.
11 utf8_bin Supported.
8.2.2.7 Expressions
GaussDB is compatible with most MySQL expressions, but there are some
dierences. If not listed, the expression behavior is the native GaussDB behavior
by default.
Table 8-44 Expressions
No.
MySQL GaussDB
1 User-dened variable @var_name Partially supported
2 Global variable @@var_name Partially supported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 559

8.2.2.8 SQL
GaussDB is compatible with most MySQL syntax, but there are some dierences.
This chapter describes the MySQL syntax supported by GaussDB.
8.2.2.8.1 DDL
No. MySQL Function Syntax GaussDB
Implementation
Dierence
1 Create primary
keys, UNIQUE
indexes, and
foreign keys during
table creation and
modication.
ALTER TABLE and
CREATE TABLE
● GaussDB does not
support the UNIQUE
INDEX|KEY
index_name syntax.
An error will be
reported when the
UNIQUE INDEX|KEY
index_name syntax is
used.
● When a constraint is
created as a global
secondary index and
USING BTREE is
specied in the SQL
statement, the
underlying index is
created as UB-tree.
● When the table joined
with the constraint is
Ustore and USING
BTREE is specied in
the SQL statement,
the underlying index
is created as UB-tree.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 560

No. MySQL Function Syntax GaussDB
Implementation
Dierence
2 Support auto-
increment
columns.
ALTER TABLE and
CREATE TABLE
● It is recommended
that the auto-
increment column be
the rst column of a
non-global secondary
index. Otherwise, an
alarm is generated
when a table is
created, and errors
may occur when some
operations are
performed on a table
that contains auto-
increment columns,
for example, ALTER
TABLE EXCHANGE
PARTITION. The auto-
increment column in
MySQL must be the
rst column of the
index.
● In the syntax
AUTO_INCREMENT =
value, value must be
a positive number less
than 2^127. MySQL
does not verify the
value.
● An error occurs if the
auto-increment
continues after an
auto-increment value
reaches the maximum
value of a column
data type. In MySQL,
errors or warnings
may be generated
during auto-
increment, and
sometimes auto-
increment continues
until the maximum
value is reached.
● GaussDB does not
support the
innodb_autoinc_lock_
mode
system variable,
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 561

No. MySQL Function Syntax GaussDB
Implementation
Dierence
but when its GUC
parameter
auto_increment_cach
e is set to 0, the
behavior of inserting
auto-increment
columns in batches is
similar to that when
the MySQL system
variable
innodb_autoinc_lock_
mode
is set to 1.
● When 0s, NULLs, and
denite values are
imported or batch
inserted into auto-
increment columns,
the auto-increment
values inserted after
an error occurs in
GaussDB may not be
the same as those in
MySQL.
– The
auto_increment_c
ache parameter is
provided to control
the number of
reserved auto-
increment values.
● When auto-increment
is triggered by parallel
import or insertion of
auto-increment
columns, the cache
value reserved for
each parallel thread is
used only in the
thread. If the cache
value is not used up,
the values of auto-
increment columns in
the table are
discontinuous. The
auto-increment value
generated by parallel
insertion cannot be
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 562

No. MySQL Function Syntax GaussDB
Implementation
Dierence
guaranteed to be the
same as that
generated in MySQL.
● When auto-increment
columns are batch
inserted into a local
temporary table, no
auto-increment value
is reserved. In normal
scenarios, auto-
increment values are
not discontinuous. In
MySQL, the auto-
increment result of an
auto-increment
column in a
temporary table is the
same as that in an
ordinary table.
● The SERIAL data type
of GaussDB is an
original auto-
increment column,
which is dierent
from the
AUTO_INCREMENT
column. The SERIAL
data type of MySQL is
the
AUTO_INCREMENT
column.
● The value of
auto_increment_os
et cannot be greater
than that of
auto_increment_incr
ement. Otherwise, an
error occurs. MySQL
allows it and states
that
auto_increment_os
et will be ignored.
● If a table has a
primary key or index,
the sequence in which
the ALTER TABLE
command rewrites
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 563

No. MySQL Function Syntax GaussDB
Implementation
Dierence
table data may be
dierent from that in
MySQL. GaussDB
rewrites table data
based on the table
data storage
sequence, while
MySQL rewrites table
data based on the
primary key or index
sequence. As a result,
the auto-increment
sequence may be
dierent.
● When the ALTER
TABLE command is
used to add or modify
auto-increment
columns, the number
of auto-increment
values reserved for
the rst time is the
number of rows in the
table statistics. The
number of rows in the
statistics may not be
the same as that in
MySQL.
● The return value of
the last_insert_id
function is a 128-bit
integer.
● When auto-increment
is performed in a
trigger or user-dened
function, the return
value of last_insert_id
is updated. MySQL
does not update it.
● If the values of the
GUC parameters
auto_increment_os
et and
auto_increment_incr
ement are out of
range, an error occurs.
MySQL automatically
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 564

No. MySQL Function Syntax GaussDB
Implementation
Dierence
changes the value to
a boundary value.
3 Support prex
indexes.
CREATE INDEX, ALTER
TABLE, and CREATE
TABLE
● The prex length
cannot exceed 2676.
The actual length of
the key value is
restricted by the
internal page. If a
column contains
multi-byte characters
or an index has
multiple keys, an error
may be reported
when the index line
length exceeds the
threshold.
● In the CREATE INDEX
syntax, the following
keywords cannot be
used as prex keys for
column names:
COALESCE, EXTRACT,
GREATEST, LEAST,
LNNVL, NULLIF, NVL,
NVL2, OVERLAY,
POSITION,
REGEXP_LIKE,
SUBSTRING,
TIMESTAMPDIFF,
TREAT, TRIM,
XMLCONCAT,
XMLELEMENT,
XMLEXISTS,
XMLFOREST,
XMLPARSE, XMLPI,
XMLROOT, and
XMLSERIALIZE.
● Prex keys are not
supported in primary
key indexes.
4
Specify character
sets and collation
rules.
ALTER SCHEMA,
ALTER TABLE, CREATE
SCHEMA, and CREATE
TABLE
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 565
No. MySQL Function Syntax GaussDB
Implementation
Dierence
5 Add columns
before the rst
column of a table
or after a specied
column during
table modication.
ALTER TABLE -
6 Compatible with
the column name
modication and
the denition
syntax.
ALTER TABLE -
7 Compatible with
the EVENT syntax
of a scheduled
task.
ALTER EVENT, CREATE
EVENT, DROP EVENT,
and SHOW EVENTS
-
8 Compatible with
the syntax for
creating
partitioned tables.
CREATE TABLE
PARTITION and
CREATE TABLE
SUBPARTITION
-
9 Specify table-level
and column-level
comments during
table creation and
modication.
CREATE TABLE and
ALTER TABLE
-
10 Specify index-level
comments during
index creation.
CREATE INDEX -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 566

No. MySQL Function Syntax GaussDB
Implementation
Dierence
11 Exchange the
partition data of
an ordinary table
and a partitioned
table.
ALTER TABLE
PARTITION
Dierences in ALTER
TABLE EXCHANGE
PARTITION:
● For auto-increment
columns, after the
ALTER EXCHANGE
PARTITION is
executed in MySQL,
the auto-increment
columns are reset. In
GaussDB, the auto-
increment columns
are not reset, and the
auto-increment
columns increase
based on the old
auto-increment value.
● If MySQL tables or
partitions use
tablespaces, data in
partitions and
ordinary tables cannot
be exchanged. If
GaussDB tables or
partitions use
dierent tablespaces,
data in partitions and
ordinary tables can
still be exchanged.
● MySQL does not
verify the default
values of columns.
Therefore, data in
partitions and
ordinary tables can be
exchanged even if the
default values are
dierent. GaussDB
veries the default
values. If the default
values are dierent,
data in partitions and
ordinary tables cannot
be exchanged.
● After the DROP
COLUMN operation is
performed on a
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 567

No. MySQL Function Syntax GaussDB
Implementation
Dierence
partitioned table or
an ordinary table in
MySQL, if the table
structure is still
consistent, data can
be exchanged
between partitions
and ordinary tables. In
GaussDB, data can be
exchanged between
partitions and
ordinary tables only
when the deleted
columns of ordinary
tables and partitioned
tables are strictly
aligned.
● MySQL and GaussDB
use dierent hash
algorithms. Therefore,
data stored in the
same hash partition
may be inconsistent.
As a result, the
exchanged data may
also be inconsistent.
● MySQL partitioned
tables do not support
foreign keys. If an
ordinary table
contains foreign keys
or other tables
reference foreign keys
of an ordinary table,
data in partitions and
ordinary tables cannot
be exchanged.
GaussDB partitioned
tables support foreign
keys. If the foreign
key constraints of two
tables are the same,
data in partitions and
ordinary tables can be
exchanged. If a
GaussDB partitioned
table does not contain
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 568

No. MySQL Function Syntax GaussDB
Implementation
Dierence
foreign keys, an
ordinary table is
referenced by other
tables, and the
partitioned table is
the same as the
ordinary table, data in
the partitioned table
can be exchanged
with that in the
ordinary table.
12 Delete the primary
key and foreign
key constraints of
a table.
ALTER TABLE DROP
[PRIMARY |
FOREIGN]KEY
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 569
No. MySQL Function Syntax GaussDB
Implementation
Dierence
13 Compatible with
the CREATE
TABLE... LIKE
syntax.
CREATE TABLE ... LIKE ● In versions earlier
than MySQL 8.0.16,
CHECK constraints are
parsed but their
functions are ignored.
In this case, CHECK
constraints are not
replicated. GaussDB
supports replication of
CHECK constraints.
● When a table is
created, all primary
key constraint names
in MySQL are xed to
PRIMARY KEY.
GaussDB does not
support replication of
primary key constraint
names.
● When a table is
created, MySQL
supports replication of
unique key constraint
names, but GaussDB
does not.
● When a table is
created, MySQL
versions earlier than
8.0.16 do not have
CHECK constraint
information, but
GaussDB supports
replication of CHECK
constraint names.
● When a table is
created, MySQL
supports replication of
index names, but
GaussDB does not.
● When a table is
created across
sql_mode, MySQL is
controlled by the
loose mode and strict
mode. The strict mode
may become invalid in
GaussDB.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 570

No. MySQL Function Syntax GaussDB
Implementation
Dierence
For example, if the
source table has the
default value
"0000-00-00",
GaussDB can create a
table that contains
the default value
"0000-00-00" in
"no_zero_date" strict
mode, which means
that the strict mode is
invalid. MySQL fails to
create the table
because it is
controlled by the strict
mode.
● MySQL supports
cross-database table
creation, but GaussDB
does not.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 571

No. MySQL Function Syntax GaussDB
Implementation
Dierence
14 Compatible with
syntax for
changing table
names.
ALTER TABLE
tbl_name RENAME
[TO | AS | =]
new_tbl_name;
RENAME {TABLE |
TABLES} tbl_name TO
new_tbl_name [,
tbl_name2 TO
new_tbl_name2, ...];
● The ALTER RENAME
syntax in GaussDB
supports only the
function of changing
the table name and
cannot be coupled
with other function
operations.
● In GaussDB, only the
old table name
column supports the
usage of
schema.table_name,
and the new and old
table names belong to
the same schema.
● GaussDB does not
support renaming of
old and new tables
across schemas.
However, if you have
the permission, you
can modify the names
of tables in other
schemas in the
current schema.
● The syntax for
renaming multiple
groups of tables in
GaussDB supports
renaming of all local
temporary tables, but
does not support the
combination of local
temporary tables and
non-local temporary
tables.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 572

No. MySQL Function Syntax GaussDB
Implementation
Dierence
15 Compatible with
the subpartition
addition syntax.
ALTER TABLE [ IF
EXISTS ] { table_name
[*] | ONLY table_name
| ONLY
( table_name )}
action [, ... ];
action:
move_clause |
exchange_clause |
row_clause |
merge_clause |
modify_clause |
split_clause |
add_clause |
drop_clause |
ilm_clause
add_clause:
ADD
{{partition_less_than_i
tem |
partition_start_end_ite
m | partition_list_item}
|
PARTITION({partition_
less_than_item |
partition_start_end_ite
m |
partition_list_item})}
● The following syntax
cannot be used to add
multiple partitions:
ALTER TABLE table_name
ADD PARTITION
(partition_denition1,
partition_denition1,...);
● Only the original
syntax for adding
multiple partitions is
supported.
ALTER TABLE table_name
ADD PARTITION
(partition_denition1), ADD
PARTITION
(partition_denition2[y1] ), ..
.;
8.2.2.8.2 DML
No.
MySQL Function Syntax GaussDB Implementation
Dierence
1 DELETE supports
deleting data from
multiple tables.
DELETE -
2 DELETE supports
ORDER BY and LIMIT.
DELETE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 573

No. MySQL Function Syntax GaussDB Implementation
Dierence
3 DELETE supports
deleting data from a
specied partition (or
subpartition).
DELETE -
4 UPDATE supports
updating data from
multiple tables.
UPDATE -
5 UPDATE supports
ORDER BY and LIMIT.
UPDATE -
6 The syntax is
compatible with SELECT
INTO.
SELECT ● In GaussDB, you can use
SELECT INTO to create a table
based on the query result.
MySQL does not support this
function.
● In GaussDB, the SELECT INTO
syntax does not support the
query result that is obtained
after the set operation of
multiple queries is performed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 574

No. MySQL Function Syntax GaussDB Implementation
Dierence
7 The syntax is
compatible with
REPLACE INTO.
REPLACE ● Dierence between the initial
values of the time type. For
example:
– MySQL is not aected by
the strict or loose mode.
You can insert time 0 into
a table.
mysql> CREATE TABLE test(f1
TIMESTAMP NOT NULL, f2
DATETIME NOT NULL, f3 DATE
NOT NULL);
Query OK, 1 row aected (0.00 sec)
mysql> REPLACE INTO test
VALUES(f1, f2, f3);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+---------------------
+---------------------+------------+
| f1 | f2 |
f3 |
+---------------------
+---------------------+------------+
| 0000-00-00 00:00:00 | 0000-00-00
00:00:00 | 0000-00-00 |
+---------------------
+---------------------+------------+
1 row in set (0.00 sec)
– The time 0 can be
successfully inserted only
when GaussDB is in loose
mode.
gaussdb=# SET b_format_version =
'5.7';
SET
gaussdb=# SET
b_format_dev_version = 's1';
SET
gaussdb=# SET sql_mode = '';
SET
gaussdb=# CREATE TABLE test(f1
TIMESTAMP NOT NULL, f2
DATETIME NOT NULL, f3 DATE
NOT NULL);
CREATE TABLE
gaussdb=# REPLACE INTO test
VALUES(f1, f2, f3);
REPLACE 0 1
gaussdb=# SELECT * FROM test;
f1 | f2 | f3
---------------------
+---------------------+------------
0000-00-00 00:00:00 | 0000-00-00
00:00:00 | 0000-00-00
(1 row)
In strict mode, the error is
reported: date/time eld
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 575

No. MySQL Function Syntax GaussDB Implementation
Dierence
value out of range:
"0000-00-00 00:00:00".
● Dierence between the initial
values of the bit string type.
For example:
– The initial value of the BIT
type is an empty string '' in
MySQL, that is:
mysql> CREATE TABLE test(f1
BIT(3) NOT NULL);
Query OK, 0 rows aected (0.01
sec)
mysql> REPLACE INTO test
VALUES(f1);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT f1, f1 IS NULL
FROM test;
+----+------------+
| f1 | f1 is null |
+----+------------+
| | 0 |
| | 0 |
+----+------------+
2 rows in set (0.00 sec)
– If the initial value of the
BIT type is NULL in
GaussDB, an error is
reported.
gaussdb=# CREATE TABLE test(f1
BIT(3) NOT NULL);
CREATE TABLE
gaussdb=# REPLACE INTO test
VALUES(f1);
ERROR: null value in column "f1"
violates not-null constraint
DETAIL: Failing row contains (null).
8
SELECT supports multi-
partition query.
SELECT -
9 UPDATE supports
multi-partition update.
UPDATE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 576
No. MySQL Function Syntax GaussDB Implementation
Dierence
10 Import data by using
LOAD DATA.
LOAD
DATA
● The execution result of the
LOAD DATA syntax is the
same as that in MySQL strict
mode. The loose mode is not
adapted currently.
● The IGNORE and LOCAL
parameters are used only to
ignore the conicting rows
when the imported data
conicts with the data in the
table and to automatically ll
default values for other
columns when the number of
columns in the le is less than
that in the table. Other
functions are not supported
currently.
● If the keyword LOCAL is
specied and the le path is a
relative path, the le is
searched from the binary
directory. If the keyword
LOCAL is not specied and
the le path is a relative path,
the le is searched from the
data directory.
● If single quotation marks are
specied as separators, escape
characters, and line breaks in
the syntax, lexical parsing
errors occur.
● The [(col_name_or_user_var
[, col_name_or_user_var]...)]
parameter cannot be used to
specify a column repeatedly.
● The newline character
specied by [FIELDS
TERMINATED BY 'string']
cannot be the same as the
separator specied by [LINES
TERMINATED BY'string'].
● If the data written to a table
by running LOAD DATA
cannot be converted to the
data type of the table, an
error is reported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 577

No. MySQL Function Syntax GaussDB Implementation
Dierence
● The LOAD DATA SET
expression does not support
the calculation of a specied
column name.
● If there is no implicit
conversion function between
the return value type of the
SET expression and the
corresponding column type,
an error is reported.
● LOAD DATA applies only to
tables but not views.
● The default newline character
of the le in Windows is
dierent from that in Linux.
LOAD DATA cannot identify
this scenario and reports an
error. You are advised to check
the newline character at the
end of lines in the le to be
imported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 578

No. MySQL Function Syntax GaussDB Implementation
Dierence
11 Compatible with
INSERT IGNORE.
INSERT
IGNORE
● GaussDB displays the error
information after the
downgrade. MySQL records
the error information after
the downgrade to the error
stack and runs the show
warnings; command to view
the error information.
● Time type dierence. For
example:
– The default values of date,
datetime, and timestamp
in GaussDB are 0.
gaussdb=# CREATE TABLE test(f1
DATE NOT NULL, f2 DATETIME
NOT NULL, f3 TIMESTAMP NOT
NULL);
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test VALUES(NULL, NULL, NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null,
null, null, null).
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (null,
null, null, null).
WARNING: null value in column
"f3" violates not-null constraint
DETAIL: Failing row contains (null,
null, null, null).
INSERT 0 1
gaussdb=#
SELECT * FROM test;
f1 | f2 |
f3
------------+---------------------
+---------------------
1970-01-01 | 1970-01-01 00:00:00
| 1970-01-01 00:00:00
(1 row)
– The default values of date,
datetime, and timestamp
in MySQL are 0.
mysql> CREATE TABLE test(f1
DATE NOT NULL, f2 DATETIME
NOT NULL, f3 TIMESTAMP NOT
NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
VALUES(NULL, NULL, NULL);
Query OK, 1 row aected, 3
warnings (0.00 sec)
mysql> show warnings;
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 579

No. MySQL Function Syntax GaussDB Implementation
Dierence
+---------+------
+----------------------------+
| Level | Code |
Message |
+---------+------
+----------------------------+
| Warning | 1048 | Column 'f1'
cannot be null |
| Warning | 1048 | Column 'f2'
cannot be null |
| Warning | 1048 | Column 'f3'
cannot be null |
+---------+------
+----------------------------+
3 rows in set (0.00 sec)
mysql> SELECT * FROM test;
+------------+---------------------
+---------------------+
| f1 | f2 |
f3 |
+------------+---------------------
+---------------------+
| 0000-00-00 | 0000-00-00 00:00:00
| 0000-00-00 00:00:00 |
+------------+---------------------
+---------------------+
1 row in set (0.00 sec)
● GaussDB does not support the
MySQL bit type. Therefore,
the INSERT IGNORE error
downgrade is not supported
when the NOT NULL
constraint of the bit type is
ignored and the length of the
inserted bit type is dierent
from that dened.
– Bit type in GaussDB
gaussdb=# CREATE TABLE test(f1
BIT(10) NOT NULL);
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test VALUES(NULL);
ERROR: Un-support feature
DETAIL: ignore null for insert
statement is not supported in
column f1.
gaussdb=# INSERT IGNORE INTO
test VALUES('1010');
ERROR: bit string length 4 does
not match type bit(10)
CONTEXT: referenced column: f1
– Bit type in MySQL
mysql> CREATE TABLE test(f1
BIT(10) NOT NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 580

No. MySQL Function Syntax GaussDB Implementation
Dierence
VALUES(NULL);
Query OK, 1 row aected, 1
warning (0.00 sec)
mysql> INSERT IGNORE INTO test
VALUES('1010');
Query OK, 1 row aected, 1
warning (0.01 sec)
● If the precision is specied for
the time type in MySQL, the
precision is displayed when
the zero value is inserted. It is
not displayed in GaussDB. For
example:
– Time precision specied in
GaussDB
gaussdb=# CREATE TABLE test(f1
TIME(3) NOT NULL, f2
DATETIME(3) NOT NULL, f3
TIMESTAMP(3) NOT NULL);
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test VALUES(NULL,NULL,NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null,
null, null).
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (null,
null, null).
WARNING: null value in column
"f3" violates not-null constraint
DETAIL: Failing row contains (null,
null, null).
INSERT 0 1
gaussdb=# SELECT * FROM test;
f1 | f2 | f3
----------+---------------------
+---------------------
00:00:00 | 1970-01-01 00:00:00 |
1970-01-01 00:00:00
(1 row)
– Time precision specied in
MySQL
mysql> CREATE TABLE test(f1
TIME(3) NOT NULL, f2
DATETIME(3) NOT NULL, f3
TIMESTAMP(3) NOT NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
VALUES(NULL,NULL,NULL);
Query OK, 1 row aected, 3
warnings (0.00 sec)
mysql> SELECT * FROM test;
+--------------
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 581

No. MySQL Function Syntax GaussDB Implementation
Dierence
+-------------------------
+-------------------------+
| f1 | f2 |
f3 |
+--------------
+-------------------------
+-------------------------+
| 00:00:00.000 | 0000-00-00
00:00:00.000 | 0000-00-00
00:00:00.000 |
+--------------
+-------------------------
+-------------------------+
1 row in set (0.00 sec)
● The execution process in
MySQL is dierent from that
in GaussDB. Therefore, the
number of generated
warnings may be dierent.
For example:
– Number of warnings
generated in GaussDB
gaussdb=# CREATE TABLE test(f1
INT, f2 INT not null);
CREATE TABLE
gaussdb=# INSERT INTO test
VALUES(1,0),(3,0),(5,0);
INSERT 0 3
gaussdb=# INSERT IGNORE INTO
test SELECT f1+1, f1/f2 FROM test;
WARNING: division by zero
CONTEXT: referenced column: f2
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (2,
null).
WARNING: division by zero
CONTEXT: referenced column: f2
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (4,
null).
WARNING: division by zero
CONTEXT: referenced column: f2
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (6,
null).
INSERT 0 3
– Number of warnings
generated in MySQL
mysql> CREATE TABLE test(f1 INT,
f2 INT not null);
Query OK, 0 rows aected (0.01
sec)
mysql> INSERT INTO test
VALUES(1,0),(3,0),(5,0);
Query OK, 3 rows aected (0.00
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 582
No. MySQL Function Syntax GaussDB Implementation
Dierence
sec)
Records: 3 Duplicates: 0
Warnings: 0
mysql> INSERT IGNORE INTO test
SELECT f1+1, f1/f2 FROM test;
Query OK, 3 rows aected, 4
warnings (0.00 sec)
Records: 3 Duplicates: 0
Warnings: 4
● The dierences between
MySQL's and GaussDB's
INSERT IGNORE in triggers
are as follows:
– INSERT IGNORE used in a
GaussDB trigger
gaussdb=# CREATE TABLE test1(f1
INT NOT NULL);
CREATE TABLE
gaussdb=# CREATE TABLE test2(f1
INT);
CREATE TABLE
gaussdb=# CREATE OR REPLACE
FUNCTION trig_test() RETURNS
TRIGGER AS $$
gaussdb$# BEGIN
gaussdb$# INSERT IGNORE INTO
test1 VALUES(NULL);
gaussdb$# RETURN NEW;
gaussdb$# END;
gaussdb$# $$ LANGUAGE plpgsql;
CREATE FUNCTION
gaussdb=# CREATE TRIGGER trig2
BEFORE INSERT ON test2 FOR
EACH ROW EXECUTE PROCEDURE
trig_test();
CREATE TRIGGER
gaussdb=# INSERT INTO test2
VALUES(NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null).
CONTEXT: SQL statement "INSERT
IGNORE INTO test1
VALUES(NULL)"
PL/pgSQL function trig_test() line
3 at SQL statement
INSERT 0 1
gaussdb=# SELECT * FROM test1;
f1
----
0
(1 rows)
gaussdb=# SELECT * FROM test2;
f1
----
(1 rows)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 583
No. MySQL Function Syntax GaussDB Implementation
Dierence
– INSERT IGNORE used in a
MySQL trigger
mysql> CREATE TABLE test1(f1 INT
NOT NULL);
Query OK, 0 rows aected (0.01
sec)
mysql> CREATE TABLE test2(f1
INT);
Query OK, 0 rows aected (0.00
sec)
mysql> DELIMITER ||
mysql> CREATE TRIGGER trig2
BEFORE INSERT ON test2 FOR
EACH ROW
-> BEGIN
-> INSERT IGNORE into test1
values(NULL);
-> END||
Query OK, 0 rows aected (0.01
sec)
mysql> DELIMITER ;
mysql> INSERT INTO test2
VALUES(NULL);
ERROR 1048 (23000): Column 'f1'
cannot be null
mysql> INSERT IGNORE INTO test2
VALUES(NULL);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test1;
+----+
| f1 |
+----+
| 0 |
+----+
1 row in set (0.00 sec)
mysql> SELECT * FROM test2;
+------+
| f1 |
+------+
| NULL |
+------+
1 row in set (0.00 sec)
● The implementation
mechanism of Boolean and
serial in GaussDB is dierent
from that in MySQL.
Therefore, the default zero
value in GaussDB is dierent
from that in MySQL. For
example:
– Behavior in GaussDB
gaussdb=# CREATE TABLE test(f1
SERIAL, f2 BOOL NOT NULL);
NOTICE: CREATE TABLE will create
implicit sequence "test_f1_seq" for
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 584
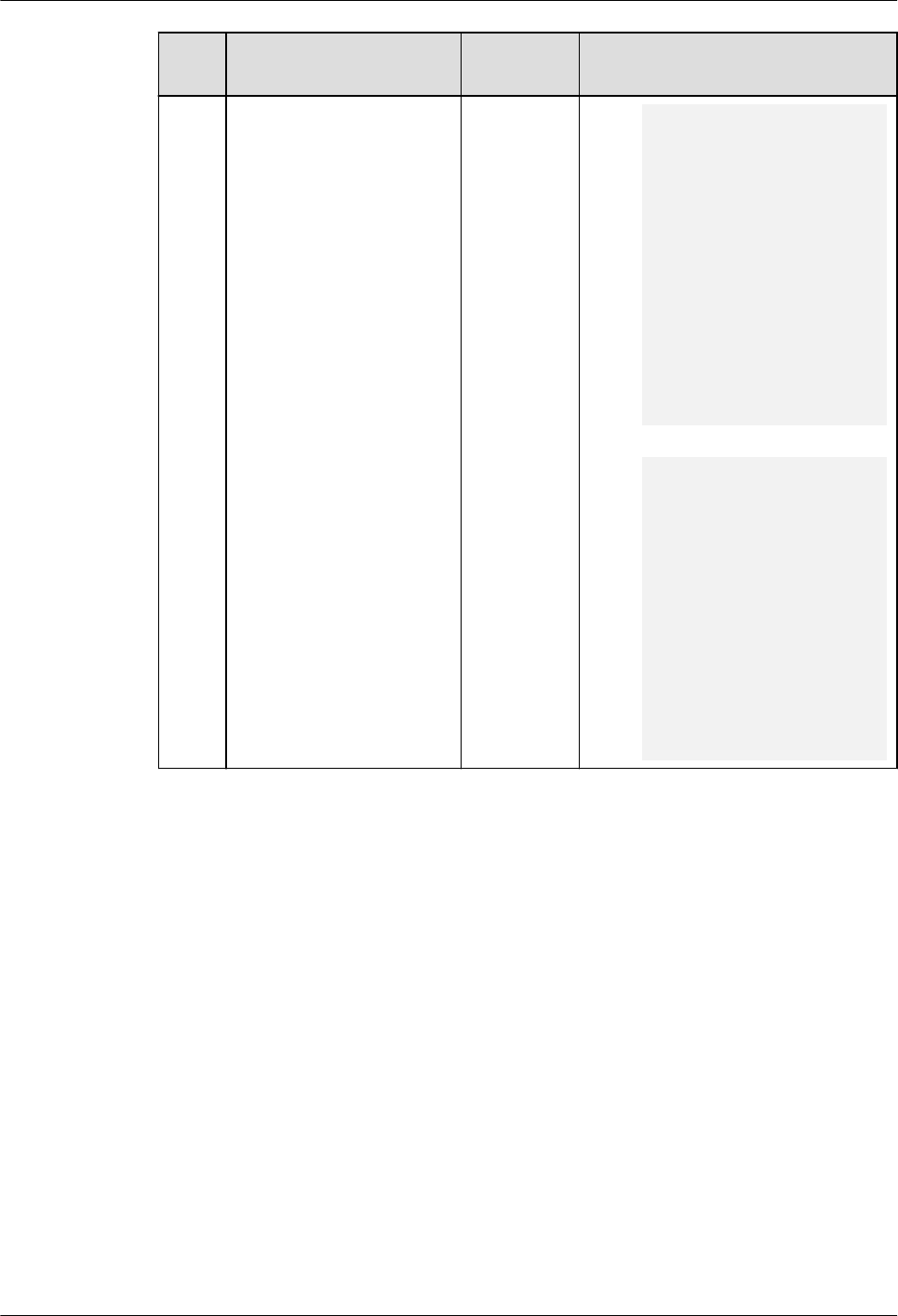
No. MySQL Function Syntax GaussDB Implementation
Dierence
serial column "test.f1"
CREATE TABLE
gaussdb=# INSERT IGNORE INTO
test values(NULL,NULL);
WARNING: null value in column
"f1" violates not-null constraint
DETAIL: Failing row contains (null,
null).
WARNING: null value in column
"f2" violates not-null constraint
DETAIL: Failing row contains (null,
null).
INSERT 0 1
gaussdb=# SELECT * FROM test;
f1 | f2
----+----
0 | f
(1 row)
– Behavior in MySQL
mysql> CREATE TABLE test(f1
SERIAL, f2 BOOL NOT NULL);
Query OK, 0 rows aected (0.00
sec)
mysql> INSERT IGNORE INTO test
values(NULL,NULL);
Query OK, 1 row aected, 1
warning (0.00 sec)
mysql> SELECT * FROM test;
+----+----+
| f1 | f2 |
+----+----+
| 1 | 0 |
+----+----+
1 row in set (0.00 sec)
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 585

8.2.2.8.3 DCL
No. Introduction Syntax Description Dierence
1 Set user-dened
variables.
SET ● Dierence in the
length of a user-
dened variable. For
example:
– There is no
restriction on the
length of MySQL
user-dened
variable names.
– The length of a
user-dened
GaussDB variable
name cannot
exceed 64 bytes. If
the length exceeds
64 bytes, the excess
part will be
truncated and an
alarm will be
generated.
2 Compatible with the
SET TRANSACTION
syntax.
SET TRANSACTION In MySQL, you can set
the transaction isolation
level and read/write
mode for the current
session and global. In
GaussDB, you need to set
the
b_format_behavior_com
pat_options parameter
to include
set_session_transaction
for the current session.
The global setting takes
eect only for the current
database.
3 Set names with
COLLATE specied.
SET [ SESSION |
LOCAL ] NAMES
{'charset_name'
[COLLATE
'collation_name'] |
DEFAULT};
GaussDB does not allow
charset_name to be
dierent from the
database character set.
For details, see "SQL
Reference > SQL Syntax >
S > SET" in
Developer
Guide
.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 586

8.2.2.9 Drivers
8.2.2.9.1 JDBC
JDBC API Reference
Obtaining Data from a Result Set
ResultSet objects provide a variety of methods to obtain data from a result set.
Table 1 lists the common methods for obtaining data. If you want to know more
about other methods, see JDK ocial documents.
Table 8-45 Common methods for obtaining data from a result set
Method Description Dierence
int getInt(int
columnIndex)
Obtains int
data by
column
index.
-
int getInt(String
columnLabel)
Obtains int
data by
column
name.
-
String
getString(int
columnIndex)
Obtains
string data
by column
index.
If the column type is integer and the column
contains the ZEROFILL attribute, GaussDB
pads 0s to meet the width required by the
ZEROFILL attribute and outputs the result.
MySQL directly outputs the result.
String
getString(String
columnLabel)
Obtains
string data
by column
name.
If the column type is integer and the column
contains the ZEROFILL attribute, GaussDB
pads 0s to meet the width required by the
ZEROFILL attribute and outputs the result.
MySQL directly outputs the result.
Date getDate(int
columnIndex)
Obtains
date data
by column
index.
-
Date
getDate(String
columnLabel)
Obtains
date data
by column
name.
-
8.2.3 MySQL Compatibility in M-Compatible Mode
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 587

8.2.3.1 MySQL Compatibility Overview
This chapter compares the M-compatible mode in GaussDB with MySQL 5.7. Only
compatibility features added later than GaussDB Kernel 505.1 are described. You
are advised to view the specications and restrictions of the features in
Developer
Guide
.
To adapt to MySQL statements and multiple connection modes such as pymysql
and JDBC, the M-compatible protocol is added to GaussDB.
GaussDB is compatible with MySQL in terms of data types, SQL functions, and
database objects.
The execution plan, optimization, and EXPLAIN result in GaussDB are dierent
from those in MySQL.
The underlying framework implementation of the GaussDB is dierent from that
of MySQL. Therefore, there are still some dierences between GaussDB and
MySQL.
NO TE
The underlying architecture of M-Compatibility is dierent from that of MySQL. Therefore,
the query performance of schemas with the same name as MySQL under
information_schema and m_schema may be dierent. For details, see chapter 6 in
M-
Compatible Developer Guide
. For example, the execution of the count function cannot be
optimized. The time consumed by the SELECT * and SELECT COUNT(*) statements is similar.
Database and Schema Design
MySQL data objects include database, table, index, view, trigger, and proc. The
mapping relationship between MySQL object layers and GaussDB is from top to
bottom and one-to-many, as shown in the following gure.
Figure 8-1 Dierences between databases and schemas in MySQL and GaussDB
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 588

● In MySQL, database and schema are synonyms. In GaussDB, a database can
have multiple schemas. In this feature, each database in MySQL is mapped to
a schema in GaussDB.
● In MySQL, an index belongs to a table. In GaussDB, an index belongs to a
schema. As a result, an index name must be unique in a schema in GaussDB
and must be unique in a table in MySQL. This dierence will be retained as a
current constraint.
8.2.3.2 Data Types
The data types of GaussDB are the same as those of MySQL in most function
scenarios, but there are some dierences.
● Unless otherwise specied, the precision, scale, and number of bits of some
data types cannot be dened as oating-point values. You are advised to use
valid integer values.
8.2.3.2.1 Numeric Data Types
Table 8-46 Integer types
No. MySQL GaussDB Dierence
1 BOOL Supported,
with
dierences
Output format: The output of SELECT
TRUE/FALSE in GaussDB is t or f, and that
in MySQL is 1 or 0.
MySQL: The BOOL/BOOLEAN type is
actually mapped to the TINYINT type.
2 BOOLEAN Supported,
with
dierences
3 TINYINT[(M
)]
[UNSIGNED
]
Supported,
with
dierences
For details, see the following note.
4 SMALLINT[(
M)]
[UNSIGNED
]
Supported,
with
dierences
For details, see the following note.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 589

No. MySQL GaussDB Dierence
5 MEDIUMIN
T[(M)]
[UNSIGNED
]
Supported,
with
dierences
MySQL requires 3 bytes to store
MEDIUMINT data.
● The signed range is –8388608 to
+8388607.
● The unsigned range is 0 to +16777215.
GaussDB is mapped to the INT type. Four
bytes are required for storage. The value
range is determined based on boundary
values.
● The signed range is –8388608 to
+8388607.
● The unsigned range is 0 to +16777215.
For other dierences, see the following
note.
6 INT[(M)]
[UNSIGNED
]
Supported,
with
dierences
For details, see the following note.
7 INTEGER[(M
)]
[UNSIGNED
]
Supported,
with
dierences
For details, see the following note.
8 BIGINT[(M)
]
[UNSIGNED
]
Supported,
with
dierences
For details, see the following note.
NO TE
Input formats:
● MySQL:
If a character string with multiple decimal points (such as "1.2.3.4.5") is entered,
MySQL will misparse the character string in loose mode, throw a warning, and insert
the character string into the table successfully. For example, after "1.2.3.4.5" is inserted
into the table, the value is 12.
● GaussDB:
If a character string with multiple decimal points (such as "1.2.3.4.5") is entered in
loose mode, the characters after the second decimal point are truncated as invalid
characters, a warning is thrown, and the character string is inserted into the table
successfully. For example, after "1.2.3.4.5" is inserted into the table, the value is 1.
After "1.6.3.4.5" is inserted into the table, the value is 2.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 590

Table 8-47 Arbitrary precision types
No. MySQL GaussDB Dierence
1 DECIMAL[(
M[,D])]
Supported,
with
dierences
MySQL decimal uses a 9 x 9 array to store
values. The integer part and decimal part
are stored separately. If the length exceeds
the value, the decimal part is truncated
rst. GaussDB truncates an integer that
contains more than 81 digits.
2 NUMERIC[(
M[,D])]
Supported,
with
dierences
3 DEC[(M[,D])
]
Supported,
with
dierences
4 FIXED[(M[,D
])]
Supported,
with
dierences
Table 8-48 Floating-point types
No.
MySQL GaussDB Dierence
1 FLOAT[(M,D
)]
Supported,
with
dierences
The FLOAT data type does not support
partitioned tables with the key partitioning
policy.
2 FLOAT(p) Supported,
with
dierences
The FLOAT data type does not support
partitioned tables with the key partitioning
policy.
3 DOUBLE[(M
,D)]
Supported,
with
dierences
The DOUBLE data type does not support
partitioned tables with the key partitioning
policy.
4 DOUBLE
PRECISION[(
M,D)]
Supported,
with
dierences
The DOUBLE PRECISION data type does not
support partitioned tables with the key
partitioning policy.
5 REAL[(M,D)
]
Supported,
with
dierences
The REAL data type does not support
partitioned tables with the key partitioning
policy.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 591

8.2.3.2.2 Date and Time Data Types
Table 8-49 Date and time data types
No. MySQL GaussDB Dierence
1 DATE Supported,
with
dierences.
GaussDB supports the date data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats:
– Separator: A backslash (\) is regarded
as an escape character in both
MySQL and GaussDB. However,
MySQL supports \0, but GaussDB
does not support \0. Therefore,
GaussDB reports an error when the
backslash is used as a separator and
the separator is followed by 0.
2 DATETIME[(f
sp)]
Supported,
with
dierences.
GaussDB supports the datetime data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats:
– Separator: A backslash (\) is regarded
as an escape character in both
MySQL and GaussDB. However,
MySQL supports \0, but GaussDB
does not support \0. Therefore,
GaussDB reports an error when the
backslash is used as a separator and
the separator is followed by 0.
3 TIMESTAMP[
(fsp)]
Supported,
with
dierences.
GaussDB supports the timestamp data
type. Compared with MySQL, GaussDB has
the following dierences in specications:
● Input formats:
– Separator: A backslash (\) is regarded
as an escape character in both
MySQL and GaussDB. However,
MySQL supports \0, but GaussDB
does not support \0. Therefore,
GaussDB reports an error when the
backslash is used as a separator and
the separator is followed by 0.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 592

No. MySQL GaussDB Dierence
4 TIME[(fsp)] Supported,
with
dierences.
GaussDB supports the time data type.
Compared with MySQL, GaussDB has the
following dierences in specications:
● Input formats:
– Separator: A backslash (\) is regarded
as an escape character in both
MySQL and GaussDB. However,
MySQL supports \0, but GaussDB
does not support \0. Therefore,
GaussDB reports an error when the
backslash is used as a separator and
the separator is followed by 0.
● When the hour, minute, second, and
nanosecond of the time type are 0, the
sign bits of GaussDB and MySQL may be
dierent.
5 YEAR[(4)] Supported. -
NO TE
● GaussDB does not support ODBC syntax literals:
{ d 'str' }
{ t 'str' }
{ ts 'str' }
● GaussDB supports standard SQL literals, and precision can be added after type
keywords, but MySQL does not support the following:
DATE[(n)] 'str'
TIME[(n)] 'str'
TIMESTAMP[(n)] 'str'
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 593

8.2.3.2.3 String Data Types
Table 8-50 String data types
No. MySQL GaussDB Dierence
1 CHAR(M) Supported,
with
dierences
● Input formats:
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
– GaussDB does not support escape
characters, but MySQL supports.
2 VARCHAR(M) Supported,
with
dierences
● Input formats:
– The length of parameters and return
values of GaussDB user-dened
functions cannot be veried. The
length of stored procedure
parameters cannot be veried.
However, MySQL supports these
functions.
– The length of temporary variables in
GaussDB user-dened functions and
stored procedures can be veried,
and an error or truncation alarm is
reported in strict or loose mode.
However, MySQL does not support
these functions.
– GaussDB does not support escape
characters, but MySQL supports.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 594

No. MySQL GaussDB Dierence
3 TINYTEXT Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the TINYTEXT
type does not support primary keys, but
GaussDB supports.
● Index: In MySQL, the TINYTEXT type
does not support other index methods
except prex indexes. GaussDB supports
these index methods.
4
TEXT Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the TEXT type
does not support primary keys, but
GaussDB supports.
● Index: In MySQL, the TEXT type does
not support other index methods except
prex indexes. GaussDB supports these
index methods.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 595

No. MySQL GaussDB Dierence
5 MEDIUMTEX
T
Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the
MEDIUMTEXT type does not support
primary keys, but GaussDB supports.
● Index: In MySQL, the MEDIUMTEXT
type does not support other index
methods except prex indexes. GaussDB
supports these index methods.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 596

No. MySQL GaussDB Dierence
6 LONGTEXT Supported,
with
dierences
● Input formats:
– GaussDB supports a maximum of 1
GB, and MySQL supports a
maximum of 4 GB minus 1 byte.
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the LONGTEXT
type does not support primary keys, but
GaussDB supports.
● Index: In MySQL, the LONGTEXT type
does not support other index methods
except prex indexes. GaussDB supports
these index methods.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 597

8.2.3.2.4 Binary Data Types
Table 8-51 Binary data types
No. MySQL GaussDB Dierence
1 BINARY[(M)] Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
– If the length of the inserted string is
less than the target length, the
padding character is 0x20 in
GaussDB and 0x00 in MySQL.
● Character set: The default character set
is the initialized character set of the
database. For MySQL, the default
character set is BINARY.
● Output formats:
– When the JDBC protocol is used, a
space at the end of the BINARY type
is displayed as a space, and that in
MySQL is displayed as \x00.
– In loose mode, if characters (such as
Chinese characters) of the BINARY
type exceed
n
bytes, the excess
characters will be truncated. MySQL
retains the rst
n
bytes. However,
garbled characters are displayed in
the output.
NOTE
Due to the dierences between GaussDB
and MySQL in BINARY llers and \0j
truncation, GaussDB and MySQL have
dierent performance in scenarios such as
operator comparison calculation, character
string-related system function calculation,
index matching, and data import and export.
For details about the dierence scenarios,
see the examples in this section.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 598

No. MySQL GaussDB Dierence
2 VARBINARY(
M)
Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Character set: The default character set
is the initialized character set of the
database. For MySQL, the default
character set is BINARY.
● Output format: When the JDBC protocol
is used, a space at the end of the
BINARY type is displayed as a space,
and that in MySQL is displayed as \x00.
3 TINYBLOB Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the TINYBLOB
type does not support primary keys, but
GaussDB supports.
● Index: In MySQL, the TINYBLOB type
does not support other index methods
except prex indexes. GaussDB supports
these index methods.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 599

No. MySQL GaussDB Dierence
4 BLOB Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the BLOB type
does not support primary keys, but
GaussDB supports.
● Index: In MySQL, the BLOB type does
not support other index methods except
prex indexes. GaussDB supports these
index methods.
5
MEDIUMBLO
B
Supported,
with
dierences
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the
MEDIUMBLOB type does not support
primary keys, but GaussDB supports.
● Index: In MySQL, the MEDIUMBLOB
type does not support other index
methods except prex indexes. GaussDB
supports these index methods.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 600

No. MySQL GaussDB Dierence
6 LONGBLOB Supported,
with
dierences
● Value range: a maximum of 1 GB.
MySQL supports a maximum of 4 GB
minus 1 byte.
● Input formats:
– GaussDB does not support escape
characters, but MySQL supports.
– Default value: When creating a table
column, you can set a default value
in the syntax. MySQL does not allow
you to set a default value.
– After a binary or hexadecimal
character string is entered, GaussDB
outputs a hexadecimal character
string, and MySQL escapes the
character string based on the ASCII
code table. If the character string
cannot be escaped, the output is
empty.
● Primary key: In MySQL, the LONGBLOB
type does not support primary keys, but
GaussDB supports.
● Index: In MySQL, the LONGBLOB type
does not support other index methods
except prex indexes. GaussDB supports
these index methods.
7
BIT[(M)] Supported,
with
dierences
● Output format: All outputs are output
as binary character strings. MySQL
escapes the character string based on
the ASCII code table. If the character
string cannot be escaped, the output is
empty.
Example:
-- GaussDB
m_db=# create table test(a binary(10));
CREATE TABLE
m_db=# insert into test values(0x8000);
INSERT 0 1
m_db=# select hex(a) from test;
hex
----------------------
80202020202020202020
(1 row)
m_db=# select * from test where hex(a) = 80000000000000000000;
a
---
(0 rows)
m_db=# CREATE TABLE test2(a binary(10));
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 601

CREATE TABLE
m_db=# INSERT INTO test2 VALUES(0x80008000);
INSERT 0 1
m_db=# SELECT hex(a) FROM test2;
hex
----------------------
80202020202020202020
(1 row)
-- MySQL
mysql> create table test(a binary(10));
Query OK, 0 rows aected (0.01 sec)
mysql> insert into test values(0x8000);
Query OK, 1 row aected (0.00 sec)
mysql> select hex(a) from test;
+----------------------+
| hex(a) |
+----------------------+
| 80000000000000000000 |
+----------------------+
1 row in set (0.00 sec)
mysql> select * from test where hex(a) = 80000000000000000000;
+------------+
| a |
+------------+
| ▒ |
+------------+
1 row in set (0.00 sec)
mysql> CREATE TABLE test2(a binary(10));
Query OK, 0 rows aected (0.00 sec)
mysql> INSERT INTO test2 VALUES(0x80008000);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT hex(a) FROM test2;
+----------------------+
| hex(a) |
+----------------------+
| 80008000000000000000 |
+----------------------+
1 row in set (0.00 sec)
8.2.3.2.5 Attributes Supported by Data Types
Table 8-52 Attributes supported by data types
No.
MySQL GaussDB
1 NULL Supported.
2 NOT NULL Supported.
3 DEFAULT Supported.
4 ON UPDATE Supported.
4 PRIMARY KEY Supported.
5 AUTO_INCREMENT Supported.
6 CHARACTER SET name Supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 602

No. MySQL GaussDB
7 COLLATE name Supported.
8.2.3.2.6 Data Type Conversion
Conversion between dierent data types is supported. Data type conversion is
involved in the following scenarios:
● The data types of operands of operators (such as comparison and arithmetic
operators) are inconsistent. It is commonly used for comparison operations in
query conditions or join conditions.
● The data types of arguments and parameters are inconsistent when a
function is called.
● The data types of target columns to be updated by DML statements
(including INSERT, UPDATE, MERGE, and REPLACE) and the dened column
types are inconsistent.
● Explicit type conversion: CAST(expr AS datatype), which converts an
expression to a data type.
● After the target data type of the nal projection column is determined by set
operations (UNION, MINUS, EXCEPT, and INTERSECT), the type of the
projection column in each SELECT statement is inconsistent with the target
data type.
● In other expression calculation scenarios, the target data type used for
comparison or nal result is determined based on the data type of dierent
expressions.
There are three types of data type conversion dierences: implicit conversion,
explicit conversion, and UINON/CASE.
Dierences in double colon conversion:
● In GaussDB, if you use double colons to convert input parameters of a
function to another type, the result may be unexpected. In MySQL, double
colons do not take eect.
Example:
m_db=# SELECT POW("12"::VARBINARY,"12"::VARBINARY);
ERROR: value out of range: overow
CONTEXT: referenced column: pow
varbinary col
m_db=# CREATE TABLE test_varbinary (
A VARBINARY(10)
);
m_db=# INSERT INTO test_varbinary VALUES ('12');
m_db=# SELECT POW(A, A) FROM test_varbinary;
pow
---------------
8916100448256
(1 row)
Dierences in implicit type conversion:
● In GaussDB, the conversion rules from small types to small types are used. In
MySQL, the conversion rules from small types to large types and from large
types to small types are used.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 603

● Due to data type dierences, some output formats of implicit conversion in
GaussDB are inconsistent.
● During implicit conversion from the BIT data type to the character data type
and binary data type in GaussDB, some output behaviors are inconsistent.
GaussDB outputs a hexadecimal character string, and MySQL escapes the
character string based on the ASCII code table. If the character string cannot
be escaped, the output is empty.
Example:
m_db=# CREATE TABLE bit_storage (
VS_COL1 BIT(4),
VS_COL2 BIT(4),
VS_COL3 BIT(4),
VS_COL4 BIT(4),
VS_COL5 BIT(4),
VS_COL6 BIT(4),
VS_COL7 BIT(4),
VS_COL8 BIT(4)
);
m_db=# CREATE TABLE string_storage (
VS_COL1 BLOB,
VS_COL2 TINYBLOB,
VS_COL3 MEDIUMBLOB,
VS_COL4 LONGBLOB,
VS_COL5 TEXT,
VS_COL6 TINYTEXT,
VS_COL7 MEDIUMTEXT,
VS_COL8 LONGTEXT
);
m_db=# INSERT INTO bit_storage VALUES(B'101', B'101', B'101', B'101', B'101', B'101', B'101', B'101');
m_db=# INSERT INTO string_storage SELECT * FROM bit_storage;
m_db=# SELECT * FROM string_storage;
VS_COL1 | VS_COL2 | VS_COL3 | VS_COL4 | VS_COL5 | VS_COL6 | VS_COL7 | VS_COL8
---------+---------+---------+---------+---------+---------+---------+---------
\x05 | \x05 | \x05 | \x05 | \x05 | \x05 | \x05 | \x05
(1 row)
m_db=# DROP TABLE bit_storage, string_storage;
mysql> CREATE TABLE bit_storage (
VS_COL1 BIT(4),
VS_COL2 BIT(4),
VS_COL3 BIT(4),
VS_COL4 BIT(4),
VS_COL5 BIT(4),
VS_COL6 BIT(4),
VS_COL7 BIT(4),
VS_COL8 BIT(4)
);
mysql> CREATE TABLE bit_storage (
VS_COL1 BIT(4),
VS_COL2 BIT(4),
VS_COL3 BIT(4),
VS_COL4 BIT(4),
VS_COL5 BIT(4),
VS_COL6 BIT(4),
VS_COL7 BIT(4),
VS_COL8 BIT(4)
);
mysql> INSERT INTO bit_storage VALUES(B'101', B'101', B'101', B'101', B'101', B'101', B'101', B'101');
mysql> INSERT INTO string_storage SELECT * FROM bit_storage;
mysql> SELECT * FROM string_storage;
+---------+---------+---------+---------+---------+---------+---------+---------+
| VS_COL1 | VS_COL2 | VS_COL3 | VS_COL4 | VS_COL5 | VS_COL6 | VS_COL7 | VS_COL8 |
+---------+---------+---------+---------+---------+---------+---------+---------+
| | | | | | | | |
+---------+---------+---------+---------+---------+---------+---------+---------+
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 604

1 row in set (0.00 sec)
mysql> DROP TABLE bit_storage, string_storage;
● When a binary or hexadecimal character string with 0x00 is inserted into the
binary data type, GaussDB inserts part of the string and truncates the
characters following 0x00. MySQL can insert the entire string.
Example:
m_db=# CREATE TABLE blob_storage (
A BLOB
);
m_db=# INSERT INTO blob_storage VALUES (0xBB00BB);
m_db=# SELECT hex(A) FROM blob_storage;
hex
-----
BB
(1 row)
m_db=# DROP TABLE blob_storage;
mysql> CREATE TABLE blob_storage (
A TEXT
);
mysql> INSERT INTO blob_storage VALUES (0xBB00BB);
mysql> SELECT hex(A) FROM blob_storage;
+--------+
| hex(a) |
+--------+
| BB00BB |
+--------+
1 row in set (0.01 sec)
mysql> DROP TABLE blob_storage;
● When a binary or hexadecimal string with 0x00 in the middle is inserted into
the string data type, GaussDB inserts part of the string and truncates the
characters following 0x00. In MySQL, the string cannot be inserted in strict
mode, and an empty string is inserted in loose mode.
Example:
m_db=# CREATE TABLE text_storage (
A TEXT
);
m_db=# INSERT INTO text_storage VALUES (b'101110110000000010111011');
m_db=# SELECT hex(A) FROM text_storage;
hex
-----
BB
(1 row)
m_db=# DROP TABLE text_storage;
mysql> CREATE TABLE text_storage (
A TEXT
);
mysql> INSERT INTO text_storage VALUES (b'101110110000000010111011');
ERROR 1366 (HY000): Incorrect string value: '\xBB\x00\xBB' for column 'A' at row 1
mysql> SELECT hex(A) FROM text_storage;
Empty set (0.00 sec)
mysql> SET SQL_MODE='';
mysql> INSERT INTO text_storage VALUES (b'101110110000000010111011');
mysql> SELECT hex(A) FROM text_storage;
+--------+
| hex(A) |
+--------+
| |
+--------+
1 row in set (0.01 sec)
mysql> DROP TABLE text_storage;
● The WHERE clause contains only common character strings. GaussDB returns
TRUE for 't', 'true', 'yes', 'y', and 'on', returns FALSE for 'no', 'f', 'o', 'false',
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 605

and 'n', and reports an error for other character strings. MySQL determines
whether to return TRUE or FALSE by converting a character string to an INT1
value.
Example:
m_db=# CREATE TABLE test_where (
A INT
);
m_db=# INSERT INTO test_where VALUES (1);
m_db=# SELECT * FROM test_where WHERE '111';
ERROR: invalid input syntax for type boolean: "111"
LINE 1: select * from test_where where '111';
m_db=# DROP TABLE test_where;
mysql> CREATE TABLE test_where (
A INT
);
mysql> INSERT INTO test_where VALUES (1);
mysql> SELECT * FROM test_where WHERE '111';
+------+
| a |
+------+
| 1 |
+------+
1 row in set (0.01 sec)
mysql> DROP TABLE test_where;
● When converting strings of the YEAR type to integers, MySQL uses scientic
notation, but GaussDB does not support scientic notation and truncates the
strings.
Example:
m_db=# CREATE TABLE test_year (
A YEAR
);
m_db=# INSERT INTO test_year VALUES ('2E3x');
WARNING: Data truncated for column.
LINE 1: insert into t1 values ('2E3x');
^
CONTEXT: referenced column: a
m_db=# SELECT * FROM test_year ORDER BY A;
a
------
2002
(1 row)
m_db=# DROP TABLE test_year;
mysql> CREATE TABLE test_year (
A YEAR
);
mysql> INSERT INTO test_year VALUES ('2E3x');
mysql> SELECT * FROM test_year ORDER BY A;
+------+
| a |
+------+
| 2000 |
+------+
1 row in set (0.01 sec)
mysql> DROP TABLE test_year;
Dierences in explicit type conversion:
In GaussDB, the conversion rules for each target type are used. In MySQL, C++
polymorphic overloading functions are used, causing inconsistent behavior in
nesting scenarios.
Example:
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 606

m_db=# SELECT CAST(GREATEST(date'2023-01-01','2023-01-01') AS SIGNED);
WARNING: Truncated incorrect INTEGER value: '2023-01-01'
CONTEXT: referenced column: cast
cast
------
2023
(1 row)
mysql> SELECT CAST(GREATEST(date'2023-01-01','2023-01-01') AS SIGNED);
+---------------------------------------------------------+
| CAST(GREATEST(date'2023-01-01','2023-01-01') AS SIGNED) |
+---------------------------------------------------------+
| 20230101 |
+---------------------------------------------------------+
Dierences between UNION, CASE, and related structures:
● In MySQL, POLYGON+NULL, POINT+NULL, and POLYGON+POINT return the
GEOMETRY type. They are not involved in GaussDB and considered as errors.
● The SET and ENUM types are not supported currently and are considered as
errors.
● When the constant type is aggregated with other types, the precision of the
output type is the precision of other types. For example, the precision of the
result of "select "helloworld" union select p from t;" is the precision of
attribute p.
● When xed-point constants and types without precision constraints (non-
string types such as int, bool, and year, and the type of the aggregation result
is the xed-point type) are aggregated, the precision constraint is output
based on the default precision 31 of xed-point numbers.
● Dierences in merge rules:
In MySQL 5.7, if YEAR is aggregated with TINYINT, INT, MEDIUMINT, BIGINT,
or BOOL, the result is of the type with UNSIGNED. In GaussDB, it is of the
type without UNSIGNED. In MySQL, if BIT is aggregated with a numeric type
such as INT, NUMERIC, FLOAT, or DOUBLE, the result type is VARBINARY. In
GaussDB, the result type is NUMERIC for aggregation between BIT and INT or
NUMERIC, DOUBLE for aggregation between BIT and FLOAT or DOUBLE, and
UINT8 for aggregation between BIT and unsigned integers.
● In MySQL, BINARY and CHAR use dierent padding characters. BINARY is
padded with '\0', and CHAR is padded with spaces. In GaussDB, BINARY and
CHAR are padded with spaces.
8.2.3.3 System Functions
GaussDB is compatible with most MySQL system functions, but there are some
dierences. Only system functions in M-compatible mode can be used. System
functions of the original GaussDB cannot be used in case of unexpected results.
Currently, some system functions in GaussDB with the same names as those in
MySQL are not supported in M-compatible mode. For some of them, the message
indicating that they are not supported in M-compatible mode is displayed. Other
functions still retain the behaviors of the original GaussDB system functions. Do
not use these functions in case of unexpected results. The following table lists the
functions with the same name.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 607
Table 8-53 Same-name functions for which a message indicating that they are
not supported in M-compatible mode is displayed
cot isEmpty json_append json_array json_array_ap
pend
json_array_ins
ert
json_contains json_contains
_path
json_depth json_extract
json_insert json_keys json_length json_merge json_merge_p
atch
json_merge_p
reserve
json_object json_quote json_remove json_valid
json_replace json_search json_set json_type json_unquote
last_insert_id md5 mod octet_length overlaps
point radians stddev_pop stddev_samp var_pop
var_samp variance lag lead -
Table 8-54 Same-name functions that retain the behaviors of the original
GaussDB system functions in M-compatible mode
ceil
decode encode format instr
position round stddev regexp_instr regexp_like
regexp_replac
e
regexp_substr row_num - -
NO TE
In M-compatible mode, system functions have the following common dierences:
1. The return value type of a system function is the same as that of MySQL only when the
node type of the input parameter is Var (table data) or Const (constant input). In other
cases (for example, the input parameter is a calculation expression or function
expression), the return value type may be dierent from that of MySQL.
2. When an aggregate function uses an expression such as another function, operator, or
SELECT clause as the input parameter (for example, SELECT sum(abs(n)) FROM t;),
the aggregate function cannot obtain the precision transferred by the input parameter
expression. As a result, the precision of the function result is dierent from that of
MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 608

8.2.3.3.1 Flow Control Functions
Table 8-55 Flow control functions
No. MySQL GaussDB Dierence
1 IF() Supported
.
If the rst parameter is TRUE and
the third parameter expression
contains an implicit type conversion
error, or if the rst parameter is
FALSE and the second parameter
expression contains an implicit type
conversion error, MySQL ignores the
error while GaussDB displays a type
conversion error.
2 IFNULL() Supported
.
If the rst parameter is not NULL
and the expression of the second
parameter contains an implicit type
conversion error, MySQL ignores the
error while GaussDB displays a type
conversion error.
3 NULLIF() Supported
, with
dierence
s.
The return value type of a function
diers in MySQL 5.7 and MySQL 8.0.
Return types are compatible with
MySQL 8.0 because it is more
appropriate.
8.2.3.3.2 Date and Time Functions
NO TE
The following describes the date and time function in M-compatible GaussDB:
● The conditions where an input parameter of a function in "Functions and Operators" in
M-compatible Developer Guide
can be a time expression are described as follows:
Time expressions (mainly including TEXT, DATETIME, DATE, and TIME) and types that
can be implicitly converted to time expressions can be used as input parameters. For
example, a number can be implicitly converted to text and then used as a time
expression.
However, the eectiveness of such condition depends on the function. For example, the
DATEDIFF function is used to calculate only the date dierence. Therefore, the time
expression is parsed as date. The TIMESTAMPDIFF function is used to calculate the time
dierence based on UNIT. Therefore, the time expression is parsed as DATE, TIME, or
DATETIME based on UNIT.
● If an input parameter of a function is an invalid date:
Generally, the supported DATE and DATETIME ranges are the same as those in MySQL.
The value of DATE ranges from '0000-01-01' to '9999-12-31', and the value of
DATETIME ranges from '0000-01-01 00:00:00' to '9999-12-31 23:59:59'. Although the
DATE and DATETIME ranges supported by GaussDB are greater than those supported by
MySQL, out-of-bounds dates are still invalid.
Most time functions generate alarms and return NULL. Only dates that can be normally
converted by CAST are normal and reasonable dates.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 609

In the new framework, most date and time functions in GaussDB are the same as
those in MySQL. The following table lists the dierences between some functions.
Table 8-56 Date and time functions
N
o.
MySQL GaussD
B
Dierence
1 ADDDATE() Support
ed
-
2 ADDTIME() Support
ed
-
3 CONVERT_TZ() Support
ed
-
4 CURDATE() Support
ed
-
5 CURRENT_DATE()/
CURRENT_DATE
Support
ed
-
6 CURRENT_TIME()/
CURRENT_TIME
Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte, for
example, SELECT
CURRENT_TIME(257) == SELECT
CURRENT_TIME(1).
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
7 CURRENT_TIMESTAMP(
)/
CURRENT_TIMESTAMP
Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte, for
example, SELECT
CURRENT_TIMESTAMP(257) ==
SELECT CURRENT_TIMESTAMP(1).
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
8 CURTIME() Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte, for
example, SELECT CURTIME(257) ==
SELECT CURTIME(1).
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
9 DATE() Support
ed
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 610

N
o.
MySQL GaussD
B
Dierence
10 DATE_ADD() Support
ed
-
11 DATE_FORMAT() Support
ed
-
12 DATE_SUB() Support
ed
-
13 DATEDIFF() Support
ed
-
14 DAY() Support
ed
-
15 DAYNAME() Support
ed
-
16 DAYOFMONTH() Support
ed
-
17 DAYOFWEEK() Support
ed
-
18 DAYOFYEAR() Support
ed
-
19 EXTRACT() Support
ed
-
20 FROM_DAYS() Support
ed
-
21 FROM_UNIXTIME() Support
ed
-
22 GET_FORMAT() Support
ed
-
23 HOUR() Support
ed
-
24 LAST_DAY() Support
ed
-
25 LOCALTIME()/
LOCALTIME
Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte, for
example, SELECT LOCALTIME(257) ==
SELECT LOCALTIME(1).
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 611

N
o.
MySQL GaussD
B
Dierence
26 LOCALTIMESTAMP/
LOCALTIMESTAMP()
Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte, for
example, SELECT
LOCALTIMESTAMP(257) == SELECT
LOCALTIMESTAMP(1).
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
27 MAKEDATE() Support
ed
-
28 MAKETIME() Support
ed
-
29 MICROSECOND() Support
ed
-
30 MINUTE() Support
ed
-
31 MONTH() Support
ed
-
32 MONTHNAME() Support
ed
-
33 NOW() Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte, for
example, SELECT
NOW(257)==SELECT NOW(1).
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 612

N
o.
MySQL GaussD
B
Dierence
34 PERIOD_ADD() Support
ed, with
dieren
ces.
1. Behaviors of integer overow
processing.
In MySQL 5.7, the maximum value
of an input parameter result of this
function is 2^32=4294967296.
When the accumulated value of the
month corresponding to period and
the month_number in the input
parameter or result exceed the
uint32 range, integer wraparound
occurs. This issue has been resolved
in MySQL 8.0. An error is reported
when the month is beyond the
range. The performance of this
function in GaussDB is the same as
that in MySQL 8.0.
2. Signs of negative period.
In MySQL 5.7, a negative year is
parsed as an abnormal value
instead of an error. An error is
reported when a GaussDB input
parameter or result is negative (for
example, January 100 minus 10000
months). This issue has been
resolved in MySQL 8.0. An error is
reported when the month is beyond
the range. The performance of this
function in GaussDB is the same as
that in MySQL 8.0.
3. Signs that the month in period
exceeds the range.
In MySQL 5.7, if the month is
greater than 12 or equal to 0, for
example, 200013 or 199900, it will
be postponed correspondingly to a
later year or the 0th month will be
processed as December of the
previous year. This issue has been
resolved in MySQL 8.0. An error is
reported when the month is beyond
the range. The performance of this
function in GaussDB is the same as
that in MySQL 8.0.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 613

N
o.
MySQL GaussD
B
Dierence
35 PERIOD_DIFF() Support
ed, with
dieren
ces.
1. Behaviors of integer overow
processing.
In MySQL 5.7, the maximum value
of an input parameter result of this
function is 2^32=4294967296.
When the accumulated value of the
month corresponding to period and
the month_number in the input
parameter or result exceed the
uint32 range, integer wraparound
occurs. This issue has been resolved
in MySQL 8.0. An error is reported
when the month is beyond the
range. The performance of this
function in GaussDB is the same as
that in MySQL 8.0.
2. Signs of negative period.
In MySQL 5.7, a negative year is
parsed as an abnormal value
instead of an error. An error is
reported when a GaussDB input
parameter or result is negative (for
example, January 100 minus 10000
months). This issue has been
resolved in MySQL 8.0. An error is
reported when the month is beyond
the range. The performance of this
function in GaussDB is the same as
that in MySQL 8.0.
3. Signs that the month in period
exceeds the range.
In MySQL 5.7, if the month is
greater than 12 or equal to 0, for
example, 200013 or 199900, it will
be postponed correspondingly to a
later year or the 0th month will be
processed as December of the
previous year. This issue has been
resolved in MySQL 8.0. An error is
reported when the month is beyond
the range. The performance of this
function in GaussDB is the same as
that in MySQL 8.0.
36
QUARTER() Support
ed
-
37 SEC_TO_TIME() Support
ed
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 614

N
o.
MySQL GaussD
B
Dierence
38 SECOND() Support
ed
-
39 STR_TO_DATE() Support
ed
Return value dierence: In GaussDB,
text is returned. In MySQL, datetime or
date is returned.
40 SUBDATE() Support
ed
-
41 SUBTIME() Support
ed
-
42 SYSDATE() Support
ed, with
dieren
ces.
The integer value of the MySQL input
parameter is wrapped when reaching
the maximum value 255 in one byte.
GaussDB does not support
wraparound.
43 TIME() Support
ed
-
44 TIME_FORMAT() Support
ed
-
45 TIME_TO_SEC() Support
ed
-
46 TIMEDIFF() Support
ed
-
47 TIMESTAMP() Support
ed
-
48 TIMESTAMPADD() Support
ed
-
49 TIMESTAMPDIFF() Support
ed
-
50 TO_DAYS() Support
ed
-
51 TO_SECONDS() Support
ed
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 615
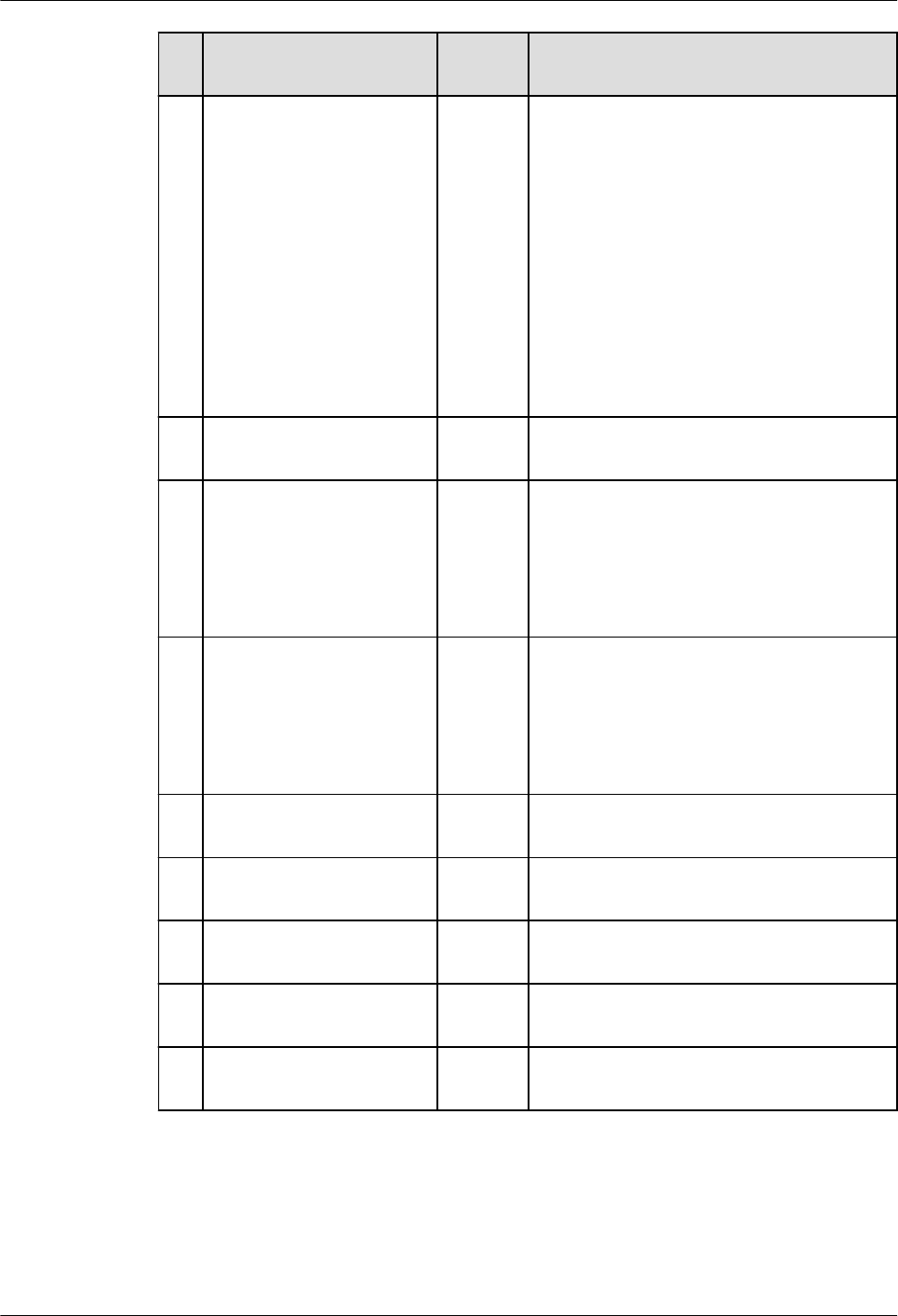
N
o.
MySQL GaussD
B
Dierence
52 UNIX_TIMESTAMP() Support
ed
MySQL determines whether to return
a xed-point value or an integer based
on whether an input parameter
contains decimal places. When
operators or functions are nested in
the input parameter, GaussDB may
return a value of the type dierent
from that in MySQL. If the inner node
returns a value of the xed-point,
oating-point, sting, or time type
(excluding the DATE type), MySQL
may return an integer, and GaussDB
returns a xed-point value.
53 UTC_DATE() Support
ed
-
54 UTC_TIME() Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte.
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
55 UTC_TIMESTAMP() Support
ed, with
dieren
ces.
The integer value of a MySQL input
parameter is wrapped based on the
maximum value 255 of one byte.
GaussDB supports only valid values
ranging from 0 to 6. For other values,
an error is reported.
56 WEEK() Support
ed
-
57 WEEKDAY() Support
ed
-
58 WEEKOFYEAR() Support
ed
-
59 YEAR() Support
ed
-
60 YEARWEEK() Support
ed
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 616

8.2.3.3.3 String Functions
Table 8-57 String functions
N
o.
MySQL GaussDB Dierence
1 ASCII() Supported -
2 BIT_LENGTH() Supported -
3 CHAR_LENGTH(
)
Supported,
with
dierences.
In GaussDB, if the character set is
SQL_ASCII, CHAR_LENGTH() returns the
number of bytes instead of characters.
4 CHARACTER_LE
NGTH()
Supported,
with
dierences.
In GaussDB, if the character set is
SQL_ASCII, CHARACTER_LENGTH()
returns the number of bytes instead of
characters.
5 CONCAT() Supported If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return value
type in GaussDB is LONGBLOB. If the
return value type in MySQL is non-binary
string (such as CHAR, VARCHAR, or
TEXT), the return value type in GaussDB
is TEXT.
6 CONCAT_WS() Supported If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return value
type in GaussDB is LONGBLOB. If the
return value type in MySQL is non-binary
string (such as CHAR, VARCHAR, or
TEXT), the return value type in GaussDB
is TEXT.
7 HEX() Supported -
8 LENGTH() Supported -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 617

N
o.
MySQL GaussDB Dierence
9 LPAD() Supported,
with
dierences.
● The default maximum padding length
in MySQL is 1398101, and that in
GaussDB is 1048576. The maximum
padding length depends on the
character set. For example, if the
character set is GBK, the default
maximum padding length in GaussDB
is 2097152.
● If the database character set is
SQL_ASCII, unexpected results may
occur.
● If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return
value type in GaussDB is LONGBLOB.
If the return value type in MySQL is
non-binary string (such as CHAR,
VARCHAR, or TEXT), the return value
type in GaussDB is TEXT.
10 REPEAT() Supported If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return value
type in GaussDB is LONGBLOB. If the
return value type in MySQL is non-binary
string (such as CHAR, VARCHAR, or
TEXT), the return value type in GaussDB
is TEXT.
11 REPLACE() Supported If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return value
type in GaussDB is LONGBLOB. If the
return value type in MySQL is non-binary
string (such as CHAR, VARCHAR, or
TEXT), the return value type in GaussDB
is TEXT.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 618

N
o.
MySQL GaussDB Dierence
12 RPAD() Supported,
with
dierences.
● The default maximum padding length
in MySQL is 1398101, and that in
GaussDB is 1048576. The maximum
padding length depends on the
character set. For example, if the
character set is GBK, the default
maximum padding length in GaussDB
is 2097152.
● If the database character set is
SQL_ASCII, unexpected results may
occur.
● If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return
value type in GaussDB is LONGBLOB.
If the return value type in MySQL is
non-binary string (such as CHAR,
VARCHAR, or TEXT), the return value
type in GaussDB is TEXT.
13 SPACE() Supported -
14 STRCMP() Supported,
with
dierences.
If the database character set is
SQL_ASCII, unexpected results may occur.
15 FIND_IN_SET() Supported,
with
dierences.
When characters are specied to be
encoded in SQL_ASCII for the database,
the server parses byte values 0 to 127
according to the ASCII standard, and
byte values 128 to 255 cannot be parsed.
If the input and output of the function
contain any non-ASCII characters, the
database cannot help you convert or
verify them.
If the return value type in MySQL is
binary string (such as BINARY,
VARBINARY, or BLOB), the return value
type in GaussDB is LONGBLOB. If the
return value type in MySQL is non-binary
string (such as CHAR, VARCHAR, or
TEXT), the return value type in GaussDB
is TEXT.
16 LCASE()
17 LEFT()
18 LOWER()
19 LTRIM()
20 REVERSE()
21 RIGHT()
22 RTRIM()
23 SUBSTR()
24 SUBSTRING()
25 SUBSTRING_IN
DEX()
26 TRIM()
27 UCASE()
28 UPPER()
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 619

N
o.
MySQL GaussDB Dierence
29 UNHEX() Supported The return value type in MySQL is
BINARY, VARBINARY, BLOB,
MEDIUMBLOB, or LONGBLOB, while the
return value type in GaussDB is xed to
LONGBLOB.
8.2.3.3.4 Forced Conversion Functions
Table 8-58 Forced conversion functions
No. MySQL GaussDB Dierence
1 CAST() Supported ● In GaussDB, CAST(expr AS CHAR[(N)]
charset_info or CAST(expr AS
NCHAR[(N)]) cannot be used to
convert character sets.
● In GaussDB, CAST(expr AS JSON)
cannot be used to convert expressions
to JSON.
● In GaussDB, you can use CAST(expr
AS FLOAT[(p)]) or CAST(expr AS
DOUBLE) to convert an expression to
the one of the oating-point type.
MySQL 5.7 does not support this
conversion.
2 CONVERT() Supported ● In GaussDB, CONVERT(expr,
CHAR[(N)] charset_info or CAST(expr,
NCHAR[(N)]) cannot be used to
convert character sets.
● In GaussDB, CAST(expr, JSON) cannot
be used to convert expressions to
JSON.
● In GaussDB, you can use
CONVERET(expr, FLOAT[(p)]) or
CONVERT(expr, DOUBLE) to convert
an expression to the one of the
oating-point type. MySQL 5.7 does
not support this conversion.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 620
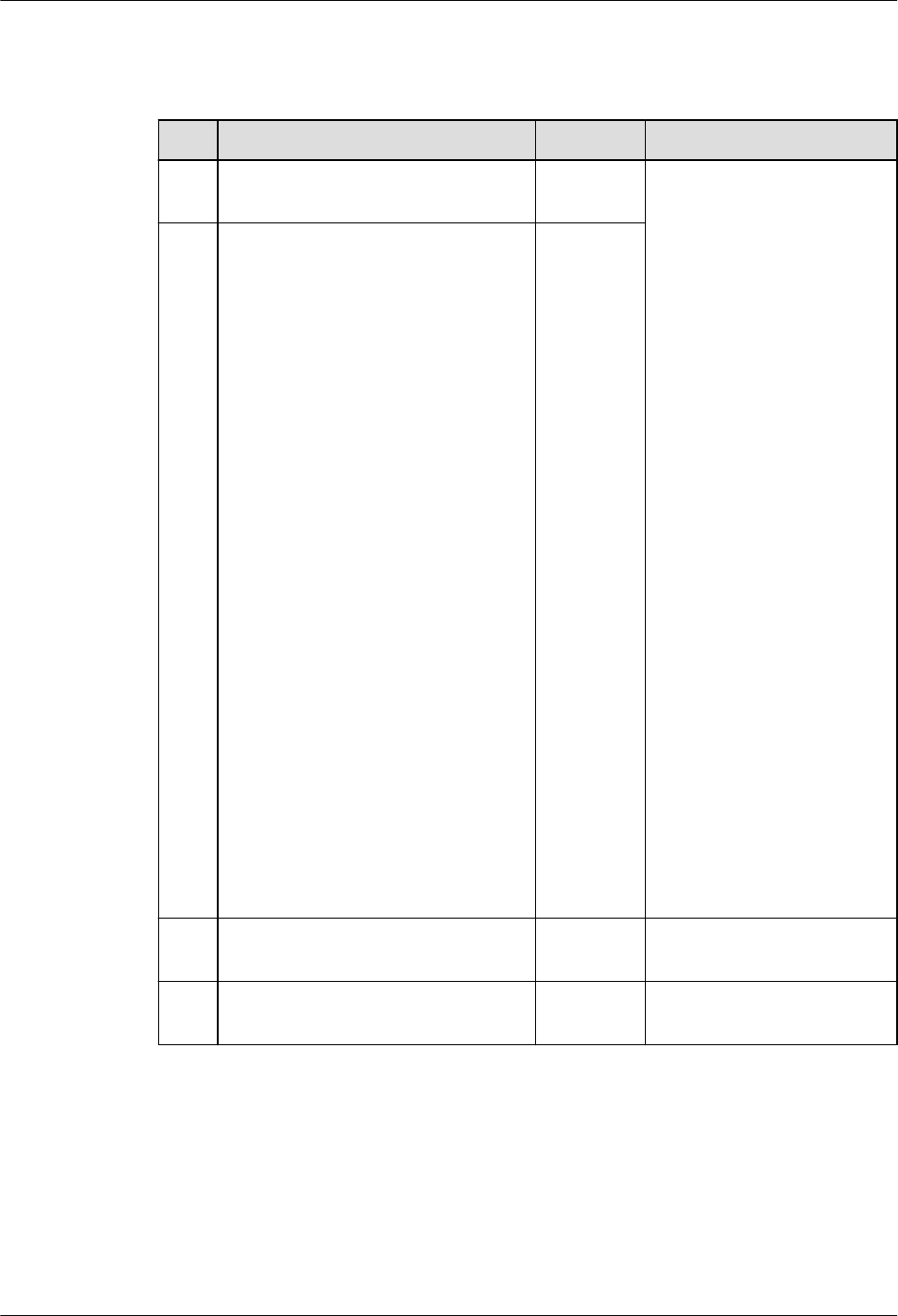
8.2.3.3.5 Encryption Functions
Table 8-59 Encryption functions
No. MySQL GaussDB Dierence
1 AES_DECRYPT() Supporte
d
1. GaussDB does not
support ECB mode,
which is an insecure
encryption mode, but
uses CBC mode by
default.
2. When characters are
specied to be
encoded in SQL_ASCII
for GaussDB, the
server parses byte
values 0 to 127
according to the ASCII
standard, and byte
values 128 to 255
cannot be parsed. If
the input and output
of the function contain
any non-ASCII
characters, the
database cannot help
you convert or verify
them.
3. The return value type
in MySQL is BINARY,
VARBINARY, BLOB,
MEDIUMBLOB, or
LONGBLOB, while the
return value type in
GaussDB is xed to
LONGBLOB.
2
AES_ENCRYPT() Supporte
d
3 SHA()/SHA1() Supporte
d
-
4 SHA2() Supporte
d
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 621
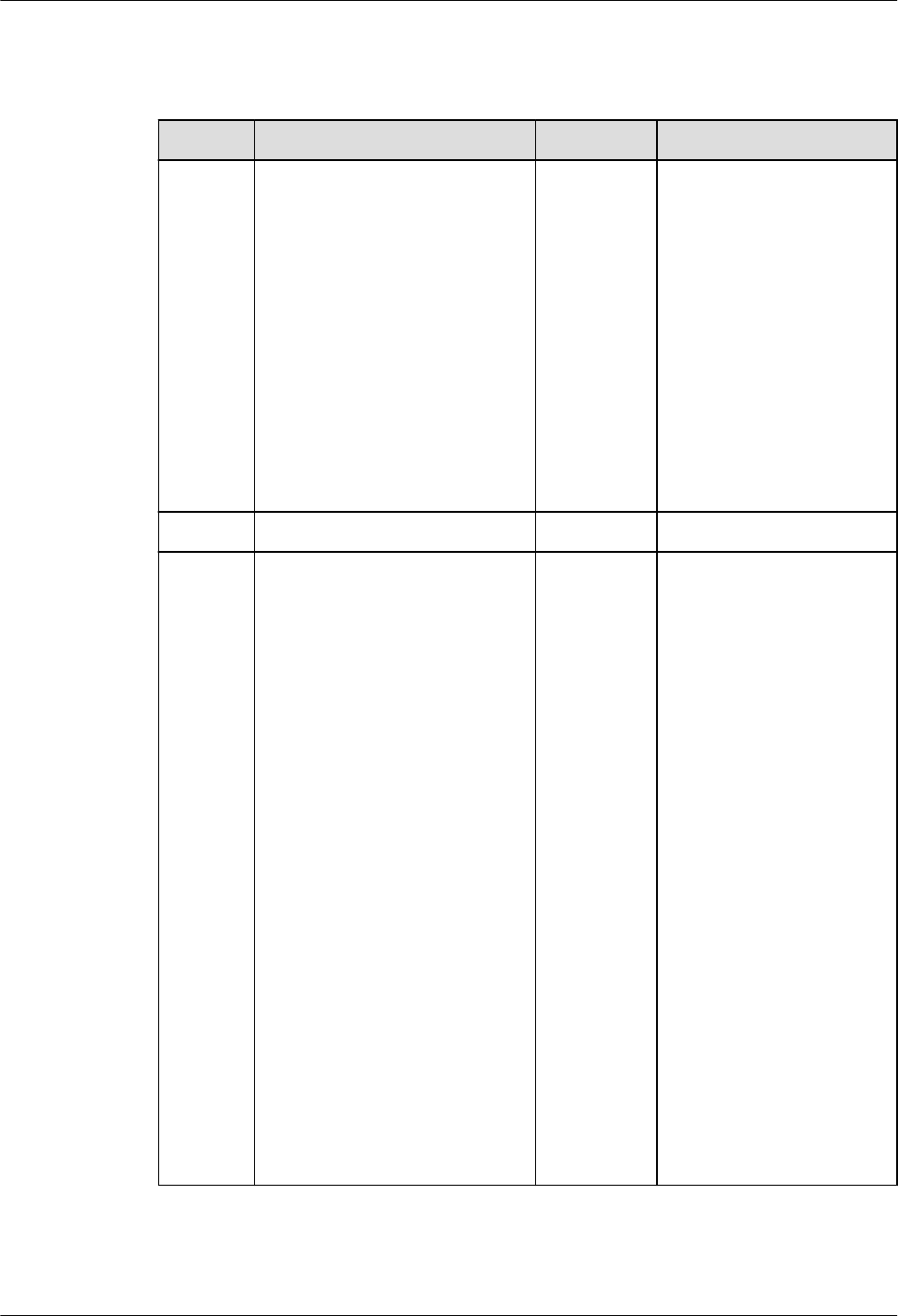
8.2.3.3.6 Comparison Functions
Table 8-60 Comparison functions
No. MySQL GaussDB Dierence
1 COALESCE() Supported,
with
dierences.
In the union distinct
scenario, the precision
of the return value is
dierent from that in
MySQL.
If there is an implicit
type conversion error in
the subsequent
parameter expression of
the rst parameter that
is not NULL, MySQL
ignores the error while
GaussDB displays a type
conversion error.
2 INTERVAL() Supported. -
3 GREATEST() Supported,
with
dierences.
If the return value type
in MySQL is binary
string (such as BINARY,
VARBINARY, or BLOB),
the return value type in
GaussDB is LONGBLOB.
If the return value type
in MySQL is non-binary
string (such as CHAR,
VARCHAR, or TEXT), the
return value type in
GaussDB is TEXT.
If the input parameter
of the function contains
NULL and the function
is invoked after the
WHERE keyword, the
returned result is
inconsistent with that of
MySQL 5.7. This
problem lies in MySQL
5.7. Since MySQL 8.0
has resolved this
problem, GaussDB are
consistent with MySQL
8.0.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 622

No. MySQL GaussDB Dierence
4 LEAST() Supported,
with
dierences.
If the return value type
in MySQL is binary
string (such as BINARY,
VARBINARY, or BLOB),
the return value type in
GaussDB is LONGBLOB.
If the return value type
in MySQL is non-binary
string (such as CHAR,
VARCHAR, or TEXT), the
return value type in
GaussDB is TEXT.
If the input parameter
of the function contains
NULL and the function
is invoked after the
WHERE keyword, the
returned result is
inconsistent with that of
MySQL 5.7. This
problem lies in MySQL
5.7. Since MySQL 8.0
has resolved this
problem, GaussDB are
consistent with MySQL
8.0.
5
ISNULL() Supported. -
8.2.3.3.7 Aggregate Functions
Table 8-61 Aggregate functions
No.
MySQL GaussDB Dierence
1 AVG() Supported, with
dierences.
● In GaussDB, if DINSTINCT is
specied and the SQL
statement contains a GROUP
BY clause, the result sequence
is not guaranteed.
● In GaussDB, if the columns in
expr are of the BIT, BOOL, or
integer type and the sum of
all rows exceeds the range of
BIGINT, overow occurs,
reversing integers.
2 BIT_AND() Supported -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 623
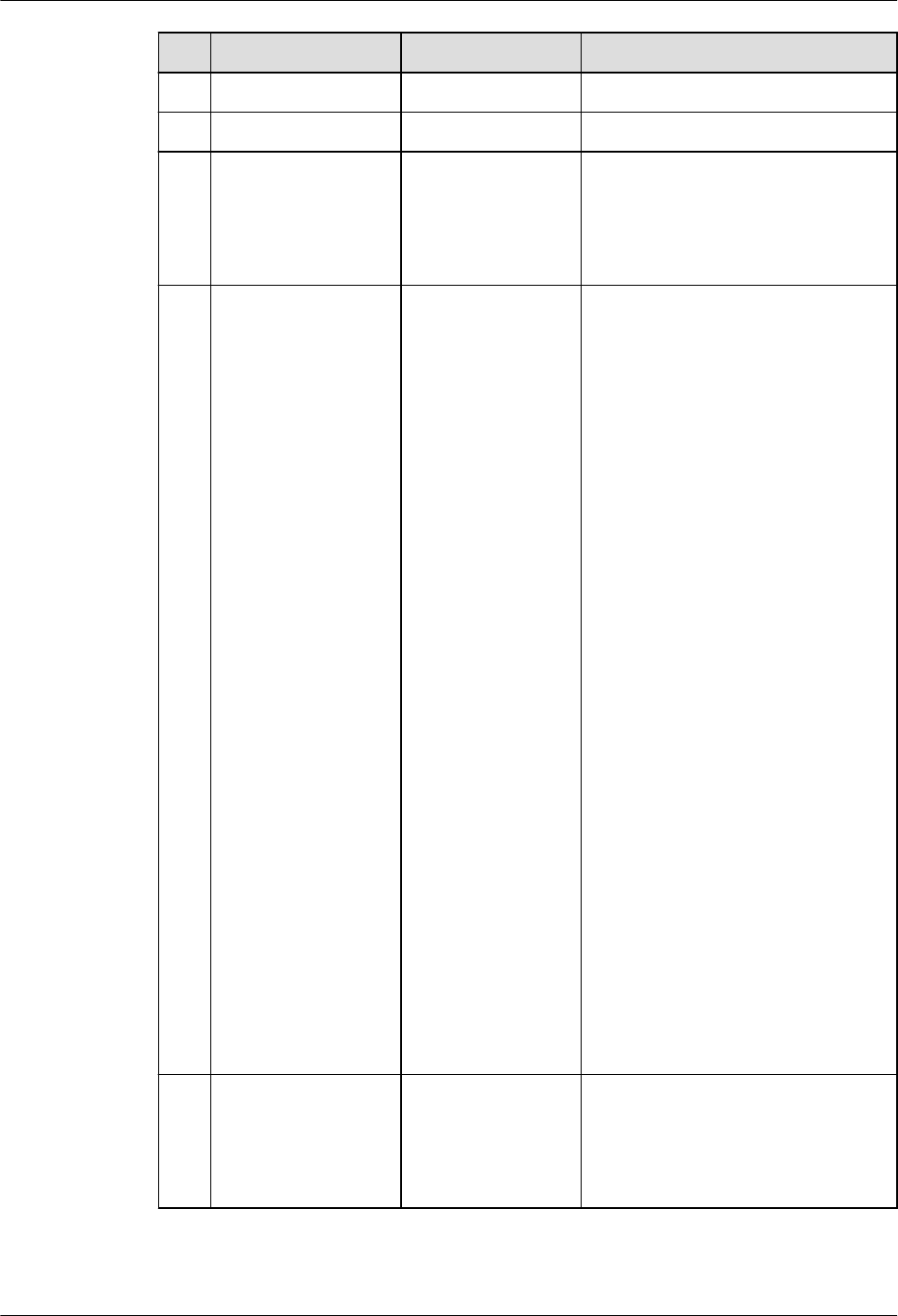
No. MySQL GaussDB Dierence
3 BIT_OR() Supported -
4 BIT_XOR() Supported -
5 COUNT() Supported, with
dierences.
In GaussDB, if DINSTINCT is
specied and the SQL statement
contains a GROUP BY clause, the
result sequence is not
guaranteed.
6 GROUP_CONCAT() Supported, with
dierences.
● In GaussDB, if DINSTINCT is
specied and the SQL
statement contains a GROUP
BY clause, the result sequence
is not guaranteed.
● In GaussDB, if the parameters
in GROUP_CONCAT contain
both the DISTINCT and
ORDER BY syntaxes, all
expressions following ORDER
BY must be in the DISTINCT
expression.
● In GaussDB,
GROUP_CONCAT(... ORDER
BY
Number
) does not
indicate the sequence of the
parameter. The number is
only a constant expression,
which is equivalent to no
sorting.
● In GaussDB, the
group_concat_max_len
parameter is used to limit the
maximum return length of
GROUP_CONCAT. If the
return length exceeds the
maximum, the length is
truncated. Currently, the
maximum length that can be
returned is 1073741823,
which is smaller than that in
MySQL.
7
MAX() Supported, with
dierences.
In GaussDB, if DINSTINCT is
specied and the SQL statement
contains a GROUP BY clause, the
result sequence is not
guaranteed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 624

No. MySQL GaussDB Dierence
8 MIN() Supported, with
dierences.
In GaussDB, if DINSTINCT is
specied and the SQL statement
contains a GROUP BY clause, the
result sequence is not
guaranteed.
9 SUM() Supported, with
dierences.
● In GaussDB, if DINSTINCT is
specied and the SQL
statement contains a GROUP
BY clause, the result sequence
is not guaranteed.
● In GaussDB, if the columns in
expr are of the BIT, BOOL, or
integer type and the sum of
all rows exceeds the range of
BIGINT, overow occurs,
reversing integers.
8.2.3.3.8 Arithmetic Functions
Table 8-62 Arithmetic functions
No.
MySQL GaussDB Dierence
1 ABS() Supported. -
2 ACOS() Supported. -
3 ASIN() Supported. -
4 ATAN() Supported. -
5 ATAN2() Supported. -
6 CEILING() Supported. -
7 COS() Supported. -
8 DEGREES() Supported. -
9 EXP() Supported. -
10 FLOOR() Supported,
with
dierences.
The return value types of the
FLOOR function in GaussDB are
dierent from those in MySQL.
When the input parameter type
is INT, the return value type is
BIGINT in GaussDB, but is INT in
MySQL.
11 LN() Supported. -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 625
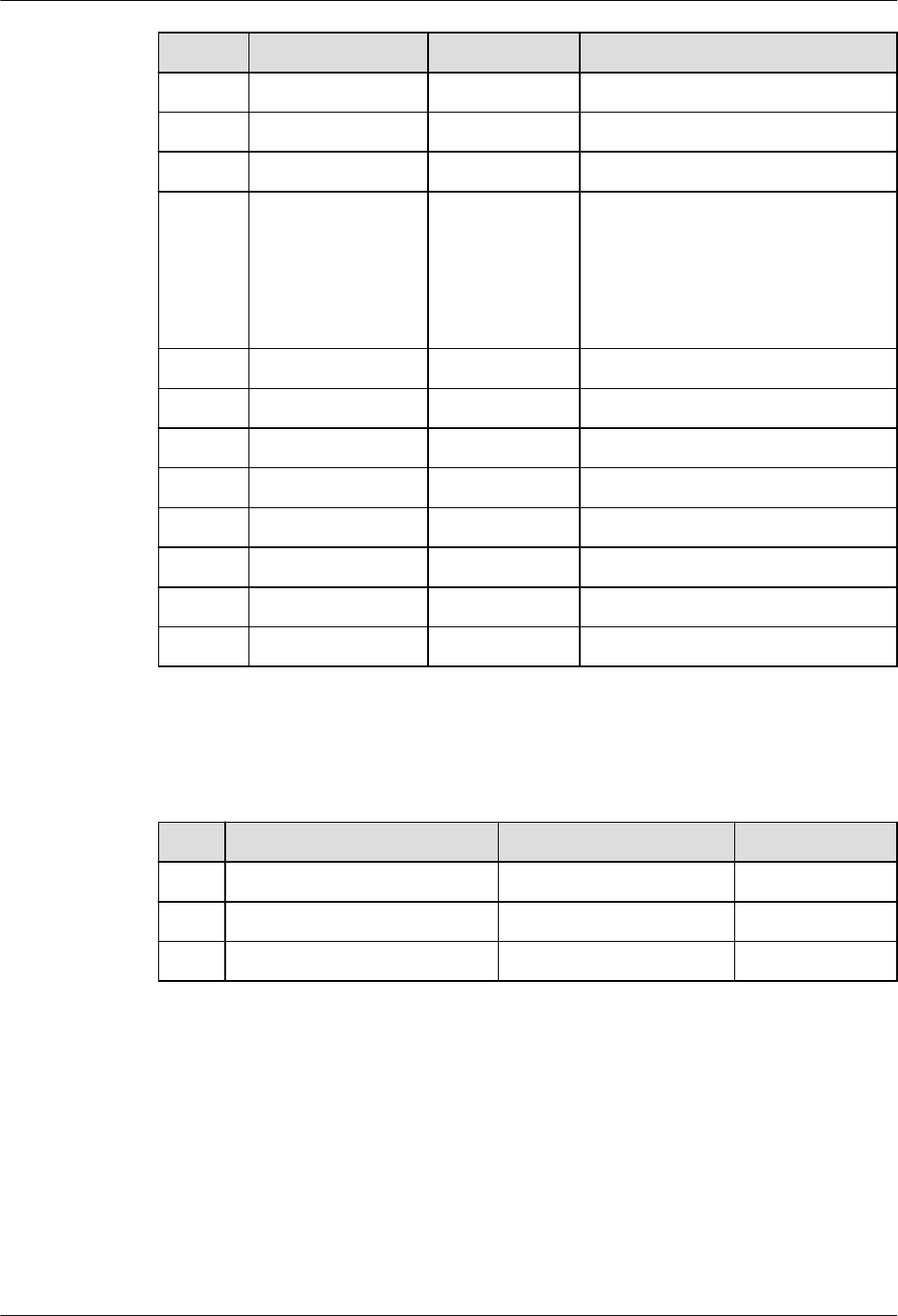
No. MySQL GaussDB Dierence
12 LOG() Supported. -
13 LOG10() Supported. -
14 LOG2() Supported. -
15 PI() Supported. The precision of the return value
of the PI function in GaussDB is
dierent from that in MySQL. It
is rounded o to 15 decimal
places in GaussDB but to six
decimal places in MySQL.
16 POW() Supported. -
17 POWER() Supported. -
18 RAND() Supported. -
19 SIGN() Supported. -
20 SIN() Supported. -
21 SQRT() Supported. -
22 TAN() Supported. -
23 TRUNCATE() Supported. -
8.2.3.3.9 Other Functions
Table 8-63 Other functions
No.
MySQL GaussDB Dierence
1 DATABASE() Supported -
2 UUID() Supported -
3 UUID_SHORT() Supported -
8.2.3.4 Operators
GaussDB is compatible with most MySQL operators, but there are some
dierences. If they are not listed, the operator behavior is the native behavior of
GaussDB by default. Currently, there are statements that are not supported by
MySQL but supported by GaussDB. You are advised not to use these statements.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 626

Operator Dierences
● NULL values in ORDER BY are sorted in dierent ways. MySQL sorts NULL
values rst, while GaussDB sorts NULL values last. In GaussDB, nulls rst and
nulls last can be used to set the sorting sequence of NULL values.
● If ORDER BY is used, the output sequence of GaussDB is the same as that of
MySQL. Without ORDER BY, GaussDB does not guarantee that the results are
ordered.
● MySQL operators must use parentheses to ensure that an expression is strictly
combined in a correct priority. Otherwise, an error is reported. For example,
SELECT 1 regexp ('12345' regexp '123').
GaussDB operators support expressions that are not strictly combined by
parentheses to be successfully executed.
● NULL values are displayed in dierent ways. MySQL displays a NULL value as
"NULL". GaussDB displays a NULL value as empty.
MySQL output:
mysql> Select NULL;
+------+
| NULL |
+------+
| NULL |
+------+
1 row in set (0.00 sec)
GaussDB output:
m_db=# select NULL;
?column?
----------
(1 row)
● After the operator is executed, the column names are displayed in dierent
ways. MySQL displays a NULL value as "NULL". GaussDB displays a NULL
value as empty.
● When character strings are being converted to the double type but there is an
invalid one, the alarm is reported dierently. MySQL reports an error when
there is an invalid constant character string, but does not report an error for
an invalid column character string. GaussDB reports an error in either
situation.
● The results returned by the comparison operator are dierent. For MySQL, 1
or 0 is returned. For GaussDB, t or f is returned.
Table 8-64 Operators
No.
MySQL GaussDB Dierence
1 <> Supported, with
dierences.
MySQL supports indexes,
but GaussDB does not.
2 <=> Supported, with
dierences.
MySQL supports indexes,
but GaussDB does not
support indexes, hash
joins, or merge joins.
3 Row
expressions
Not supported. MySQL supports <=>, but
GaussDB does not.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 627

No. MySQL GaussDB Dierence
4 -- Supported. MySQL indicates that an
operand is negated twice
and the result is equal to
the original operand.
GaussDB indicates a
comment.
5 !! Supported, with
dierences.
MySQL: The meaning of !!
is the same as that of !,
indicating NOT.
GaussDB: The
exclamation mark (!)
indicates NOT. If there is a
space between two
exclamation marks (! !), it
indicates NOT for twice. If
there is no space between
them (!!), it indicates
factorial.
NOTE
● In GaussDB, when both
factorial (!!) and NOT (!)
are used, a space must
be added between them.
Otherwise, an error is
reported.
● In GaussDB, when
multiple NOT operations
are required, use a space
between exclamation
marks (! !).
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 628

No. MySQL GaussDB Dierence
6 [NOT] REGEXP Supported, with
dierences.
● GaussDB and MySQL
support dierent
metacharacters in
regular expressions.
For example, GaussDB
allows \d to indicate
digits, \w to indicate
letters, digits, and
underscores (_), and \s
to indicate spaces.
However, MySQL does
not support these
metacharacters and
considers them as
normal character
strings.
● In GaussDB, '\b' can
match '\\b', but in
MySQL, the matching
will fail.
● In the new GaussDB
framework, a
backslash (\) indicates
an escape character. In
MySQL, two
backslashes (\\) are
used.
● MySQL does not
support two operators
to be used together.
● GaussDB reports an
error when the input
parameter of the
pattern string pat is
invalid and only the
right single parenthesis
')' exists. MySQL has a
bug, which has been
xed in later versions.
● When de|abc matches
de or abc, if there is a
null value on the left
or right of |, MySQL
reports an error. This
bug has been xed in
later versions.
● The regular expression
of the blank character
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 629

No. MySQL GaussDB Dierence
[\t] can match the
character class
[:blank:] in GaussDB,
but MySQL's [\t]
cannot match [:blank:].
MySQL has a bug,
which has been xed
in later versions.
● GaussDB supports
non-greedy pattern
matching. That is, the
number of matching
characters is as small
as possible. A question
mark (?) is added after
some special
characters, for
example, ??, *?, +?,
{n}?, {n,}?, and {n,m}?.
MySQL 5.7 does not
support non-greedy
pattern matching, and
the error message
"Got error 'repetition-
operator operand
invalid' from regexp" is
displayed. MySQL 8.0
already supports this
function.
● In the binary character
set, the text and BLOB
types are converted to
the bytea type. The
REGEXP operator does
not support the bytea
type. Therefore, the
two types cannot be
matched.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 630

No. MySQL GaussDB Dierence
7 LIKE Supported, with
dierences.
MySQL: The left operand
of LIKE can only be an
expression of a bitwise or
arithmetic operation, or
expression consisting of
parentheses. The right
operand of LIKE can only
be an expression
consisting of unary
operators (excluding
NOT) or parentheses.
GaussDB: The left and
right operands of LIKE
can be any expression.
8 [NOT]
BETWEEN AND
Supported, with
dierences.
MySQL: [NOT] BETWEEN
AND is nested from right
to left. The rst and
second operands of
[NOT] BETWEEN AND
can only be expressions of
bitwise or arithmetic
operations, or expressions
consisting of parentheses.
GaussDB: [NOT]
BETWEEN AND is nested
from left to right. The
rst and second operands
of [NOT] BETWEEN AND
can be any expression.
9 IN Supported, with
dierences.
MySQL: The left operand
of IN can only be an
expression of a bitwise or
arithmetic operation, or
expression consisting of
parentheses.
GaussDB: The left
operand of IN can be any
expression.
10 ! Supported, with
dierences.
MySQL: The operand of !
can only be an expression
consisting of unary
operators (excluding
NOT) or parentheses.
GaussDB: The operand
of ! can be any
expression.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 631

No. MySQL GaussDB Dierence
11 # Not supported. MySQL supports the
comment tag (#), but
GaussDB does not.
Table 8-65 Dierences in operator combinations
Example of Operator
Combination
MySQL GaussD
B
Description
SELECT 1 LIKE 3 & 1; Not
support
ed
Support
ed
The right operand of LIKE
cannot be an expression
consisting of bitwise operators.
SELECT 1 LIKE 1 +1; Not
support
ed
Support
ed
The right operand of LIKE
cannot be an expression
consisting of arithmetic
operators.
SELECT 1 LIKE NOT 0; Not
support
ed
Support
ed
The right operand of LIKE can
only be an expression consisting
of unary operators (such as +, -,
or ! but except NOT) or
parentheses.
SELECT 1 BETWEEN 1
AND 2 BETWEEN 2
AND 3;
Right-
to-left
combina
tion
Left-to-
right
combina
tion
It is recommended that
parentheses be added to specify
the priority.
SELECT 2 BETWEEN
1=1 AND 3;
Not
support
ed
Support
ed
The second operand of
BETWEEN cannot be an
expression consisting of
comparison operators.
SELECT 0 LIKE 0
BETWEEN 1 AND 2;
Not
support
ed
Support
ed
The rst operand of BETWEEN
cannot be an expression
consisting of pattern matching
operators.
SELECT 1 IN (1)
BETWEEN 0 AND 3;
Not
support
ed
Support
ed
The rst operand of BETWEEN
cannot be an expression
consisting of IN operators.
SELECT 1 IN (1) IN (1); Not
support
ed
Support
ed
The second left operand of the
IN expression cannot be an
expression consisting of INs.
SELECT ! NOT 1; Not
support
ed
Support
ed
The operand of ! can only be an
expression consisting of unary
operators (such as +, -, or ! but
except NOT) or parentheses.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 632

NO TE
Combinations of operators that are supported in Gauss but not supported in MySQL are not
recommended. You are advised to combine operators according to the rules in MySQL.
Index Dierences
● Currently, GaussDB supports only UB-tree and B-tree indexes.
● For fuzzy match (LIKE operator), the default index created can be used in
MySQL, but cannot be used in GaussDB. You need to use the following syntax
to specify opclass to, for example, text_pattern_ops, so that LIKE operators
can be used as indexes:
CREATE INDEX indexname ON tablename(col [opclass]);
● In the B-tree/UB-tree index scenario, the original logic of the native GaussDB
is retained. That is, index scan supports comparison of types in the same
operator family, but does not support other index types currently.
● In the operation scenarios involving index column type and constant type, the
conditions that indexes of a WHERE clause are supported in GaussDB is
dierent from those in MySQL, as shown in the following table. For example,
GaussDB does not support indexes in the following statement:
create table t(_int int);
create index idx on t(_int) using BTREE;
select * from t where _int > 2.0;
NO TE
In the operation scenarios involving index column type and constant type in the
WHERE clause, you can use the cast function to convert the constant type to the
column type for indexing.
select * from t where _int > cast(2.0 as signed);
Table 8-66 Dierences in index support
Index Column
Type
Constant Type GaussDB MySQL
Integer Integer Yes Yes
Floating-point Floating-point Yes Yes
Fixed-point Fixed-point Yes Yes
String String Yes Yes
Binary Binary Yes Yes
Time with date Time with date Yes Yes
TIME TIME Yes Yes
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 633

Index Column
Type
Constant Type GaussDB MySQL
Time with date Type that can be
converted to
time type with
date (for
example,
integers such as
20231130)
Yes Yes
Time with date TIME Yes Yes
TIME Constants that
can be converted
to the TIME type
(for example,
integers such as
203008)
Yes Yes
Floating-point Integer Yes Yes
Floating-point Fixed-point Yes Yes
Floating-point String Yes Yes
Floating-point Binary Yes Yes
Floating-point Time with date Yes Yes
Floating-point TIME Yes Yes
Fixed-point Integer Yes Yes
String Time with date Yes No
String TIME Yes No
Binary String Yes Yes
Binary Time with date Yes No
Binary TIME Yes No
Integer Floating-point No Yes
Integer Fixed-point No Yes
Integer String No Yes
Integer Binary No Yes
Integer Time with date No Yes
Integer TIME No Yes
Fixed-point Floating-point No Yes
Fixed-point String No Yes
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 634

Index Column
Type
Constant Type GaussDB MySQL
Fixed-point Binary No Yes
Fixed-point Time with date No Yes
Fixed-point TIME No Yes
String Binary No Yes
Time with date Integer (that
cannot be
converted to the
time type with
date)
No Yes
Time with date Floating-point
(that cannot be
converted to the
time type with
date)
No Yes
Time with date Fixed-point (that
cannot be
converted to the
time type with
date)
No Yes
TIME Integer (that
cannot be
converted to the
TIME type)
No Yes
TIME Character string
(that cannot be
converted to the
TIME type)
No Yes
TIME Binary (that
cannot be
converted to the
TIME type)
No Yes
TIME Time with date No Yes
Table 8-67 Whether index use is supported
Index Column
Type
Constant Type Use Index or
Not
MySQL
String Integer No No
String Floating-point No No
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 635

Index Column
Type
Constant Type Use Index or
Not
MySQL
String Fixed-point No No
Binary Integer No No
Binary Floating-point No No
Binary Fixed-point No No
Time with date Character string
(that cannot be
converted to the
time type with
date)
No No
Time with date Binary (that
cannot be
converted to the
time type with
date)
No No
TIME Floating-point
(that cannot be
converted to the
TIME type)
No No
TIME Fixed-point (that
cannot be
converted to the
TIME type)
No No
8.2.3.5 Character Sets
GaussDB allows you to specify the following character sets for databases,
schemas, tables, or columns.
Table 8-68 Character sets
No.
MySQL GaussDB
1 utf8mb4 Supported
2 utf8 Supported
3 gbk Supported
4 gb18030 Supported
5 binary Supported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 636

NO TE
● utf8 and utf8mb4 refer to the same character set in GaussDB. The maximum code
length is 4 bytes. As a result, if the current character set is utf8 and the collation is set
to utf8mb4_bin, utf8mb4_general_ci, utf8mb4_unicode_ci, or utf8mb4_0900_ai_ci
(for example, by running select _utf8'a' collate utf8mb4_bin), MySQL reports an error
but GaussDB does not report an error. The dierence also exists when the character set
is utf8mb4 and the collation is set to utf8_bin, utf8_general_ci, or utf8_unicode_ci.
● The lexical syntax is parsed based on byte streams. If a multi-byte character contains
code that is consistent with symbols such as '\', '\'', and '\\', the behavior of the multi-
byte character is inconsistent with that in MySQL. In this case, you are advised to disable
the escape character function temporarily.
8.2.3.6 Collation Rules
GaussDB allows you to specify the following collation rules for schemas, tables, or
columns.
NO TE
Dierences in collation rules:
● Currently, only the character string type and some binary types support the specied
collation rules. You can check whether the typcollation attribute of a type in the
pg_type system catalog is not 0 to determine whether the type supports the collation.
The collation can be specied for all types in MySQL. However, collation rules are
meaningless except those for character strings and binary types.
● The current collation rules (except binary) can be specied only when the corresponding
character set is the same as the database-level character set. In GaussDB, the character
set must be the same as the database character set, and multiple character sets cannot
be used together in a table.
● The default collation of the utf8mb4 character set is utf8mb4_general_ci, which is the
same as that in MySQL 5.7.
Table 8-69 Collation rules
No.
MySQL GaussDB
1 utf8mb4_general_ci Supported
2 utf8mb4_unicode_ci Supported
3 utf8mb4_bin Supported
4 gbk_chinese_ci Supported
5 gbk_bin Supported
6 gb18030_chinese_ci Supported
7 gb18030_bin Supported
8 binary Supported
9 utf8mb4_0900_ai_ci Supported
10 utf8_general_ci Supported
11 utf8_bin Supported
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 637

No. MySQL GaussDB
12 utf8_unicode_ci Supported
8.2.3.7 Transactions
GaussDB is compatible with MySQL transactions, but there are some dierences.
This section describes transaction-related dierences in GaussDB M-compatible
databases.
Default Transaction Isolation Levels
The default isolation level of an M-compatible database is READ COMMITTED,
and that of MySQL is REPEATABLE-READ.
-- View the current transaction isolation level.
m_db=# SHOW transaction_isolation;
Sub-transactions
In an M-compatible database, SAVEPOINT is used to create a savepoint (sub-
transaction) in the current transaction, and ROLLBACK TO SAVEPOINT is used to
roll back to a savepoint (sub-transaction). After the sub-transaction is rolled back,
the parent transaction can continue to run, the rollback of a sub-transaction does
not aect the transaction status of the parent transaction.
No savepoint (sub-transaction) can be created in MySQL.
Nested Transactions
A nested transaction refers to a new transaction started in a transaction block.
In an M-compatible database, if a new transaction is started in a normal
transaction block, a warning is displayed indicating that an ongoing transaction
exists and the start command is ignored. If a new transaction is started in an
abnormal transaction block, an error is reported. The transaction can be executed
only after ROLLBACK or COMMIT is executed. If ROLLBACK or COMMIT is
executed, the previous statement is rolled back.
In MySQL, if a new transaction is started in a normal transaction block, the
previous transaction is committed and then the new transaction is started. If a
new transaction is started in an abnormal transaction block, the error is ignored,
and the previous error-free statement is committed and the new transaction is
started.
-- In an M-compatible database, if a new transaction is started in a normal transaction block, a warning is
generated and the transaction is ignored.
m_db=# DROP TABLE IF EXISTS test_t;
m_db=# CREATE TABLE test_t(a int, b int);
m_db=# BEGIN;
m_db=# INSERT INTO test_t values(1, 2);
m_db=# BEGIN; --The warning "There is already a transaction in progress" is displayed.
m_db=# SELECT * FROM test_t ORDER BY 1;
m_db=# COMMIT;
-- In an M-compatible database, if a new transaction is started in an abnormal transaction block, an error is
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 638
reported. The transaction can be executed only after ROLLBACK/COMMIT is executed.
m_db=# BEGIN;
m_db=# ERROR sql; --Error statement.
m_db=# BEGIN; --An error is reported.
m_db=# COMMIT; -- It can be executed only after ROLLBACK/COMMIT is executed.
Statements Committed Implicitly
An M-compatible database uses GaussDB for storage and inherits the GaussDB
transaction mechanism. If a DDL or DCL statement is executed in a transaction,
the transaction is not automatically committed.
In MySQL, if DDL, DCL, management-related, or lock-related statements are
executed, the transaction is automatically committed.
-- In M-compatible database, table creation and GUC parameter setting support rollback.
m_db=# DROP TABLE IF EXISTS test_table_rollback;
m_db=# BEGIN;
m_db=# CREATE TABLE test_table_rollback(a int, b int);
m_db=# \d test_table_rollback;
m_db=# ROLLBACK;
m_db=# \d test_table_rollback; -- This table does not exist.
Dierences in SET TRANSACTION
In an M-compatible database, if SET TRANSACTION is used to set the isolation
level or transaction access mode for multiple times, only the last setting takes
eect. Transaction features can be separated by spaces or commas (,).
In MySQL, SET TRANSACTION cannot be used to set the isolation level or
transaction access mode for multiple times. Transaction features can only be
separated by commas (,).
Table 8-70 Dierences in SET TRANSACTION
No.
Syntax Function Dierence
1 SET
TRANSACTIO
N
Sets transactions. In an M-compatible database, SET
TRANSACTION takes eect in
session-level transactions. In MySQL,
SET TRANSACTION takes eect in
the next transaction.
2 SET SESSION
TRANSACTIO
N
Sets session-level
transactions.
-
3 SET GLOBAL
TRANSACTIO
N
Sets global
session-level
transactions. This
feature is
applicable to
subsequent
sessions and has
no impact on the
current session.
In an M-compatible database,
GLOBAL takes eect in global
session-level transactions and is
applicable only to the current
database instance.
In MySQL, this feature takes eect in
all databases.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 639

-- SET TRANSACTION takes eect in session-level transactions.
m_db=# SET TRANSACTION ISOLATION LEVEL READ COMMITTED READ WRITE;
m_db=# SHOW transaction_isolation;
m_db=# SHOW transaction_read_only;
-- In an M-compatible database, if the isolation level or transaction access mode is set for multiple times,
only the last setting takes eect.
m_db=# SET SESSION TRANSACTION ISOLATION LEVEL READ COMMITTED, ISOLATION LEVEL
REPEATABLE READ, READ WRITE, READ ONLY;
m_db=# SHOW transaction_isolation; -- repeatable read
m_db=# SHOW transaction_read_only; -- on
Dierences in START TRANSACTION
In an M-compatible database, when START TRANSACTION is used to start a
transaction, the isolation level can be set. If the isolation level or transaction
access mode is set for multiple times, only the last setting takes eect. In the
current version, consistency snapshot cannot be enabled immediately. Transaction
features can be separated by spaces or commas (,).
In MySQL, if START TRANSACTION is used to start a transaction, the isolation level
cannot be set and the transaction access mode cannot be set for multiple times.
Transaction features can only be separated by commas (,).
-- Start a transaction and set the isolation level.
m_db=# START TRANSACTION ISOLATION LEVEL READ COMMITTED;
m_db=# COMMIT;
-- Set the access mode for multiple times.
m_db=# START TRANSACTION READ ONLY, READ WRITE;
m_db=# COMMIT;
Transaction-related GUC Parameters
Table 8-71 Dierences in transaction-related GUC parameters
No.
GUC
Paramete
r
Function Dierence
1 autocomm
it
Sets the
automatic
transaction
commit
mode.
The current version does not support SET
autocommit = o in an M-compatible
database.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 640

No. GUC
Paramete
r
Function Dierence
2 transactio
n_isolation
Sets the
isolation
level of the
current
transaction
in an M-
compatible
database.
Sets the
isolation
level of a
session-
level
transaction
in MySQL.
1. In an M-compatible database, you can
only change the isolation level of the
current transaction by running the SET
command. To change the session-level
isolation level, use
default_transaction_isolation.
In MySQL, you can run the SET command
to change the transaction level for a
session.
2. The current version of an M-compatible
database supports the following isolation
levels, which are case-sensitive and space-
sensitive:
● READ COMMITTED
● READ UNCOMMITTED
● REPEATABLE READ
● SERIALIZABLE
● DEFAULT (The level is set to be the
same as the default isolation level in
the session.)
MySQL supports the following isolation
levels, which are case-insensitive but
space-sensitive:
● READ-UNCOMMITTED
● READ-COMMITTED
● REPEATABLE-READ
● SERIALIZABLE
3. In GaussDB, the value of
transaction_isolation of a new
transaction is initialized to the value of
default_transaction_isolation.
3
tx_isolatio
n
Sets the
transaction
isolation
level.
tx_isolatio
n and
transaction
_isolation
are
synonyms.
M-compatible databases do not support this
parameter currently.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 641

No. GUC
Paramete
r
Function Dierence
4 default_tr
ansaction_
isolation
Sets the
transaction
isolation
level.
In an M-compatible database, the SET
command is used to change the transaction
isolation level for a session.
MySQL does not support this system
parameter.
5 transactio
n_read_on
ly
Sets the
access
mode of a
transaction.
1. In an M-compatible database, only the
access mode of the current transaction can
be changed by using the SET command. If
you want to change the access mode of a
session-level transaction, you can use
default_transaction_read_only.
In MySQL, you can run the SET command
to change the transaction level for a
session.
2. In GaussDB, the value of
transaction_read_only of a new
transaction is initialized to the value of
default_transaction_read_only.
6 tx_read_o
nly
Sets the
access
mode of a
transaction.
tx_read_on
ly and
transaction
_read_only
are
synonyms.
M-compatible databases do not support this
parameter currently.
7 default_tr
ansaction_
read_only
Sets the
access
mode of a
transaction.
In an M-compatible database, the SET
command is used to change the access mode
of a session-level transaction. MySQL does
not support this system parameter.
8.2.3.8 SQL
GaussDB is compatible with most MySQL syntax, but there are some dierences.
This section describes the MySQL syntax supported by GaussDB.
Some keywords can be used as identiers in MySQL, but cannot or are restricted
to be identiers in M-compatible mode, as listed in Keywords restricted to be
identiers.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 642
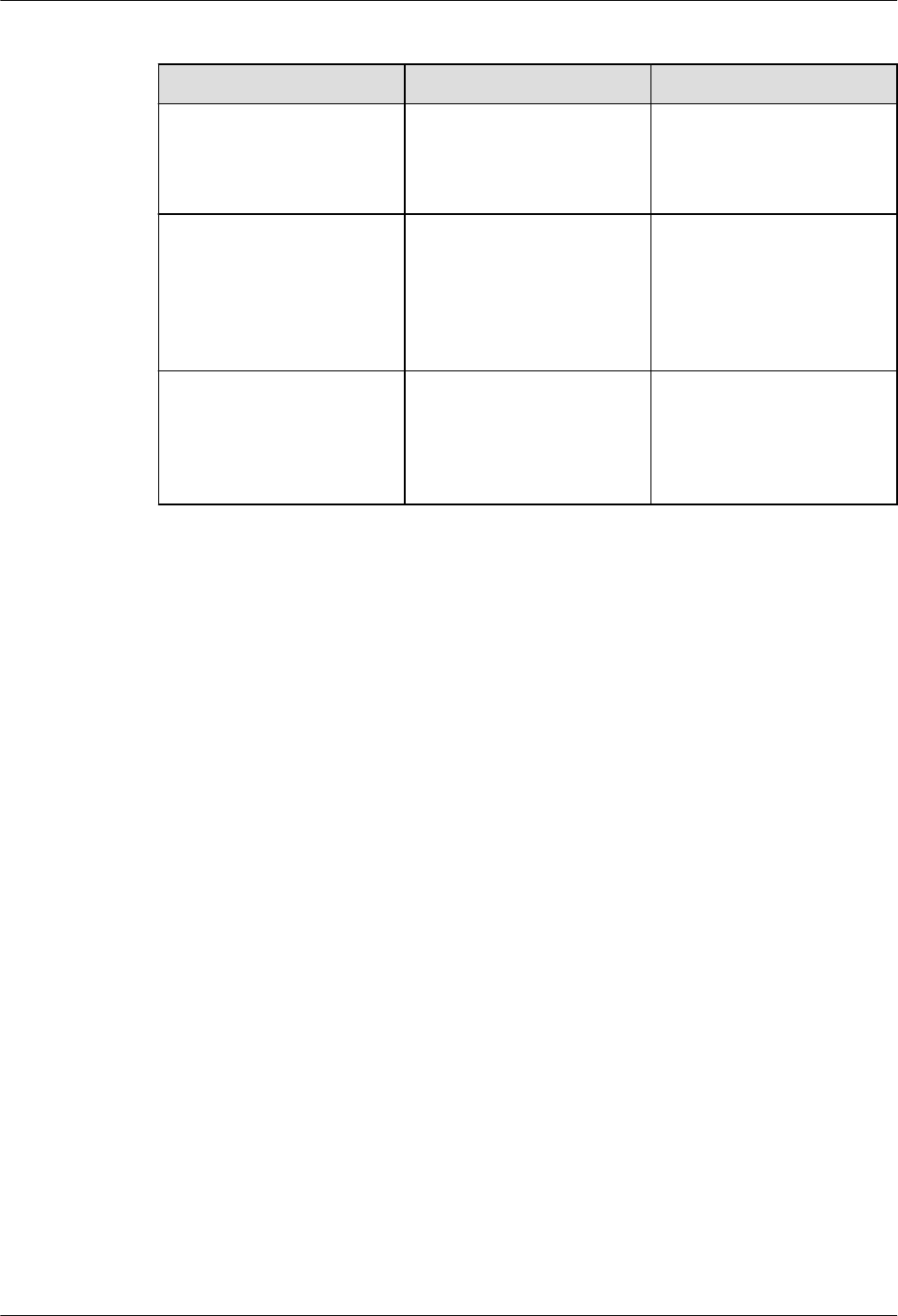
Table 8-72 Keywords restricted to be identiers
Keyword Type Keyword Constraint
Reserved (Type or
function is allowed.)
COLLATION and
COMPACT
They cannot be used as
identiers in other
databases except for
functions and variables.
Non-reserved (Type or
function is not allowed.)
BIT, BOOLEAN,
COALESCE, DATE,
NATIONAL, NCHAR,
NONE, NUMBER, TEXT,
TIME, TIMESTAMP, and
TIMESTAMPDIFF
They cannot be used as
identiers for functions
or variables.
Reserved ANY, ARRAY, BUCKETS,
DO, END, LESS, MODIFY,
OFFSET, ONLY,
RETURNING, SOME, and
USER
They cannot be used as
identiers in any
database.
8.2.3.8.1 Keywords
The constraint dierences are as follows:
● In M-compatible mode, keywords are reserved keywords. In MySQL, keywords
are non-reserved keywords. In M-compatible mode, keywords cannot be used
as table names, column names, column aliases, AS column aliases, AS table
aliases, table aliases, function names, or variable names. In MySQL, keywords
can be used as these names or aliases.
● In M-compatible mode, keywords are non-reserved keywords. In MySQL,
keywords are reserved keywords. In M-compatible mode, keywords can be
used as table names, column names, column aliases, AS column aliases, AS
table aliases, table aliases, function names, or variable names. In MySQL,
keywords cannot be used as these names or aliases.
● In M-compatible mode, keywords are reserved keywords (functions or types).
In MySQL, keywords are reserved keywords. In M-compatible mode, keywords
can be used as column aliases, AS column aliases, function names, or variable
names. In MySQL, keywords cannot be used as these names or aliases.
● In M-compatible mode, keywords are reserved keywords (functions or types).
In MySQL, keywords are non-reserved keywords. In M-compatible mode,
keywords cannot be used as table aliases, column names, AS table aliases, or
table aliases. In MySQL, keywords can be used as these names or aliases.
● In M-compatible mode, keywords are non-reserved keywords (cannot be
functions or types). In MySQL, keywords are reserved keywords. In M-
compatible mode, keywords can be used as table aliases, column names,
column aliases, AS column aliases, AS table aliases, table aliases, or variable
names. In MySQL, keywords cannot be used as these names or aliases.
● In M-compatible mode, keywords are non-reserved keywords (cannot be
functions or types). In MySQL, keywords are non-reserved keywords. In M-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 643

compatible mode, keywords cannot be used as function names. In MySQL,
keywords can be used as these names or aliases.
NO TE
Among non-reserved keywords, reserved keywords (functions or types), and non-
reserved keywords (not functions or types) in M-compatible mode, the following
keywords cannot be used as column aliases:
BETWEEN, BIGINT, BLOB, CHAR, CHARACTER, CROSS, DEC, DECIMAL, DIV, DOUBLE,
EXISTS, FLOAT, FLOAT4, FLOAT8, GROUPING, INNER, INOUT, INT, INT1, INT2, INT3,
INT4, INT8, INTEGER, JOIN, LEFT, LIKE, LONGBLOB, LONGTEXT, MEDIUMBLOB,
MEDIUMINT, MEDIUMTEXT, MOD, NATURAL, NUMERIC, OUT, OUTER, PRECISION,
REAL, RIGHT, ROW, ROW_NUMBER, SIGNED, SMALLINT, SOUNDS, TINYBLOB, TINYINT,
TINYTEXT, VALUES, VARCHAR, VARYING, and WITHOUT.
SIGNED and WITHOUT can be used as column aliases in MySQL.
8.2.3.8.2 Identiers
Dierences in identiers in M-compatible mode are as follows:
● In GaussDB, unquoted identiers cannot start with a dollar sign ($). In MySQL
unquoted identiers can start with a dollar sign ($).
● GaussDB unquoted identiers support case-sensitive database objects.
● GaussDB identiers support extended characters from U+0080 to U+00FF.
MySQL identiers support extended characters from U+0080 to U+FFFF.
● As for unquoted identier, a table that starts with a digit and ends with an e
or E as the identier cannot be created in GaussDB. For example:
-- GaussDB reports an error indicating that this operation is not supported. MySQL supports this
operation.
m_db=# CREATE TABLE 23e(c1 int);
ERROR: syntax error at or near "23"
LINE 1: CREATE TABLE 23e(c1 int);
^
m_db=# CREATE TABLE t1(23E int);
ERROR: syntax error at or near "23"
LINE 1: CREATE TABLE t1(23E int);
^
● As for quoted identiers, tables whose column names contain only digits or
scientic computing cannot be directly used in GaussDB. You need to use
them in quotes. This rule also applies to the dot operator (.) scenarios. For
example:
-- Create a table whose column names contain only numbers or scientic computing.
m_db=# CREATE TABLE t1(`123` int, `1e3` int, `1e` int);
CREATE TABLE
-- Insert data into the table.
m_db=# INSERT INTO t1 VALUES(7, 8, 9);
INSERT 0 1
-- The result is not as expected, but is the same as that in MySQL.
m_db=# SELECT 123 FROM t1;
?column?
----------
123
(1 row)
-- The result is not as expected, but is the same as that in MySQL.
m_db=# SELECT 1e3 FROM t1;
?column?
----------
1000
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 644

(1 row)
-- The result is not as expected and is not the same as that in MySQL.
m_db=# SELECT 1e FROM t1;
e
---
1
(1 row)
-- The correct way to use is as follows:
m_db=# SELECT `123` FROM t1;
123
-----
7
(1 row)
m_db=# SELECT `1e3` FROM t1;
1e3
-----
8
(1 row)
m_db=# SELECT `1e` FROM t1;
1e
----
9
(1 row)
-- Dot operator scenarios are not supported by GaussDB but supported by MySQL.
m_db=# SELECT t1.123 FROM t1;
ERROR: syntax error at or near ".123"
LINE 1: SELECT t1.123 FROM t1;
^
m_db=# SELECT t1.1e3 FROM t1;
ERROR: syntax error at or near "1e3"
LINE 1: SELECT t1.1e3 FROM t1;
^
m_db=# SELECT t1.1e FROM t1;
ERROR: syntax error at or near "1"
LINE 1: SELECT t1.1e FROM t1;
^
-- The correct way to use in dot operator scenarios is as follows:
m_db=# SELECT t1.`123` FROM t1;
123
-----
7
(1 row)
m_db=# SELECT t1.`1e3` FROM t1;
1e3
-----
8
(1 row)
m_db=# SELECT t1.`1e` FROM t1;
1e
----
9
(1 row)
m_db=# DROP TABLE t1;
DROP TABLE
● In GaussDB, the partition name is case-sensitive when it is enclosed in double
quotation marks (SQL_MODE must be set to ANSI_QUOTES) or backquotes,
but in MySQL the partition name is case-insensitive.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 645

8.2.3.8.3 DDL
Description Syntax Dierence
Create primary keys,
UNIQUE indexes, and
foreign keys during
table creation and
modication.
ALTER TABLE and
CREATE TABLE
● GaussDB: When the table
joined with the constraint
is Ustore and USING
BTREE is specied in the
SQL statement, the
underlying index is created
as UB-tree.
● GaussDB: Foreign keys can
be used as partition keys.
● The index name,
constraint name, and key
name are unique in a
schema in GaussDB and
unique in a table in
MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 646

Description Syntax Dierence
Support auto-
increment columns.
ALTER TABLE and
CREATE TABLE
● It is recommended that an
auto-increment column in
GaussDB be the rst
column of an index.
Otherwise, an alarm is
generated during table
creation. The auto-
increment column in
MySQL must be the rst
column of the index.
Otherwise, an error is
reported during table
creation. In GaussDB, an
error occurs when some
operations (such as ALTER
TABLE EXCHANGE
PARTITION) are
performed on a table that
contains auto-increment
columns.
● For AUTO_INCREMENT =
value, value must be a
positive number less than
2^127 in GaussDB. In
MySQL, value can be 0.
● In GaussDB, an error
occurs if the auto-
increment continues after
an auto-increment value
reaches the maximum
value of a column data
type. In MySQL, errors or
warnings may be
generated during auto-
increment, and sometimes
auto-increment continues
until the maximum value
is reached.
● GaussDB does not support
the
innodb_autoinc_lock_mod
e
system variable, but
when its GUC parameter
auto_increment_cache is
set to 0, the behavior of
inserting auto-increment
columns in batches is
similar to that when the
MySQL system variable
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 647

Description Syntax Dierence
innodb_autoinc_lock_mod
e
is set to 1.
● In GaussDB, when 0s,
NULLs, and denite values
are imported or batch
inserted into auto-
increment columns, the
auto-increment values
inserted after an error
occurs in GaussDB may
not be the same as those
in MySQL.
– The
auto_increment_cache
parameter is provided
to control the number
of reserved auto-
increment values.
● In GaussDB, when auto-
increment is triggered by
parallel import or
insertion of auto-
increment columns, the
cache value reserved for
each parallel thread is
used only in the thread. If
the cache value is not
used up, the values of
auto-increment columns
in the table are
discontinuous. The auto-
increment value generated
by parallel insertion
cannot be guaranteed to
be the same as that
generated in MySQL.
● In GaussDB, when auto-
increment columns are
batch inserted into a local
temporary table, no auto-
increment value is
reserved. In normal
scenarios, auto-increment
values are not
discontinuous. In MySQL,
the auto-increment result
of an auto-increment
column in a temporary
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 648

Description Syntax Dierence
table is the same as that
in an ordinary table.
● The SERIAL data type of
GaussDB is an original
auto-increment column,
which is dierent from the
AUTO_INCREMENT
column. The SERIAL data
type of MySQL is the
AUTO_INCREMENT
column.
● GaussDB does not allow
the value of
auto_increment_oset to
be greater than that of
auto_increment_increme
nt. Otherwise, an error
occurs. MySQL allows it
and states that
auto_increment_oset
will be ignored.
● If a table has a primary
key or index, the sequence
in which the ALTER TABLE
command rewrites table
data may be dierent
from that in MySQL.
GaussDB rewrites table
data based on the table
data storage sequence,
while MySQL rewrites
table data based on the
primary key or index
sequence. As a result, the
auto-increment sequence
may be dierent.
● When the ALTER TABLE
command in GaussDB is
used to add or modify
auto-increment columns,
the number of auto-
increment values reserved
for the rst time is the
number of rows in the
table statistics. The
number of rows in the
statistics may not be the
same as that in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 649

Description Syntax Dierence
● The return value of the
last_insert_id function in
GaussDB is a 128-bit
integer.
● When GaussDB performs
auto-increment in a
trigger or user-dened
function, the return value
of last_insert_id is
updated. MySQL does not
update it.
● If the values of the GUC
parameters
auto_increment_oset
and
auto_increment_increme
nt in GaussDB are out of
range, an error occurs.
MySQL automatically
changes the value to a
boundary value.
Support
prex
indexes.
CREATE INDEX, ALTER
TABLE, and CREATE
TABLE
● GaussDB: The prex
length cannot exceed
2676. The actual length of
the key value is restricted
by the internal page. If a
column contains multi-
byte characters or an
index has multiple keys,
an error may be reported
when the index line length
exceeds the threshold.
● GaussDB: The primary key
index does not support
prex keys. The prex
length cannot be specied
when a primary key is
created or added.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 650
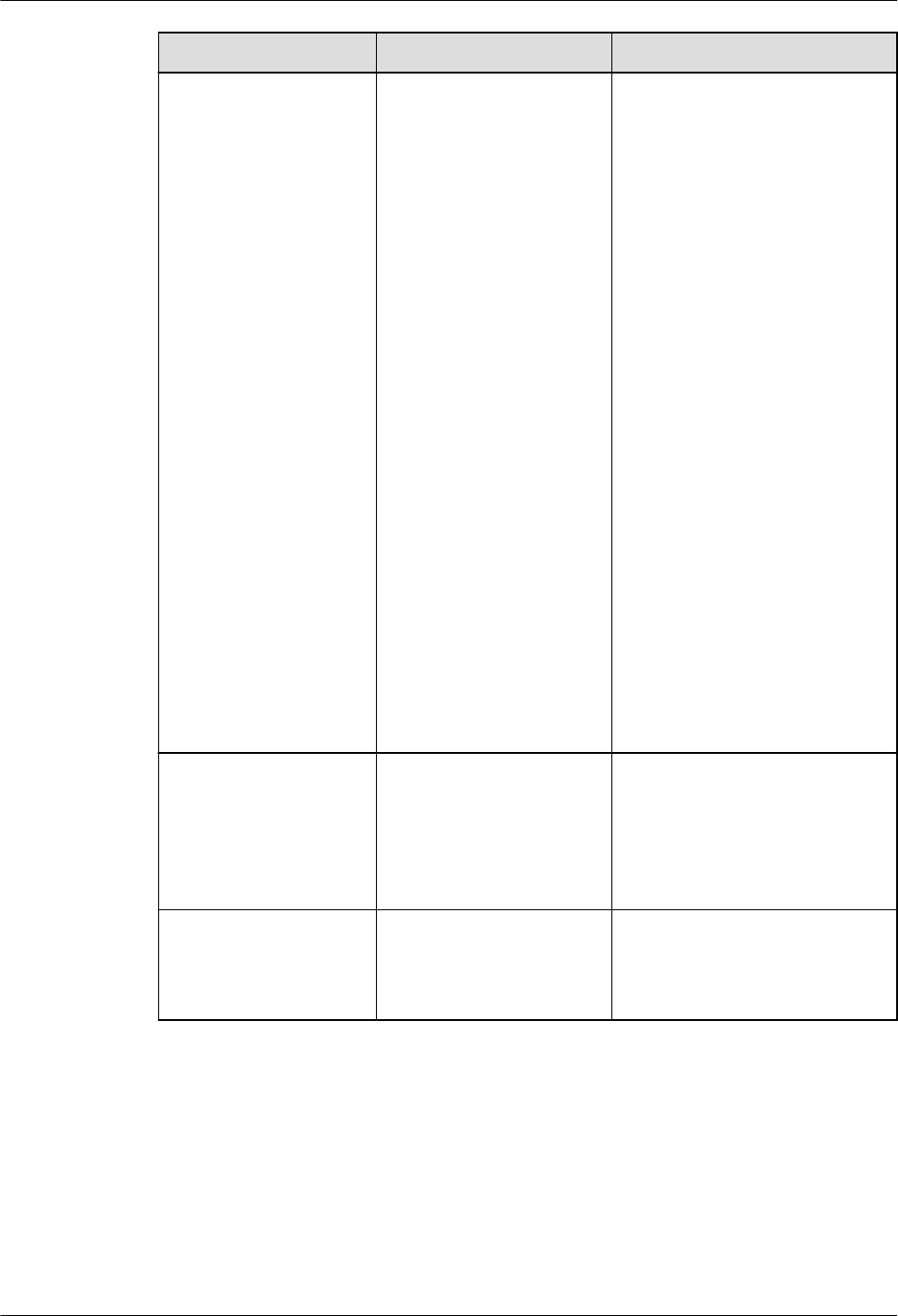
Description Syntax Dierence
Specify character sets
and collation rules.
ALTER SCHEMA, ALTER
TABLE, CREATE
SCHEMA, and CREATE
TABLE
● When you specify a
database-level character
set, except binary
character sets, the
character set of a new
database or schema
cannot be dierent from
that specied by
server_encoding of the
database.
● When you specify a table-
level or column-level
character set and
collation, MySQL allows
you to specify a character
set and collation that are
dierent from the
database-level character
set and collation. In
GaussDB, the table-level
and column-level
character sets and
collations support only the
binary character sets and
collations or can be the
same as the database-
level character sets and
collations.
Add columns before
the rst column of a
table or after a
specied column
during table
modication.
ALTER TABLE -
Compatible with the
column name
modication and the
denition syntax.
ALTER TABLE Currently, the DROP INDEX,
DROP KEY, or ORDER BY is
not supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 651

Description Syntax Dierence
Compatible with the
syntax for creating
partitioned tables.
CREATE TABLE
PARTITION and CREATE
TABLE SUBPARTITION
● For partition_key, the
partition key of the
partitioning policy
supports only one column
and does not support
expressions.
● For subpartition_key, the
partition key of the
partitioning policy
supports only one column
and does not support
expressions.
● The generated column
cannot be used as the
partition key of a
partitioned table.
Specify table-level
and column-level
comments during
table creation and
modication.
CREATE TABLE and
ALTER TABLE
-
Specify index-level
comments during
index creation.
CREATE INDEX -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 652

Description Syntax Dierence
Exchange the
partition data of an
ordinary table and a
partitioned table.
ALTER TABLE
PARTITION
Dierences in ALTER TABLE
EXCHANGE PARTITION:
● For auto-increment
columns, after the ALTER
EXCHANGE PARTITION is
executed in MySQL, the
auto-increment columns
are reset. In GaussDB, the
auto-increment columns
are not reset, and the
auto-increment columns
increase based on the old
auto-increment value.
● If MySQL tables or
partitions use tablespaces,
data in partitions and
ordinary tables cannot be
exchanged. If GaussDB
tables or partitions use
dierent tablespaces, data
in partitions and ordinary
tables can still be
exchanged.
● MySQL does not verify the
default values of columns.
Therefore, data in
partitions and ordinary
tables can be exchanged
even if the default values
are dierent. GaussDB
veries the default values.
If the default values are
dierent, data in
partitions and ordinary
tables cannot be
exchanged.
● After the DROP COLUMN
operation is performed on
a partitioned table or an
ordinary table in MySQL,
if the table structure is
still consistent, data can
be exchanged between
partitions and ordinary
tables. In GaussDB, data
can be exchanged
between partitions and
ordinary tables only when
the deleted columns of
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 653

Description Syntax Dierence
ordinary tables and
partitioned tables are
strictly aligned.
● MySQL and GaussDB use
dierent hash algorithms.
Therefore, data stored in
the same hash partition
may be inconsistent. As a
result, the exchanged data
may also be inconsistent.
● MySQL partitioned tables
do not support foreign
keys. If an ordinary table
contains foreign keys or
other tables reference
foreign keys of an
ordinary table, data in
partitions and ordinary
tables cannot be
exchanged. GaussDB
partitioned tables support
foreign keys. If the foreign
key constraints of two
tables are the same, data
in partitions and ordinary
tables can be exchanged.
If a GaussDB partitioned
table does not contain
foreign keys, an ordinary
table is referenced by
other tables, and the
partitioned table is the
same as the ordinary
table, data in the
partitioned table can be
exchanged with that in
the ordinary table.
Modify the partition
key information of a
partitioned table.
ALTER TABLE MySQL allows you to modify
the partition key information
of a partitioned table, but
GaussDB does not.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 654

Description Syntax Dierence
Compatible with the
CREATE TABLE... LIKE
syntax.
CREATE TABLE ... LIKE ● In versions earlier than
MySQL 8.0.16, CHECK
constraints are parsed but
their functions are
ignored. In this case,
CHECK constraints are not
replicated. GaussDB
supports replication of
CHECK constraints.
● When a table is created,
all primary key constraint
names in MySQL are xed
to PRIMARY KEY.
GaussDB does not support
replication of primary key
constraint names.
● When a table is created,
MySQL supports
replication of unique key
constraint names, but
GaussDB does not.
● When a table is created,
MySQL versions earlier
than 8.0.16 do not have
CHECK constraint
information, but GaussDB
supports replication of
CHECK constraint names.
● When a table is created,
MySQL supports
replication of index
names, but GaussDB does
not.
● When a table is created
across sql_mode, MySQL is
controlled by the loose
mode and strict mode.
The strict mode may
become invalid in
GaussDB.
For example, if the source
table has the default value
"0000-00-00", GaussDB
can create a table that
contains the default value
"0000-00-00" in
"no_zero_date" strict
mode, which means that
the strict mode is invalid.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 655

Description Syntax Dierence
MySQL fails to create the
table because it is
controlled by the strict
mode.
Compatible with the
subpartition addition
syntax.
ALTER TABLE [ IF EXISTS ]
{ table_name [*] | ONLY
table_name | ONLY
( table_name )} add_clause;
add_clause:
ADD
{{partition_less_than_item |
partition_start_end_item |
partition_list_item} |
PARTITION({partition_less_than
_item |
partition_start_end_item |
partition_list_item})}
The syntax of the original
partitioned table is retained.
The following syntax cannot
be used to add multiple
partitions:
ALTER TABLE table_name ADD
PARTITION (partition_denition1,
partition_denition1,…);
Only the original syntax for
adding multiple partitions is
supported.
ALTER TABLE table_name ADD
PARTITION (partition_denition1),
ADD PARTITION
(partition_denition2[y1] ), ...;
Compatible with the
TRUNCATE
subpartition syntax.
ALTER TABLE [ IF EXISTS ]
table_name
truncate_clause;
For truncate_clause, the
supported subitems are
dierent:
● M-compatible mode:
TRUNCATE PARTITION { { ALL |
partition_name [, ...] } | FOR
( partition_value [, ...] ) }
[ UPDATE GLOBAL INDEX ]
● MySQL:
TRUNCATE PARTITION
{partition_names | ALL}
Index name of a
primary key
CREATE TABLE table_name
( col_denitine ,PRIMARY KEY
[index_name] [ USING
method ] ( { column_name |
( expression ) }[ ASC | DESC ] }
[, ... ] ) index_parameters
[USING method| COMMENT
'string'])
The index name created after
being specied by a primary
key in GaussDB is the index
name specied by a user. In
MySQL, the index name is
PRIMARY.
Delete dependent
objects.
DROP drop_type name
CASCADE;
In GaussDB, CASCADE needs
to be added to delete
dependent objects. In MySQL,
CASCADE is not required.
The NOT NULL
constraint does not
allow NULL values to
be inserted.
CREATE TABLE t1(id int NOT
NULL DEFAULT 8);
INSERT INTO t1
VALUES(NULL);
INSERT INTO t1 VALUES(1),
(NULL),(2);
In MySQL loose mode, NULL
is converted and data is
successfully inserted. In
MySQL strict mode, NULL
values cannot be inserted.
GaussDB does not support
this feature. NULL values
cannot be inserted in loose
or strict mode.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 656

Description Syntax Dierence
The CHECK constraint
takes eect.
CREATE TABLE The CREATE TABLE that
contains the CHECK
constraint takes eect in
MySQL 8.0. MySQL 5.7 parses
the syntax but the syntax
does not take eect.
GaussDB synchronizes this
function of MySQL 8.0, and
the GaussDB CHECK
constraint can reference
other columns, but MySQL
cannot.
A maximum of 32767 CHECK
constraints can be added to a
table in GaussDB.
The algorithm and
lock options of an
index do not take
eect.
CREATE INDEX ...
DROP INDEX ...
Currently, the index options
algorithm_option and
lock_option in the CREATE/
DROP INDEX statement in
M-compatible mode are
supported only in syntax. No
error is reported during
creation, but they do not
take eect.
The storage of hash
partitions and level-2
partitions in CREATE
TABLE in GaussDB is
dierent from that in
MySQL.
CREATE TABLE In GaussDB, the hash
functions used by hash
partitioned tables and level-2
partitioned tables in the
CREATE TABLE statement are
dierent from those used in
MySQL. Therefore, the
storage of hash partitioned
tables and level-2 partitioned
tables is dierent from that
in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 657

Description Syntax Dierence
Partitioned table
index
CREATE INDEX GaussDB partitioned table
indexes are classied into
local and global indexes. A
local index is bound to a
specic partition, and a
global index corresponds to
the entire partitioned table.
For details about how to
create local and global
indexes and the default rules,
see "SQL Syntax > SQL
Statement > C > CREATE
INDEX " in
Developer Guide
.
For example, if a unique
index is created on a non-
partition key, a global index
is created by default.
MySQL does not have global
indexes. In GaussDB, if the
partitioned table index is a
global index, the global index
is not updated by default
when operations such as
DROP, TRUNCATE, and
EXCHANGE are performed on
table partitions. As a result,
the global index becomes
invalid and cannot be
selected in subsequent
statements. To avoid this
problem, you are advised to
explicitly specify the UPDATE
GLOBAL INDEX clause at the
end of the partition syntax or
set the global GUC
parameter
enable_gpi_auto_update to
true (recommended) so that
global indexes can be
automatically updated during
partition operations.
The escape character
(\) is not supported in
COMMENT.
CREATE TABLE ...
COMMENT 'string'
CREATE
INDEX ...COMMENT
'string'
GaussDB: The escape
character (\) is not supported
in COMMENT.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 658

Description Syntax Dierence
If the table is
partitioned by key in
the CREATE/ALTER
TABLE statement,
algorithms cannot be
specied. Input
parameters of some
partition denition do
not support
expressions.
CREATE TABLE and
ALTER TABLE
GaussDB: If the table is
partitioned by key in the
CREATE/ALTER TABLE
statement, algorithms cannot
be specied.
The syntaxes that do not
support expressions as input
parameters are as follows:
● PARTITION BY HASH()
● PARTITION BY KEY()
● VALUES LESS THAN()
Partitioned tables do
not support
LINEAR/KEY hash.
CREATE TABLE ...
PARTITION ...
GaussDB: Partitioned tables
do not support LINEAR/KEY
hash.
The CHECK and
AUTO_INCREMENT
syntaxes cannot be
used in the same
column.
CREATE TABLE The column using CHECK
does not take eect in
MySQL 5.7. When both
CHECK and
AUTO_INCREMENT are used
on the same column, only
AUTO_INCREMENT takes
eect. However, GaussDB
reports an error.
Delete dependent
tables.
DROP TABLE In GaussDB, CASCADE must
be added to delete
dependent tables. In MySQL,
CASCADE is not required.
SET does not support
FOREIGN_KEY_CHECK
S.
SET Currently, GaussDB does not
support SET
FOREIGN_KEY_CHECKS=0|1.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 659

Description Syntax Dierence
Options related to
table denition.
CREATE TABLE ... and
ALTER TABLE ...
● GaussDB does not support
the following options:
AVG_ROW_LENGTH,
CHECKSUM,
COMPRESSION,
CONNECTION, DATA
DIRECTORY, INDEX
DIRECTORY,
DELAY_KEY_WRITE,
ENCRYPTION,
INSERT_METHOD,
KEY_BLOCK_SIZE,
MAX_ROWS, MIN_ROWS,
PACK_KEYS, PASSWORD,
STATS_AUTO_RECALC,
STATS_PRESISTENT, and
STATS_SAMPLE_PAGES.
● The following options do
not report errors in
GaussDB and do not take
eect: ENGINE and
ROW_FORMAT.
Encrypt the CMKs of
CEKs in round robin
(RR) mode and
encrypt the plaintext
of CEKs.
ALTER COLUMN
ENCRYPTION KEY
The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
The encrypted
equality query feature
adopts a multi-level
encryption model.
The master key
encrypts the column
key, and the column
key encrypts data.
This syntax is used to
create a master key
object.
CREATE CLIENT
MASTER KEY
The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
Create a CEK that can
be used to encrypt a
specied column in a
table.
CREATE COLUMN
ENCRYPTION KEY
The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 660

Description Syntax Dierence
Send keys to the
server for caching.
This function is used
only when the
memory decryption
emergency channel is
enabled. This is a
fully-encrypted
function.
\send_token The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
Send keys to the
server for caching.
This function is used
only when the
memory decryption
emergency channel is
enabled. This is a
fully-encrypted
function.
\st The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
Destroy the keys
cached on the server.
This function is used
only when the
memory decryption
emergency channel is
enabled. This is a
fully-encrypted
function.
\clear_token The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
Destroy the keys
cached on the server.
This function is used
only when the
memory decryption
emergency channel is
enabled. This is a
fully-encrypted
function.
\ct The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
Set the parameters
for accessing the
external key manager
in the fully-encrypted
database features.
\key_info KEY_INFO The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
Enable third-party
dynamic libraries and
set related
parameters. This is a
fully-encrypted
function.
\crypto_module_info
MODULE_INFO
The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 661

Description Syntax Dierence
Enable third-party
dynamic libraries and
set related
parameters. This is a
fully-encrypted
function.
\cmi MODULE_INFO The M-compatible mode
does not support the full
encryption. Therefore, this
syntax is not supported.
The GENERATED
ALWAYS AS
statement cannot
reference columns
generated by
GENERATED ALWAYS
AS.
Generated Always AS In GaussDB, the GENERATED
ALWAYS AS statement
cannot reference columns
generated by GENERATED
ALWAYS AS, but it can in
MySQL.
Currently, ALTER
TABLE does not
support the RENAME
= syntax.
ALTER TABLE In GaussDB, ALTER TABLE
supports only RENAME TO
and RENAME AS syntaxes. In
MySQL, it supports
RENBAME TO, RENAME AS,
and RENAME = syntaxes.
Disable the GUC
parameter
enable_expr_fusion.
SET
enable_expr_fusion=
ON
In M-compatible mode, the
GUC parameter
enable_expr_fusion cannot
be enabled.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 662

Description Syntax Dierence
Compatible with the
CREATE VIEW AS
SELECT syntax.
CREATE VIEW table_name AS
query;
● For the following types,
the query using the
CREATE VIEW view_name
AS query syntax cannot
contain calculation
operations (such as
function call and
calculation using
operators):
– BINARY[(n)]
– BOOLEAN/BOOL
– VARBINARY(n)
– CHAR[(n)]
– VARCHAR(n)
– TIME[(p)]
– DATETIME[(p)]
– TIMESTAMP[(p)]
– BIT[(n)]
– NUMERIC[(p[,s])]
– DECIMAL[(p[,s])]
– DEC[(p[,s])]
– FIXED[(p[,s])]
– FLOAT4[(p, s)]
– FLOAT8[(p,s)]
– FLOAT[(p)]
– REAL[(p, s)]
– FLOAT[(p, s)]
– DOUBLE[(p,s)]
– DOUBLE
PRECISION[(p,s)]
– TEXT
– TINYTEXT
– MEDIUMTEXT
– LONGTEXT
– BLOB
– TINYBLOB
– MEDIUMBLOB
– LONGBLOB
● In the simple query
scenario, an error message
is displayed for the
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 663

Description Syntax Dierence
preceding calculation
operations in M-
compatible mode. For
example:
m_db=# CREATE TABLE TEST
(salary int(10));
CREATE TABLE
m_db=# INSERT INTO TEST
VALUES(8000);
INSERT 0 1
m_db=# CREATE VIEW view1 AS
SELECT salary/10 as te FROM
TEST;
ERROR: Unsupported type
numeric used with expression in
CREATE VIEW statement.
m_db=# CREATE TABLE TEST
(salary int(10));
CREATE TABLE
m_db=# INSERT INTO TEST
VALUES(8000);
INSERT 0 1
m_db=# CREATE VIEW view2 AS
SELECT sec_to_time(salary) as te
FROM TEST;
ERROR: Unsupported type time
used with expression in CREATE
VIEW statement.
● In non-simple query
scenarios such as
composite query and
subquery, the calculation
operations of the
preceding types in M-
compatible mode are
dierent from those in
MySQL. In M-compatible
mode, the data type
column precision attribute
of the created table is not
retained.
Range of index
names that can be
duplicated
CREATE TABLE, CREATE
INDEX
In MySQL, an index name is
unique in a table. Dierent
tables can have the same
index name. In M-compatible
mode, the index name must
be unique in the same
schema. In M-compatible
mode, the same rules apply
to constraints and keys that
automatically create indexes.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 664

Description Syntax Dierence
View dependency
dierences
CREATE VIEW and
ALTER TABLE
In MySQL, view storage
records only the table name,
column name, and database
name of the target table, but
does not record the unique
identier of the target table.
GaussDB parses the SQL
statement used for creating a
view and stores the unique
identier of the target table.
Therefore, the dierences are
as follows:
1. In MySQL, you can modify
the data type of a column
on which a view depends
because the view is
unaware of the
modication of the target
table. In GaussDB, such
modication is forbidden
and the attempt will fail.
2. In MySQL, you can
rename a column on
which a view depends
because the view is
unaware of the
modication of the target
table, but the view cannot
be queried after the
operation. In GaussDB,
each column precisely
stores the unique
identier of the
corresponding table and
column. Therefore, the
column name in the table
can be modied
successfully without
changing the column
name in the view. In
addition, the view can be
queried after the
operation.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 665
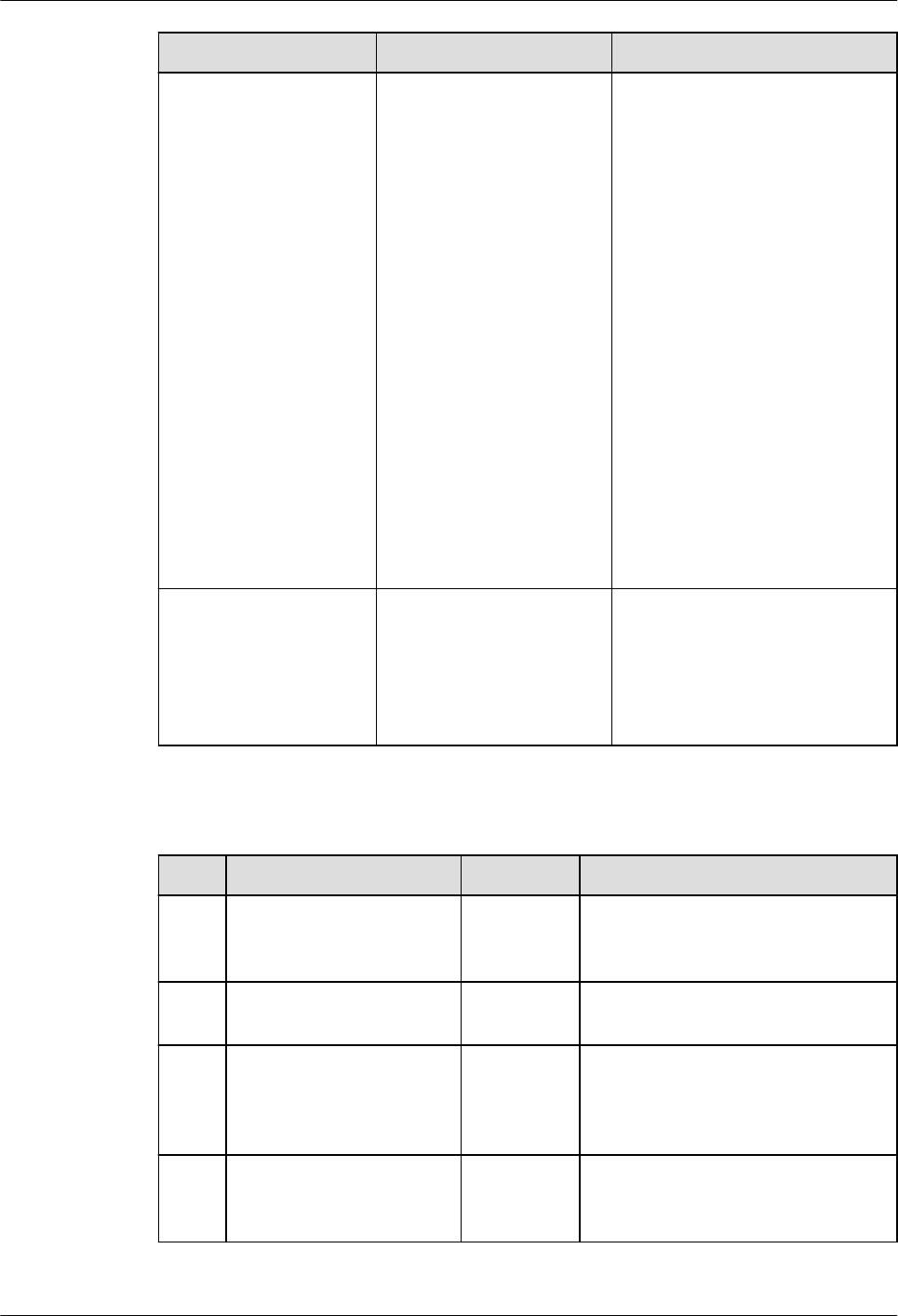
Description Syntax Dierence
Foreign key
dierences
CREATE TABLE GaussDB foreign key
constraints are insensitive to
types. If the data types of the
elds in the main and child
tables are implicitly
converted, foreign keys can
be created. MySQL are
sensitive to foreign key types.
If the column types of the
two tables are dierent,
foreign keys cannot be
created.
MySQL does not allow you to
modify the data type or
name of a table column
where the foreign key of the
column is located by running
MODIFY COLUMN or
CHANGE COLUMN, but
GaussDB supports such
operation.
Dierences
in index
ascending and
descending orders
CREATE INDEX In MySQL 5.7, ASC | DESC is
parsed but ignored, and the
default behavior is ASC. In
MySQL 8.0 and GaussDB,
ASC | DESC is parsed and
takes eect.
8.2.3.8.4 DML
No.
Description Syntax Dierence
1 DELETE supports
deleting data from
multiple tables.
DELETE -
2 DELETE supports
ORDER BY and LIMIT.
DELETE -
3 DELETE supports
deleting data from a
specied partition (or
subpartition).
DELETE -
4 UPDATE supports
updating data from
multiple tables.
UPDATE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 666

No. Description Syntax Dierence
5 UPDATE supports
ORDER BY and LIMIT.
UPDATE -
6 The syntax is
compatible with SELECT
INTO.
SELECT ● In GaussDB, you can use
SELECT INTO to create a table
based on the query result.
MySQL does not support this
function.
● In GaussDB, the SELECT INTO
syntax does not support the
query result that is obtained
after the set operation of
multiple queries is performed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 667

No. Description Syntax Dierence
7 The syntax is
compatible with
REPLACE INTO.
REPLACE ● Dierence between the initial
values of the time type. For
example:
– MySQL is not aected by
the strict or loose mode.
You can insert time 0 into
a table.
mysql> CREATE TABLE test(f1
TIMESTAMP NOT NULL, f2
DATETIME NOT NULL, f3 DATE
NOT NULL);
Query OK, 1 row aected (0.00 sec)
mysql> REPLACE INTO test
VALUES(f1, f2, f3);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT * FROM test;
+---------------------
+---------------------+------------+
| f1 | f2 |
f3 |
+---------------------
+---------------------+------------+
| 0000-00-00 00:00:00 | 0000-00-00
00:00:00 | 0000-00-00 |
+---------------------
+---------------------+------------+
1 row in set (0.00 sec)
– The time 0 can be
successfully inserted only
when GaussDB is in loose
mode.
gaussdb=# SET b_format_version =
'5.7';
SET
gaussdb=# SET
b_format_dev_version = 's1';
SET
gaussdb=# SET sql_mode = '';
SET
gaussdb=# CREATE TABLE test(f1
TIMESTAMP NOT NULL, f2
DATETIME NOT NULL, f3 DATE
NOT NULL);
CREATE TABLE
gaussdb=# REPLACE INTO test
VALUES(f1, f2, f3);
REPLACE 0 1
gaussdb=# SELECT * FROM test;
f1 | f2 | f3
---------------------
+---------------------+------------
0000-00-00 00:00:00 | 0000-00-00
00:00:00 | 0000-00-00
(1 row)
In strict mode, the error is
reported: date/time eld
value out of range:
"0000-00-00 00:00:00".
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 668

No. Description Syntax Dierence
● Dierence between the initial
values of the bit string type.
For example:
– The initial value of the
MySQLBIT type is an
empty string '', and the
length is M/8 (rounded
up), that is:
mysql> CREATE TABLE test(f1
BIT(3) NOT NULL);
Query OK, 0 rows aected (0.01
sec)
mysql> REPLACE INTO test
VALUES(f1);
Query OK, 1 row aected (0.00 sec)
mysql> SELECT f1, length(f1)
FROM test;
+----+------------+
| f1 | length(f1) |
+----+------------+
| | 1 |
+----+------------+
1 row in set (0.00 sec)
– In GaussDB, if the initial
value of the BIT type is an
empty string '' and the
length is 0, an error is
reported.
gaussdb=# CREATE TABLE test(f1
BIT(3) NOT NULL);
CREATE TABLE
gaussdb=# REPLACE INTO test
VALUES(f1);
REPLACE 0 1
gaussdb=#
SELECT f1, length(f1) FROM test;
+----+------------+
| f1 | length(f1) |
+----+------------+
| | 0 |
+----+------------+
(1 row)
8
SELECT supports multi-
partition query.
SELECT -
9 UPDATE supports
multi-partition update.
UPDATE -
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 669

No. Description Syntax Dierence
10 Import data by using
LOAD DATA.
LOAD
DATA
When LOAD DATA is used to
import data, GaussDB diers
from MySQL in the following
aspects:
● The execution result of the
LOAD DATA syntax is the
same as that in M* strict
mode. The loose mode is not
adapted currently.
● The IGNORE and LOCAL
parameters are used only to
ignore the conicting rows
when the imported data
conicts with the data in the
table and to automatically ll
default values for other
columns when the number of
columns in the le is less than
that in the table. Other
functions are not supported
currently.
● If the keyword LOCAL is
specied and the le path is a
relative path, the le is
searched from the binary
directory. If the keyword
LOCAL is not specied and
the le path is a relative path,
the le is searched from the
data directory.
● If single quotation marks are
specied as separators,
escape characters, and line
breaks in the syntax, lexical
parsing errors occur.
● The [(col_name_or_user_var
[, col_name_or_user_var]...)]
parameter cannot be used to
specify a column repeatedly.
● The newline character
specied by [FIELDS
TERMINATED BY 'string']
cannot be the same as the
separator specied by [LINES
TERMINATED BY'string'].
● If the data written to a table
by running LOAD DATA
cannot be converted to the
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 670
No. Description Syntax Dierence
data type of the table, an
error is reported.
● The LOAD DATA SET
expression does not support
the calculation of a specied
column name.
● If there is no implicit
conversion function between
the return value type of the
SET expression and the
corresponding column type,
an error is reported.
● LOAD DATA applies only to
tables but not views.
● The default newline character
of the le in Windows is
dierent from that in Linux.
LOAD DATA cannot identify
this scenario and reports an
error. You are advised to
check the newline character
at the end of lines of the le
to be imported.
11
INSERT supports the
VALUES reference
column syntax.
INSERT
INTO
tabname
VALUES(1,
2,3) ON
DUPLICAT
E KEY
UPDATE b
=
VALUES(co
lumn_nam
e)
The format of
table-
name
.
column-name
is not
supported by VALUES() in the
ON DUPLICATE KEY UPDATE
clause in GaussDB, but is
supported in MySQL.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 671
No. Description Syntax Dierence
12 LIMIT dierences DELETE,
SELECT,
and
UPDATE
The LIMIT clauses of each
statement in GaussDB are
dierent from those in MySQL.
The maximum parameter value
of LIMIT (of the BIG INT type) in
GaussDB is
9223372036854775807. If the
actual value exceeds the number,
an error is reported. In MySQL,
the maximum value of LIMIT (of
the unsigned LONGLONG type)
is 18446744073709551615. If
the actual value exceeds the
number, an error is reported.
You can set a small value in
LIMIT, which is rounded o
during execution. The value
cannot be a decimal in MySQL.
In a DELETE statement, GaussDB
does not allow limit to be 0,
while MySQL allows limit to be
0.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 672

No. Description Syntax Dierence
13 Dierence in using
backslashes (\)
INSERT The usage of backslashes (\) can
be determined by parameters in
GaussDB and MySQL, but their
default usages are dierent.
In MySQL, the
NO_BACKSLASH_ESCAPES
parameter is used to determine
whether backslashes (\) in
character strings and identiers
are parsed as common
characters or escape characters.
By default, backslashes (\) are
parsed as escape characters in
character strings and identiers.
If set sql_mode is set to
'NO_BACKSLASH_ESCAPES',
backslashes (\) cannot be parsed
as escape characters in character
strings and identiers.
In GaussDB, the
standard_conforming_strings
parameter is used to determine
whether backslashes (\) in
character strings and identiers
are parsed as common
characters or escape characters.
The default value is on,
indicating that backslashes (\)
are parsed as common text in
common character string texts
according to the SQL standard. If
set
standard_conforming_strings is
set to o, backslashes (\) can be
parsed as escape characters in
character strings and identiers.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 673
No. Description Syntax Dierence
14 If the inserted value is
less than the number of
columns, MySQL
reports an error while
GaussDB supplements
null values.
INSERT In GaussDB, if the column list is
not specied and the inserted
value is less than the number of
columns, values are assigned
based on the column sequence
when the table is created by
default. If a column has a non-
null constraint, an error is
reported. If no non-null
constraint exists and a default
value is specied, the default
value is added to the column. If
no default value is specied, null
is added.
15 The columns sorted in
ORDER BY must be
included in the columns
of the result set.
SELECT In GaussDB, when used with the
GROUP BY clause, the columns
to be sorted in ORDER BY must
be included in the columns of
the result set retrieved by the
SELECT statement. When used
with the DISTINCT keyword, the
columns to be sorted in ORDER
BY must be included in the
columns of the result set
retrieved by the SELECT
statement.
16 Do not use ON
DUPLICATE KEY
UPDATE to modify
constraint columns.
INSERT -
17 Duplicate column
names are allowed in
the SELECT result.
SELECT -
18 NATURAL JOIN in
GaussDB is dierent
from that in MySQL.
SELECT In GaussDB, NATURAL [ [LEFT |
RIGHT] OUTER] JOIN allows you
not to specify LEFT | RIGHT. If
LEFT | RIGHT is not specied,
NATURAL OUTER JOIN is
NATURAL JOIN. You can use
JOIN consecutively.
19 If the foreign key data
type is timestamp or
datetime, an error is
reported for attempts
to update or delete the
foreign table.
UPDATE/
DELETE
If the foreign key data type is
timestamp or datetime, an error
is reported for attempts to
update or delete the foreign
table, but in MySQL the table
can be updated or deleted.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 674

No. Description Syntax Dierence
20 Compatibility in terms
of nature join and using
SELECT ● In GaussDB, join sequence is
strictly from left to right.
MySQL may adjust the
sequence.
● In GaussDB and MySQL,
columns involving join in the
left or right table cannot be
ambiguous during natural join
or using. (Generally,
ambiguity is caused by
duplicate names of columns
in the left or right temporary
table.) The join sequence
diers in two databases,
which may lead to dierent
behaviors.
– Behavior in GaussDB:
m_regression=# CREATE TABLE
t1(a int,b int);
CREATE TABLE
m_regression=# CREATE TABLE
t2(a int,b int);
CREATE TABLE
m_regression=# CREATE TABLE
t3(a int,b int);
CREATE TABLE
m_regression=# SELECT * FROM t1
JOIN t2;
a | b | a | b
---+---+---+---
(0 rows)
m_regression=# SELECT * FROM t1
JOIN t2 natural join t3; -- Failed.
Duplicate contents exist in
columns a and b of the temporary
table obtained by t1 join t2.
Therefore, there is ambiguity in
nature join.
ERROR: common column name
"a" appears more than once in left
table
– Behavior in MySQL:
mysql> SELECT * FROM t1 JOIN t2
NATURAL JOIN t3;
Empty set (0.00 sec)
mysql> SELECT * FROM (t1 join t2)
NATURAL JOIN t3;
ERROR 1052 (23000): Column 'a'
in from clause is ambiguous
21
The WITH clause is
compatible with MySQL
8.0.
SELECT,
INSERT,
UPDATE,
and
DELETE
-
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 675

No. Description Syntax Dierence
22 Compatibility in terms
of join
SELECT Commas (,) cannot be used as a
way of join in GaussDB, but can
be used in MySQL.
GaussDB does not support use
index for join.
23 If the column
expression in the
SELECT statement is a
function expression or
arithmetic expression,
the column name in the
query result is ?
column?.
SELECT In GaussDB, if the column
expression in the SELECT
statement is a function
expression or arithmetic
expression, the column name in
the query result is ?column?. In
MySQL, the name is the
corresponding expression.
24 SELECT export le (into
outle)
SELECT ...
INTO
OUFILE ...
In the le exported by using the
SELECT INTO OUTFILE syntax,
the display precision of values of
the FLOAT, DOUBLE, and REAL
types in GaussDB is dierent
from that in MySQL. The syntax
does not aect the import using
COPY the values after import.
25 UPDATE/INSERT/
REPLACE ... SET
species the schema
name and table name.
UPDATE/
INSERT/
REPLACE ...
SET
The three-segment format for
UPDATE/REPLACE SET is
database.table.column in
MySQL, and is table.column.led
in GaussDB, where led indicates
the attribute in the specied
composite type.
For INSERT ... SET, MySQL
supports column, table.column,
and database.table.column.
GaussDB supports only column
and does not support
table.column and
database.table.column.
26 The execution sequence
of UPDATE SET is
dierent from that of
MySQL.
UPDATE ...
SET
In MySQL, UPDATE SET is
performed in sequence. The
results of UPDATE at the front
aect subsequent results of
UPDATE, and the same column
can be set for multiple times. In
GaussDB, all related data is
obtained rst, and then UPDATE
is performed on the data at a
time. The same column cannot
be set for multiple times.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 676

No. Description Syntax Dierence
27 IGNORE feature INSERT The execution process in MySQL
is dierent from that in
GaussDB. Therefore, the number
and information of generated
warnings may be dierent.
28 HAVING syntax SELECT In GaussDB, HAVING can only
reference columns in the GROUP
BY clause or columns used by
aggregate functions. However,
MySQL supports more: it allows
HAVING to reference SELECT
columns in the list and columns
in external subqueries.
8.2.3.8.5 DCL
No. Description Syntax Dierence
1 Set names with
COLLATE specied.
SET [ SESSION |
LOCAL ] NAMES
{'charset_name'
[COLLATE
'collation_name'] |
DEFAULT};
GaussDB does not allow
charset_name to be
dierent from the
database character set.
For details, see "SQL
Reference > SQL Syntax >
SQL Statements > S >
SET" in the
M-compatible
Development Guide
.
8.2.3.8.6 Other Statements
No.
Description Syntax Dierence
1 Transaction-
related
syntax
Default
database
isolation level
The default isolation level of M-
compatible mode is READ COMMITTED,
and that of MySQL is REPEATABLE
READ.
Only the READ COMMITTED and
REPEATABLE READ isolation levels take
eect in M-compatible databases.
2 Transaction-
related
syntax
Transaction
nesting
In M-compatible mode, nested
transactions are not automatically
committed, but in MySQL, they are
automatically committed.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 677

No. Description Syntax Dierence
3 Transaction-
related
syntax
Autocommit In M-compatible mode, GaussDB is
used for storage and the GaussDB
transaction mechanism is inherited. If
DDL or DCL is executed in a
transaction, the transaction is not
automatically committed. In MySQL, if
DDL, DCL, management-related, or
lock-related statements are executed,
the transaction is automatically
committed.
4 Transaction-
related
syntax
Rollback is
required after
an error is
reported.
If an error is reported for a transaction
in an M-compatible database, rollback
needs to be performed. There is no
such restriction in MySQL.
5 Transaction-
related
syntax
Lock
mechanism
The M-compatible lock mechanism can
be used only in transaction blocks.
There is no such restriction in MySQL.
6 Lock
mechanism
Lock
mechanism
● After the read lock is obtained, write
operations cannot be performed on
the current session in MySQL, but
write operations can be performed
on the current session in an M-
compatible database.
● After MySQL locks a table, an error
is reported when other tables are
read. M-compatible does not have
such restriction.
● In MySQL, if the lock of the same
table is obtained in the same
session, the previous lock is
automatically released and the
transaction is committed. M-
compatible databases do not have
this mechanism.
● M-compatible databases allow LOCK
TABLE to be used only inside a
transaction block, and have no
UNLOCK TABLE command. Locks are
always released at the end of
transactions.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 678

8.2.3.8.7 Users and Permissions
Description
In M-compatible mode, the behaviors and syntaxes related to user and permission
control inherit the GaussDB mechanism but are not synchronized with those in
MySQL.
User and permission behaviors are the same as those in GaussDB. For details, see
"Database Security Management > Managing Users and Their Permissions" in
Developer Guide
.
Some syntaxes for users and permissions are tailored in GaussDB. For details
about the syntaxes, see "SQL Reference > SQL Syntax > SQL Statements" in
M-
Compatibility Developer Guide
. For details about the syntax dierences between
an M-compatible database and GaussDB, see Table 8-73.
When a user is created, a schema with the same name as the user is automatically
created in an M-compatible database, but it is not created in MySQL.
Table 8-73 Syntax dierences between an M-compatible database and GaussDB
No
.
Syntax Description Dierence
1 CREATE ROLE Creates a role. In an M-compatible
database:
Options involving the
following keywords
cannot be specied:
ENCRYPTED,
UNENCRYPTED,
RESOURCE POOL, PERM
SPACE, TEMP SPACE,
and SPILL SPACE.
2 CREATE USER Creates a user.
3 CREATE GROUP Creates a user group.
CREATE GROUP is the
alias of CREATE ROLE
and is not
recommended.
4 ALTER ROLE Modies role attributes.
5 ALTER UER Modies user attributes.
6 ALTER GROUP Modies the attributes
of a user group.
-
7 DROP ROLE Deletes a role. -
8 DROP USER Deletes a user. -
9 DROP GROUP Deletes a user group. -
10 DROP OWNED Deletes the database
objects owned by a
database role.
-
11 REASSIGN OWNED Changes the owner of a
database object.
This syntax is not
supported in an M-
compatible database.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 679

No
.
Syntax Description Dierence
12 GRANT Grants permissions to
roles and users.
In an M-compatible
database, permissions on
objects such as functions,
stored procedures,
tablespaces, and
database links cannot be
granted or revoked.
13 REVOKE Revokes permissions
from one or more roles.
14 ALTER DEFAULT
PRIVILEGES
Sets the permissions that
will be granted to
objects created in the
future. (It does not aect
permissions granted to
existing objects.)
This syntax is not
supported in an M-
compatible database.
Dierences
● Syntax format dierences
For details about the M-compatible permission granting syntaxes, see "SQL
Reference > SQL Syntax > G > GRANT" in
M-Compatibility Developer Guide
.
The permission granting syntax in MySQL is as follows:
-- Global, database-level, table-level, and stored procedure–level permission granting syntax
GRANT
priv_type [(column_list)]
[, priv_type [(column_list)]] ...
ON [object_type] priv_level
TO user [auth_option] [, user [auth_option]] ...
[REQUIRE {NONE | tls_option [[AND] tls_option] ...}]
[WITH {GRANT OPTION | resource_option} ...]
-- Syntax for granting permissions to a user proxy
GRANT PROXY ON user
TO user [, user] ...
[WITH GRANT OPTION]
object_type: {
TABLE
| FUNCTION
| PROCEDURE
}
priv_level: {
*
| *.*
| db_name.*
| db_name.tbl_name
| tbl_name
| db_name.routine_name
}
user:
'user_name'@'host_name'
auth_option: {
IDENTIFIED BY 'auth_string'
| IDENTIFIED WITH auth_plugin
| IDENTIFIED WITH auth_plugin BY 'auth_string'
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 680

| IDENTIFIED WITH auth_plugin AS 'auth_string'
| IDENTIFIED BY PASSWORD 'auth_string'
}
tls_option: {
SSL
| X509
| CIPHER 'cipher'
| ISSUER 'issuer'
| SUBJECT 'subject'
}
resource_option: {
| MAX_QUERIES_PER_HOUR count
| MAX_UPDATES_PER_HOUR count
| MAX_CONNECTIONS_PER_HOUR count
| MAX_USER_CONNECTIONS count
}
● Dierences in types of permissions granted
In MySQL, the following types of permissions can be granted.
Table 8-74 Types of permissions that can be granted in MySQL
Permission Type Denition and Permission Level
ALL [PRIVILEGES] Grants all permissions of a specied
access level, except GRANT OPTION
and PROXY.
ALTER Enables ALTER TABLE. Level: global,
database, and table.
ALTER ROUTINE Allows you to modify or delete
stored procedures. Level: global,
database, and routine.
CREATE Enables database and table creation.
Level: global, database, and table.
CREATE ROUTINE Enables stored procedure creation.
Level: global and database.
CREATE TABLESPACE Allows you to create, modify, or
delete tablespaces or log le groups.
Level: global.
CREATE TEMPORARY TABLES Enables CREATE TEMPORARY
TABLE. Level: global and database.
CREATE USER Enable CREATE USER, DROP USER,
RENAME USER, and REVOKE ALL
PRIVILEGES. Level: global.
CREATE VIEW Allows you to create or modify
views. Level: global, database, and
table.
DELETE Enable DELETE. Level: global,
database, and table.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 681

Permission Type Denition and Permission Level
DROP Allows you to delete databases,
tables, or views. Level: global,
database, and table.
EVENT Enable scheduled tasks. Level: global
and database.
EXECUTE Allows you to execute stored
procedures. Level: global, database,
and stored procedure.
FILE Allows you to enable the server to
read or write les. Level: global.
GRANT OPTION Allows you to grant permissions to
or remove permissions from other
accounts. Level: global, database,
table, stored procedure, and proxy.
INDEX Allows you to create or delete
indexes. Level: global, database, and
table.
INSERT Enables INSERT. Level: global,
database, table, and column.
LOCK TABLES LOCK TABLES is enabled on tables
with the SELECT permission. Level:
global and database.
PROCESS Allows you to view all running
threads through SHOW
PROCESSLIST. Level: global.
PROXY Enables a user proxy. Level: from
user to user.
REFERENCES Enables foreign key creation. Level:
global, database, table, and column.
RELOAD Enables FLUSH. Level: global.
REPLICATION CLIENT Allows you to query the location of
the source server or replica server.
Level: global.
REPLICATION SLAVE Allows replicas to read binary logs
from the source. Level: global.
SELECT Enables SELECT. Level: global,
database, table, and column.
SHOW DATABASES Enables SHOW DATABASES to
display all databases. Level: global.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 682

Permission Type Denition and Permission Level
SHOW VIEW Enables SHOW CREATE VIEW.
Level: global, database, and table.
SHUTDOWN Enables mysqladmin shutdown.
Level: global.
SUPER Enables other management
operations, such as the CHANGE
MASTER TO, KILL, PURGE BINARY
LOGS, SET GLOBAL, and
mysqladmin debug commands.
Level: global.
TRIGGER Enables TRIGGER. Level: global,
database, and table.
UPDATE Enables UPDATE. Level: global,
database, table, and column.
USAGE Equivalent to "no privilege".
M-compatible databases support the following permissions by level:
Table 8-75 Types of permissions that can be granted in M-compatible
databases
Object
Permissions That Can Be Granted
Schema CREATE, USAGE, ALTER, DROP, and
COMMENT
Table and view SELECT, INSERT, UPDATE, DELETE,
TRUNCATE, REFERENCES, TRIGGER,
ALTER, DROP, COMMENT, INDEX,
and VACUUM
Column SELECT, INSERT, UPDATE,
REFERENCES, and COMMENT
Sequence SELECT, USAGE, UPDATE, ALTER,
DROP, and COMMENT
● The schema-level objects to which permissions are granted are represented by
'dbname.*' in MySQL, but '{DATABASE | SCHEMA} dbname' in M-
compatible databases.
● In MySQL, a username consists of two parts:
username
@
hostname
, but a
username is only itself in M-compatible databases.
● MySQL allows you to modify user authentication, secure connection, and
resource parameter attributes (including auth_option, tls_option, and
resource option) with the GRANT syntax. In M-compatible databases,
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 683

permission granting syntax does not support this function, and you need to
use CREATE USER and ALTER USER to set user attributes.
● MySQL supports permission granting with a user proxy. GRANT PROXY ON is
used to manage permissions of users in a unied manner. MySQL 5.7 does
not provide the role mechanism, but MySQL 8.0 and M-compatible databases
provide the role mechanism. If a role can manage and control the permissions
of users in a unied manner, it can replace GRANT PROXY ON.
● M-compatible databases have a concept called public. All users have public
permissions and they can query some system catalogs and system views.
Users can grant or revoke public permissions. In MySQL, newly created users
have only the global usage permission, which is almost low to none. They
have only the permission to connect to the database and query the
information_schema database.
● In M-compatible databases, the owner of an object has all permissions on the
object by default. For security purposes, the owner can discard some
permissions. However, ALTER, DROP, COMMENT, INDEX, VACUUM, and re-
grantable permissions on the object are implicitly inherent permissions of the
owner: MySQL does not have a concept called owner. Even if a user creates a
table, the user cannot perform operations such as IUD on the table without
being granted the corresponding permissions.
● In MySQL, All users have the USAGE permission, which indicates no
permission. When REVOKE or GRANT USAGE is executed, no modication is
performed. In M-compatible databases, the USAGE permission has the
following meanings:
– For schemas, USAGE allows access to objects contained in the schema.
Without this permission, it is still possible to see the object names.
– For sequences, USAGE allows use of the nextval function.
● In M-compatible databases, administrator roles can be set for users, including
system administrator (SYSADMIN), security administrator (CREATEROLE),
audit administrator (AUDITADMIN), monitoring administrator (MONADMIN),
O&M administrator (OPRADMIN), and security policy administrator
(POLADMIN). By default, the system administrator with the SYSADMIN
attribute has the highest permission in the system. After separation of duties
is enabled, the system administrator does not have the CREATEROLE attribute
(security administrator) or the AUDITADMIN attribute (audit administrator).
That is, the system administrator can neither create roles or users, nor view or
maintain database audit logs. In MySQL, administrator roles cannot be set for
users, and there is no design for separation of duties.
● In M-compatible databases, the ANY permission can be granted to a user,
indicating that the user can have the corresponding permission in non-system
mode, including CREATE ANY TABLE, SELECT ANY TABLE, and CREATE ANY
INDEX. In MySQL, ANY permission cannot be granted.
● MySQL provides SHOW GRANTS to query user permissions. In M-compatible
databases, you can run a gsql client meta-command '\l+', '\dn+', or '\dp' to
query permission information, or query related columns in system catalogs
such as pg_namespace, pg_class, and pg_attribute for permission information.
● When a database, table, or column is deleted from MySQL, the related
permission granting information is still retained in the system catalog. If an
object with the same name is created again, the user still has the original
permissions. In M-compatible databases, when a database, table, or column is
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 684

deleted, related permission granting information is deleted. If an object with
the same name is created again, permissions need to be granted again.
● When granting database-level permissions, MySQL supports fuzzy match of
database names using underscores (_) and percent signs (%). However, M-
compatible databases do not support fuzzy match of object names using
special characters such as underscores (_) or percent signs (%), which are
identied as common characters.
● In MySQL, if a user specied in the GRANT statement does not exist, a user
account is created by default (this feature has been removed from MySQL
8.0). In M-compatible databases, permissions cannot be granted to users who
are not created.
8.2.3.8.8 System Catalogs and System Views
No
.
System Catalog or
System View
Column Dierence
1 information_schema.
columns
generation_expression The output of this
column varies due to
dierent string
concatenation logics of
expressions in M-
compatible mode and
MySQL.
2 information_schema.
columns
data_type The output result of this
column in M-compatible
mode, having not been
modied due to the data
type format_type
involved, is dierent from
that in MySQL.
3 information_schema.
columns
column_type The output result of this
column in M-compatible
mode, having not been
modied due to the data
type format_type
involved, is dierent from
that in MySQL.
4 information_schema.
tables
engine This column is not
supported in M-
compatible mode.
5 information_schema.
tables
version This column is not
supported in M-
compatible mode.
6 information_schema.
tables
row_format This column is not
supported in M-
compatible mode.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 685

No
.
System Catalog or
System View
Column Dierence
7 information_schema.
tables
avg_row_length In M-compatible mode,
the result of dividing the
size of the data les by
the number of all tuples
(including live tuples and
dead tuples) is used. If
there is no tuple in the
table, the value is null.
8 information_schema.
tables
max_data_length This column is not
supported in M-
compatible mode.
9 information_schema.
tables
data_free In M-compatible mode, it
indicates the result of
(Number of invalid
tuples/Total number of
tuples) x Data le size. If
there is no tuple in the
table, the value is null.
10 information_schema.
tables
check_time This column is not
supported in M-
compatible mode.
11 information_schema.
tables
create_time In M-compatible mode,
this behavior of column
is dierent from that in
MySQL. When a view is
created in MySQL, this
column is set to null. In
M-compatible mode, the
actual table creation time
is displayed. The value is
null if it is a table or
view provided by the
database.
12 information_schema.
tables
update_time The value is null if it is a
table or view provided by
the M-compatible
database.
13 information_schema.
statistics
collation The value can only be A
or D but not NULL in M-
compatible mode.
14 information_schema.
statistics
packed This column is not
supported in M-
compatible mode.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 686

No
.
System Catalog or
System View
Column Dierence
15 information_schema.
statistics
sub_part This column is not
supported in M-
compatible mode.
16 information_schema.
statistics
comment This column is not
supported in M-
compatible mode.
17 information_schema.
partitions
subpartition_name In M-compatible mode, if
a partition is not a
level-2 partition, the
value is null.
18 information_schema.
partitions
subpartition_ordinal_p
osition
In M-compatible mode, if
a partition is not a
level-2 partition, the
value is null.
19 information_schema.
partitions
partition_method In M-compatible mode:
Partitioning policy. If the
partition is not a level-1
partition, the value is
null.
● 'r': range partition.
● 'l': list partition.
● 'h': hash partition
● 'i': interval partition.
20 information_schema.
partitions
subpartition_method In M-compatible mode:
Level-2 partitioning
policy. If a partition is not
a level-2 partition, the
value is null.
● 'r': range partition.
● 'l': list partition.
● 'h': hash partition
● 'i': interval partition.
21 information_schema.
partitions
partition_description In M-compatible mode,
level-1 partitions and
level-2 partitions are
distinguished.
22 information_schema.
partitions
partition_expression This column is not
supported in M-
compatible mode.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 687

No
.
System Catalog or
System View
Column Dierence
23 information_schema.
partitions
subpartition_expressio
n
This column is not
supported in M-
compatible mode.
24 information_schema.
partitions
data_length This column is not
supported in M-
compatible mode.
25 information_schema.
partitions
max_data_length This column is not
supported in M-
compatible mode.
26 information_schema.
partitions
index_length This column is not
supported in M-
compatible mode.
27 information_schema.
partitions
data_free This column is not
supported in M-
compatible mode.
28 information_schema.
partitions
create_time This column is not
supported in M-
compatible mode.
29 information_schema.
partitions
update_time This column is not
supported in M-
compatible mode.
30 information_schema.
partitions
check_time This column is not
supported in M-
compatible mode.
31 information_schema.
partitions
checksum This column is not
supported in M-
compatible mode.
32 information_schema.
partitions
partition_comment This column is not
supported in M-
compatible mode.
33 information_schema.
partitions
nodegroup This column is not
supported in M-
compatible mode.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 688

NO TE
● The precision range cannot be specied for the command output of the integer type in
a view. For example, the bigint(1) type in MySQL corresponds to the bigint type in M-
compatible mode, and the bigint(21) unsigned type in MySQL corresponds to the bigint
unsigned type in M-compatible mode.
● The int type in MySQL corresponds to the integer type in M-compatible mode.
● M-compatible mode does not support columns of the set and enum types that are
supported in MySQL. This version does not support or display Column_priv column in
the m_schema.columns_priv view, Table_priv,Column_priv column in the
m_schema.tables_priv view, Routine_type,Proc_priv column in the m_schema.procs_priv
view, the type,language,sql_data_access,is_deterministic,security_type,sql_mode
column in the m_schema.proc view, or the type column in the m_schema.func view.
● table_rows, avg_row_length, data_length, data_free, index_length, and cardinality in
information_schema.tables and information_schema.statistics are obtained based on
statistics. Therefore, run ANALYZE to update statistics before viewing them. (If data is
updated in the database, you are advised to delay running ANALYZE.)
● The index columns contained in information_schema.statistics must be complete table
columns in the created indexes. If the index columns are expressions, they are not in this
view.
● table_row and avg_row_length in information_schema.partitions are obtained based
on statistics. Before viewing the value, run ANALYZE to update the statistics. (If data is
updated in the database, you are advised to delay running ANALYZE.)
● In information_schema.partitions, level-1 and level-2 partitions are displayed separately.
● The format of the grantee column supported in MySQL is '
user_name
'@'
host_name
'.
In the M-compatible database, it is the name of the user or role to which the permission
is granted.
● For the host column supported in the M-compatible database, the hostname of the
current node is returned.
● In MySQL, you need the permission before viewing m_schema.tables_priv,
information_schema.user_privileges, information_schema.schema_privileges,
information_schema.table_privileges, information_schema.column_privileges,
m_schema.columns_priv, m_schema.func, and m_schema.procs_priv. In the M-
compatible database, you can view them with the default permission. For example, for
table t1, you need the corresponding permission in MySQL so that you can view the
corresponding permission information in the permission view. In the M-compatible
database, you can view the permission information related to table t1 in the view.
GaussDB
Service Overview 8 Compatibility with MySQL Databases
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 689

9 Security
9.1 Shared Responsibilities
Huawei guarantees that its commitment to cyber security will never be
outweighed by the consideration of commercial interests. To cope with emerging
cloud security challenges and pervasive cloud security threats and attacks, Huawei
Cloud builds a comprehensive cloud service security assurance system for dierent
regions and industries based on Huawei's unique software and hardware
advantages, laws, regulations, industry standards, and security ecosystem.
Figure 9-1 illustrates the responsibilities shared by Huawei Cloud and users.
● Huawei Cloud: Ensure the security of cloud services and provide secure
clouds. Huawei Cloud's security responsibilities include ensuring the security
of our IaaS, PaaS, and SaaS services, as well as the physical environments of
the Huawei Cloud data centers where our IaaS, PaaS, and SaaS services
operate. Huawei Cloud is responsible for not only the security functions and
performance of our infrastructure, cloud services, and technologies, but also
for the overall cloud O&M security and, in the broader sense, the security and
compliance of our infrastructure and services.
● Tenant: Use the cloud securely. Tenants of Huawei Cloud are responsible for
the secure and eective management of the tenant-customized
congurations of cloud services including IaaS, PaaS, and SaaS. This includes
but is not limited to virtual networks, the OS of virtual machine hosts and
guests, virtual rewalls, API Gateway, advanced security services, all types of
cloud services, tenant data, identity accounts, and key management.
Huawei Cloud Security White Paper elaborates on the ideas and measures for
building Huawei Cloud security, including cloud security strategies, the shared
responsibility model, compliance and privacy, security organizations and
personnel, infrastructure security, tenant service and security, engineering security,
O&M security, and ecosystem security.
GaussDB
Service Overview 9 Security
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 690
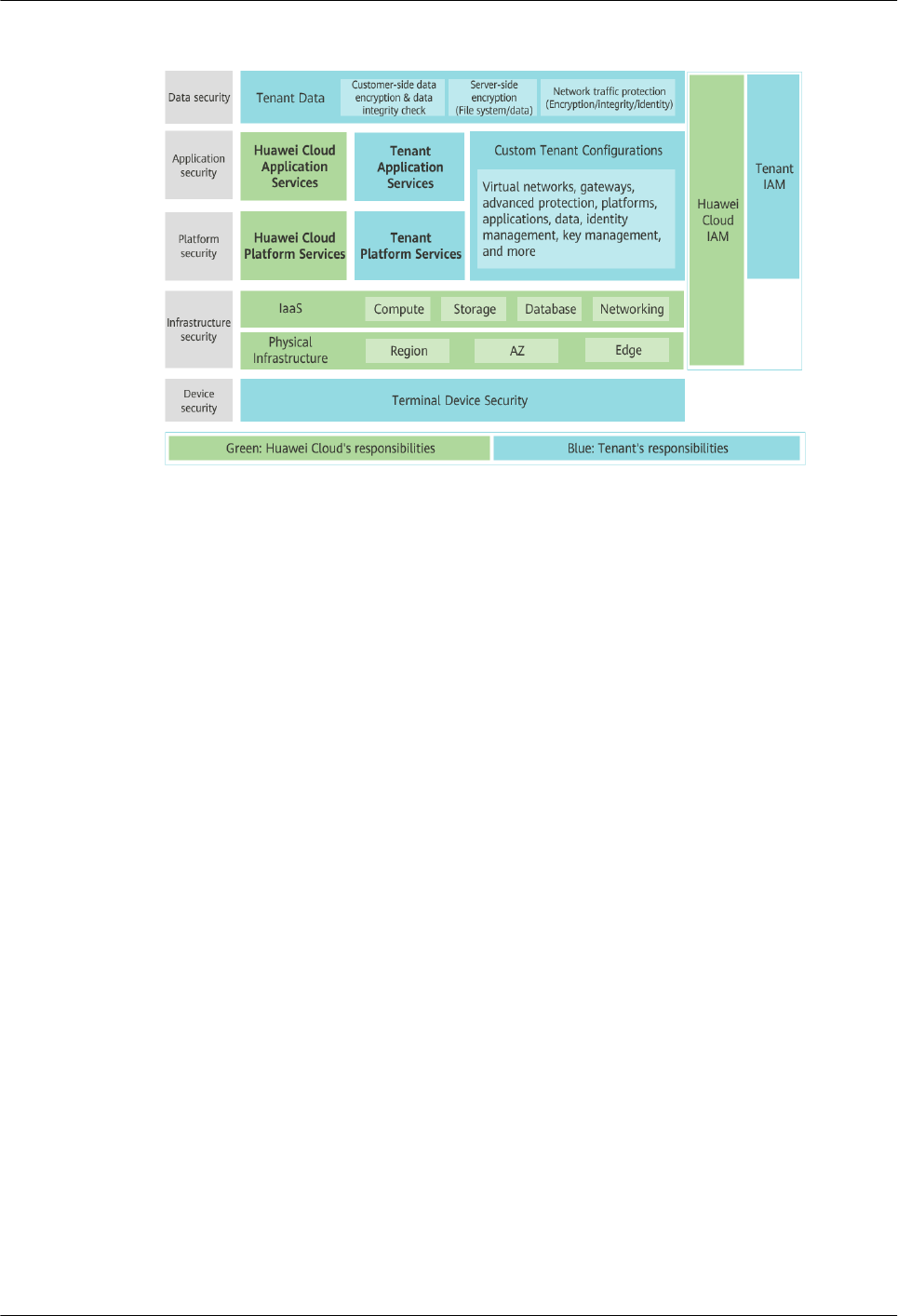
Figure 9-1 Huawei Cloud shared security responsibility model
9.2 Identity Authentication and Access Control
9.2.1 Service Access Control
Identity Authentication
When you access GaussDB, the system authenticates your identity using password
and IAM authentication.
● Password verication
To manage your instance, you need to use Data Admin Service (DAS) to log in
to your instance. The login is successful only after your account and password
are veried.
● IAM verication
You can use Identity and Access Management (IAM) to provide ne-grained
control of GaussDB permissions. IAM provides identity authentication,
permissions management, and access control, helping you to securely access
your Huawei Cloud resources. IAM users can use GaussDB resources only after
their accounts and passwords are veried. For details, see Step 2: Create IAM
Users and Log In.
Access Control
● Permissions control
If you need to assign dierent permissions to dierent employees in your
enterprise to access your DB instance resources, IAM is a good choice. For
details, see Permissions Management.
● VPCs and subnets
A VPC is a logically isolated, congurable, and manageable virtual network. It
helps improve the security of cloud resources and simplies network
GaussDB
Service Overview 9 Security
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 691

deployment. You can dene security groups, virtual private networks (VPNs),
IP address segments, and bandwidth for a VPC. This facilitates internal
network conguration and management and allows you to change your
network in a secure and convenient network manner.
A subnet provides dedicated network resources that are logically isolated from
other networks for security.
For details, see Creating a VPC.
● Security groups
A security group is a logical group that provides access control policies for the
GaussDB instances that have the same security requirements and are
mutually trusted in a VPC. To ensure database security and reliability, you
need to congure security group rules to allow only specic IP addresses and
ports to access your GaussDB instances.
For details, see Conguring Security Group Rules.
9.3 Data Protection
GaussDB provides a series of methods and features to ensure data security and
reliability.
Table 9-1 Methods for data security
Method
Description Reference
Transmission
encryption
(HTTPS)
HTTP and HTTPS are both supported, but
HTTPS is recommended for enhanced
security.
Making an API
Request
Data backup You can back up and restore databases to
ensure data reliability.
Working with
Backups
Critical
operation
protection
With this function enabled, the system
authenticates user's identity when they
perform any risky operations like deleting
an instance. This enhances the protection
for your data and conguration.
Introduction to
Sensitive
Operation
Protection
SSL You can use SSL to encrypt the connection
between GaussDB and the client. It
ensures the privacy, authentication, and
integrity of Internet communications.
SSL Connection
GaussDB
Service Overview 9 Security
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 692

9.4 Audit and Logs
Audit
Cloud Trace Service (CTS) records operations on the cloud resources in your
account. You can use the logs generated by CTS to perform security analysis, track
resource changes, audit compliance, and locate faults.
For details about how to enable and congure CTS, see Enabling CTS.
With CTS, you can record operations associated with GaussDB for future query,
audit, and backtracking. For details, see Key Operations Supported by CTS.
Logs
GaussDB provides a variety of log types and functions for database analysis or
audit. You can download logs on the management console.
● Error logs
GaussDB allows you to download error logs. Error logs are generated when
the database is running. These logs can help you analyze problems with the
database. For details about error logs, see Error Logs.
● Slow query logs
You can download slow query logs to locate slow SQL statement execution
problems and tune the database accordingly. For details about slow query
logs, see Slow Query Logs.
9.5 Risk Monitoring
Cloud Eye is a comprehensive monitoring platform for resources like cloud
databases and cloud servers. It enables you to monitor resources, congure alarm
rules, identify resource exceptions, and quickly respond to resource changes.
Introducing Metrics
You can monitor resources and operations, such as CPU usage and network
throughput using Cloud Eye. For details about supported monitoring metrics and
how to create alarm rules, see Monitoring Metrics.
The monitoring interval can be 1 minute, or 10 seconds. The default monitoring
interval is 1 minute. To improve the accuracy of monitoring metrics, you can
enable Monitoring by Seconds.
Event Monitoring
Event monitoring provides reporting, query, and alarm functions for event data.
You can create alarm rules for both system events and custom events. When
specic events occur, Cloud Eye generates alarms for you.
GaussDB
Service Overview 9 Security
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 693

9.6 Fault Recovery
Automated backups are created during the backup time window of your GaussDB
instances. GaussDB saves automated backups based on the retention period (1 to
732 days) you specied. For details, see Conguring an Automated Backup
Policy.
Based on your service requirements, you can:
● Restore data to the original instance, a new instance or an existing
instance.
● Restoring a DB Instance to a Specic Point in Time.
Multiple-AZ Deployment
An AZ is a physical region where resources have their own independent power
supply and networks. AZs are physically isolated but interconnected through an
internal network. GaussDB supports multiple-AZ deployment for cross-AZ DR.
Failover
There is one shard for a primary/standby instance and multiple shards for a
distributed instance. Each shard consists of one primary DN and multiple standby
DNs. If the primary DN becomes unavailable, GaussDB automatically fails over to
a standby DN.
9.7 Certicates
Compliance Certicates
Huawei Cloud services and platforms have obtained various security and
compliance certications from authoritative organizations, such as International
Organization for Standardization (ISO), system and organization controls (SOC),
and Payment card industry (PCI) compliance standards. These certications are
available for download.
Figure 9-2 Downloading compliance certicates
GaussDB
Service Overview 9 Security
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 694

10 Permissions Management
If you need to assign dierent permissions to employees in your company to
access your GaussDB resources, IAM is a good choice for ne-grained permissions
management. IAM provides identity authentication, permissions management,
and access control, helping you securely manage access to your resources.
If your account does not need individual IAM users for permissions management,
you can skip this section.
With IAM, you can use your account to create IAM users for your employees, and
assign specic permissions to dierent users to control their access to specic
resource types. For example, you can grant software developers in your company
permissions to use GaussDB resources but not the permissions needed to delete
them or perform any high-risk operations.
IAM can be used for free. You pay only for the resources in your account. For more
information about IAM, see IAM Service Overview.
GaussDB Permissions
By default, new IAM users do not have any permissions assigned. You need to add
a user to one or more groups, and attach permission policies or roles to these
groups. Users inherit permissions from the groups to which they are added and
can perform specied operations on cloud services.
GaussDB is a project-level service deployed for specic regions. To assign GaussDB
permissions to a user group, specify the scope as region-specic projects and
select the project for the permissions to take eect. If All projects is selected, the
permissions will be granted to the user group in all region-specic projects. When
accessing GaussDB, the users need to switch to the authorized region.
You can use roles and policies to manage user permissions.
● Roles: A coarse-grained way of granting permissions related to users
responsibilities. Only a limited number of service-level roles for authorization
are available. When using roles to grant permissions, you may need to assign
additional roles because of the dierent dependencies involved with role-
based permissions. Roles are not ideal for ne-grained authorization and
secure access control.
● Policies: A more ne-grained system. Policies let you dene permissions
required to perform operations on specic cloud resources under certain
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 696

conditions. This mechanism allows for more exible policy-based
authorization, meeting requirements for secure access control. For example,
you can grant IAM users only the permissions needed to manage a certain
type of GaussDB resources. Most policies dene permissions based on APIs.
Table 10-1 lists all the system-dened policies supported by GaussDB.
Table 10-1 System-dened permissions for GaussDB
Policy Name Description Category
GaussDB FullAccess Full permissions for
GaussDB
System-dened policy
GaussDB
ReadOnlyAccess
Read-only permissions
for GaussDB
System-dened policy
Table 10-2 lists the common operations supported by each system policy of
GaussDB. Choose appropriate system policies based on this table.
Table 10-2 Common operations supported by the GaussDB system policies
Operation
GaussDB FullAccess GaussDB ReadOnlyAccess
Creating a
GaussDB instance
√ x
Deleting a
GaussDB instance
√ x
Querying GaussDB
instances
√ √
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 697

Table 10-3 Common operations and supported actions
Operation Action Remarks
Creating a DB
instance
gaussdb:instance:create
gaussdb:param:list
To select a VPC,
subnet, and security
group, congure the
following actions:
vpc:vpcs:list
vpc:vpcs:get
vpc:subnets:get
vpc:securityGroups:get
To create a yearly/
monthly instance,
congure the following
actions:
bss:order:update
bss:order:view
bss:balance:view
To create an encrypted
instance, congure the
following actions for
the project:
kms:cmk:get
kms:cmk:list
To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Changing CPU and
memory
specications of an
instance
gaussdb:instance:modifySpec To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Adding nodes gaussdb:instance:modifySpec To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 698

Operation Action Remarks
Scaling up storage
space
gaussdb:instance:modifySpec To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Rebooting a DB
instance
gaussdb:instance:restart To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Deleting a DB
instance
gaussdb:instance:delete To unsubscribe from a
yearly/monthly
instance, congure the
following actions:
"bss:unsubscribe:updat
e"
To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Querying instances gaussdb:instance:list None
Querying instance
details
gaussdb:instance:list If the VPC, subnet, and
security group are
displayed in the
instance list, congure
vpc:*:get and vpc:*:list.
If the used disk is
displayed, congure
ces:*:list.
Changing a DB
instance password
gaussdb:instance:modify To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Changing a DB
instance name
gaussdb:instance:modify None
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 699

Operation Action Remarks
Binding or unbinding
an EIP
gaussdb:instance:modify To display EIPs on the
console, congure the
following actions:
vpc:publicIps:get
vpc:publicIps:list
To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Creating a parameter
template
gaussdb:param:create
gaussdb:param:list
None
Modifying a
parameter template
gaussdb:param:modify None
Obtaining parameter
templates
gaussdb:param:list None
Applying a
parameter template
gaussdb:param:apply To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create
Deleting a parameter
template
gaussdb:param:delete None
Creating a manual
backup
gaussdb:backup:create To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
Obtaining backups gaussdb:backup:list None
Modifying the
backup policy
gaussdb:instance:modifyBacku
pPolicy
None
Deleting a manual
backup
gaussdb:backup:delete To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create"
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 700

Operation Action Remarks
Restoring data to a
new DB instance
gaussdb:instance:create To select a VPC,
subnet, and security
group, congure the
following actions:
vpc:vpcs:list
vpc:vpcs:get
vpc:subnets:get
vpc:securityGroups:get
To report event
monitoring of a failed
operation, congure
the following actions:
"ces:alarmsOnO:put"
"ces:alarms:create
Querying project
tags
gaussdb:tag:list None
Adding or deleting
project tags in
batches
gaussdb:instance:dealTag None
Modifying quotas gaussdb:quota:modify None
Querying predened
tags
gaussdb:instance:list To query predened
tags, congure the
following action:
tms:resourceTags:list
Querying congured
log groups
- To query congured
log groups, congure
the following action:
lts:groups:get
Querying congured
log streams
- To query congured
log streams, congure
the following action:
lts:topics:get
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 701
Operation Action Remarks
Enabling autoscaling gaussdb:instance:autoEnlargeP
olicy
To enable autoscaling,
congure the following
actions for the IAM
users instead of your
Huawei account:
● iam:agencies:listAge
ncies
● iam:agencies:create
Agency
● iam:permissions:list
RolesForAgencyOn-
Project
● iam:permissions:gra
ntRoleToGroupOn-
Project
● iam:roles:listRoles
Performing DBMind-
related operations
gaussdb:instance:sqlCollect
gaussdb:instance:sqlDiagnosis
gaussdb:instance:riskAnalysis
gaussdb:instance:indexAdvise
gaussdb:instance:sqlCo
llect (SQL data
collection)
gaussdb:instance:sqlDi
agnosis (Slow query
diagnosis)
gaussdb:instance:riskA
nalysis (Risk
prediction)
gaussdb:instance:index
Advise (Index
recommendations)
GaussDB
Service Overview 10 Permissions Management
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 702

11 GaussDB Constraints
To ensure the stability and security of GaussDB, certain constraints are put in place
for access or permissions control. Table 11-1 describes such constraints.
There is no SLA commitment, so GaussDB single-replica instances cannot be used
in production environments. For function constraints of single-replicas, see Table
11-2.
Table 11-1 Function constraints
Function
Constraints
Database access ● To access a GaussDB instance that is not publicly
accessible, the instance must be in the same VPC
subnet as the ECSs associated with the instance.
● The ECSs must be allowed by the security group to
access the GaussDB instance.
If a GaussDB instance and the ECSs belong to
dierent security groups, no communication between
them is established by default. To allow it, you must
add an inbound rule to the GaussDB security group.
● The default port number of the GaussDB instance is
8000.
● The database port can be set when a DB instance is
created and can be changed after the DB instance is
created.
Deployment ECSs where DB instances are deployed are not directly
visible to you. You can only access the DB instances
through IP addresses and database ports.
GaussDB
Service Overview 11 GaussDB Constraints
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 703

Function Constraints
Database root
permissions
Only the root user permissions are available on the
instance creation page.
NOTE
After August 30, 2022, the root user of newly created instances
and upgraded existing instances has the sysadmin permission.
To upgrade your existing instance, contact technical support.
If your existing instances are not upgraded, the root user only
has the following permissions: createrole, createdb, and
monadmin. The root user has fewer permissions than the
administrator. When some SQL syntax or functions, such as
create tablespace, are executed, an error message is displayed,
indicating that the permissions are insucient.
GaussDB instance
reboot
GaussDB DB instances cannot be rebooted through
commands. They must be rebooted on the management
console.
GaussDB backup les GaussDB backup les are stored in OBS buckets and are
not visible to you.
Specication changes ● By default, the specications cannot be reduced. If
you need to reduce the specications, contact
Huawei Cloud technical support.
● Before you change the instance specications, ensure
that the instance is available. If the instance or node
is abnormal, or the storage space is full, you cannot
perform this operation.
● During the specication change for HA (1 primary +
2 standby) instances, a primary/standby failover is
triggered. During the failover, services are interrupted
for about 1 minute.
● For a single-replica instance, changing instance
specications will reboot the instance and interrupt
services for 5 to 10 minutes.
● Changing the CPU and memory specications will
cause the instance to reboot, services will be
temporarily interrupted during the reboot.
Failover For primary/standby instances, services are unavailable
for about 10 seconds when the primary node is being
switched to the standby node.
Data restoration To prevent data loss, you are advised to back up key
data before data restoration.
Storage space If the storage space of an instance is full, data cannot
be written to databases. You are advised to periodically
check the storage space.
Performance tuning Performance tuning may need to reboot the instance
and interrupt services.
GaussDB
Service Overview 11 GaussDB Constraints
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 704

Table 11-2 Function constraints of single-replica primary/standby instances
Function Supported by
Versions
Earlier Than
3.0
Supported by 3.0 and Later
Creating an
instance
Yes Yes
Restarting a
DB instance
Yes Yes
Modifying
parameters
Yes Yes
Applying
parameters
Yes Yes
Resetting a
password
Yes Yes
Creating a
full backup
No Yes
Creating a
dierential
backup
No Yes
Deleting a
backup
No Yes
Modifying
the backup
policy
No Yes
Restoring
data to the
original
instance
No Yes
Restoring
data to a
new
instance
No Yes
Restoring
data to an
existing
instance
No Yes
Scaling up
storage
Yes Yes
GaussDB
Service Overview 11 GaussDB Constraints
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 705

Function Supported by
Versions
Earlier Than
3.0
Supported by 3.0 and Later
Changing
CPU and
memory
specicatio
ns of an
instance
Yes Yes
Hot patch
upgrade
No Yes
In-place
upgrade
Yes (The
version can be
upgraded only
to 3.0 or
later.)
Yes
Gray
upgrade
No Yes (only supported in version 3.207 or later)
Viewing
monitoring
metrics
Yes Yes
Deleting an
instance
Yes Yes
Rebuilding
a deleted
instance
No Yes
Querying
the disk
usage
Yes Yes
Creating a
database
Yes Yes
Querying a
database
Yes Yes
Creating a
schema and
user
Yes Yes
Deleting a
schema and
user
Yes Yes
Performing
database
operations
Yes Yes
GaussDB
Service Overview 11 GaussDB Constraints
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 706

12 Billing
Currently, GaussDB supports pay-per-use and yearly/monthly billing.
Billing Items
You are billed for GaussDB DB instances, database storage, and backup storage
(optional).
Table 12-1 GaussDB billing items
Item
Billing Method
DB instance Yearly/monthly and pay-per-use
Database
storage
Yearly/monthly and pay-per-use
Backup storage
(optional)
GaussDB provides backup storage up to 100% of your
provisioned database storage at no additional charge. If
more backup storage is required, tiered pricing starts.
Public network
trac
GaussDB instances are accessible from both private and
public networks. Only the trac from public networks is
billed.
For pricing details, see Product Pricing Details. You can use the price calculator to
estimate the cost for your GaussDB usage.
Billing Modes
GaussDB provides the following two billing modes:
● Yearly/Monthly: Provides a larger discount than pay-per-use billing and is
recommended for long-term use.
● Pay-per-use (hourly): You can start and stop instances as needed and will be
billed based on the duration of your use of instances. Billing starts when your
instance is created and ends when your instance is deleted. Pricing is listed on
a per-hour basis, but bills are calculated based on the actual usage duration.
GaussDB
Service Overview 12 Billing
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 707

Specication Changes
● Changing GaussDB instance specications: You can change GaussDB instance
specications as required. After the change, you are charged based on the
new instance specications.
● Scaling up storage space: You can change the storage space as required. After
scaling the storage space, you are charged based on the new storage space.
Storage space can only be scaled up. The storage space must be a multiple of
(Number of shards x 40 GB).
Renewing a DB Instance
Currently, GaussDB supports pay-per-use and yearly/monthly billing. You can
congure instance specications and storage space based on your service
requirements.
● Pay-per-use: Pricing is listed on a per-hour basis, but bills are calculated based
on the actual usage duration. If your account balance is not paid in a timely
manner, your account will be in arrears.
● Yearly/monthly: An upfront payment is required when you purchase the
service. No additional fees are incurred as you use the service.
Expiration and Overdue Payment
● Service Expiration
Service expiration is only for DB instances billed on a yearly/monthly basis.
After a yearly/monthly DB instance expires, you can neither perform any
operations on the management console nor invoke related APIs. Automatic
monitoring, alarm reporting and other O&M operations will also be
unavailable. If the account is not topped up or the resource package is not
renewed before the retention period expires, the DB instance will become
unavailable and data stored in the DB instance will be deleted and cannot be
recovered.
● Overdue Payment
Overdue payment is only for DB instances billed on the pay-per-use basis.
A pay-per-use DB instance is billed by hour. If the account balance is not
enough to cover the payment, the DB instance is in arrears. If the DB instance
is renewed within the retention period, it will be available and charged from
the original expiration date.
GaussDB
Service Overview 12 Billing
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 708

13 Related Services
Table 13-1 shows the relationship between GaussDB and other services.
Table 13-1 Related services
Service Description
Elastic Cloud
Service (ECS)
Enables you to access GaussDB instances through an ECS to
reduce application response time and public network trac
fees.
Virtual Private
Cloud (VPC)
Isolates your network and controls access to your GaussDB
instances.
Object Storage
Service (OBS)
Stores automated and manual backups of your GaussDB
instances.
Cloud Eye Acts as an open monitoring platform that monitors
GaussDB resources in real time. It reports alarms and issues
warnings promptly to ensure you are notied immediately
if your services are not running properly.
Cloud Trace
Service (CTS)
Provides records of operations on cloud service resources,
enabling you to query, audit, and backtrack operations.
Data Admin
Service (DAS)
Provides a visualized GUI interface for you to connect and
manage cloud databases.
GaussDB
Service Overview 13 Related Services
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 709

A Change History
Released On Description
2023-12-30 Modied the following content:
● Added GaussDB Engine Version Description.
● Added Mapping Between GaussDB DB Engine and
Kernel Engine Versions.
● Added Checking the DB Engine and Kernel Engine
Version of a GaussDB Instance.
● Added Logs.
● Revised GaussDB Infographics, What Is GaussDB?,
Instance Specications, DB Instance Parameters, and
Data Protection.
GaussDB
Service Overview A Change History
Issue 01 (2024-04-30) Copyright © Huawei Cloud Computing Technologies Co., Ltd. 710

